Dipartimento di Scienze - 19 giugno 2015 1 Pamela Peretti Dottorato di ricerca in Scienze XXI°...
-
date post
15-Jan-2016 -
Category
Documents
-
view
216 -
download
0
Transcript of Dipartimento di Scienze - 19 giugno 2015 1 Pamela Peretti Dottorato di ricerca in Scienze XXI°...

Dipartimento di Scienze - 21 aprile 2023 1
Pamela Peretti
Dottorato di ricerca in Scienze
XXI° cicloscrutinio annuale
a.a 2007/2008
Dipartimento di ScienzeUniversità degli Studi “G. d’Annunzio”
Pescara
tutor: Prof. Stefano Bistarelli

My PhD thesis
Dipartimento di Scienze - 21 aprile 2023 2

Risk management is a detailed process of identifying factors that could damage or disclose data, evaluating those factors in light of data value and countermeasure cost, and implementing cost-effective solutions for mitigating or reducing risk.
Dipartimento di Scienze - 21 aprile 2023 3

Dipartimento di Scienze - 21 aprile 2023 4
Terminology
An asset is any tangible or intangible item owned by an organization that has a value for an enterprise and that needs protection.

Dipartimento di Scienze - 21 aprile 2023 5
Terminology
Any potential occurrence that may cause an undesirable or unwanted outcome for an organization or for a specific asset is a threat.

Dipartimento di Scienze - 21 aprile 2023 6
Terminology
The absence or the weakness of a countermeasure or safeguard is a vulnerability.
An attack is any intentional attempt to exploit a vulnerability of an organization's security infrastructure to cause damage, loss, or disclosure of assets.

Dipartimento di Scienze - 21 aprile 2023 7
Terminology
Exposure is being susceptible to asset loss because of an attack; there is the possibility that a vulnerability can or will be exploited by an attacker or event.

Dipartimento di Scienze - 21 aprile 2023 8
Terminology
Risk is the possibility or likelihood that a threat will exploit a vulnerability to cause harm to an asset.

Dipartimento di Scienze - 21 aprile 2023 9
Terminology
A countermeasure is anything that removes a vulnerability or protects against one or more specific attacks.

select the appropriate countermeasures
Identify the possible countermeasures
Identify the possible threats
Dipartimento di Scienze - 21 aprile 2023 10
Assessment methodology
Quantitative approaches Assigns absolute numeric attribute values to assets, threats, vulnerabilities and
countermeasures.
Qualitative approaches Qualitative risk analysis is a scenario-based approach. You rank threats on a scale to
evaluate their risks, costs, and effects. Instruments: brainstorming, Delphi technique, focus groups, surveys, questionnaires, checklists and interviews.
Identify asset

Dipartimento di Scienze - 21 aprile 2023 11
Assign the AV select the appropriate countermeasures
Identify the possible countermeasures
Identify the possible threats
Identify asset
Quantitative approaches
The Asset Value (AV) is a synthetic measure of the cost of creation, development support, replacement and ownership value of an asset.

Dipartimento di Scienze - 21 aprile 2023 12
Calculate the EF and the SLE
Calculate the ARO
Calculate the ALE select the appropriate countermeasures
Identify the possible countermeasures
Identify the possible threats
Identify asset
Quantitative approaches
The Exposure factor (EF) represents the percentage of loss that an organization would experience if a specific asset were violated by an attack.
The Single Loss Exposure (SLE) represents a measure of an organization's loss from a single threat against a specific asset and can be computed by using the following formula:

Dipartimento di Scienze - 21 aprile 2023 13
Calculate the EF and the SLE
Calculate the ARO
Calculate the ALE
select the appropriate countermeasures
Identify the possible countermeasures
Identify the possible threats
Identify asset
Quantitative approaches
The Annualized Rate of Occurrence (ARO) is the expected frequency with which a specific threat or attack will occur within a single year.
The Annualized Loss Expectancy (ALE) is the annually expected financial loss of an organization which can be ascribed to a threat and can be computed by using the following formula:

Evaluate the RM and the CSI
Dipartimento di Scienze - 21 aprile 2023 14
select the appropriate countermeasures
Identify the possible countermeasures
Identify the possible threats
Identify asset
Quantitative approaches
The Risk Mitigated by a countermeasure (RM) represents the effectiveness of a countermeasure in mitigating the risk of loss deriving from exploiting a vulnerability. It is a numeric value between 0 and 1.
The Cost of a Security Investment (CSI) is the cost that an organization must face for implementing a given countermeasure.

