UNIFIED SECURITY - Comstormedia.gswi.westcon.com/media/westcon-AT/Customer-Downloads/c… · F5...
Transcript of UNIFIED SECURITY - Comstormedia.gswi.westcon.com/media/westcon-AT/Customer-Downloads/c… · F5...

UNIFIED SECURITYUNIFIED SECURITY
Ralf SydekumRalf SydekumTechnical Manager Central EuropeTechnical Manager Central Europe
UNIFIED SECURITYUNIFIED SECURITY

CyberCyber--attacks in the News for 2011attacks in the News for 2011
IBM X-Force 2011 Trend and Risk Report March 2012

of network traffic is encrypted bypassing security controls
Security is still expendable… Security device sprawl is a
30% Blended attacks… are overwhelming conventional security devices at the edge of the data center.
Security ChallengesSecurity Challenges
Traditional network devices are failing under load… 3 out of 6 major firewalls failed under stability testing, and 5 out of 6 were vulnerable to a common exploit.
Security is still expendable… 9 out of 10 IT organizations admit to sacrificing security for performance.
Over 90% of IT administrator want…
Security Context
Security device sprawl is a challenging problem… IT biggest security challenge with device sprawl is operational complexity.

Statement Statement -- SONY SONY Online EntertainmentOnline Entertainmenthttp://blog.eu.playstation.com/http://blog.eu.playstation.com/
•• On April 16th and 17th, 2011….. Personal information from On April 16th and 17th, 2011….. Personal information from approximately 24.6 million SOE accounts may have been approximately 24.6 million SOE accounts may have been stolen…,stolen…,•• Name, eName, e--mail, login, hashed password,…mail, login, hashed password,…
•• As As well as certain information from an outdated database from well as certain information from an outdated database from 2007 for 10.700 customer in EU2007 for 10.700 customer in EU•• Name, bank account number, address,…Name, bank account number, address,…

Sony stock performance: Sony stock performance: Nov 2010Nov 2010--Nov Nov 20112011

•• Several companies stopped the service for Several companies stopped the service for WikiLeaksWikiLeaks although although it is not proven that it is not proven that WikiLeaksWikiLeaks violates the existing lawviolates the existing law
•• Amazon removed all Amazon removed all WikiLeaksWikiLeaks content from their serverscontent from their servers•• EveryDNSEveryDNS switched off the DNS resolution for wikileaks.orgswitched off the DNS resolution for wikileaks.org•• Several financial institutes locked up donation accountsSeveral financial institutes locked up donation accounts
What happened What happened toto WikiLeaksWikiLeaks??

Finally…Finally…
•• Thousand of internet users unloaded their accumulated anger starting Thousand of internet users unloaded their accumulated anger starting 7th Dec 20107th Dec 2010
•• Web Web servers of servers of Swiss Swiss PostfinancePostfinancebank were down bank were down for several for several hourshours
•• Credit card companies Credit card companies likelike•• Credit card companies Credit card companies likelikeMastercardMastercard and VISA and VISA where where notnotaccessible for several hours/dayaccessible for several hours/dayover over several several daysdays
•• Paypal’sPaypal’s transaction network transaction network werewereslowslow but not but not taken down completelytaken down completely

•• 3 Basic Classes of Attack 3 Basic Classes of Attack •• L7 (HTTP/Web): Slowloris L7 (HTTP/Web): Slowloris
•• Creates massive concurrent sessions Creates massive concurrent sessions •• Firewalls quickly overwhelmedFirewalls quickly overwhelmed•• Server resources completely consumed Server resources completely consumed
•• L4: TCP Flood/Syn Flood L4: TCP Flood/Syn Flood •• Targets any TCP aware deviceTargets any TCP aware device
•• L3: ICMP FloodL3: ICMP Flood
WikiLeaks DDoS Attack ProfileWikiLeaks DDoS Attack Profile
Border Router (Internet Connection)
ICMP flood TCP FloodSlowloris
•• L3: ICMP FloodL3: ICMP Flood•• ICMP protocol attackICMP protocol attack•• Consumes router, Firewall and server resourcesConsumes router, Firewall and server resources
•• BIGBIG--IP/ASM stopped attacks!IP/ASM stopped attacks!•• Combination of core TMOS functionality, Combination of core TMOS functionality, iRulesiRules and and
ASM (Application Security ASM (Application Security ManagerManager))
PCI Compliant Firewall
F5 BIG-IP with ASM Module
Intrusion Prevention Device

