the threat - Control Design · 2013. 8. 20. · Price/Part Number CHECK OUT PRICES ON ETHERNET...
Transcript of the threat - Control Design · 2013. 8. 20. · Price/Part Number CHECK OUT PRICES ON ETHERNET...

Q3 • 2013
P9 WHERE ARE OUR WIRE WIZARDS?P17 FLASHBACK 2006: MEET THE MANAGED SWITCHESP20 NETWORK NOISE: KEEP IT DOWN
Effective network security has to keep its firewalls up,
but it must also track down and eliminate internal menaces
Indentifythe threat

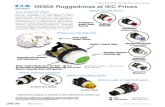
the #1 value in automation
Order Today, Ships Today!* See our Web site for details and restrictions. © Copyright 2013 AutomationDirect, Cumming, GA USA. All rights reserved. 1-800-633-0405
Manage your traffi cStride Ethernet Switches for Industrial Applications
Also
Available
Cat5e CablesConverters and
Modbus GatewaysEthernet Network
Support
Advanced Industrial Hardware• Unmanaged switches off er up to 9 ports in plastic or metal housings• Managed switches in metal cases support up to 16 ports• All RJ45 ports are auto-detecting, auto-crossover and auto-polarity• Redundant power inputs with surge and spike protection• SC (push-pull type) fi ber optic connector models, in addition to ST (slotted bayonet) style versions• SFP transceiver modules with LC fi ber connectors available
Real-time Performace• Store and forward wire speed switching - no delays• Full-duplex operation with fl ow control (no collisions!)• Auto crossover (MDI/MDIX) and auto polarity
True Industrial Design• Ethernet Isolation -1500 VRMS 1 minute• Wide operating temperature ranges• UL (CUL) listed and CE certifi ed• Hazardous locations rated for Class 1, Div. 2
$99 u.s.SE-SW5U
Starting at:
Our STRIDE family of industrial grade Ethernet switches and media converter is specifi cally builtfor industrial environments. Talk to your control system devices such as PLCs and HMIs reliably athigh speed. Install Stride switches and your Ethernet control network will maintain more consistent cycle times even underheavy I/O and data exchange. Our newest managed switches off er fast Ethernet and Gigabit options, as well as fi ber SFPtransceiver modules for select units. Managed switches off er security, redundancy and enhanced traffi c fi ltering.
Product DescriptionAutomationDirect
STRIDE
Price/Part Number
CHECK OUT PRICES ON ETHERNET SWITCHES
AutomationDirect prices are U.S. published prices from April 2013 Price List.Prices subject to change without notice.
5-port unmanaged Ethernet switch with (5) 10/100BaseT RJ45 Ethernet ports
8-port unmanaged Ethernet switch with (8) 10/100BaseT RJ45 Ethernet ports
16-port managed Ethernet switch with (16) 10/100BaseT RJ45 Ethernet ports
5-port managed Ethernet switch with (5) 10/100BaseT RJ45 Ethernet ports
$99.00 SE-SW5U
$174.00 SE-SW8U
$445.00 SE-SW5M
$1,290.00 SE-SW8MG-4P
$1,150.00 SE-SW16M
8-port managed Ethernet switch with (8) Gigabit RJ45 Ethernet ports and (4) combo SFP ports
$199 u.s.SE-SW5U-WT
Starting at:$445 u.s.SE-SW5M
Starting at:
Research, price, and buy at:www.automationdirect.com/
ethernet-switches

cover story
32013 • Q3 • IndustrIal networkIng
Industrial network generationsEthernet Keeps Extending Its
Reach, but There’s a Lot of Legacy
Connectivity Doing Important
Work, So They Still Need to Talk
Flashback 2006: a Hub Is not a router Is not a switchNetwork Performance Relies
on a Thorough Understanding
of the Capabilities of Hubs,
Routers, and Switches
by Mark laMendola
5 FIrst bIt
Counterfeits and Courage
6 Packets
Process Industry Ethernet
Nodes to Double by 2016
9 bus stoP
Where’s the Wizard for Wires?
20 ParIty cHeck
Network Noise
21 bandwIdtH
PoE Strives for Higher Power
25 Products
26 terMInator
The Shift to Industrial Networks
Features
coluMns & dePartMents
17
INDUSTRIAL NETWORKING is published four times annually to select subscribers of CONTROL and CONTROL DESIGN magazines by PUTMAN MEDIA INC. (also publishers of CHEMICAL
PROCESSING, FOOD PROCESSING, PHARMACEUTICAL MANUFACTURING and PLANT SERVICES), 555 W. Pierce Road, Suite 301, Itasca, IL. (Phone: 630/467-1300; Fax: 630/467-1124.) Address all
correspondence to Editorial and Executive Offices, same address. ©Putman Media 2013. All rights reserved. The contents of this publication may not be reproduced in whole or part without consent
of the copyright owner. INDUSTRIAL NETWORKING assumes no responsibility for validity of claims in items reported. Single copies $15.
Identify the threatEffective Network Security Has to Keep Its Firewalls Up,
but It Also Must Track Down and Eliminate Internal Menaces
by jIM Montague, executIve edItor
e v a l u a t e 1 0
r e s e a r c H 2 2
d e s I g n 1 7
volume xI, no. 3C O N T E N T S

netTAP: Cost-effective
fl exibility for traditional
Protocol Converter
applications.
netBRICK: Fortifi ed
netTAP capabilities
IP67-rated for harsh
environments.
Find out why Hilscher protocol converters are a great choice for your application. Visit our website at www.hilscher.com/usa or call 1.630.505.5301.©2013 Hilscher North America, Inc. All trademarks are the properties of their respective companies.
Supported Real-Time Ethernet Systems• EtherCAT• EtherNet/IP• POWERLINK• PROFINET• SERCOS III• Modbus TCPSupported Fieldbus Systems• CANopen• CC-Link (Slave)• DeviceNet• PROFIBUS
Hilscher ‘Single-Solution’ Gateways Bring Effi ciency to Any Environment.Gateways are the best way to interconnect today’s industrial networks. Hilscher’s netTAP and
netBRICK Protocol Converters support up to 1,000 combinations of Fieldbus, Ethernet and
serial protocols. Plus, our SYCON.net graphical confi guration tool lets you easily confi gure
and test your entire network and every device on it
Features: netTAP netBRICK
NEW Real-time Ethernet to Real-time Ethernet •
Fieldbus to Fieldbus •
Fieldbus to Serial RS232/422/485 • •
Real-Time-Ethernet to Fieldbus • •
Real-Time-Ethernet to Serial RS232/422/485 •
Master or Slave on either side • •
MMC/SD-card for confi guration storage •
Confi guration and Diagnostic via USB • •
IP20-rated, DIN Rail mounting •
IP67-rated enclosure •

52013 • Q3 • IndustrIal networkIng
DOWNTIME, LOST
REVENUE AND
POTENTIAL DAMAGE
OR INJURY CAUSED BY
A NETWORK SECURITY
BREACH CAN BE
ASSESSED IN THE SAME
WAY THAT FREQUENCY
AND SEVERITY ARE
CALCULATED FOR
SAFETY INCIDENTS.
F I R S T B I T
Whenever I get the chance to research
and report on network security, I’m inexplicably
reminded of a couple of old hardware stories. I
think this is because they help me understand
what’s going on with all the digital data lying
around on ethernet cables or through the air, and
perhaps how to help keep those networks and
their information secure.
he irst is my cover article, “Do You Know Who
Made Your valves?” (www.controlglobal.com/
valves) that appeared in control in november
2007. he story was about the growing precision
of counterfeit valves and other process control
equipment, and how to identify these increasingly
hard-to-recognize components. It was pretty
amazing. I learned that false process-control
components are accompanied by counterfeit
plates, marks, documentation, certiications
and other veriication, but some counterfeiters
even use phony sales representatives and set
up fake companies to distract and deceive their
victims. In fact, many fakes have become almost
indistinguishable from genuine products, using
rFID chips, laser etchings, holographic labels and
even castings that mimic the originals.
In this story, graham ogden, r&D director
of rotork (www.rotork.com), stated, “end users
shouldn’t buy a device or components unless
they’re sure where it came from, and they need
to understand the entire supply chain between
where a device was built and their plant. If you
can completely trace a product back to its
manufacturers, then you can be as sure as possible
that you have the genuine one you wanted.”
to combat modern counterfeiting, most process
control users buy products only from manufacturers
and distributors that are well-known to them,
though the lure of deals on eBay can be strong. as a
result, some purchasers measure wall thicknesses of
valves, retest device performance, and communicate
often with their suppliers. hey repeatedly conirm
logistics details, and track and trace shipments to
make sure no unauthorized disruptions or intrusions
occur in their supply chains.
It was this slightly obsessive, Fedex-style of
checking on shipments that I’ve long thought
would be a useful model for checking data
packets on industrial networks to help improve
their security. continual polling, data encryption,
restricted routing, security certiicates and
other basic security methods always seemed
very similar to the physical veriications used
to prevent counterfeits. so, I’ve been glad to
see many examples of this model coming to
pass, and then going even further with added
procedures for whitelisting authorized network
participants, conducting deep-packet inspections,
and performing several types of monitoring traic
for unusual activity. he main lesson is that it’s
important to maintain barriers, but it’s just as
crucial to examine internal communications, too.
Likewise, the second item that sticks in my
memory when I research security is my “Don’t
get Burned” (www.controlDesign.com/burned)
cover article in the May 2009 issue of control
Design. It was about the usual machine safety
precautions, but several sources also stressed
the need to perform more proactive, task-
based risk assessments (ras), and comply with
internationally harmonized safety standards at
the design stage and onward, instead of seeking to
protect operators and equipment after equipment
is already built.
In that story, c. Fred hayes, Packaging Machinery
Manufacturers Institute’s (www.pmmi.org)
standards and safety coordinator, stated, “When
the attorneys realized it would be a lot worse to
ship a machine to europe with safety functions
that it didn’t have in north america, they came to
understand that ras could be very useful.”
so, the best defense for machine safety has
shifted to having a good ra ofense. of course,
it’s no secret that safety principles are an excellent
way for engineers to understand and implement
security as well. his is because downtime, lost
revenue and potential damage or injury caused
by a network security breach can be assessed in
the same way that frequency and severity are
calculated for safety incidents. heir common goal
is reducing the probabilities of adverse events.
so, don’t sit on your hands and count on
security or safety by obscurity. carry out a
proactive ra for network security as well as for
process or machine safety. segment your network
with managed ethernet switches serving as
irewalls, but also implement some network and
data evaluation tools to ferret out unauthorized
traic and those counterfeit data packages.
Counterfeits and Courage
JIM MONTAGU EEXECUTIVE EDITOR

