Current Flattening in Software and Hardware for Security Applications
description
Transcript of Current Flattening in Software and Hardware for Security Applications

Radu Muresan
CODES+ISSS'04, September 8-10, 2004, Stockholm, Sweden 1
Current Flattening in Software and Hardware for Security Applications
Authors: R. Muresan, C. GebotysPresentation By: Radu Muresan

Radu Muresan
CODES+ISSS'04, September 8-10, 2004, Stockholm, Sweden 2
Outline Introduction Power analysis attacks (PAAs)
Definitions, examples, countermeasures Current flattening technique
Definition, methodology, implementations
Current flattening as a countermeasure against PAAs
Results and conclusions

Radu Muresan
CODES+ISSS'04, September 8-10, 2004, Stockholm, Sweden 3
Introduction Embedded
systems are increasingly used in security applications
The software and the hardware components must be secure against all threats
Current flattening is a potential countermeasure against PAAs Secret-key Cryptosystem: ke = kd
Public – key Cryptosystem: ke ≠ kd
Encryption
Decryption
Ciphertext
Message Channel
Plaintext
Plaintext
KeyGeneration
kd
ke
Key Channel

Radu Muresan
CODES+ISSS'04, September 8-10, 2004, Stockholm, Sweden 4
What is a Power Analysis Attack ? Side-channel attacks
exploit correlation between secret parameters and variations in timing, power consumption, and other emanations from cryptographic devices to reveal secret keys
CryptographicDevice
R
Currentor
PowerMeasurement
Power Supply
Attacker’s Point

Radu Muresan
CODES+ISSS'04, September 8-10, 2004, Stockholm, Sweden 5
Example, DPA Attack on a Scalar Multiplication Algorithm for EC Protocols
DPA, uses correlation between power consumption and specific key-dependent bits
kP, scalar multiplication Double-and-add approach, binary k(2) = (kn-1,...,k0)
kP1,kP2,...,kPn => Ci(t) = power kn-1 = 1; After the first iteration => Q[0] = 2Pi Second iteration
If kn-2=1 => Q[1] = 4P If kn-2=0 => Q[1] = 5P
g(t)=<Ci(t)>i=1,...,k|si=1 - <Ci(t)>i=1,...,k|si=0

Radu Muresan
CODES+ISSS'04, September 8-10, 2004, Stockholm, Sweden 6
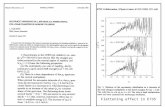
Example, DPA Attack on a Scalar Multiplication Algorithm for EC Protocols
A peak is observed when 4Pi are computed by the card
No peak is observed when 4Pi are never computed by the card
Simulated correlation function between the points 4Pi and power consumptionCi(t) when kn-2 = 0.

Radu Muresan
CODES+ISSS'04, September 8-10, 2004, Stockholm, Sweden 7
Countermeasures Against PAAs Against timing attacks
Equalizing; Randomizing; Blinding Against simple power analysis attacks
Avoiding; Creating; Symmetric Against differential power analysis attacks
Randomization; Blinding Hardware: non-deterministic techniques
Against all PAAs Proposed: current flattening technique

Radu Muresan
CODES+ISSS'04, September 8-10, 2004, Stockholm, Sweden 8
What is Current Flattening? Current flattening
targets a flat (emission free) current consumption measured at an attacker’s point of a cryptographic device
CryptographicDevice
Attacker’s Point
CurrentFlattening(internal)
ExternalCurrentFilteringDevices

Radu Muresan
CODES+ISSS'04, September 8-10, 2004, Stockholm, Sweden 9
Behind Current Flattening Current
consumption in a processor is a function of: The hardware
architecture The instruction type The instruction
sequencing Data manipulated
Examples of current dynamics

Radu Muresan
CODES+ISSS'04, September 8-10, 2004, Stockholm, Sweden 10
Software Method Program execution is
composed of two types of cycles charging; discharging
Code transformations are generated for classes of instructions
Current measurements used for determining code transformations
ClassFLATTEN0 [ALU Units]
FLATTENi [ALU Units]
ALU 1 1
NOP 0 0
CONTROL 4 3
Example

