SlingSecure USB Eng
-
Upload
slingsecure-mobile-encryption -
Category
Technology
-
view
994 -
download
1
description
Transcript of SlingSecure USB Eng

UST
USB Security Token

Mobile and Fixed networks Security OEM
SlingSecure S.r.l. concentrates its activity on the development of hardware and software platforms designed to support integration and custom developments for
SlingSecure S.r.l.

SlingSecure Secure Environment
SlingSecure
Secure Environment product range is based on a proven security architecture designed to deliver high-end performances to integrators and developers

SlingSecure Secure Environment
SlingSecure range ü ESE -‐ Embedded Secure Engine
ü mSE -‐ Micro Secure Environment
ü UST -‐ USB Security Token

E S E Embedded Secure Engine Technical Features ü Cryptographic Libraries
-‐ AES (128,192,256) -‐ DES/3DES -‐ IMAC/HMAC/CMAC NIST 800-‐38B -‐ SHA1, SHA256 -‐ AES/DES variaCons and Custom Algorithms on demand -‐ Up to 4 concurrent cryptographic sessions
ü Physical Random Noise Generator FIPS 140-‐2 ü Unique Serial Number/ID ü Local/Remote/Auto/Manual ZEROIZE ü Keys Secure Repository ü Keys GeneraCon & Management ü Administrator/User profiles ü Encrypted CommunicaCon APIs
User Application
ESE Communication Library
Encrypted Communication Channel
Crypto Core
Policies Custom Algorithms (up to 6 Variants)
Over Ciphered Keys Data Base
U n i q u e I D Serial Number
EMBEDDED SECURE ENGINE

E S E Easy HW/SW IntegraCon ü ANSI C SoVware Library
-‐ Micro Controller Independent
-‐ Several Compilers/IDE supported ü Serial Com Channel (RX/TX up to 450 Kb/s) ü USB Channel (up to 11 Mb/s) ü Power Management
-‐ Frequency management -‐ Three power modes supported:
-‐ 50mA (3V) @ 58.924MHz -‐ 12mA (3V) @ 14.7456MHz -‐ 2mA (3 V) @ Idle state
ü Small Package (9x9x0.85mm) ü Single Power Supply (2.9V-‐5V) ü Physical Random Noise Generator FIPS
140-‐2
Oscillator
PCysicaJ RNG
System
SO Card o r S P 1 Ftash
USB interface ready
SP1
UAAT (Rx/Tx)

m S E micro Secure Environment All the SlingSecure features in a MicroSD
ASIC
2xUART
SD Ctrl
512KByte FLASH
32bit MCU ♦6xDMA+lnt Ctrl
96KByte RAM
2xSPI
SE Engine 2xUSB HS Ext BUS
Available 2Q 2011
SPI or BUS
NAND Flash
ü HW crypto engine ü Standard and custom algorithms ü SD card interface (up to 450Mb/s) ü Integrated memory (up to 4 GB) ü Internal keys database ü Suitable for Mobile Applica3ons

UST USB Secure Environment
USB security adapter for
ü microSD card encryption ü secure mass storage ü security operations
-‐ file encryp3on - strong authen3ca3on - digital signature - running secured OS
- running secured applica3ons
MicroSD
NO drivers NO soKware installed on PC
vs**?'
A u t h e n t i c a t i o n and Encryption

UST Typical USE ü MicroSD EncrypCon • Secure and hide enPre parPPons on microSD cards
ü Host EncrypCon • Secure any data (files, documents, etc.) stored on PCs or Servers
using one or more access passwords
ü Secure Data Sharing (or sending) • Encrypt data and share (e-‐mail, file sharing, Vp, etc.)
ü Physical Data Shipment • Encrypt the enPre microSD using a shared access key and ship the card (the microSD will only show the clear parPPon to unauthenPcated accesses)
ü Running secured applicaCons and OS • Boot and run complete OS or specific applicaPons from the UST
memory • Run Secure Virtual Machines
• Based on symmetric access keys, PKI can be supported