6 IndustrIal networkIng • Q3 • 2013
Process Industry Ethernet Nodes Double by 2016
In 2016, ethernet noDes In Process
industries will be nearly double what the level was
ending in 2011, according to a new study from
Ihs/IMs research entitled, “he World Market for
Industrial Ethernet and Fieldbus technologies –
2013 Edition.” It’s evident today that the technology
increasingly challenges ieldbus for leadership in the
industrial networking market.
Industrial Ethernet nodes in process industries
are projected to rise to 8.7 million units in 2016,
from 4.4 million in 2011. According to the study, this
means that industrial Ethernet will account for 45%
of networked nodes connected in process industries
in 2016, up from 39% in 2011. his growth will
come at the expense of ieldbus, itself anticipated to
expand by 51% during the same ive-year period.
“he process industry is renowned for being slow
to adopt new technology,” said tom Moore, analyst
for industrial Ethernet and ieldbus technologies at
Ihs. “however, in some key areas, industrial Ethernet
adoption is beginning to overtake ieldbus as the
mainstream networking technology.”
A good example within the process sector, reports
Moore, is safety. Although not always driven by
compulsory legislation, process safety systems—i.e.,
safety integrated systems—are updated regularly by
companies that want to ensure operator safety and
maximize line uptime. his shorter lifecycle means
that new technologies can break into the market more
quickly and are easier to implement, given greater
opportunity for refreshing the network upon reitting.
BETTER BE CONNECTED
“here is also a move to greater connectivity,” Moore
continued. “networking is becoming more of a
commodity, which means that remote monitoring
and control are more accessible. his is also true of
discrete automation.”
process components and systems, such as remote
terminal units and distributed control systems, are
already widely networked. Approximately 95% of
new-unit shipments are projected to be network
enabled in 2016, up from 90% in 2011. “he increase
is projected to be relatively slow, but is likely to
reach 100%,” Moore states. “network-enabling
products are now almost seen as a commodity and
are expected by the process industry. As networking
ability increases, the number of average nodes is also
increasing. his enables the use of more elaborate
networks and topologies.”
he use of industrial Ethernet is expected to
grow across industrial automation. Ihs projects
a compound annual growth rate (cAGr) of just
north of 14% to 2016 for new process-automation
networked nodes. he growth rate is well above
that for new ieldbus nodes, envisioned to be less
than 9% to 2016.
As adoption of industrial Ethernet increases
in process industries, it seems that an industrial
Ethernet-based network is a wise choice for those
looking to upgrade networking infrastructure
in the near future. While ieldbus adoption is
still growing, several advantages from industrial
Ethernet can be enjoyed, including uniication and
simpliication of networks that can result in lower
costs and greater up-time.
still, Moore recognizes, that ieldbus has
some advantages. hArt, a big part of process
industries, is able to overlay signals on 4-20 mA
wiring, a major advantage for those with existing
infrastructure. here is also the sizable legacy of
some ieldbus solutions, which means that a large
amount of machinery still uses older protocols.
Industrial Ethernet will have to overcome these
hurdles, but Ihs says it has largely replaced ieldbus
in many applications in the past 10-15 years.
reduced overheads, more accessible data and
decreased downtime are major advantages that
will drive adoption of industrial Ethernet in the
longer term.
Molex (www.molex.com) is
celebrating its 75th year in the
global electronics industry.
Established in 1938, Molex
developed interconnect
solutions for design problems
including simple PCB
connectors and stamped
circuitry, nylon plugs and
receptacles for color TVs.
Siemon (www.siemon.com), a
network infrastructure specialist,
celebrates 110 years serving
U.S.-based manufacturing. The
company’s global manufacturing
headquarters was among the
first manufacturers of its kind to
achieve ISO:9001 and ISO:14001
certification.
sercos int’l (sercos.org) held
its 11th sercos PlugFest at the
Institute for Control Engineering
of Machine Tools and
Manufacturing (ISW) in Stuttgart,
Germany. New sercos products
from competing vendors were
tested with each other to insure
interoperability. Products
included CNC, RC, motion
controls, PLCs, electrical and
pneumatic I/O systems, servo
drives and sensor technology.
The Monsanto chemical
manufacturing plant in
Muscatine, Iowa, was
selected in May by the HART
Communication Foundation
(www.hartcomm.org) as
recipient of the 2012 HART
Plant of the Year Award, which
showcases end users who
demonstrate ingenuity in the
use of HART Communication
for real-time operational
improvements.
PA C K E T S
bits & bytes
61.4%7,067 users
38.5%4,437 users
55.2%10,697 users
44.8%8,684 users
2011
2016
FieldBus
Ethernet
thE World MArkEt For
IndustrIAl EthErnEt & FIEldbus
Ethernet node growth comes largely from
fieldbus’ share, which itself also is growing.

PA C K E T S
thIs sprInG, thE FIEldbus FoundAtIon (FF, www.Fieldbus.
org) conducted the irst live demonstration of its Foundation
for remote operations Management (roM) technology at the
petrobras research and development facility (Cenpes) in rio de
Janeiro, brazil.
touting the “irst development of its kind” integrating remote
input/output (i/o), isa 100.11a, wirelesshart, wired hart, and
Foundation ieldbus h1 protocols into a single, standard data
management environment, Foundation for roM extends the
capabilities of Foundation ieldbus to wired and wireless devices
installed in some of the world’s harshest and most remote locations,
providing a uniied digital infrastructure for asset management in
applications ranging from tank farms and terminals to pipelines,
ofshore platforms, and even oeM skids.
whether operating on a wired or wireless hse backhaul network,
FF states that the Foundation for roM solution enables automation
end users to bring device data into the Foundation ieldbus
infrastructure, which provides a single source of data management,
diagnostics, alarms and alerts, data quality control, control-in-the-
ield capability and object-oriented block structure.
petrobras is said to be interested in specifying Foundation for roM
technology for “ambitious projects” it is undertaking in the upstream
and downstream hydrocarbon industry. he company has a record-
setting $224 billion capital spending plan through 2015 with most of
the investments targeted at the upstream sector in the pre-salt area
of the santos basin.
he petrobras Centro de pesquisas leopoldo américo Miguez
de Mello, also known as Cenpes, is the largest oil and gas research
center in the southern hemisphere. during the ield demonstration
and press day event, a series of tests were performed on a distillation
process pilot plant to evaluate the use of ieldbus-based roM devices
with wireless protocols for remote applications.
Miguel borges, senior equipment engineer at the Cenpes facility,
believes Foundation for
roM can be an enabling
technology for remote
applications on petrobras’
ofshore platforms.
“he Fieldbus
Foundation’s roM solution
is attractive to us, since
we want to gain access to
diagnostic information from
devices installed at our
remote sites,” borges said.
“For petrobras, the primary objective of this live demonstration was
to verify that we could access and use remotely, with Foundation
for roM, all the operational functionalities available locally.
another objective was to check the interoperability of roM
devices of diferent manufacturers over the backhaul. we found
this technology provides very easy and quick integration, and is
transparent to the user.”
during the functional testing, petrobras technicians accessed
device diagnostics in wireless devices, including device status.
integration of video was demonstrated through observation of
a control valve to determine if the valve was open or closed. a
temperature sensor for a hart temperature transmitter was also
pulled to show how the diagnostic alert would be visible in the same
context as a Foundation ieldbus h1 device.
supplier members sponsoring the Foundation for roM
demonstrations included apatechnologies, auMa, azbil,
beka associates, belden, bii, buerkert werke, emerson process
Management, endress+hauser, Festo brazil, Fuji electric, honeywell,
invensys operations Management, leoni-Kerpen, Magnetrol, Mtl,
pepperl+Fuchs, phoenix Contact, r. stahl, rotork, smar, softing,
stonel, turck, westlock, and Yokogawa electric.
Successful FF ROM Field Demo In Brazil
Quick Disconnectvs Hard-Wiring: What is the
ideal connectivity systemfor your industrial application? askTURCK.com
©2013 TURCK

Reliable Networks Sincere ServiceMoxa Inc. Tel: 1-888-669-2872 [email protected] www.moxa.com
Proven Reliability
in the Toughest
Applications
Industrial Wireless LAN & Cellular Solutions
Look for this white paper
on Google to learn more
Or download it directly at www.moxa.
com/industrial_wireless_whitepaper
Critical Elements
of Industrial-Grade
Wireless Devices
AWK SeriesIndustrial IEEE 802.11 Wireless AP/Bridge/Client
OnCell Series Industrial Cellular Solutions
EMS Protection
Galvanic Isolation Protection
Extreme Temperatures and Water Resistance
Shock & Vibration Protection
Resistance to External Interference

92013 • Q3 • IndustrIal networkIng
prEsEnt-day engineers have a lot of
excellent technology at their disposal. in many cases,
the complexities of an application can be reduced
through software “wizards” or pre-packaged scripts.
But, for much of our systems to function, we still
depend on reliable connection of copper conductor
to copper conductor, and for those connections
to be both secure and accurate. no amount of
wizardry can overcome issues arising from an
incorrect or intermittent electrical connection.
okay, i guess a network wizard might suggest
something like “check electrical connection,”
but it ofers little help to get it right the irst
time. Making reliable terminations still requires
craftsmanship and care in the actual (as opposed
to virtual) world.
terminations need to be made reliably under
all manner of adversity. standing still for an
hour or more in front of a ield junction box, an
electrician’s hands might not be the steadiest.
Maybe it’s not just the cold—the stanley Cup
playofs went to three overtimes last night, so it
could have been an especially early morning at the
hotel or campsite. repeatedly stripping jackets,
shields and insulation from conductors, properly
shortening signal and drain wires, applying heat
shrink, aixing a ferrule, and landing on the correct
one of hundreds of densely-packed terminals can
be a signiicant challenge even when we’re free of
aliction, environmental or otherwise.
he irst step to get a pair of wires landed
properly is to remove the jacket. foregoing
metal armored cable for the moment, the risk in
improperly removing the PvC or polymer jacket
is to nick or even sever one of the contained
conductors. if your electricians still use a pocket
knife or utility knife, there might be some
relatively inexpensive tools that can improve their
accuracy and productivity.
Most of the all-in-one tools for crimping rJ45
(ethernet) jacks have an appliance for measuring
and removing the proper length of insulation, but
i’ve used them with mixed results, i.e., i still end up
cutting or nicking some of the contained conductors.
it might be worth investing in a tool that’s speciically
for jacket removal. searching the internet, you can
ind capable oferings from manufacturers such as
Wiha and Xcelite that can be adjusted precisely for
a speciic cable thickness, which is useful if you’re
landing many pairs of the same speciication.
for the conductors, there’s another cadre of
capable specialty tools for stripping signal-gauge
(16 to 24 aWg) pairs for termination, again without
nicking any of the strands. he self-adjusting variety
of wire strippers have the potential to increase
eiciency and minimize errors and rework.
now that you’ve invested maybe $200 per
electrician, aiming for more reliable and consistent
wire preparation, what do you do with the neatly
stripped ends? if you’re using a cage-clamp block
like those made for many years by Wago, you might
think you’re done. But even with spring-clamps,
strands can get splayed and cause short circuits or
intermittent connections to adjacent terminals,
as well as weaken the termination you aimed to
make. he preemptive solution for preventing
the scourge of the stray strands is the “shoelace”
ferrule. its function is very similar to the aglets on
shoelaces—they keep unruly strands together.
While crimping a ferrule on each conductor adds
time to the job, and creates another opportunity
for quality and craftsmanship missteps, most
believers use them religiously. you can argue that
the problems avoided by more consistent and
precise terminations far outnumber those that
arise from an errant crimp job. a little training,
the right crimping tool, and using the proper
gauge ferrule for the conductor should keep
crimping problems to a minimum. and if you’re
using screw terminals, most of the experienced
installers i know highly recommend tightening to
spec with a torque screwdriver.
What about after the cable’s pulled, and the
backhoe chops it in two, hundreds of feet away?
Before you pull in all new wire, you might be able
to recover more quickly with a “Quickon” splicing
connector from Phoenix Contact. it’s bigger and
more expensive than a butt splice, but when
installed according to the instructions, it provides
an iP68 high-integrity repair. While it looks and
feels like a robust solution, users should check its
suitability for the particular area and hazard rating.
While we can’t click a wizard to simplify
terminations, we can take some steps to improve
the eiciency, accuracy, and overall quality of our
termination jobs. and you might even notice that
your small investment pays dividends in the care
and pride of the workforce.
Where’s the Wizard for Wires?
92013 • Q3 • IndustrIal networkIng
B U S S T O P
WHILE WE CAN’T CLICK
A WIZARD TO SIMPLIFY
TERMINATIONS, WE
CAN TAKE SOME STEPS
TO IMPROVE THE
EFFICIENCY, ACCURACY,
AND OVERALL QUALITY
OF OUR TERMINATION
JOBS. YOU MIGHT EVEN
NOTICE THAT YOUR
SMALL INVESTMENT
PAYS DIVIDENDS IN THE
CARE AND PRIDE OF
THE WORKFORCE.
JOHN [email protected]

