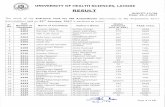
Virtual machines image protection in Cloud computing Muhammad Kazim (2011-NUST-MSCCS-23) Thesis...
-
Upload
norman-baldwin -
Category
Documents
-
view
218 -
download
3
Transcript of Virtual machines image protection in Cloud computing Muhammad Kazim (2011-NUST-MSCCS-23) Thesis...
Virtual machines image protection in Cloud
computing
Muhammad Kazim (2011-NUST-MSCCS-23)
Thesis Supervisor
Dr. Muhammad Awais Shibli
G.E.C Members
Dr. Abdul Ghafoor Abbasi
Dr. Hamid Mukhtar
Ms. Rahat Masood
Department of Computing, School of Electrical Engineering and Computer
Sciences, NUST - Islamabad
Agenda
• Introduction
• Motivation
• Research Methodology
• Problem Statement
• Research Contributions
• Implementation
• Results
• Evaluation
• Conclusion
Department of Computing, School of Electrical Engineering and Computer
Sciences, NUST - Islamabad
Virtualization
• In Cloud computing, Virtualization is the basis of providing Infrastructure as a Service (IaaS).
• A single system can concurrently run multiple isolated virtual machines (VMs), operating systems or multiple instances of a single operating system (OS).
• Virtualization maximizes the jobs a single CPU can do.
• Organizations are using virtualization to gain efficiency in platform and application hosting.
Department of Computing, School of Electrical Engineering and Computer Sciences, NUST –
Islamabad
Virtualization in Cloud
Figure 1: Virtualization in Cloud
Department of Computing, School of Electrical Engineering and Computer Sciences, NUST -
Islamabad
Virtual Disk Image
• A single file or directory representing the hard drive of a guest operating system.
• Encapsulates all components of a guest OS, including the applications and virtual resources used by guest OS.
• Provides the ability to quickly launch and deploy virtual machines across various hosts.
Department of Computing, School of Electrical Engineering and Computer Sciences, NUST - Islamabad
Motivation
• According to different surveys , virtualization security is one of the most important security issues in Cloud.
• Disk images in storage can be compromised through attacks such as unauthorized access, data leakage, malware installation and snapshot access in storage.
• Through attacks integrity, and confidentiality of images and sensitive customer data stored in them can be compromised.
• Standard bodies (NIST, CSA and PCI DSS) have published security guidelines to emphasize the importance of virtualization and disk images security.
Department of Computing, School of Electrical Engineering and Computer Sciences, NUST -
Islamabad
Research Methodology
Identifying problem
statement
Develop hypothesis
Testing and evaluation
Design framework
Defining research area
Literature review
Framework implementation
Department of Computing, School of Electrical Engineering and Computer Sciences, NUST - Islamabad
Figure 2: Thesis research methodology
Related Work• Literature survey
• IaaS Security
• Security analysis of virtualization
• Virtual machines security
• Disk images security
• Security guidelines on virtualization
• National Institute of Standards and Technology (NIST)
• Cloud Security Alliance (CSA)
• Payment Card Industry Data Security Standard (PCI DSS)
• Industrial solutions
• Storage Made Easy, Piston Cloud and Metacloud
Department of Computing, School of Electrical Engineering and Computer Sciences, NUST - Islamabad
Problem StatementVirtual machine images are vulnerable to infrastructure, hypervisor and storage attacks in Cloud. Therefore, VM images must be secured in Cloud storage through best security practices, both for protecting the sensitive customer data and maintaining the integrity of disk images.
Department of Computing, School of Electrical Engineering and Computer Sciences, NUST - Islamabad
Research Contributions
• Theoretical (Two research publications)
• Practical (Development of disk image protection framework)
Department of Computing, School of Electrical Engineering and Computer Sciences, NUST - Islamabad
Conference Papers
• Muhammad Kazim, Rahat Masood, Muhammad Awais Shibli, Abdul Ghafoor Abbasi, “Security aspects of virtualization in Cloud computing”, 12th International Conference on Computer Information Systems and Industrial Management Applications, CISIM, Springer, Krakow-Poland 2013, September 25-27.
• Muhammad Kazim, Rahat Masood, Muhammad Awais Shibli, “Securing the virtual machine images in Cloud computing”, 6th International Conference on Security of Information and Networks (SIN 2013), ACM-SIGSAC, Aksaray-Turkey 2013, November 26-28.
Department of Computing, School of Electrical Engineering and Computer Sciences, NUST - Islamabad
Analysis of virtualization security in Cloud
The security analysis of Cloud virtualization was done from three different aspects including:
•General requirements for securing Cloud virtualization components including hypervisor, virtual machines, disk images and service providers.