One UST adapter ... mulCple SD cards Many microSD cards One UST Adapter
ü Several microSD cards* can be plugged and encrypted with a single UST adapter *one at a time
ü Two authenCcaCon levels available • UST adapter access password • MicroSD access password
ü Switch from an encrypted card to another by simply using the access password of each microSD
MicroSD cards

UST USB Secure Environment
ü Hidden secure microSD parCCon ü Hardware format and zeroize ü Fully compaCble with
• MicrosoV Windows XP/Vista
• Apple Mac OS X
• GNU Linux Authentication
MicroSD

UST OperaCng Modes The UST adapter shows different partitions according to the operating mode
ü Clear ParCCon (default) • AutomaCcally shown aVer USB inserCon
• Contains User applicaCon and Admin (if required)
ü Secure ParCCon • AcCve only aVer successful authenCcaCon
ü Only one ac3ve par33on at a 3me

UST EncrypCon Technique The microSD secure parCCon is fully encrypted
v Standard or custom encrypCon algorithm or
v OFB mode 256 bit key, 128 bit Init Vector
v Both file allocaCon table and data sectors are encrypted
v IniCal Vectors (IV) are generated separately for each microSD sector
• IV stored in special/unaccessible area microSD Sectors
1 sector contains 32 IVs
v UST exclusive security features

UST Smart Card Extension
ü UST device supports plug-‐in Smart Cards
ü High Level HW and SW security (up to EAL5+ CC)
ü Dynamic UST device customizaCon
ü AddiConal encrypCon algorithms and funcCons
ü Extended UST Libraries to export Smart Card funcConaliCes for host-‐side secure applicaCons
Smart Card UST Device
Authentication
MicroSD
NO PC/SC drivers on PC PKI Infrastructure enabled Mul3 Factor Authen3ca3on

UST USB Secure Environment
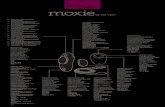
UST interface main elements 1. Display
2. microSD slot
3. Trackball
4. Smart Card slot
5. Zeroize button

UST Hardware Architecture ü SlingSecure
• micro controller centric architecture ü FPGA
• scalable for specific requirement and customisaPon • standard 250.000 gates • up to 1.000.000 gates
ü microSD -‐ Read Only • for applicaPons and OEM SW • Extended internal keys database • standard size 2GB
ü microSD -‐ removable • Clear + Secure parPPon • standard size 4GB
ü Smart Card • ISO7816 interface • plugin form factor
ü Display & trackball
• for direct password inserPon
Display
trackball
Smart Card removable microSD
i n t e r n a l m i c r o S D Read Only
SS Micro

UST SDK & Development Libraries
HOST Apps
HOST Libraries
HOST Drivers
UST Firmware
Custom ApplicaCons UST Secure Drive
UST Secure Document
USE PC Test U S E R N G Evaluator
BASIC AP
PS
S m a r t C a r d APDU Library
Card Access Library
AdministraCon Library
Secure MicroSD Library
CommunicaCon Library
Crypto Library
Standard USB Mass Storage Drivers
Smart Card APDU Library
Card Access Library
User Interface Library
Coprocessor Library
RNG Library STD Crypto Library
UST Hardware MicroCTRL Physical RNG Custom HW (FPGA)
Display & Trackball MicroSD Smart Card
SlingSecure provided
Hardware Peripherals HOST OS provided USR provided
HOST SDK
CO
RE SDK

UST Crypto Libraries UST based Secure ApplicaCons can be easily developed using libraries
• Host Libraries - Provide UST device Communication - Export internal UST secure capabilities • Core Libraries
- Encryption/Decryption Management - Key Management - microSD Secure Management - Users Management - Anti tampering Management - Custom Secure Functions & Algorithms
PC/ Host
Host Secure Application
Host Libraries
Core Libraries
UST