EFFECTIVE NETWORK SECURITY HAS TO KEEP ITS FIREWALLS UP,
BUT IT ALSO MUST TRACK DOWN AND ELIMINATE INTERNAL MENACES
BY JIM MONTAGUE, EXECUTIVE EDITOR

112013 • Q3 • IndustrIal networkIng
lockInG thE door Is Good. bEInG AWAkE And AWArE Is bEttEr.
network access and security always has been about keeping out what
you don’t want to get in, but these days it’s also about inding and
eliminating what got in but shouldn’t be there.
so, while passwords, encrypted data, segmented networks, and
managed ethernet switches as irewalls are all essential, they’re just
the start of what it takes to make industrial networks and control
applications secure. in the past few years, some viruses, worms and
other malicious software have been modiied to circumvent the usual
barriers, exploit patching schedules, while others like stuxnet and similar
copycats can conduct man-in-the-middle attacks in which they pose as
authorized entities, while rewriting critical software behind the scenes.
“here’s no such thing as security-by-obscurity or truly air-gapped
systems,” says eric cosman, engineering consultant at dow chemical
(www.dow.com) and co-chair of the isa-99 industrial cybersecurity
committee (http://isa99.isa.org/isa99%20wiki/home.aspx). “even in
cases where a control system doesn’t have a network connection, it’s
possible to compromise the system by simply inserting an infected
UsB drive. here’s no substitute for understanding your systems, how
they’re conigured, and what your vulnerabilities are.”
consequently, all data and communications from the plant loor to
the business level must be monitored and inspected for unauthorized
and unusual activity. Luckily, increasingly capable and inexpensive
microprocessors, software and hardware components make these
network protection and detection devices usable by everyone. hese
security tools include it-based network sniing tools, deep packet
inspection software, and a variety of other devices and methods that
evaluate whether data and communications on a network is really
supposed to be there or not.
SECURE CONTAINER SHIFTING
For instance, europe container terminal (www.ect.nl) runs 265
driverless container vehicles, 127 storage cranes and 36 container
gantries 24/7/365 to move 7 million tons of goods per year through
the Port of rotterdam. however, all this automated loading and
unloading of 20-foot, equivalent-unit containers requires a huge
amount of logistical coordination and reliable hardwired, wireless and
iberoptic networking, especially between the cranes and agVs and
their network servers and redundant computing centers.
“he independent crane controls require protection from any
type of network interference from human error to denial-of-service
attacks,” says ingo hilgenkamp, product marketing manager for i/o
and networks at Phoenix contact electronics (www.phoenixcontact.
com). “however, this security mechanism must not prevent ect’s
operators from switching to backup radios if a malfunction occurs in
the iberoptic cables, which wind onto and of of large reels.”
to safeguard communications and make sure the cranes and agVs
precisely execute only authorized commands from operators, ect
implemented Phoenix contact’s mguard ethernet switches/irewalls,
security appliances and mechanical components, which are prewired,
conigured and din-rail mounted (Figure 1). Based on a hardened
embedded Linux operating system, mguard rs4000 switches have
four complementary security components, including bidirectional,
stateful inspection irewall; lexible network address translation (nat)
router; secure virtual private network (VPn) gateway; and optional
protection against malware using common internet ile system (ciFs)
integrity monitoring (ciM).
hese managed switches also act as media converters, and
pass signals from the iberoptic network to the ethernet network
and enable connection to the radio system if the iberoptic side
malfunctions. also, the switches and FL mguard security devices
connect over a cable protected by a special lock on the connector,
providing a layer of physical security. he connector requires a special
key to add or remove connections.
“Because all dispatchers and other users authenticate on the server,
the system maintains a high level of access security. he server also
administers permissions for individual users,” hilgenkamp explains. “on
the digital network, the ethernet switch ilters data traic, allowing
communication to take place solely between the server and the crane,
and drops all other data packets. From there, the systems checks data
transmission via universally applicable irewall rules, requiring only
minimal customization for the individual cranes. he strict separation
of input and output rules and their concise descriptions in table form
help simplify the coniguration, while the web-based gUi allows
adapting the rules to meet changes in the network structure.
“For example, the irewall rules ensure that the system doesn’t
inadvertently communicate with the wrong crane, and that the
controller continues performing its tasks without running into
network overload problems. hese rules also reliably eliminate the
risk of access and tampering by unauthorized persons or an external
service. he log ile can also help determine if communication
occurred with the cranes, and reconstruct the history of the iP
address used to determine where and when it was used. while
performing maintenance, the crane maintenance staf can activate
a special irewall rule set via the so-called ‘User Firewall,’ allowing
them to load updates or check the availability of replacement parts.
security certiicates installed on FL mguard ensure its coniguration
remains fully protected, and it also provides added security against
spooing and man-in-the-middle attacks.”
dan schafer, business development manager for networks and
security at Phoenix contact, reports, “here’s a lot of fear out there about
network security, but there’s also a lot more awareness and collaboration
between it and engineering on addressing security, though it’s a slow
evolution. so, while we’re mainly a components company, we started
our control industry solutions (cis) group about 18 months ago to pull
some of these issues together, such as deciding what controls, network
and other programs work best together, or what network architecture
and protection is most useful in a particular application.”

DEFENSE AT A DISTANCE
While some machines and production lines
retain traditional standalone postures, most are
networked within their facilities and increasingly
are tied to business-level networks and all their
accompanying risks and needs for security.
kMt Waterjet systems (www.kmtwaterjet.
com) in baxter springs, kansas, wanted
to improve its global service by centrally
diagnosing the operating status of all its
streamline ultra-high-pressure pumps, and
managing and performing service-related
control tasks via a secure dial-in and i rewalled
internet connection.
as a result, KMt integrated at least three
ethernet links on each high-pressure pump
to connect to its hMi, PLc and local i rewall,
which performs a dual function. it prevents
unauthorized access to the pumps locally by
i ltering for internet protocol (iP) or media
access control (Mac) addresses, and converts
iP addresses with nat technology because each
high-pressure pump worldwide must have the
same iP address on the hMi and PLc for service
reasons. h e company’s network topology for
its pumps include eagle mguard switches with
VPn capability and spider 5tX eec connection
components from hirschmann, a division of
Belden (www.belden.com).
to reduce the need for trained technicians to
coni gure iP addresses locally, KMt also adopted
a UsB auto-coni guration adapter (aca) for
redundant storage of the i rewall parameters.
however, to allow secure dial-up connections to
the pumps, a second i rewall system with a VPn
option is incorporated in the customer’s control
center. h is i rewall is identical to the local
i rewall, and is also equipped with another aca.
h is ensures a consistent service concept and
high security, even for access via the internet.
GOOD ADVICE, BETTER PRACTICES
while improving an application and network’s
security can seem overwhelming and
unapproachable at i rst, it’s actually very similar
to most control and automation projects.
“You have to own your network,” says
Mariam gallegos, product specialist for
networks and security at Phoenix contact.
“You have to know what you have, and then
you have to i nd out all the access points and
vulnerabilities in your network, and know where
it’s weak and where someone might get in.”
once inventory and awareness are achieved,
gallegos adds that Layer 3 managed ethernet
switches can be deployed to check iP and
Mac addresses, dei ne communication
routing, and perform nat tasks to provide
protection in a segmented network.
similarly, the U.s. industrial control systems-
cyber emergency response team (https://ics-
cert.us-cert.gov) recommends several strategies
for segmenting a company’s manufacturing
and business networks, and protecting them
from external threats. one of these consists of
a digital demilitarized zone (dMZ) between
a corporate local area network (Lan) and a
control system Lan adds a layer of protection
because no communication takes place directly
from one Lan to the other (Figure 2).+1-661-716-5100
www.prosoft-technology.com
Connect Protocolscon•nect [k' nekt] pro•to•cols ['prōt e kôls]
Deinition
ProSoft Technology Where Automation Connects
PROFIBUS
Siemens Industrial EthernetASCII
BAC
net
Modbus
Mo
db
us
TC
P
Modbus
DNP3PROFIBUS
ASCII
DF1
IEC-60870-104
HARTEtherNet/IPAllen-Bradley Remote I/O
DNP3
PROFIBUS
Modbus Plus
IEC-61850 IEC-61850
Siemens Industrial Ethernet
LonWorks
DF1
DF1
MetasysN2
DeviceNet
ASC
II
Data Highway Plus
HART
MetasysN2
Mo
db
us Modbus TCP
Modbus Plus
DN
P3
ASC
II
LonWorks
ASCII
EtherNet/IPMetasysN2BACnet
Modbus TCPIEC-60870-104
Siem
ens
Ind
ust
rial
Eth
ern
et
HARTPROFIBUS
Modbus TCP
A S I A PA C I F I C | A F R I C A | E U R O P E | M I D D L E E A S T | L AT I N A M E R I C A | N O R T H A M E R I C A

