· 38 42 Corporate History 54 62 12B 12B OAIWA 10B 12B 22 10B Organization mNa-co.corn
TOR AND ATTACKS ON TOR Lecture 12b · TOR TOR stands for The Onion Router It enables anonymous...
Transcript of TOR AND ATTACKS ON TOR Lecture 12b · TOR TOR stands for The Onion Router It enables anonymous...

Slide title
In CAPITALS
50 pt
Slide subtitle
32 pt
Muhammad Rizwan Asghar
August 21, 2020
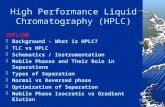
TOR AND ATTACKS ON TOR
Lecture 12b
COMPSCI 316
Cyber Security
Source of most slides: Northeastern University, USA

Top right
corner for
field
customer or
partner logotypes.
See Best practice
for example.
Slide title
40 pt
Slide subtitle
24 pt
Text
24 pt
5
20 pt
2
FOCUS OF THIS LECTURE
Understand TOR
Learn how TOR works
Discuss attacks on TOR

Top right
corner for
field
customer or
partner logotypes.
See Best practice
for example.
Slide title
40 pt
Slide subtitle
24 pt
Text
24 pt
5
20 pt
3
TOR
TOR stands for The Onion Router
It enables anonymous communication
It is free and open-source
Basic design: A mix network with
improvements
Mixes in TOR are known as Relays

Top right
corner for
field
customer or
partner logotypes.
See Best practice
for example.
Slide title
40 pt
Slide subtitle
24 pt
Text
24 pt
5
20 pt
4
IMPROVEMENTS IN TOR
Perfect forward secrecy
Introduces guards to improve source anonymity
Takes bandwidth into account when selecting relays
Offers hidden services
– Servers that are only accessible via TOR
– Hidden services provide 2-way anonymity

Top right
corner for
field
customer or
partner logotypes.
See Best practice
for example.
Slide title
40 pt
Slide subtitle
24 pt
Text
24 pt
5
20 pt
5
DEPLOYMENT AND STATS
Largest anonymity preserving service
– Publicly available since 2002
– Continues to be developed and improved
Currently, over 6000 TOR relays
– Source: https://metrics.torproject.org/networksize.html
All relays are run by volunteers
It is suspected that some are controlled by intelligence
agencies
Roughly, 500K-6M users
– Source: https://metrics.torproject.org/userstats-relay-country.html

Top right
corner for
field
customer or
partner logotypes.
See Best practice
for example.
Slide title
40 pt
Slide subtitle
24 pt
Text
24 pt
5
20 pt
6
TOR IN ACTION
Relays form an anonymous circuit
Traffic is protected with layers of encryption
Relay
<KP, KS>
<KP, KS>
<KP, KS>
<KP, KS>
<KP, KS>
<KP, KS>
<KP, KS>
<KP, KS>[KP , KP , KP]
Encrypted
Tunnels
Non-encrypted
data
E(KP , E(KP , E(KP , M))) = C

Top right
corner for
field
customer or
partner logotypes.
See Best practice
for example.
Slide title
40 pt
Slide subtitle
24 pt
Text
24 pt
5
20 pt
7
TOR CIRCUIT
TOR users can use any number of relays
Default configuration is 3
Entry/
Guard
Middle Exit

Top right
corner for
field
customer or
partner logotypes.
See Best practice
for example.
Slide title
40 pt
Slide subtitle
24 pt
Text
24 pt
5
20 pt
8
TOR: MALICIOUS ENTRY
Source known
Destination unknown
Entry/
Guard
Middle Exit

Top right
corner for
field
customer or
partner logotypes.
See Best practice
for example.
Slide title
40 pt
Slide subtitle
24 pt
Text
24 pt
5
20 pt
9
TOR: MALICIOUS RELAY
Source unknown
Destination unknown
Entry/
Guard
Middle Exit

Top right
corner for
field
customer or
partner logotypes.
See Best practice
for example.
Slide title
40 pt
Slide subtitle
24 pt
Text
24 pt
5
20 pt
10
TOR: MALICIOUS EXIT
Source unknown
Destination known
Entry/
Guard
Middle Exit

Top right
corner for
field
customer or
partner logotypes.
See Best practice
for example.
Slide title
40 pt
Slide subtitle
24 pt
Text
24 pt
5
20 pt
11
TOR: MALICIOUS ENTRY & EXIT
Source known
Destination known
Entry/
Guard
Middle Exit

Top right
corner for
field
customer or
partner logotypes.
See Best practice
for example.
Slide title
40 pt
Slide subtitle
24 pt
Text
24 pt
5
20 pt
12
PREDECESSOR ATTACK
Assumptions
– N total relays
– M of them are controlled by an attacker
Attacker goal: control the first and last relays
– M/N chance for first relay
– (M-1)/(N-1) chance for the last relay
– Roughly, (M/N)2 chance overall for a single circuit
However, clients periodically build new circuits
– Over time, the chances for the attacker to be in the correct
positions improves!

Top right
corner for
field
customer or
partner logotypes.
See Best practice
for example.
Slide title
40 pt
Slide subtitle
24 pt
Text
24 pt
5
20 pt
13
CIRCUIT LIFETIME
To mitigate the predecessor attack, one possibility is to
increase the circuit lifetime
Issues
– If you happen to choose the attacker as guard and exit, you
are screwed
– A single attacker in the circuit (as guard or exit) can still
perform statistical inference attacks
Bottom line: long lived circuits are not a solution
– TOR’s default circuit lifetime is 10 minutes

Top right
corner for
field
customer or
partner logotypes.
See Best practice
for example.
Slide title
40 pt
Slide subtitle
24 pt
Text
24 pt
5
20 pt
14
SELECTING RELAYS
How do clients locate TOR relays?
TOR Consensus File
– Hosted by trusted directory servers
– Lists all known relays
IP address, uptime, measured bandwidth, etc.
Not all relays are created equal
– Entry/guard and exit relays are specially labelled
TOR does not select relays randomly
– Chance of selection is proportional to bandwidth

Top right
corner for
field
customer or
partner logotypes.
See Best practice
for example.
Slide title
40 pt
Slide subtitle
24 pt
Text
24 pt
5
20 pt
15
SAMPLE QUESTION
Let us assume that we have a TOR circuit of
length 3. Which one of the following least affects
anonymity?
a) A malicious guard
b) A malicious middle node
c) A malicious exit node
d) Both a and c

Top right
corner for
field
customer or
partner logotypes.
See Best practice
for example.
Slide title
40 pt
Slide subtitle
24 pt
Text
24 pt
5
20 pt
16
SAMPLE QUESTION: ANSWER
Let us assume that we have a TOR circuit of
length 3. Which one of the following least affects
anonymity?
a) A malicious guard
b) A malicious middle node
c) A malicious exit node
d) Both a and c
Answer) b

Top right
corner for
field
customer or
partner logotypes.
See Best practice
for example.
Slide title
40 pt
Slide subtitle
24 pt
Text
24 pt
5
20 pt
17
TO BE CONTINUED
See the next lecture

Top right
corner for
field
customer or
partner logotypes.
See Best practice
for example.
Slide title
40 pt
Slide subtitle
24 pt
Text
24 pt
5
20 pt
18
Questions?
Thanks for your attention!