•Identification of possible attacks on virtualization components.
•Analysis of existing techniques for the security of virtualization components.
Department of Computing, School of Electrical Engineering and Computer Sciences, NUST - Islamabad
Virtual machines security analysisRequirements Attacks Solutions
Isolation between virtual machines should be properly implemented
Malicious programs use covert channels to communicate with other VMs in unauthorized way
Vigilant can monitor faults in guest OS of VM
Update the OS regularly and use anti-virus software, secure internet and restrict remote access
Malicious programs can monitor traffic, steal critical data, and tampering the functionality of VMs
Security features such as firewall, HIPS, log monitoring must be provided in guest OS
Securely boot the guest VMs
Attacker can tamper boot process of guest VMs
Security protocol by J. Kong can be to ensure secure boot of guest VMs
There must be limit on VMs resource usage
Using a malicious VM to consume extra resources of the system, resulting in DOS attack
Administrator must deploy a software or application that limits VMs to use authorized resources
Department of Computing, School of Electrical Engineering and Computer Sciences, NUST - Islamabad
Disk images security analysisRequirements Attacks Solutions
Disk images must be secured from storage attacks
Attacker can compromise the stored images by installing malware and accessing the contents of images
Use encryption and hashing of images before saving them
Snapshot access must be prevented from authorized access
VM checkpoint attacks Checkpoint attacks can be prevented by encrypting the checkpoints using SPARC
Apply updates and patches to maintain images secure
Old images are vulnerable to zero day attacks
Nuwa is a tool designed to apply efficient patching to VM images in Cloud
Backup of the virtual machines images must bemaintained
Unauthorized access to the backup data can result in leakage of sensitiveinformation
Backup of VM images must be encrypted. J. Wei et.al. proposed an image management system to manage Cloud VM imagesDepartment of Computing, School of
Electrical Engineering and Computer Sciences, NUST - Islamabad
Implementation Perspective
• Implement a framework that that ensures confidentiality of images through encryption.
• Images are decrypted when required by the VM.
• Hashing techniques are used to ensure integrity of images.
Department of Computing, School of Electrical Engineering and Computer Sciences, NUST -
Islamabad
Encrypted Virtual Disk Images in Cloud (EVDIC)
• To secure the virtual machine images from storage attacks in Cloud, EVDIC is proposed.
• EVDIC protects the virtual machine images in Cloud by encrypting them before storage. The images are decrypted only when required by the virtual machine.
• EVDIC proposes the security of key management and key exchange process.
16Department of Computing, School of Electrical Engineering and Computer Sciences, NUST -
Islamabad
Disk Image Storage in Cloud
Figure 4: Image Encryption in Cloud
Department of Computing, School of Electrical Engineering and Computer Sciences, NUST - Islamabad
Disk Image Retrieval in Cloud
Figure 5: Image Decryption in Cloud
Department of Computing, School of Electrical Engineering and Computer Sciences, NUST -
Islamabad
OpenStack
• OpenStack is a highly scalable and elastic cloud computing platform for both large and small public private Clouds.
• There are currently seven core components of OpenStack: Compute, Object Storage, Identity, Dashboard, Block Storage, Network and Image Service.
Department of Computing, School of Electrical Engineering and Computer Sciences, NUST -
Islamabad
Deployment of OpenStack for development
• Devstack • A documented shell script to build complete OpenStack development
environments
• Deployment of Devstack• Setup a fresh supported Linux installation
• Clone devstack
• Deploy your OpenStack Cloud
http://devstack.org/
Department of Computing, School of Electrical Engineering and Computer
Sciences, NUST - Islamabad
Debugging of source code
• Debugging of Swift through command line Pdb (Python debugger)
Department of Computing, School of Electrical Engineering and Computer
Sciences, NUST - Islamabad
Figure 6: Command line debugging using pdb
Virtual machines in OpenStack
Department of Computing, School of Electrical Engineering and Computer
Sciences, NUST - Islamabad
Figure 7: Virtual machines cycle in OpenStack
Integration of Image encryption and decryption with Swift
• OpenStack Swift API is implemented as a set of ReSTful web services.
• The proxy server initiates an internal Swift PUT request to the object servers.
• Object servers processes images chunk by chunk so each chunk gets encrypted and gets stored as part of encrypted file.
• For decryption object server decrypts each chunk before it sends the image to the proxy server.