besides segmenting and irewalls, defense-in-
depth must include network traic monitoring
and malware scans of internal communications,
says Mike Baldi, chief cybersecurity architect
at Honeywell Process Solutions (www.
honeywellprocess.com). “Many of these tools,
like Network Intrusion Prevention Systems
(NIPS) or Network Intrusion Detection Systems
(NIDS) and deep-packet inspection irewalls,
come from the IT side, so we’re adapting them
for process control networks. he good news is
that scanning and benchmarking are easier for
process control because we already have many
rules about who can talk to whom, and it will be
simpler for us to detect traic deviations.”
COLLABORATION KEY TO SECURITY
Surprisingly, one of the main tools that veteran
end users employ to improve their network
security is simple human collaboration.
“From the beginning of a project, we put
in a cross-functional team to handle network
security,” said Tom Moroney, manager of
deepwater technology deployment and
geosciences at Shell Exploration & Production
(www.shell.com) at Honeywell Users Group
2013 this past June. “his team includes
both our IT division and Shell’s leadership.
We’re migrating our Well Reservoir Facility
Management (WRFM) program to an
interrelated, four-pillar structure, which
includes understanding assets; knowing the
risks and uncertainties of each; deciding how
they need to be instrumented; and how to
capture, store, analyze and consume data
from them. his means all kinds of tools and
software have to it together and operate
securely, and so we must be able to talk to our
IT and our global architecture departments,
and then look for suggestions from suppliers
like Honeywell.”
Hot-swappableSmart Plug & Play Operation
Copper & fiber
Modular
All Gigabit
24 ports
better. together.
Visit better.redlion.net to learn how our industrial automation and industrial
networking products work together to connect. monitor. control.
©2013 Red Lion Controls Inc. All Rights Reserved. +1 (717) 767-6511 I [email protected] I better.redlion.net
+Introducing the ultimate in
network fl exibility—Red Lion’s
new NT24k modular GigE switch
series from N-Tron, the pioneers
in industrial Ethernet. With all
Gigabit and versatile connectivity
options, the NT24k has
confi guration fl exibility to meet
all of your industrial networking
requirements.
> All Gigabit Modular Design
> Up to 24 Port Connections
> Robust Remote Monitoring
> Smart Plug & Play Operation
> DIN Rail & Rackmount Options
> Extreme EnvironmentsNew NT24k Managed Gigabit Ethernet Switch
MADE IN
THE USA
ProtectIng Port oPeratIons
Figure1: An army of cranes and automatic guided vehicles (AGVs) uses hardwired,
fiberoptic and wireless networks protected by managed Ethernet switches/firewalls,
VPNs and hardware to securely coordinate container unloading and loading, and
move 7 million tons of cargo per year at the Port of Rotterdam.
EC
T a
nd
Ph
oe
nix
Co
nta
ct

14 IndustrIal networkIng • Q3 • 2013
shell has six loating and four ixed structures in the Gulf of Mexico
and two loating, production, storage and oloading (Fpso) vessels in
brazil, and together they operate about 200 wells that produce 400,000
to 600,000 bpd. “hey also run abut 20,000 osIsoft pI tags or sensing and
measurement points, which generate about 410 million data points per
day, covering everything from complex well geometries to oil reservoir
management and beyond,” Moroney explained “We wouldn’t be able to
process all that data if we couldn’t pay attention to integrating it securely.”
similarly, dow’s cosman adds, “I would describe our cybersecurity
program as a collaborative efort between our It and operations
groups, involving expertise and experience from both areas. detailed
knowledge of information security comes largely from It, while the
knowledge and experience of the speciic needs and constraints
associated with manufacturing facilities comes from operations. In my
opinion, this type of partnership or collaboration is an essential irst
step in adequately addressing the security of plant level systems.”
With such a working partnership in place, cosman says the next
step is to have an accurate and current inventory of the systems to
be protected, followed by a strategy for organizing these systems
into a documented architecture based on principles like network
segmentation, defense in depth and least privilege. detailed
information about what is required here is provided in the IsA-62443
standards [see “cooperation on cybersecurity standards” sidebar].
“We also maintain relationships with and participate in selected
external parties, such as standards development organizations
like IsA, government agencies such as the u.s. dept. of homeland
security, and trade associations for information sharing and
benchmarking,” cosman adds. “he nature and degree of this type
of external engagement has to be driven by business interests and is
often constrained by resource availability.”
UPCOMING, EVERYDAY SECURITY
security has become less dramatic and grown closer to the routine
safety and maintenance tasks that operators and technicians carry
out every day, and that’s because many users and developers’
understanding of security evolved from putting up a set-and-forget
barrier to ongoing inspections of their networks, traic and data.
“We see network routers and irewalls being combined with
integrated switching functions and vice versa, and this convergence
SEVEN STEPS TO SECURITY
One of the most thorough lists about how to achieve network
security is “Seven Steps to ICS and SCADA Security” by Eric
Byres, PE, CTO and engineering vice president of Tofino
Security (www.tofinosecurity.com), a subsidiary of Belden, and
John Cusimano, security director at exida Consulting (www.
exida.com). Their whitepaper is at http://web.tofinosecurity.
com/download-7-steps. The steps are:
• Assess Existing Systems. Perform a high-level risk assessment to quantify and rank dangerous risks. This will show users
how to prioritize their security funding and projects.
• Document Policies and Procedures. Develop industrial control system (ICS)-specific documents that describe your company
policy, standards and procedures for control system security.
They should refer back to corporate IT security documents.
Separate ICS security documents will help those responsible
for ICS security to understand their security-related
expectations and responsibilities. Also, become familiar with
security regulations and standards for your industry.
• Train Personnel and Contractors. After documenting policies and procedures, make sure senior management supports
them, and that staff is aware, trained and follows them.
• Segment the Control System Network. Network segmentation into zones connected by firewalled conduits is the most
important tactical step you can take to improve the security
of your industrial automation system.
• Control Access to the System. Once your network is partitioned, the next step is to control access to the assets
in those zones with physical and logical controls. Physical
access controls include locked cabinets, locked doors, fences,
etc. Likewise, logical access should include multiple levels of
control and authentication.
• Harden the Components. This means locking down functions of the components in your system to prevent unauthorized
access or changes, remove unnecessary functions or features,
patch any known vulnerabilities, and set configurable
options to their most secure settings. This is especially
important in modern control systems which use lots of
commercial off-the-shelf technology.
• Monitor and Maintain System Security. Maintain vigilance by monitoring and maintaining security throughout the lifecycle
of your system. This involves updating antivirus signatures
and installing security patches on Windows servers. It also
involves monitoring your system for suspicious activity.
Finally, periodically test and assess your system. Assessments
involve audits to verify the system is still configured for
optimal security as well as updating security controls to the
latest standards and best practices. It’s vital to remember that
effective ICS and SCADA security isn’t a one-time project. It’s an
ongoing, iterative process, so you’ll need to repeat the seven
steps and update materials and measures as systems, people,
business objectives and threats change.
“YOU HAVE TO OWN YOUR NETWORK. YOU
HAVE TO KNOW WHAT YOU HAVE, AND THEN
YOU HAVE TO FIND OUT ALL THE ACCESS POINTS
AND VULNERABILITIES IN YOUR NETWORK,
AND KNOW WHERE IT’S WEAK AND WHERE
SOMEONE MIGHT GET IN.”

There used to be dozens of different government, trade organization
and corporate efforts on cybersecurity, but most of them were
unaware of the others and what they were doing. Now, most
are organized around the U.S. Dept. of Homeland Security and
its Industrial Control Systems-Cyber Emergency Response Team
(https://ics-cert.us-cert.gov) with help from the National Institute of
Standards and Technology (www.nist.gov). Likewise, several standards
efforts are underway to establish uniform best practices by the
International Society of Automation (www.isa.org), the International
Electrotechnical Commission (www.iec.ch) and other groups.
“In the U.S., perhaps the most significant current activity is the
development of a critical infrastructure Cybersecurity Framework in
partial response to President Obama’s executive order in February,”
says Eric Cosman, engineering consultant at Dow Chemical (www.
dow.com) and co-chair of the ISA-99 cybersecurity committee (http://
isa99.isa.org/ISA99%20Wiki/Home.aspx). “The framework is expected
to be submitted to the president later this year, and made generally
available in early 2014.” More information about the framework is at
NIST’s web page at www.nist.gov/itl/cyberframework.cfm.
“In the area of standards and certification, work continues
on developing standards in the ISA/IEC 62443 series, as well as
certification systems via the ISA Security Compliance Institute’s (http://
ISCI.org) ISASecure effort,” Cosman adds. “ISA-62443-3-3 standard,
‘System Security Requirements and Security Levels,’ was approved by
ISA and will be issued soon; the IEC version is being translated.”
Cosman says there have been formal liaison relationships
between various cybersecurity groups and committees for some
time. “For example, there’s been cooperation between the ISA-99
committee and IEC TC 65 WG10 in developing the ISA/IEC 62443
standards,” he says. “ISA and the Automation Federation (www.
automationfederation.org) also have several people contributing
to development of the NIST framework. Recently, ICS-CERT Joint
Working Group (ICSJWG) formed a standards subgroup to facilitate
communications and cooperation between the private and public
sectors, particularly for reviewing and promoting the ISA/IEC 62443
standards and the NIST Special Publication SP800-82, which will be
revised this year. Though it might not seem so to the casual observer,
there is and has been considerable cooperation and collaboration
between many groups and committees working in this area.”
Detailed information about what constitutes an effective
cybersecurity management system for control systems is available
via a combination of ISO/IEC 27001 and ISA-62443-2-1, which
is available as a draft at http://isa99.isa.org/Documents/Drafts/
ISA-62443-2-1-WD.pdf. “However, both of these are detailed
standards documents, and may not be suitable for the purpose of
getting general guidance,” Cosman explains. Depending on staff
available, it may be necessary to hire a consultant to help develop a
comprehensive program. “ Cosman would direct individual owner/
operators to their automation system suppliers. With few exceptions,
he says, all major suppliers have stepped up.”
COOPERATION ON CYBERSECURITY STANDARDS
Process Controllers Visual Management HMIs & Panel
Meters
Protocol
ConversionEthernet Switches & Wireless Devices
better. together.
Red Lion has been delivering award-winning industrial automation products to customers worldwide for over forty years. Now
these innovative products are even better when paired with industrial networking from N-Tron and Sixnet, the pioneers in Ethernet
and cellular M2M solutions for industrial environments.
Visit better.redlion.net to learn how our industrial automation and
networking products work together to connect. monitor. control.
©2013 Red Lion Controls Inc. All Rights Reserved. +1 (717) 767-6511 I [email protected] I better.redlion.net
+

indicates security will be built into more
control products in the future,” Gallegos
says. “In fact, antivirus, anti-malware
and whitelisting capabilities are already
showing up in some plcs and I/o devices
on networks. For example, we already do
cIM scans of industrial computers, not
necessarily to i nd viruses, but just to
build a baseline database. h is can help
us look for deviations in the i le system
later, and then set up alerts, which can
be a big help in improving security and
coni guration management in the future.
For instance, having a test, identii cation
and alert for altered executable i les would
have identii ed stuxnet or other zero-day
exploits before they were eventually found
by antivirus programs.”
cosman adds, “i can’t predict the future,
but the trends i see include an increasing
level of integration of security technology
into industrial control systems out of the
box. h is trend has been in place for a few
years now, and i expect it will continue. h e
other trend i’ve observed is an increasing
shift from network security to a broader
view of system security—embracing the
people, process and technology aspects of
the overall automation system, including
functions from manufacturing operations
down to and including safety systems and
machine controls. i also believe that as the
various standards and practices continue to
mature, we’ll be able to demonstrate that the
landscape is not as confusing as it appears.
again, much if not most of the standards
related material is converging on the iec
62443 series.”
RTU/PLC/DCS
Controller units
and field devices
Control
system
firewall
Data
DMZ
Business/
corporate
networkProduction
control
system
network 2
ICCP
PEERS
Corporate
firewall
Internet
keePIng lans aPart
Figure 2: A digital demilitarized zone (DMZ) between a corporate local area network
(LAN) and a control system LAN adds a layer of protection because no communication
takes place directly from one LAN to the other, according to the U.S. Industrial Control
Systems-Cyber Emergency Response Team.
ICS
-CE
RT