Dipartimento di Scienze - 21 aprile 2023 15
Calculate the ROIselect the appropriate
countermeasuresIdentify the possible
countermeasuresIdentify the
possible threatsIdentify asset
Quantitative approaches
Given an attack a and a countermeasure c which is able to mitigate a, the Return on Investment (ROI) is the benefit that a defender of an IT system expects from the introduction of c into the system over the costs for implementing that countermeasure.

Dipartimento di Scienze - 21 aprile 2023 16
Calculate the ROI
Calculate the ROA
select the appropriate countermeasures
Identify the possible countermeasures
Identify the possible threats
Identify asset
Quantitative approaches
The Return on Attack (ROA) is the gain that an attacker expects from a successful attack a over the costs he sustains due to the adoption of a countermeasure c by its target.
where GI is the expected gain of the attack, GI RMc is the lost profit produced by c and costa is the cost associated to an attack strategy a.

Dipartimento di Scienze - 21 aprile 2023 17
Qualitative approaches
Qualitative risk analysis is a scenario-based approach.
A scenario is a written description of a single major threat. The description focuses on how a threat would be instigated and what effects it could have on the organization, the IT infrastructure, and specific assets.

Interruption of
service
Diffusion of reserved
information
Loss of
data
A security scenario
Dipartimento di Scienze - 21 aprile 2023 18

Defence trees are an extension of attack trees [Schneier00].
Attack tree: the root is an asset of an IT system paths from a leaf to the root represent attacks to the asset the non-leaf nodes can be:
and-nodes or-nodes
Defence tree: attack tree a set of countermeasures
root
and-nodes
or-nodes
Defence trees
Dipartimento di Scienze - 21 aprile 2023 19

Dipartimento di Scienze - 21 aprile 2023 20
c7
c6
c9
c8
a3 a4
c2
c3
c1
c4
c5
c3
a1 a2
c11
c10
c13
c12
a5 a6
Steal datastored in a server
Obtain root privileges
Attack the system with a remote login
Steal theserver
Defence trees

Quantitative evaluation
1. An economic evaluation of threats Considering multiple attacks and countermeasures Combining the defender's and the attacker's points of view
2. Three novel indexes The Exposure Factor during Critical Time The Exposure Factor under Retaliation The Risk Mitigated against Collusion
3. Interaction between attackers and defender Defence tree as strategic game Using economic indexes as payoffs
Dipartimento di Scienze - 21 aprile 2023 21

Quantitative evaluation
1. An economic evaluation of threats Considering multiple attacks and countermeasures Combining the defender's and the attacker's points of view
2. Three novel indexes The Exposure Factor during Critical Time The Exposure Factor under Retaliation The Risk Mitigated against Collusion
3. Interaction between attackers and defender Defence tree as strategic game Using economic indexes as payoffs
Dipartimento di Scienze - 21 aprile 2023 22

An economic evaluation of threats
Dipartimento di Scienze - 21 aprile 2023 23
The Return on Investment (ROI) The Return on Attack (ROA)

12
3
Multiple attacks and countermeasures
Dipartimento di Scienze - 21 aprile 2023 24
single attack multiple countermeasures
multiple attacks single countermeasure
multiple attacks multiple countermeasures

Multiple attacks and countermeasures
Dipartimento di Scienze - 21 aprile 2023 25

Multiple attacks and countermeasures
Dipartimento di Scienze - 21 aprile 2023 26

Quantitative evaluation
1. An economic evaluation of threats Considering multiple attacks and countermeasures Combining the defender's and the attacker's points of view
2. Three novel indexes The Exposure Factor during Critical Time The Exposure Factor under Retaliation The Risk Mitigated against Collusion
3. Interaction between attackers and defender Defence tree as strategic game Using economic indexes as payoffs
Dipartimento di Scienze - 21 aprile 2023 27