Radu Muresan
CODES+ISSS'04, September 8-10, 2004, Stockholm, Sweden 11
Hardware Method Pipeline
current flattening module

Radu Muresan
CODES+ISSS'04, September 8-10, 2004, Stockholm, Sweden 12
Hardware Method Feedbac
k current module

Radu Muresan
CODES+ISSS'04, September 8-10, 2004, Stockholm, Sweden 13
Does Current Flattening Protect Against PAAs?
Software method does not support DPA due to the fact that the program to data dependencies are not covered
Hardware method has potential to cover all PAAs Supports real-time current adjustment at
the clock frequency Covers both current to data and to
instruction dependencies

Radu Muresan
CODES+ISSS'04, September 8-10, 2004, Stockholm, Sweden 14
Results of Software Flattening The experiments
used the polymulNIST.asm implementation of an EC scalar multiplication (kP), where: P a fixed point
on a known elliptic curve
k a secret key Target processor:
Motorola SC140 DSP Real current measurements

Radu Muresan
CODES+ISSS'04, September 8-10, 2004, Stockholm, Sweden 15
Results of Software Flattening Pk-Pk current
variation reduced by 70 to 78%
Energy consumption increased by 71 to 74%
Execution time increased by up to 135%
Ver-sion
StartTime [μs]
End Time[μs]
EnergyProg.[μJ]
Mean[mA]
S[mA]
Pk-Pk[mA]
M1 25 681 209.9 0.168 18.85 67.7
M2 25 1569 363.2 0.124 1.60 20.3
M4 25 1545 359.9 0.125 1.91 16.8
M7 25 1569 365.5 0.125 1.98 14.3
Data analysis for software flattening

Radu Muresan
CODES+ISSS'04, September 8-10, 2004, Stockholm, Sweden 16
Results of Hardware Flattening Instantaneous
current simulation for polymul.asm polymul.asm is a
subroutine of polymulNIST.asm
polymul.asm is a target of PAAs
Target system Motorola SC140
DSP plus the Feedback Current Module
Current simulation and real current measurement

Radu Muresan
CODES+ISSS'04, September 8-10, 2004, Stockholm, Sweden 17
Results of Hardware Flattening Pk-Pk current
variation reduced by 94 to 97%
Energy consumption increased by up to 16%
Execution time increased by up to 29%
Wave-form
RunTime [μs]
Energy[μJ]
Max[mA]
S[mA]
Pk-Pk
[mA]
blue 21.3 6.04 167.7 2.47 22.4
red 21.3 6.14 168.5 1.87 19.2
mag. 23.7 6.47 144.0 0.38 1.2
black 27.5 7.01 134.0 0.13 0.6
Data analysis for hardware flattening

Radu Muresan
CODES+ISSS'04, September 8-10, 2004, Stockholm, Sweden 18
Conclusions The paper presented the mechanisms
of the internal current flattening technique (ICF)
ICF controls power consumption and current variation Countermeasure against PAAs
Limitations Increased execution time and energy
consumption

Radu Muresan
CODES+ISSS'04, September 8-10, 2004, Stockholm, Sweden 19
Future Work
Investigate an ASIC implementation of the PAAR architecture
Methods to improve the performance and energy consumption of implementations using ICF

Radu Muresan
CODES+ISSS'04, September 8-10, 2004, Stockholm, Sweden 20
References Used for the Presentation Slides 3 and 4
W. Mao, “Modern Cryptography”, Prentice Hall, 2004 O. Kommerling, M. G. Kuhn, “Design principles for
tamper-resistant smartcard processors”, In Workshop on Smartcard Technology 1999
Slides 5, 6 and 7 J-S. Coron, “Resistance against dpa for elliptic curve
cryptosystems”, CHES’99 P. Kocher, et al., “Differential power analysis”, In
CRYPTO’99 Slide 9
R. Muresan, C. Gebotys, “Instantaneous current modeling in a complex vliw processor core”, In ACM TECS, 2004

Radu Muresan
CODES+ISSS'04, September 8-10, 2004, Stockholm, Sweden 21
THANK YOU!
Questions?