IN ETHERNET NETWORKS, THE THREE MAIN HARDWARE
components besides cable and connectors are hubs, routers, and
switches. how and why you select and implement each of them
will determine the functionality, reliability, security, and flexibility
of your industrial network. let’s look at these devices, starting
with the simplest of the three.
HUBS IN THE NETWORK UNIVERSE
A hub acts much like those three-way plugs you might use in your
home’s electrical outlets. hubs simply connect one pathway to
another. his capability can actually complicate things, reports the
engineering staf at flg networking services (www.lgnetworking.
com) in overland Park, Kan. FLg provides network design and
security services to industries that include polymer processing, paper
goods, and printing. “when you put multiple devices on a cable
without some kind of traic control, you get collisions,” says Fred
granville, FLg’s principal. “hubs assume every device is on the same iP
subnet.” in short, a hub doesn’t diferentiate between the data paths
it’s connecting; it just connects them.
“We generally don’t recommend hubs, but they still have a place,”
advises dan Parker, project applications engineer at Curry Controls
(www.currycontrols.com) in lakeland, fla. “for ieldbuses, the
hub provides an essential function for impedance matching and
multiple connections. And, where a customer requires a simple
data connection, we use simple, low-cost hubs to provide it.” Curry
provides design, engineering, integration, installation, and service for
industrial and municipal process control and radio telemetry systems.
So, hubs are useful when you don’t need to diferentiate between
the data paths you’re connecting, and just want low speed and no
processing in that connection. “We develop our own control systems
and use ethernet in special ways that are internal to our system, so
we use hubs to monitor traic,” adds ernesto colon, vice president
of turbine Diagnostic services (www.turbinedoctor.com) in odessa,
Fla, a ield service company servicing power-generation equipment,
manufacturing turbine, and balance-of-plant (BOP) controls for
various industries. “We also use hubs due to cost and lower latencies.”
In short, because hubs have limited capabilities, the heavy lifting in
networking is left to the routers and switches.
ROUTERS PROVIDE DIRECTION
Granville explains that routers are critical for networking. “A router
provides a connection from one IP subnet to another, allowing you to
talk between IP networks and subnets,” he says “Routers interconnect
local area networks (LANs) and virtual LAN (VLAN) segments
in a switched environment. However, a router doesn’t propagate
broadcasts. Switches do.”
NETWORK PERFORMANCE RELIES ON A THOROUGH UNDERSTANDING
OF THE CAPABILITIES OF HUBS, ROUTERS AND SWITCHES
a Hub Is not a router Is not a switch
BY MARK LAMENDOLA
FIgure 1: coMPlex MacHIne = coMPlex network
An industrial communications network can be as complex and
multi-layered as the production machine system itself, in this
case, a paper-making system.
CO
NT
EM
PO
RA
RY
CO
NT
RO
LS
HUBS ARE USEFUL WHEN YOU DON’T
NEED TO DIFFERENTIATE BETWEEN THE
DATA PATHS YOU’RE CONNECTING,
AND JUST WANT LOW SPEED AND
NO PROCESSING IN THAT CONNECTION.
Last year, we celebrated our 10th
anniversary by republishing some
of the more ‘timeless’ content we’d produced since 2002. hey were
well-received, so we decided to do it again from time to time. Here’s
one from Summer 2006 that reminds us, as Ethernet was emerging,
how switches looked to be a key to the performance and reliability
that industrial users would need.
INDUSTRIAL NETWORKING
SUMMER 2013
17D E S I G N

INDUSTRIAL NETWORKING
SUMMER 2013
18 D E S I G N
routers also solve some otherwise intractable security problems.
“one customer wanted a webcam, but didn’t want to open its
network to an outside connection,” says r. Andrew bowman, pE,
vice president for engineering at sitesecure (www.sitesecure.com)
in sanford, Fla. “We plugged a router into their network. he router
became the device with the Ip address.” sitesecure provides security
and safety solutions, including design, installation and startup.
parker also has seen many misapplications of routers. “usually,
these result from the great divide between the plant-floor,
industrial types and the information technology types,” he
explains. “the It folks want every device on the network to be
dns-enabled, so they have control over the device. the plant-
floor folks want every device to have a fixed address, so it can be
communicated with simply and easily on a regular, repeatable
basis, as with, for example, plc-to-plc communications.”
parker believes the problem goes beyond turf battles. “routers
often operate as dns servers,” he continues. “In the typical scenario,
the plant goes into operation and everything is ine until there’s a
power failure. hen, as the power-up order changes, each device
is re-assigned an address. his drives the control system crazy, and
production time is lost while it’s all sorted out.”
SWITCHES MAKE IT HAPPEN
While routers connect networks together, switches actually run the
network. his is when expertise-driven functions such as product
selection, system design and installation can quickly become
complicated (Figure 1).
so, the switch is the real workhorse of industrial networks, as
Granville hinted, but it needs to be industrial grade. “Industrial
switches have several advantages over their commercial
counterparts,” says roger McFall, control systems project manager
at A&E Engineering (www.aeengr.com) in Greer, s.c., which
provides automation and information services from design
through integration. “compact size with dIn-rail mounting is
one advantage. low port density is another because many plant
applications have a small number of Ethernet devices per panel,
but have many panels.”
steve byars, also a control systems project manager with
A&E, adds, “he ruggedized, higher temperature, and vibration
speciications of industrial switches (Figure 2) are critical in harsh
industrial environments.”
All of these networking pros agree that you have to use industrial
switches, not consumer-grade ones. he next decision about switches
is whether to choose managed or unmanaged.
“If switches, cables, or any other connected devices experience
communication failures, a managed switch can alert you,” says Wright
sullivan, A&E’s vice president. “With an unmanaged switch, you ind
the problem only after equipment has failed, so you’re lying blind.”
granville adds, “as a rule of thumb, i don’t recommend using
unmanaged switches in an enterprise. an unmanaged switch
provides dedicated bandwidth per port, but there’s so much more
you can and should do with a managed switch. troubleshooting,
for example, is a huge issue.”
a&e’s Byars agrees. “Most managed switches come with a web
browser tool for monitoring your entire network down to the port
level,” he adds. “For any network larger than a handful of switches, this
is a critical tool for troubleshooting.”
Parker says many of his customers require managed switches for
any ethernet networking project because they provide eicient
delivery of network data packets.
it gets better. “we completed a project for a water company,
connecting six rtU cabinets via managed switches,” says Mike
nicholas, senior project manager for emerson Process Management’s
Bristol division (www.bristolbabcock.com) in watertown, conn.,
which supplies and commissions remote automation units for
process and other industries. “he switches allowed 10/100 Mbps
Ethernet connectivity to all rtu cabinets. Fiberoptic cable extended
the connection distance far beyond the 100 m limitation of 10baset
cable. he self-healing ring switches ensured that bandwidth was
maintained for all connections, and provided network reliability with
dual, self-healing communication paths.”
Managed switches also help avoid the tyranny of numbers that results
from setting up separate physical networks for each department, such
as It versus plant systems. “If you’re sharing infrastructure with other
departments, you need to manage your switches with a virtual network,”
FIgure 2: Heat be gone
The heat-sink capability inside this managed switch allows it to
perform reliably in high-temperature environments.
GA
RR
ET
CO
M
Fred Granville, principal of FLG Networking Services, identifies
seven things users can do only with a managed switch:
1. Provide redundant connections between a pair of switches,
and have both carry traic
2. see into traic (port errors, volume, type of traic)
3. Phone home
4. Create virtual local area networks (Vlans)
5. do Vlan trunking
6. Implement quality of service (Qos)
7. Prioritize traic
Managed swItcHes only

19INDUSTRIAL NETWORKING
SUMMER 2013
warns bowman. “You have to subdivide physical
switches into VlAns. It’s a matter of assigning
speciic traic by function to speciic ports, so
you have no crosstalk between functions.”
With separate networks, the accumulation
of multiple device footprints makes it
diicult to have a space-eicient installation
(Figure 3). Bowman identiied two other
problems. “Deploying physically separate
networks can be very expensive if there
isn’t suicient cable to support a second
network, and it adds to the infrastructure the
IT department must support,” he cautions.
“Managed switches provide the answer to
both of those downsides.”
here are more reasons to use managed
switches. “Intelligent switching gives you control
over the network and control over the device,”
says David LaBree, CTO of Prime Telecom
(www.primeusa.net) in Tampa, Fla., which
provides network engineering, integration,
and maintenance services to municipal and
ISP networks. “his speeds up troubleshooting
immensely. You can logically go through the
troubleshooting process, rather than physically
going into the ield. A device might seem to be
malfunctioning, but the problem could be the
communication to the device.”
In addition, the push since 9/11 for security
enhancements has required Prime’s installed
network to allow for additional devices such
as IP-enabled security cameras, VOIP audio
capability, and badge/card reader systems,
says Parker. “We can set up a VPN within a
managed switch, and allow for segregation
of the industrial control equipment and the
security systems,” he adds.
Bowman says many layers of security come
with more sophisticated hardware.
COMPLETE THE THOUGHT PROCESS
While correct hardware selection is critical,
it’s not the end of the story. “here are
tradeofs,” points out Bowman. “You have
to plan your system. Simply adding things
as you go can make implementation more
diicult and costly.”
Existing standards help with this planning.
“By using standards such as Rapid-Spanning,
Tree Protocol (RSTP) for fault tolerance,
designers can increase network availability and
reliability without resorting to proprietary or
complicated techniques,” says Sullivan.
Byars agrees with this premise. “By avoiding
proprietary protocols, you need not commit
to one vendor for your switches,” he adds.
“Existing networking standards cover most
of the functions needed when designing an
Ethernet network for the plant loor.”
What standards are Byars and Sullivan
talking about? “Hubs and switches can carry
many types of protocols,” says Granville.
“hey aren’t tied to TCP/IP, but that’s pretty
much the standard protocol today.”
Two other often-overlooked standards that
can be critical are VLANs and Quality of Service
(QoS). “hese tools allow you to separate
mission-critical control traic from lower-
priority traic to ensure that critical messages
go through,” says McFall. “hese capabilities are
found only in managed switches that support
the 802.1p and 802.1q standards.”
Of course, you need to connect the devices
correctly. “Don’t neglect correct cable selection
or overlook cable routing,” warns Colon. “We
even color code the cables by function.”
As Ethernet devices proliferate, the
plant-loor network becomes an even more
mission-critical infrastructure. “Proper use
of managed switches, IT standards, and
a well-designed network are the keys to
reliable manufacturing in the Ethernet era,”
concludes Sullivan.
COMMON MISTAKES,
UNCOMMON PROBLEMS
Another reality is that sometimes users
get networking wrong, and misapply
redundancy, for example. “One project
required redundancy on network switches
with fiberoptic capability,” Parker says.
“The consulting firm provided the
fiberoptic backbone design, but called for
single, multi-fiber cables to each switch
with redundant connectivity provided
by using differing pairs of fiber. We
recommended improving this by using
separate cables and paths, which resulted
in half of the redundant backbone being
run down the left side of the production
line and the other half run down the
right side.” This turned out to be a smart
recommendation.
“Each redundant path had spurs to each
item of equipment,” adds Parker. “he cost
of this enhancement seemed excessive to
the end user until a plant incident rendered
the right side of the production line cabling
unusable. he left side of the line network
continued to operate and allowed for a safe,
fully automatic shutdown. his functionality
can be implemented only with redundant-
ring-enabled network switches.”
Unfortunately, Colon says, security and
reliability often lose out. “Customers hear the
pitches about wireless and just start installing
equipment,” he states. “hey don’t realize
they’re opening their networks to hacking
and possible sabotage.”
Granville couldn’t agree more, saying,
“Implementing wireless correctly requires
extensive expertise.”
Bad communication during planning
is, perhaps, the biggest mistake. “he IT
department and the plant loor must
communicate up front,” Parker insists. “his
precludes a lot of heartache and sorrow
during the implementation phase of a
project. he IT folks must understand what
the plant loor needs and vice-versa.”
In 2006, Mark lamendola was a freelance writer and
frequent contributor to CONTROL DESIGN with many
years of experience working in and writing about
industrial automation issues.
FIgure 3: HIgH PerForMance In
sMall sPaces
This panel is equipped with PLCs (right),
an access point (top left), and directly
below the access point are industrial
Ethernet switches with fiberoptic
connectivity.
CU
RR
Y C
ON
TR
OL
S