Three novel indexes
Dipartimento di Scienze - 21 aprile 2023 28
The Exposure Factor during critical time (EFCT) expresses the influence that the criticality of a specific time instance plays on the EF.
The Exposure Factor under retaliation (EFR) expresses the influence that the chance of retaliating an attack to an asset plays on the EF.
The Risk Mitigated against collusion (RMC) expresses the influence that collusion of attackers plays on the RM.

Quantitative evaluation
1. An economic evaluation of threats Considering multiple attacks and countermeasures Combining the defender's and the attacker's points of view
2. Three novel indexes The Exposure Factor during Critical Time The Exposure Factor under Retaliation The Risk Mitigated against Collusion
3. Interaction between attackers and defender Defence tree as strategic game Using economic indexes as payoffs
Dipartimento di Scienze - 21 aprile 2023 29

We consider a strategic game: 2 players: the defender and the attacker of a system. Sd: the set of defender's strategies (the countermeasures)
Sa: the set of attacker's strategies (the vulnerability) ROI and ROA: payoff functions for the defender and the attacker
Strategic game
Dipartimento di Scienze - 21 aprile 2023 30
a1a2
c2
c3
c3 c1
Ud=1Ua=1
Ud=0Ua=2
Ud=1Ua=2
Ud=1Ua=0

Selection of a single countermeasure/attack
16
!The set of strategies for the defender and the attacker is composed by a single action.
Install asecurity door
Install a videosurveillanceequipment
c4 c2
c3Assume
a securityguard
Install asafety lock
Install a videosurveillanceequipment
c2
c3Assume
a securityguard
c1
Go outunobserve
d
a1 a2
Have the keys
Break downthe door
Go outunobserve
d
Steal theserver
Strategic game: example
Dipartimento di Scienze - 21 aprile 2023 31

Selection of a single countermeasure/attack
16
!The set of strategies for the defender and the attacker is composed by a single action.
Strategic game: example
Dipartimento di Scienze - 21 aprile 2023 32

Qualitative evaluation
Cp-defence trees AND-composition of preference OR-composition of preference
Translation of AND/OR attacks into ASO programs AND attacks OR attacks
Dipartimento di Scienze - 21 aprile 2023 33

Qualitative evaluation
Cp-defence trees AND-composition of preference OR-composition of preference
Translation of AND/OR attacks into ASO programs AND attacks OR attacks
Dipartimento di Scienze - 21 aprile 2023 34

Cp-defence trees
Cp-defence tree is a defence tree enriched with conditional preference
over attack and countermeasures.
A
C
c11
c10
c13
c12
c7
c6
c9
c8
c2
c3
c1
c4
c5
c3
a5 a6a3 a4a1 a2
a1 c1Â c2Â c3
a2 c5Â c3Â c4
a3 c6Â c7
a4 c8Â c9
a5 c11Â c10
a6 c13Â c12
a2Âa1Âa6Âa5Âa3Âa4
Cp-net [Boutiliet99] are a graphical formalism to specify and representing conditional preference relations.
Dipartimento di Scienze - 21 aprile 2023 35

An and-attack is an attack composed by a set of actions that an attacker has to successfully achieve to obtain his goal.
AND-composition of preference
a
bx Æ y Æ z
x a  b  c
y b  c
z a  b c
a
b
c
x
c
b
y
a
b
zA = {x,y,z}C = {a,b,c}
: a  b  c
and-composition
Dipartimento di Scienze - 21 aprile 2023 36

An and-attack is an attack composed by a set of actions that an attacker has to successfully achieve to obtain his goal.
AND-composition of preference
a
b
x Æ y
x a  b
y c  d c
a
b
x
d
c
yA = {x,y}C = {a,b,c,d}
dx  y
: c  d  a  b
and-composition
Dipartimento di Scienze - 21 aprile 2023 37