Department of Computing, School of Electrical Engineering and Computer
Sciences, NUST - Islamabad
Image Encryption Module in Swift
Figure 8: Image Encryption in OpenStack
Department of Computing, School of Electrical Engineering and Computer
Sciences, NUST - Islamabad
Image Decryption Module in Swift
Department of Computing, School of Electrical Engineering and Computer
Sciences, NUST - Islamabad
Figure 9: Image Decryption in OpenStack
Department of Computing, School of Electrical Engineering and Computer
Sciences, NUST - Islamabad
Virtual machines cycle in OpenStack
Figure 10: IEM and IDM in OpenStack
Results
• After VM termination, image is stored into Swift encrypted storage.
• AES is block sized encryption, that adds extra padding to images.
• Encryption of images maintains their confidentiality in Cloud storage.
• Hash of image is taken before encryption. During decryption hash of image is calculated again, and compared with the original hash to ensure integrity of image.
Department of Computing, School of Electrical Engineering and Computer
Sciences, NUST - Islamabad
Evaluation• Various tools can be used to explore and modify the images
including CDmage, Daemon tools and Archive Manager.
• The content of encrypted images cannot be displayed by these tools.
• Our system provides protection to images from data leakage, data alteration and image modification.
• Performance evaluation of the system shows ~15% overhead caused on image processing time due to increase of image size after encryption, retrieval of encryption keys during encryption, decryption and applying the cryptographic techniques.
Department of Computing, School of Electrical Engineering and Computer
Sciences, NUST - Islamabad
Evaluation
Department of Computing, School of Electrical Engineering and Computer
Sciences, NUST - Islamabad
Figure 11: Image upload in Swift Figure 12: Image download in Swift
Conclusion
• Image encryption module encrypts all virtual disk images before storage in OpenStack. They are decrypted when required by the virtual machine.
• Integrity and confidentiality of virtual machine images in storage is ensured. They are secure from all possible storage attacks such as data theft, malware installation and hypervisor issues.
Department of Computing, School of Electrical Engineering and Computer
Sciences, NUST - Islamabad
Future Directions
• Encryption of accounts to protect users and images lists in Swift.
• Integration of Key Management protocol with Swift image encryption.
• Encryption of persistent storage used by virtual machines during execution.
Department of Computing, School of Electrical Engineering and Computer
Sciences, NUST - Islamabad
References
[1] Shubhashis Sengupta, Vikrant Kaulgud, Vibhu Saujanya Sharma, “Cloud Computing Security - Trends and Research Directions”, IEEE World Congress on Services, Washington, DC, USA, 2011.
[2] Jakub Szefer, Ruby B. Lee, “A Case for Hardware Protection of Guest VMs from Compromised Hypervisors in Cloud Computing”, 31st International Conference on Distributed Computing Systems Workshops, Washington, DC, USA, 2011.
[3] Jinzhu Kong, “Protecting the confidentiality of virtual machines against untrusted host”, International Symposium on Intelligence Information Processing and Trusted Computing, Washington, DC, USA, 2010.
[4] Farzad Sabahi, “Secure Virtualization for Cloud Environment Using Hypervisor-based Technology”, International Journal of Machine Learning and Computing vol. 2, no. 1, February 2012, pp.39-45.
[5] Jenni Susan Reuben, “A Survey on Virtual Machine Security”, TKK T-110.5290 Seminar on Network Security, 2007.
Department of Computing, School of Electrical Engineering and Computer
Sciences, NUST - Islamabad
[6] Seongwook Jin, Jeongseob Ahn, Sanghoon Cha, and Jaehyuk Huh, “Architectural Support for Secure Virtualization under a Vulnerable Hypervisor”, Proceedings of the 44th Annual IEEE/ACM International Symposium on Microarchitecture, USA, 2011.
[7] Ryan Shea, Jiangchuan Liu, “Understanding the Impact of Denial of Service on Virtual Machines”, IEEE 20th International Workshop on Quality of Service (IWQoS), Burnaby, BC, Canada, 2012.
[8] Wu Zhou, Peng Ning, Xiaolan Zhang, “Always up-to-date: scalable offline patching of VM images in a compute cloud”, Proceedings of the 26th Annual Computer Security Applications Conference, New York, USA, 2010, pp. 377-386.
[9] J.Wei, X. Zhang, G. Ammons, V. Bala, and P. Ning, “Managing security of virtual machine images in a cloud environment," in Proceedings of the 2009 ACM workshop on Cloud computing security. ACM, 2009, pp. 91- 96.
[10] Mikhail I. Gofman, Ruiqi Luo, Ping Yang, Kartik Gopalan, “SPARC: A security and privacy aware Virtual Machine checkpointing mechanism”, Proceedings of the 10th annual ACM workshop on Privacy in the electronic society, New York, USA, 2011, pp. 115-124.
Department of Computing, School of Electrical Engineering and Computer
Sciences, NUST - Islamabad