Network Noise
thE bAnE oF All nEtWorks Is “noIsE.”
this is especially true for wireless networks as they
do not have a conductor to guide and contain
the signal. normally, cables also are shielded and
twisted to reduce susceptibility to external factors.
A cisco whitepaper, “20 Myths of Wi-Fi
Interference: dispel Myths to Gain high-performing
and reliable Wireless,” includes statistics that
technical support engineers at a major Wi-Fi
infrastructure vendor reported to cisco. In a service
call to a major customer, they found almost “20
sources of interference, contributing to over 50%
of the problems on the customer’s Wi-Fi network,”
and “one out of every three Wi-Fi problems our
service technicians get called out for is related
to interference.” In addition, a recent survey
of 300 customers found that “troubleshooting
interference won ‘top honors’ as the biggest
challenge in managing a Wi-Fi network.”
In the whitepaper, Jupiter research reports that
67% of all residential Wi-Fi problems are linked to
interferring devices such as cordless phones, baby
monitors and microwave ovens. he correlation
is likely valid in an industrial setting because many
other types of devices also emit in the unlicensed
band, including microwave devices, cordless
and cellular phones, bluetooth devices, wireless
video cameras, Zigbee devices, luorescent lights,
wiMaX, etc. even bad electrical connections can
cause broad rf spectrum emissions. Compounding
the interference problem is that this noise is
often intermittent. in addition, the interference
might occur only at certain times of day, which
is easier to determine than truly random events,
such as larger vehicles occasionally blocking the
transmission path.
fortunately, the solution to noise problems can
be addressed by following the simple physics of
wireless network design.
Typical issues to be aware of when designing
for wireless in industrial settings include fresnel
efect, difraction, scattering, relection, moisture/
humidity, trees (leaves or no leaves), frequency, etc.
Difraction occurs when the radio path between
the transmitter and receiver is obstructed by a
surface that has sharp irregularities/edges and
isn’t too close to either antenna. he result is that
the fresnel zone acts to reproduce secondary
“shadow” fresnel wavelets that, although severally
limited in signal strength to the original, allow
waves to bend around the obstacle, even when
line-of-sight does not exist. higher frequencies
bend less than lower frequencies.
a relected wave can increase or decrease the
signal level at the receiver. in many cases, the
received signal level tends to be very unstable.
his is commonly referred to as multipath fading.
he throughput (speed) of a wireless system is
inversely proportional to the distance between the
transmitter and the receiver. herefore, everything
being equal, the closer a wireless client is to a
transmitter, the greater the throughput. however,
when noise causes the network to retransmit
packets, distance has a double whammy of more
“path” through the contaminating environment.
some networks also are less susceptible to noise
than others. ieee 802.11n supports multiple-input
multiple-output (MiMo) antennas, and is able
to use signal relections to improve the signal,
which efectively reduces the zone of interference
associated with the device to a smaller area by a
factor of two versus a traditional system.
a useful source of information on industrial
wireless network design is the isa-100’s original
standard document, “isa-Tr100.00.01-2006
he automation engineer’s Guide to wireless
Technology Part 1: he Physics of radio, a
Tutorial.” its objective is to give readers a realistic
understanding of how radio links can complement
and/or replace wired connections, the factors
inluencing link range, and the pitfalls for the unwary.
industry realizes that, as we increasingly rely on
wireless for a wide range of functions, guidance
on how to overcome its challenges is needed. he
Telecommunications industry assn’s (Tia) Tr-
8.18 engineering Committee on wireless systems
Compatibility—interference and Coverage issued a
call for interest on May 1, 2013 to develop a series of
documents addressing “wireless Communication
systems – Performance in noise and interference
limited situations.” To participate, contact Tia at
703/907-7000 or their website www.tiaonline.org.
Ian Verhappen, P.eng., is an isa fellow, isa
Certiied automation Professional, member
of the Control automation hall of fame,
and a recognized authority on industrial
communications technologies.
A RECENT SURVEY
OF 300 CUSTOMERS
FOUND THAT
“TROUBLESHOOTING
INTERFERENCE WON
‘TOP HONORS’ AS THE
BIGGEST CHALLENGE
IN MANAGING A WI-fI
network.”
IAN VERHAPPEN [email protected]
20 IndustrIal networkIng • Q3 • 201320 IndustrIal networkIng • Q3 • 201320
PA R I T Y C H E C K

212013 • Q3 • IndustrIal networkIng
poWEr oVEr EthErnEt (poe). SoundS like a
two-for-one sale, right? well, in many ways it is, but
just like any great deal, Poe has a few drawbacks,
too. it evolved from a grab bag of proprietary
technologies with diferent power levels and
speciications, and it was deined in the ieee 802.3af
standard released in 2003, which was updated as
ieee 802.3at in 2009.
“Poe has been around for a long time, and
everyone had their own proprietary methods
before there were standards,” says tom hajjar, vice
president of r&d at l-Com (www.l-com.com),
which supplies radios, surge protectors for Poe,
injectors and switches. “his is why most of the
market is still non-compliant. we make products
for everyone, but we also comply with the Poe
standards, so users can have products from diferent
manufacturers work together safely. Most of the
world is going with ieee 802.3af and 802.3at, but
non-compliant, proprietary Poe isn’t going away
anytime soon.”
larry komarek, ethernet product manager at
Phoenix Contact (www.phoenixcontact.com),
says, “Poe has been growing, but ieee 802.3af only
delivers a maximum of 15 w, which limits it mostly
to security cameras and wireless access points.
however, ieee 802.3at provides 24 w at the end of a
100-meter cable and up to 34 w at the source, so it
can power more devices, such as barcode readers, iP
scanners and machine-vision inspection equipment.”
to deliver more power and enable more devices,
komarek explains that ieee set up a study group
in april 2013 to investigate how Poe can deliver
electricity over all four pairs of wires in typical Cat
5e and Cat 6 ethernet cabling, instead of continuing
to be limited to the two pairs that it used for power
up to now. Phoenix Contact has ofered Poe options
for its managed ethernet switches for a while, such
as a module that plugs into the switch’s backplane
along with its midspan injector. however, it’s also
just introduced an unmanaged Poe switch that runs
on 24 w and complies with 802.3at.
“we also see more distributed devices, intelligent
sensors and integrated circuits with lower power
draws, and they can use Poe as well,” komarek adds.
“and, more managed and unmanaged ethernet
switches have embedded Poe, so they no longer
need midspan injectors.”
Shane dufy, iber and telecommunications
product manager at B&B electronics (www.bb-elec.
com), explains that less-costly microprocessors and
more-reliable power supplies provide more options
for deploying Poe. hese include switches with
dual-power supplies, cleaner power for cameras, or
managed switches with added intelligence that can
deliver alerts on their condition or imminent failure.
B&B makes managed and unmanaged Poe switches,
including its Giga-Mini/Mc iber-to-ethernet
switches, which are unmanaged, but still have some
added logic for monitoring a iberoptic link, and
independently resetting its Poe if that link goes down.
“Besides being simpler to install due to fewer
power supplies, Poe also means users don’t need a
battery backup for each connected device,” dufy
says. “Poe only needs a battery backup or uPS for its
central power supply.”
Still, dufy conirms that many users and
developers also want ieee 802.3at to move up to
deliver 60 w, which is ofered by some proprietary,
non-standard components and suppliers. “if they’ve
got outside heaters, illumination or other auxiliary
devices, they want more power. developers also are
going from 2.4 Ghz to 5 Ghz, and putting multiple
radios in one device, but they need stronger and
denser signals,” dufy adds. “So far, there are two
ways to get to 60 w—putting more than 30 w on
the irst two pairs of wires, which isn’t approved by
the standards bodies, or putting 30 w on the second
two pairs. So, Poe’s next step is standardizing a 60-w
output, but the hurdle is handling heat on the wire.”
Mike hannah, marketing manager for networks
and security at rockwell automation (www.
rockwellautomation.com), adds that some users
even want to get Poe up to 95 w. “his means Poe
could start to drive i/o blocks on machines and
even some controllers and hMis,” hannah says.
rockwell automation is scheduled to launch its
Stratix 8000 modular, managed ethernet switches
with four or eight Poe ports this summer, and it
plans to expand its Stratix 5700 managed switch
family with a ixed port at lower cost later in the fall.
Both of these switches support the ieee 802.3af and
ieee 802.3at standards.
“as the number of intelligent devices on ethernet
in automation continues to increase—for example,
in process instrumenation—users can employ Poe
for data and power, which helps simplify the design
and deployment of systems,” adds hannah.
PoE Strives for Higher Power
212013 • Q3 • IndustrIal networkIng
B A N D W I D T H
“SOME USERS EVEN
WANT TO GET PoE UP
TO 95 W. THIS MEANS
PoE COULD START TO
DRIVE I/O BLOCKS ON
MACHINES AND EVEN
SOME CONTROLLERS
AND HMIS.”
JIM MONTAGU EEXECUTIVE EDITOR