OR-composition of preference
An or-attack is an attack composed by different and alternative actions that an attacker has to successfully achieve to obtain his goal.
x Ç y Ç z
a,b,c
b,c
a
a,b
a,c
x a  b  c
y c  a
z a  b
<b,a,a>
<b,c,b>
A = {x,y,z}C = {a,b,c}
b b a c a b
[b,c] [a,b]
<a,a,a> <a,a,b>
<a,c,a> <a,c,b>
<b,a,a> <b,a,b>
<b,c,a> <b,c,b><c,a,a> <c,a,b>
<c,c,a> <c,c,b>
[a]
[a,b]
[a,c]
[b,c]
[a,b,c]
or-composition
Dipartimento di Scienze - 21 aprile 2023 38

Qualitative evaluation
Cp-defence trees AND-composition of preference OR-composition of preference
Translation of AND/OR attacks into ASO programs AND attacks OR attacks
Dipartimento di Scienze - 21 aprile 2023 39

Translation of AND-attacks
The optimal answer set associated to <Pand,Φ> is the set M4={root, x,a}
The preferred set of countermeasures is the set {a}.
a
b
c
x
a
b
y
rx1: x Ã
rx2: a Ç b Ç c à x
x1: a > b > c à x
Px
Py
rx1: x Ã
rx2: a Ç b Ç c à x
x1: a > b > c à x
ry1: y Ã
ry2: a Ç b à y
y1: a > b à y
ry1: y Ã
ry2: a Ç b à y
y1: a > b à y
r1: root ÃPand
r2: x Ç y à root
ANDAND
Dipartimento di Scienze - 21 aprile 2023 40

Translation of OR-attacks
The optimal answer set associated to <Por,Φ> is M’1={root’, x, y, a}
The preferred set of countermeasures is the set {a}.
a
b
c
x
a
b
y
rx1: x Ã
rx2: a Ç b Ç c à x
x1: a > b > c à x
Px
Py
rx1: x Ã
rx2: a Ç b Ç c à x
x1: a > b > c à x
ry1: y Ã
ry2: a Ç b à y
y1: a > b à y
ry1: y Ã
ry2: a Ç b à y
y1: a > b à y
r1: root’ ÃPor
r3: y à root’
OR
r2: x à root’
OR
Dipartimento di Scienze - 21 aprile 2023 41

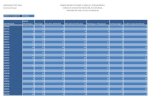
Dipartimento di Scienze - 21 aprile 2023 42
ASO and Cp-defence tree
root a12 root
a34 root
a56 root
a1 a12
a2 a12
a3 a34
a4 a34
a5 v a6 a56
c1 v c2 v c3 a1
c3 v c4 v c5 a2
c6 v c7 a3
c8 v c9 a4
c10 v c11 a5
c12 v c13 a6
c1 > c2 > c3 a1
c5 > c3 > c4 a2
c6 > c7 a3
c8 > c9 a4
c11 > c10 a5
c13 > c12 a6
Logic programming
Conditional preference rules

Dipartimento di Scienze - 21 aprile 2023 43
ASO and Cp-defence tree
root a12 root
a34 root
a56 root
a1 a12
a2 a12
a3 a34
a4 a34
a5 v a6 a56
1: c5 > c3 > c4 a2
2: c1 > c2 > c3 a1
3: c13 > c12 a6
4: c11 > c10 a5
5: c6 > c7 a3
6: c8 > c9 a4
c1 v c2 v c3 a1
c3 v c4 v c5 a2
c6 v c7 a3
c8 v c9 a4
c10 v c11 a5
c12 v c13 a6
Logic programming
Ranking of preference rules

Dipartimento di Scienze - 21 aprile 2023 44
Pamela Peretti
Dottorato di ricerca in Scienze
XXI° cicloscrutinio annuale
a.a 2007/2008
Dipartimento di ScienzeUniversità degli Studi “G. d’Annunzio”
Pescara
tutor: Prof. Stefano Bistarelli