The Three Threat VectorsThe Three Threat Vectors
Network Attacks Application AttacksDDoS Attacks

Unified Security Unified Security Architecture Architecture
Traditional Approach
LOAD BALANCER
FIREWALLWEB APPFIREWALL
DDoSPROTECTION
DNSSECURITY
ACCESSMANAGEMENTAND REMOTE
ACCES

DNS WEB ACCESS
LTM

DATA CENTER FIREWALLDATA CENTER FIREWALLDATA CENTER FIREWALLDATA CENTER FIREWALL

BIF
UR
CAT
ION
Next Generation Firewall
EnterpriseDatacenter
Datacenter Firewall
Internet Datacenter
Two different use cases Two different use cases
BIF
UR
CAT
ION
OF
FIR
EW
ALLSCharacteristics
• Outbound User Inspection• UserID and AppID• Who is doing What?• 1K users to 10K web sites• Broad but Shallow
Datacenter
(Users)
Datacenter
(servers)
Characteristics
• Inbound Application Protection• Application Delivery Focus• 1M users to 100 Apps• Narrow but Deep• 12 Protocols (HTTP, SSL, etc)

Internet Data Center Perimeter FirewallInternet Data Center Perimeter FirewallPerimeter Firewall with Load Balancer
Today
Overview• Traditional firewall• Standalone load balancer
Load Balancer
Limitations• DDoS protection• Connections• Scale• Device management• Defense methods

Internet Data Center Perimeter FirewallInternet Data Center Perimeter FirewallPerimeter Firewall with Load Balancer
With BIG-IPOverview• Consolidated Device• Firewall Service• Application Delivery• Web Application Firewall
Benefits
BIG-IP LTM with ASM
Benefits• Application fluency• SSL visibility• DDoS protection 30 + types• Dynamic defense methods• Best price to performance class• OWASP top 10 protection

Connections per SecondConnections per Second
Competitor ABC + 4 Blades$124,000
F5 BIG-IP 11050$129,995

WEB SECURITY SERVICES WEB SECURITY SERVICES WEB SECURITY SERVICES WEB SECURITY SERVICES

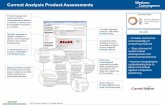
Integrated ADC SecurityIntegrated ADC SecurityBIGBIG--IP Application Security Manager IP Application Security Manager
• Simplifies and streamlines network topology • Unifies app. security and deliver for full L2 to L7 protection
BIG-IP LTM + ASM
SECURE APPLICATIONS & DATA
• Application Proxy• Transaction Assurance• Resource Cloaking• Network and protocol attack
prevention• Secure Network Address
Translation• Port Mapping• Selective Content Encryption
BIG-IP LTM + ASM
PROTECT WEB APPLICATIONS
• Layer 7 Web app. protection
• Secures latest interactive apps.
• Protects from OWASP Top 10+
• Educates admin. on attack type
• Logs and reports all traffic
• Meets PCI Compliance
• Out-of-the-box deployment
• Quickly resolves vulnerabilities

OWASP Top 10 Web Application Security Risks: OWASP Top 10 Web Application Security Risks: 1.1. Injection Injection 2.2. CrossCross--Site Scripting (XSS) Site Scripting (XSS) 3.3. Broken Authentication and Session Management Broken Authentication and Session Management
Protection Protection FFrom Top Web Application rom Top Web Application VulnerabilitiesVulnerabilities(Open Web Application Security Project)(Open Web Application Security Project)
4.4. Insecure Direct Object References Insecure Direct Object References 5.5. CrossCross--Site Request Forgery (CSRF) Site Request Forgery (CSRF) 6.6. Security Misconfiguration Security Misconfiguration 7.7. Insecure Cryptographic Storage Insecure Cryptographic Storage 8.8. Failure to Restrict URL Access Failure to Restrict URL Access 9.9. Insufficient Transport Layer Protection Insufficient Transport Layer Protection 10.10. Unvalidated Redirects and Forwards Unvalidated Redirects and Forwards
Source: www.owasp.org