22 IndustrIal networkIng • Q3 • 201322 IndustrIal networkIng • Q3 • 2013
R E S E A R C H
etHernet to all plX30 standalone dIn-rail-
mounted protocol gateway
provides one Ethernet port and
up to four isolated serial ports
for Ethernet/Ip to Modbus tcp/
Ip; Ethernet/Ip to Modbus serial,
1 & 4 port; Modbus tcp/Ip to
Modbus serial, 1 & 4 port; Ethernet/Ip to siemens Industrial Ethernet;
and Ethernet/Ip to AscII, 1 & 4 port. hey support multiple I/o
connections to Ethernet/Ip-enabled pAcs, providing real time transfer
of up to 4,000 words of data between hMIs and scAdA systems,
power monitors and low computers.
ProSoft Technology; 661/716-5100; www.prosoft-technology.com
access access scalance X-200rna redundant
network access (rna) modules are
designed for high network availability,
and connect terminal devices into
redundant network structures. he
modules comply with ieC 63439-
3, and support star, ring or tree
structures using Parallel redundancy
Protocol (PrP) or ring structures using
high availability seamless redundancy Protocol (hsr). Diagnostics
are available via leD, integrated web server or signaling contact.
Siemens Industry; 800/964-4114; www.siemens.com/RNA
sIMPlIFy MaPPIng stratix 5700 managed industrial
ethernet switches include an
optional integrated network
address translation (naT)
feature for simpliied integration
of IP-address mapping from a set of local, machine-level IP addresses
to the end user’s broader plant-process network. he switches are
available with six, 10 and 20 ixed-port conigurations, and include
Ieee-1588 time synchronization, Qos (prioritization) and resilient
ethernet Protocol (reP).
Rockwell Automation; 800/223-5354; www.ab.com
PrIorIty delIvery eKI-3000 light-industrial, unmanaged switches
are ive and eight port ethernet switches
in 10/100 and gigabit versions. Priority
ports prioritize the traic, and delay the less
immediately necessary data. smart diagnostic
functions help discover a fault on the system
without painstaking port analysis. advanced
power saving functions save up to 60%
consumption by shutting down ports that have
no link, and budgeting power based on the
length of the ethernet cable according to the
Ieee 802.3az energy eicient standard.
Advantech Industrial Automation; 800/205-7940;
www.advantech.com/ea
ETHERNET KEEPS EXTENDING ITS REACH, BUT THERE’S A LOT OF LEGACY
CONNECTIVITY DOING IMPORTANT WORK, SO THEY STILL NEED TO TALK
Industrial Network Generations
our Most recent surveY oF the InDustrIaL netWorKIng
audience identiied some network switch use and application trends.
We learned that almost 70% of respondents said their speed
requirement was 100 Mbps, while nearly all the rest said they needed
gigabit speed or faster. In addition, 61% of respondents connect with
both copper and iberoptic cables, while 31% use only copper and 8%
use only iberoptics. Further, 33% indicated their ethernet switches
are Power over ethernet (Poe)-enabled.
“We also see an increased need for gigabit ethernet, and the
ability to mix copper and iber connectivity on a single device,” says
Diane Davis, director of ethernet networking at red Lion controls.
“he need for higher (Gigabit) speed is largely being driven by the
use of cameras for security throughout industrial applications.
cameras and displays, in turn, are driving an increasing interest in
power-over-Ethernet.”
Industrial automation has embraced Ethernet and Ip networking, and
adoption of these technologies is growing, states paul Wacker, product
marketing manager at Moxa. “however, there’s still a huge installed base
of devices and equipment with only serial (i.e., Modbus) connectivity,”
Walker says. “In addition, there still are many manufacturers that don’t
have the resources or expertise to add Ethernet to their products.
Industrial Ethernet Gateways allow these serial devices to be connected
to Ethernet, with built-in protocol conversion between Ethernet/Ip
and legacy protocols like Modbus rtu.”

232013 • Q3 • IndustrIal networkIng
R E S E A R C H
tcP to rtu single port Mb-Gateway module
converts Modbus tcp to Modbus rtu.
It has an automatic read function, and
is equipped with one rJ45 10/100 Mbps
Ethernet port and one rs-422/485 two-
or four-wire serial port. It supports up to
12 Modbus tcp client (master) Ethernet
connections and up to 128 rtu server
(slave) serial connections. he gateway
module is 35mm dIn-rail mountable, and supports netEdit or Web
browser coniguration tools.
AutomationDirect; 770/889-2858; www.automationdirect.com
one box does It all spectre3G-W 802.11b/g/n
wireless cellular router is a single-
box solution that provides local
machine-to-machine (M2M)
network connectivity via built-
in Wi-Fi hotspot, Ethernet 10/100 and I/o ports. It connects to the
Internet via cdMA and hspA+ cellular telephone networks, and can
serve as a Wi-Fi access point (Ap) or hotspot, and scan for and tie into
existing short-distance, wireless networks.
B&B Electronics; 800/346-3119; www.bb-elec.com
MedIa FrIendly In-cabinet, Ip-20-rated Ethernet switches
with a multimode iberoptic port unit for
environments requiring conversion from
iber to copper are approved for hazardous
locations per ul and AtEX ratings. hey
conform to all necessary IEEE standards,
support Ethernet/Ip, Modbus tcp and
proinet, and are available in small expansion,
ive- to eight-port unmanaged conigurations
and eight-port managed options.
Turck; 800/544-7769; www.turck.us
network backbone Ghs gigabit modular Ethernet
switch for use as an automation
backbone device in automotive
or infrastructure applications, or
for connectivity to higher-level
networks, supports all common
Gigabit and Fast Ethernet standards and It standard protocols, as
well as proinet and Ethernet/Ip. on-board display provides access to
diagnostics and coniguration options without additional software
and tools. It accommodates up to 28 ports with up to 12 for Gigabit,
and has a -20 to 55 °c rating.
Phoenix Contact; 800/322-3225; www.phoenixcontact.com
excHange data MGate 5105-Mb-EIp industrial Ethernet
gateway for Modbus rtu/AscII/tcp and
Ethernet/Ip uses the gateway as a Modbus
master or slave to integrate existing Modbus
devices onto an Ethernet/Ip network
to collect data and exchange data with
Ethernet/Ip devices. he gateway converts
stored Modbus data into Ethernet/Ip
packets, so the Ethernet/Ip scanner can
control or monitor Modbus devices.
Moxa; 888/moxa-usa; www.moxa.com
It’s autoMatIc Ethernet Eco switch 852-1111 is
plug-and-play, connects up to ive
network devices to an Ethernet
network with data rates of 10,
100 or 1,000 Mbps. It includes
automatic data rate adjustment
(autonegotiation) or automatic
transmit/receive cable detection
(Auto-MdIX). up to 2,000 devices
can be managed via MAc address list. Full-duplex communication
complies with IEEE 802.3x in an operating range of 0–60 °c.
Wago; 800/din-rail; www.wago.us
ForM your cHoIce Anybus compactcom has
multiple form factors: chip,
full network connectivity
solution on one chip for
integration into the user´s
pcb design; brick, for users with limited space or who want to add
network connectors; and module with a complete, interchangeable
communication module. performance level 30 is for general
automation, such as general-purpose drives, sensors and hMIs,
while 40-series is for high-performance industrial communication.
HMS Industrial Networks; 312/829-0601; www.anybus.com
be dIrect brad direct-link unmanaged switches
in ive- and eight-port modules have
ultra-lock push-pull technology.
Machine-mount, Ip67, sealed
switch modules reduce network cabling
and installation costs. direct-link eight-port
switches operate in -40 to 75 °c for nEMA 6 and
Ip67 environmental ratings, and are compatible with brad industrial
products including cordsets, receptacles, ield-attachable connectors,
I/o modules, pc interfaces, gateways, switches and diagnostic tools.
Molex; 800/78molex; www.molex.com

24 IndustrIal networkIng • Q3 • 201324 IndustrIal networkIng • Q3 • 2013
R E S E A R C H
24
IndustrIal routers Industrial routers include fast EbW-h100
cellular router with an integrated, two-port
switch that uses both hspA and Gprs for data
transfer. EbW-E100 is a pure Ethernet router
with one public and one local lAn interface.
Insys Microelectronics; 49-941-586-92-0; www.insys-icom.com
gateway to autoMatIon Webport is a remote access gateway that allows
users to interact with automation systems using
native programming tools. Webport provides
data logging and alarm notifi cation via email and
SMS. it provides secure access via the internet or
cellular network using a VPn; datalogging and
reporting; alarm and event notifi cation via email,
SMS or FtP; and simultaneous serial and ethernet
device connectivity.
Spectrum Controls; 425/746-9481; www.spectrumcontrols.com
transMIt. rePeat wnM wireless network module sends process signals
between remote fi eld sites. a single unit transmits
up to 30 miles, and acts as a repeater for a virtually
unlimited transmission range. h e bidirectional
WnM uses spread-spectrum, frequency-hopping to
avoid interference. operating at standard frequencies
of 902-928 Mhz or 2.4-2.4835 ghz, WnM doesn’t
require a regulatory license.
Moore Industries-Int’l; 818/894-7111; www.miinet.com
unMasked gigabit routers are designed to of er secure
and reliable communication between ethernet-
based systems as well as higher-level networks.
integrated “stateful inspection” fi rewall and
nat masquerading security protect against
unauthorized access. additional features include prioritization and
channeling of network data trai c, IP address mapping to reduce IP
addresses, and adjustment of IP address areas.
Weidmüller; 800/849-9343; www.weidmuller.com
ease and Power eotec 2104 industrial ethernet switch comes
preconfi gured for ring redundancy. h e switch
uses self-healing ring topology, ease of operation
of an unmanaged switch, but provides port
mirroring, broadcast storm protection and
priority queuing like a managed switch. In
addition to of ering 30 ms + 5 ms/hop recovery time, the switch
allows for real-time data transfer with ieee 802.3 ethernet compliance.
Ultra Electronics; 512/434-2800; www.ultra-nspi.com
coPPer and FIber nt24k managed Gigabit
ethernet industrial switch
with up to 24 Gigabit ethernet
ports has a modular format for
dif erent confi guration options.
rack or din-rail models
provide Gigabit and 100Baset
connectivity options in copper and fi ber. it includes expanded shock
and vibration tolerances and an extreme operating temperature range.
Management features include web browser management, SnMP, jumbo
frame support, port trunking, port mirroring, dhCP client, 802.1Q
Vlan and 802.1p QoS.
Red Lion Controls; 717/767-6511; www.redlion.net/NT24k
Pass tHe FaIlover test rSP ethernet switch series supports ieC-
standard redundancy protocols, which
provide failover times of 0 ms, based
on the ieC 62439 standard. Security
functions include authentication, radius
support, role-based access, port security,
SShv2, httPS and SFtP. h ey provide
precision time synchronization in accordance with Ieee 1588v2. h e
switches are fanless with 11 ports, of which three can be used for sFP
transceivers that support 100BaseFX or gigabit ethernet.
Belden/Hirschmann; 314/854-8000; www.belden.com
rs485 to etHernet ethernet-over-rs-485 products deploy,
transport and access ethernet/IP data on
existing functional rs-485 infrastructure.
hardened ethernet routers and switches use
existing twisted-pair wiring or proprietary cabling
to rapidly create and enable extremely reliable networks without
impacting existing functionality, reliability or security.
PCN; 858/434-0605; www.pcntechnology.com
two’s better PPM-gige-2 two-channel gigabit ethernet
Lan module has self-stacking I/o
expansion and standard rJ45 connectors
to plug into 10/100/1000 Mbps networks
using standard cat. 5 unshielded, twisted-
pair copper. two gigabit ethernet
controllers combine a triple-speed, Ieee
802.3-compliant media access controller with a triple-speed ethernet
transceiver, 32-bit PcI bus controller and embedded memory. It has
crossover detection and auto-correction, polarity correction, adaptive
equalization, cross-talk cancellation, echo cancellation, timing
recovery and error correction.
WinSystems; 817/274-7553; www.winsystems.com

