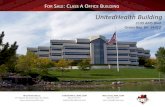
UnitedHealth Group
description
Transcript of UnitedHealth Group

UnitedHealth GroupUnitedHealth Group
David YerichDavid Yerich
Director, eDiscovery Director, eDiscovery
EMC User GroupEMC User Group
Tuesday 3/1/2011Tuesday 3/1/2011

OverviewOverview
E.D.R.M.E.D.R.M. Why UHG Legal chose KazeonWhy UHG Legal chose Kazeon Kazeon and eDiscoveryKazeon and eDiscovery Kazeon and File ManagementKazeon and File Management Kazeon and Record ManagementKazeon and Record Management

Electronic Discovery Reference Electronic Discovery Reference Model (EDRM)Model (EDRM)

Information Information ManagementManagement IdentificationIdentification PreservationPreservation CollectionCollection Analysis, Processing & Analysis, Processing &
ReviewReview
Collect and manage Collect and manage information from information from electronic sources, electronic sources, from initial creation of from initial creation of electronically stored electronically stored information through its information through its final disposition, final disposition, to to mitigate risk and mitigate risk and expenses should expenses should eDiscovery become an eDiscovery become an issue.issue.
Legal team develops Legal team develops and executes plan to and executes plan to identify and validate identify and validate potentially relevant potentially relevant ESI sources, ESI sources, including people and including people and systems.systems.
Ensure ESI is Ensure ESI is protected against protected against inappropriate inappropriate alteration or alteration or destruction. When destruction. When duty to preserve is duty to preserve is triggered, promptly triggered, promptly isolate and protect isolate and protect potentially relevant potentially relevant data in ways that are data in ways that are legally defensible; legally defensible; reasonable; reasonable; proportionate; proportionate; efficient; auditable; efficient; auditable; broad but tailored broad but tailored and mitigate risksand mitigate risks
In a legally In a legally defensible defensible manner,manner, gather gather ESI for further ESI for further processing, processing, review, etc., review, etc., in in litigation matters, litigation matters, governmental governmental inquiries and inquiries and internal internal investigations.investigations.
Analysis: Analysis: Evaluate ESI Evaluate ESI for content and context, for content and context, including key patterns, including key patterns, topics, people and topics, people and discussion to enable discussion to enable litigation teams to make litigation teams to make informed decisions about informed decisions about strategy and scope strategy and scope based on verified data. based on verified data. Processing Processing Reduce the Reduce the volume of ESI and volume of ESI and convert it, if necessary, to convert it, if necessary, to forms suitable for review forms suitable for review and analysis. and analysis. ReviewReview Evaluate ESI for Evaluate ESI for relevance and privilege. relevance and privilege. Develop facts, reduce Develop facts, reduce risk, reduce cost, risk, reduce cost, leverage technology, leverage technology, facilitate collaboration facilitate collaboration and communication.and communication.

Why Kazeon?Why Kazeon?
eDiscovery (core use)eDiscovery (core use) Index / Search Large Sets of DataIndex / Search Large Sets of Data View Indexed Data DirectlyView Indexed Data Directly Quick Implementation Quick Implementation CostCost
File Management / Record Management File Management / Record Management (additional use cases)(additional use cases) Reporting / Act Upon FilesReporting / Act Upon Files PotentialPotential to Identify Record Data to Identify Record Data

eDiscoveryeDiscovery




Basic File ManagementBasic File Management
ReportingReporting– Identify Types of Data on SharesIdentify Types of Data on Shares
Basic Crawl - Objective CriteriaBasic Crawl - Objective Criteria– File Type / ExtensionFile Type / Extension– Created / Modification DatesCreated / Modification Dates– Last Accessed DatesLast Accessed Dates– Owner / GroupsOwner / Groups
ActAct– Copy, Move, DeleteCopy, Move, Delete

Deep File ManagementDeep File Management
ReportingReporting– Identify Potential Risk AreasIdentify Potential Risk Areas
Deep Crawl – Document DataDeep Crawl – Document Data– SSN #’sSSN #’s– Credit Card #’s Credit Card #’s – Confidential or Privileged DesignationsConfidential or Privileged Designations
ActAct– Copy, Move, DeleteCopy, Move, Delete




Identify Records?Identify Records?
Programmatically Identify Data based on a Programmatically Identify Data based on a combination of factors:combination of factors:
Full text searching Full text searching – key words / phraseskey words / phrases
Identified FactorsIdentified Factors– SSN, Credit Card DataSSN, Credit Card Data
Basic MetadataBasic Metadata– Creation / Modification DatesCreation / Modification Dates– File Ownership / Group RightsFile Ownership / Group Rights

The EndThe End
Questions?Questions?