Customer Website
Mitigate Vulnerabilities NowMitigate Vulnerabilities Now
• Finds a vulnerability
• Virtual-patching with
one-click on BIG-IP ASM
Web Application Scanner
BIG-IP Application Security Manager
• Verify, assess, resolve and retest in one UI
• Automatic or manual creation of policies
• Discovery and remediation in minutes
• Vulnerability checking,
detection and remediation
• Complete website protection

•• 3 free basic scans with “Open Cenzic Cloud Trial Account"3 free basic scans with “Open Cenzic Cloud Trial Account"•• "Connect with Cenzic Cloud" (for existing users)"Connect with Cenzic Cloud" (for existing users)•• Import vulnerabilities from Cenzic Cloud or load file Import vulnerabilities from Cenzic Cloud or load file
Quick Cenzic Cloud ConnectionQuick Cenzic Cloud Connection

IP IntelligenceIP IntelligenceIdentify and allow or block IP addresses with malicious activityIdentify and allow or block IP addresses with malicious activity
IP Intelligence Service
• Use IP intelligence to defend attacks
• Reduce operation and capital expenses
?
Scanners
Internally infected devices and servers

•• Fast IP update of malicious activity Fast IP update of malicious activity •• Global sensors capture IP behaviorsGlobal sensors capture IP behaviors•• Threat correlation reviews/ blocks/ releases Threat correlation reviews/ blocks/ releases
IP IntelligenceIP IntelligenceHow it worksHow it works
Key Threats Sensor Techniques
Web Attacks
Reputation
Windows Exploits
Botnets
Scanners
Network Attacks
DNS
Semi-open Proxy Farms
Exploit Honeypots
Naïve User Simulation
Web App Honeypots
Third-party Sources

Graphical ReportingGraphical ReportingDetailed chart path of threats in ASMDetailed chart path of threats in ASM

WEB ACCESS MANAGEMENTWEB ACCESS MANAGEMENTWEB ACCESS MANAGEMENTWEB ACCESS MANAGEMENT

One Access Solution One Access Solution –– BIGBIG--IP APMIP APM
All AccessUse Cases
Web Access Management:• Proxy to HTTP apps
– Custom– 3rd party
Remote Access: • SSL VPN
– Network Access– Portal Access– App Tunnels
BIG-IP Access Policy Manager
Application Access Control:• Proxy to Non-HTTP apps
– Citrix ICA– ActiveSync– Outlook Anywhere

Web Access ManagementAuthentication Alternatives Today
APP 1
APP 2
APP 3
123
Proxy Web Servers
APP n
1 Code in the Application• Costly, difficult to
change• Not repeatable, less
secure
2 3Agents on Servers• Difficult to manage• Not interoperable or secure• Decentralized and costly
Specialized Access Proxies• Doesn’t scale and not
reliable• More boxes and
expensive
Directory

Enable Simplified Enable Simplified Application AccessApplication AccessWith With BIGBIG--IP Access Policy Manager (APM)IP Access Policy Manager (APM)

Authentication All in One and Fast SSO Authentication All in One and Fast SSO F5 BIGF5 BIG--IP Access Policy ManagerIP Access Policy Manager
Dramatically reduce infrastructure costs; increase productivityDramatically reduce infrastructure costs; increase productivity

Control Access of EndpointsControl Access of EndpointsEnsure strong endpoint securityEnsure strong endpoint security
Allow, deny, or remediate Allow, deny, or remediate Invoke protected workspace Invoke protected workspace
BIG-IP APM
• Client or machine certificates
• Antivirus software versionand updates
• Software firewall status
• Access to specific applications
• Restrict USB access
• Cache cleaner leaves no trace
• Ensure no malware enters corporate network
Allow, deny, or remediate Allow, deny, or remediate users based on endpoint users based on endpoint attributes such as:attributes such as:
Invoke protected workspace Invoke protected workspace for unmanaged for unmanaged devices:devices:

!Non-
compliantInformation
App Security with BIGApp Security with BIG--IP ASM and APMIP ASM and APM
!Illegal
requests
ASM allowslegitimate requests
ASMStops bad requests /responses
!InfrastructuralIntelligenceAPM offers authentication
and authorization
!Unauthorised
Access
Reduces the attack vector because only authenticate d, authorized and legal requests are permitted to the relevant ap plication servers
APMStops
unauthorizedrequests
BrowserApplications

DNSDNS SECURITY USE CASESSECURITY USE CASESDNSDNS SECURITY USE CASESSECURITY USE CASES

DNS Attacks Are CommonDNS Attacks Are Common

DNS DNS is is Vulnerable to AttacksVulnerable to Attacks
Data Center
DNS Servers www.company.com
• Multiple DNS attacks: DDoS, Cache Poisoning, Man-in-the-middle• Application timeouts (401 errors)• Lost customers, lost productivity• Loss of Revenue and Brand Equity
LDNS

Complete DNS Protection Complete DNS Protection BIGBIG--IP Global Traffic ManagerIP Global Traffic Manager
LDNS
Data Center
company.com
X QA i
• High Performance DNS – Multicore GTM
• Scalable DNS - DNS Express
• Malformed UDP packets are dropped
• Spread the load across devices - IP Anycast
• Secure DNS Queries - DNSSEC
• Route based on nearest Datacenter - Geolocation
• Complete DNS control with – DNS iRules
LDNS
A
X
Q
i

Exponential and Efficient DNS Performance Exponential and Efficient DNS Performance Implement DNS ExpressImplement DNS Express
DNS ExpressDNS Express
•• HighHigh--speed response and DDoS protection with inspeed response and DDoS protection with in--memory DNSmemory DNS
•• Authoritative DNS serving out of RAMAuthoritative DNS serving out of RAM
•• Configuration size for tens of millions of recordsConfiguration size for tens of millions of records
•• Scalable DNS PerformanceScalable DNS Performance
•• Consolidate DNS ServersConsolidate DNS Servers DNS Server•• Consolidate DNS ServersConsolidate DNS Servers
ManageDNS
Records
NIC
OSAdminAuthRoles
DynamicDNS
DHCP
AnswerDNS
Query
AnswerDNS
Query
AnswerDNS
Query
AnswerDNS
Query
AnswerDNS
Query
DNS Express in TMOS
DNS Server
queries/second BIG-IP 1600: ~300k qpsBIG-IP 3900: ~600k qpsBIG-IP 8900: ~1.5 Million
VIPRIONUp to 6 million qps!

Rethinking your approach through Rethinking your approach through consolidationconsolidation
Traditional Datacenter
Anti-DDoS
IPS
F5 Datacenter Firewall Transformation
Anti-DDoS
Remote AccessIPS
Firewall
Load Balancer
App Servers
• Traditional firewalls blind to SSL• Limited DDoS protection• Management headache across devices
• Layer 3-7, DDoS protection• High performance and flexible• Achieve 4X cost reduction
Remote Access
Firewall
Load Balancer

Summary Summary –– F5 Unified SecurityF5 Unified Security
















![DEPARTMENT OF STATE [Public Notice 11050] Office of the ... · Billing Code 4710-20 DEPARTMENT OF STATE [Public Notice 11050] Office of the Chief of Protocol; Gifts to Federal Employees](https://static.fdocuments.in/doc/165x107/5f5ac6cff6f309295c0c42bd/department-of-state-public-notice-11050-office-of-the-billing-code-4710-20.jpg)

![Lync & Juniper - Westcon-Comstormedia.gswi.westcon.com/media/6.1_Westcon_Presentation_Lync_201… · A/V Edge – SRTP:443,3478,[TCP:50,000-59,999] SRTP consists of two unidirectional](https://static.fdocuments.in/doc/165x107/5af383ea7f8b9a8c30914548/lync-juniper-westcon-av-edge-srtp4433478tcp50000-59999-srtp-consists.jpg)