252013 • Q3 • IndustrIal networkIng
P R O D U C T S
ad Index
Advantech Automation ..............................................28
AutomationDirect .......................................................... 2
Hilscher ............................................................................. 4
Moxa.................................................................................... 8
ProSoft ..............................................................................12
Red Lion ....................................................................13, 15
Sealevel ............................................................................16
Turck .................................................................................... 7
CONTACT US
555 W. Pierce Rd., Suite 301, Itasca, Illinois 60143
630/467-1300 • Fax: 630/467-1124
EDITORIAL TEAM
Editor In Chief Joe Feeley
Executive Editor Jim Montague
Digital Managing Editor Katherine Bonfante
Associate Digital Editor Sarah Cechowski
Senior Technical Editor Walt Boyes
Senior Technical Editor Dan Hebert
Editorial Assistant Lori Goldberg
DESIGN & PRODUCTION TEAM
Senior Production Manager Anetta Gauthier
Art Director Angela Labate
PUBLISHING TEAM
Group Publisher/VP, Content Keith Larson
Director of Circulation Jack Jones
VP, Creative Services Steve Herner
EXECUTIVE STAFF
President & CEO John Cappelletti
VP, Circulation Jerry Clark
SUBSCRIPTIONS
888/644-1803
SALES TEAM
Northeastern and Mid-Atlantic Regional Manager
Dave Fisher • [email protected]
24 Cannon Forge Dr., Foxboro, Massachusetts 02035
508/543-5172 • Fax: 508/543-3061
Midwestern and Southern Regional Manager
Greg Zamin • [email protected]
555 W. Pierce Rd., Suite 301, Itasca, Illinois 60143
630/467-1300 • Fax: 630/467-1124
Western Regional Manager
Laura Martinez • [email protected]
218 Virginia, Suite 4, El Segundo, California 90245
310/607-0125 • Fax: 310/607-0168
Inside Sales Manager
Polly Dickson • [email protected]
630/467-1300 • Fax: 630/467-1124
REPRINTS
Foster Reprints
Claudia Stachowiak • [email protected]
866/879-9144 ext.121 • www.fosterprinting.com
MaIntaIn your IntegrIty cable entry system (cEs) permits prewired cables through
an enclosure wall without cutting the connector end of pre-
wired cable. cable grommets fit nearly any type of cable before
mounting to the enclosure wall. Plastic sealing frames have metal
reinforcements for rigidity and protect against deformation. hermoplastic or nBr rubber cable
grommets provide strain relief and IP65 protection.
Phoenix Contact; 800/322-3225; www.phoenixcontact.com
cloud servIceacecs enables remote control configurations, monitoring and automatic alerts by e-mail
or SMS, providing system maintenance backup and recovery if needed. it’s included with
company’s intel PnV and CdV based panel PCs free of charge when pre-installed in panel PC,
which is bundled with windows XP and windows 7. users worldwide can access the cloud
and link to devices via the internet.
Avalue ; 732/414-6500 www.avalue.com.tw
resPects Its elders explosion-protected remote i/o system iS1+ provides Fast
ethernet connection, Profibus redundancy, dtM support,
integration of optical rings and modules with integrated
magnetic valves. he modules are downward-compatible to
predecessors, allowing users to exchange or upgrade legacy
devices without any changes to project planning and wiring.
R. Stahl; 800/782-4357; www.stahl.de
network alert nhL series network monitoring light towers notify administrator of network
abnormalities as they develop via LeD lights, audible alarms and e-mail.
Monitoring is via snMP trapping, pinging and user-background applications.
a test switch operates all functions directly. event notification reports
automatically e-mail to up to eight addresses. Socket transmissions and rSh
commands make it lexible to support varied application needs.
Patlite; 310/328-3222; www.patlite.com
no sHutdown cxn Modular, hrough-Panel, remote-access interface connector provides the
means to pass a rJ45 connector-equipped cable to the inside of a panel
or piece of equipment without shutting down or opening the door of the
equipment. with the dust cover latched, the connector interface has an
iP67 rating. connections on the inside of the cabinet or panel can be the
same connector or a screw-clamp terminal block.
ASI; 877/650-5160; www.asi-ez.com
can do wIndows extended canblue ii intelligent can/Bluetooth module comes with
a new Pc interface mode and bridge-and-gateway mode. support
of the windows driver package, Virtual can interface (Vci), enables
wireless access for Pc-based applications to can networks. he
generic mode enables easy access to can networks for non-windows
systems, such as embedded systems and handheld service devices.
Ixxat Automation; +49-751-561-46-0; www.ixxat.com

SIMON GRANT [email protected]
thE proGrEssIon oF thE IntErnEt And
networked computing has had an efect on
almost all business sectors and industries, some
more signiicantly afected than others. Now it’s
revolutionizing the automation industry, or at least
it will for Automation GT.
he focus of automation traditionally has been
centered on the mechatronics of a standalone
machine—the mechanical engineering, electrical
engineering and controls engineering of a system.
Our vision is to expand from a simple mechatronic
machine to a shared network of systems that
talk to each other and report to a management
portal in real time. he technology we foresee
means that, with a few clicks of a mouse, a COO
sitting at his or her desk in Silicon Valley can pull
a comparative summary of all systems installed
in Shanghai or Buenos Aires, and drill down on a
speciic machine to see its operational eiciency
and what parts need service.
We’ve begun to standardize the tools with
which automation systems operate, and network
them to the same controls operating platform.
Instead of various machines reporting (or
not reporting) to separate and isolated data
repositories, all machines report to one master
platform where you can view data for each
machine as well as a comparative summary of all
operating systems. Data becomes information.
currently, machines are installed with custom
code, custom coniguration, custom reporting,
and custom management. Instead of a unique
coniguration for each machine, systems should be
on a standardized platform, so users can look at
any machine through the same interface and view
aggregated data that can be crunched and compared.
We can build machines on an integrated It
infrastructure, so users can store information on a
shared database. Identity proiles can be set up for
management and access control. he ability to read
data or make code changes will be permitted only
to authorized users at login. his level of regulation
isn’t normally practiced because, until now, the
technology didn’t exist. hat’s going to change
and Automation GT is among the irst custom
automation houses to ofer it. We’re already doing it
for our customers that operate internationally.
Another added bonus of placing automation
systems onto a shared infrastructure is centralized
“recipe” management. We have a customer that
uses automation to build patient-speciic medical
devices. hey have 700+ spreadsheets of code for
any one order. For each assembly, a system operator
manually plugs in the code to give the machine
the set of brains it needs to assemble the speciied
product. he problem is that the spreadsheets
are not controlled. If someone accidently changes
a number, no one knows. So, we suggest that all
recipes be uploaded to a database. When the
system operator needs to change the recipe, he or
she can simply select “recipe 4” or “recipe 4,652.”
his can be done on the HMI directly or remotely
through the shared server. he machine will reach
out to the database, pull the selected recipe, put it
on the machine, and the machine will start running.
hat recipe is managed and controlled, so no one
can change it. And if someone wants to change it,
you can program in change control on the server,
so the operator is required to ill in a form and
say “this is how I’m going to modify it, this is how
I’ve tested the new code, etc.” Furthermore, upon
program modiication, alerts can be set up to signal
management that recipe 4,652 was changed on
Machine A by operator X.
It’s important that you have a uniied relationship
among your engineering, automation and controls,
and It groups. When those three are aligned and
able to communicate, you can use the tools from
the It side and the controls and software side, and
train your mechatronics engineers to listen and talk
to all of these. his trifecta is a very powerful system.
recent advances in networking, virtual machine
technology and cloud computing have allowed an
elegant integration of automation and business sys-
tems. his opens up the analysis and reporting tools
that manufacturing, engineering and management
are already comfortable using.
As the automation industry progresses, more
companies will network systems together. he level
of control management, security, and information is
unparalleled by any other applicable technology.
Simon Grant is president and CEO of Automation
GT in Carlsbad, Calif, which designs and
manufactures automated assembly, inspection,
and test systems in the medical device,
pharmaceutical and biotechnology markets. Learn
more at www.automationgt.com
The Shift to Industrial Networks
26 IndustrIal networkIng • Q3 • 2013
T E R M I N A T O R
2626
AS THE AUTOMATION
INDUSTRY PROGRESSES,
MORE COMPANIES WILL
NETWORK SYSTEMS
TOGETHER. THE
LEVEL OF CONTROL
MANAGEMENT,
SECURITY AND
INFORMATION IS
UNPARALLELED BY ANY
OTHER APPLICABLE
TECHNOLOGY.

For additional information, please contact
Foster Printing Service, the official reprint
provider for Industrial Networking.
Give yourself a competitive advantage with reprints. Call us today!
Call 866.879.9144 or
Use reprints to
maximize your
marketing initiatives
and strengthen your
brand’s value.
Reprints are a simple way to put
information directly into the hands
of your target audience. Having been
featured in a well-respected publication
adds the credibility of a third-party
endorsement to your message.
REPRINTS ARE IDEAL FOR:
n New Product Announcements
n Sales Aid For Your Field Force
n PR Materials & Media Kits
n Direct Mail Enclosures
n Customer & Prospect
Communications/Presentations
n Trade Shows/Promotional Events
n Conferences & Speaking Engagements
n Recruitment & Training Packages
CUSTOM REPRINTS

www.advantech.com
Customizable Functionality and Flexible Connectivity• Daisy chain connection with auto-bypass protection• Remote monitoring and control from a smart phone/pad• Group configuration capability to setup multiple modules• Intelligent control ability by Peer-to-Peer and GCL function• Multiple protocol support: Modbus TCP, TCP/IP, UDP, HTTP, DHCP• Web language support: XML, HTML 5, Java Script
ADAM-625015-ch Isolated Digital I/O Modbus TCP Module
ADAM-625616-ch Isolated Digital Output Modbus TCP Module
ADAM-62606-ch Relay Output Modbus TCP Module
ADAM-62664-ch Relay Output Modbus TCP Module with 4-ch DI