UST Security Keys • Master Key (Km) -‐ internally generated -‐ one for each device -‐ using USE RNG • SD Key (Ksd): generated when microSD is formaled • Admin Key (Ka): Customer generated used inside admin soVware • Remote Management Keys (Ke, Ks): generated by key management system Encryption Algorithms • Customer developed encrypCon algorithms • AES256 (with custom SBOX1) used to encrypt microSD FAT and Data • CMAC with AES256 (with custom SBOX2) used for authenCcaCon • AES256 (with custom SBOX2) used to cipher communicaCon protocol
• SHA256 used for digest funcCons
Algorithm structure can be fully customised on request

UST Key Repositories Any USE device supports two key repositories • Manual Keys
• Can be added/deleted by the user • Can be imported/exported • Can be generated using USE internal RNG
• Remotely Managed Keys • Can be generated exclusively by Key Remote Management system • Can be imported only to the designated USE device • Cannot be exported by the user
Over-Ciphering Key
Keys are encrypted by means of an unique Over-Ciphering Key
Manual Keys
Managed Keys
Key Repositories
UST 2
Key ID (4 bytes) Attributes/Policies Encrypted Key Value (16 Bytes)
IN
AES 256
Clear Key Value (16 Bytes)
OUT

UST -‐ Manual Keys
Manual keys are managed by the User • Enabled only if defined in the USE device policies
• Can be exported/imported (manual backup, manual transfer)
• Can be generated manually or by means of the USE physical RNG
• Under the User responsibility
Export/Import process • To export one or more manual keys the public identifier (public key)
of the destination USE device is required • The exported key is encrypted and signed using a public key
algorithm
• A family key can be used to limit the manual key export process (closed group)
• The process can be used for manual key backup (export to itself)
Export/Import Process
Encrypted Key
UST 1
Export
Signature
Import
UST 2

UST Backup
UST can produce encrypted backups readable by ü same UST ü "rescue" UST Full Data and Manual Key Backup
• Manual Keys only • Public and Private data • KRM managed keys backup up on KRM server
Keys are encrypted by means of an unique Over-Ciphering Key
UST
Backup data
Encrypted Keys and Data Signature
Backup DataBase
Backup CD
Backup microSD

UST KRM -‐ Keys Remote Management UST devices can be remotely managed if two special keys are provided at IniCalizaCon Time • KRM AuthenWcaWon Key • KRM EncrypWon Key
The keys above are univocally generated by the Key Remote Management (KRM) Server • One KRM pair per UST device • The KRM pairs are stored both in the UST device and in the KRM server
The KRM Server generates operaConal keys for any UST device • Every operaWonal key is encrypted and signed for the
specific UST device • The generated key is imported by the user and stored in
the internal UST Remote Managed Key repository Remotely Managed Keys cannot be exported
UST Win/Linux M a c O S Server
Managed
M a n a g e d K e y Database
Key Remote Management (KRM) Server
GeneraCon
Signature Encrypted Key
Import
UST

KRM Security
KRM Security Engine
• KRM Key generation • KRM Authentication and Encryption • Administrator Authentication KRM System scalability
• One UST admin supports UST network Growth
• 1MB memory manages over 1500 UST devices
GeneraCon
W i n / L i n u x MacOS Server
Managed Key Database
Managed Keys
Key Remote Management (KRM) Server
Encrypted Key Signature
Import
UST

UST Firmware Update
UST Firmware updates are ü Encrypted for each single device
ü Signed by the OEM ^ USEpro FW Update
SN: none -‐ APP: none -‐
Firmware Update
A d m i n Password
Upload New Firmware
*J
Admin Login
WaiPng for device..,
UST Administrator Login is required for firmware update
Firmware 2...N
OEM
Encrypted Firmware Signature
Encrypted Firmware Signature Firmware 1

UST Standard ApplicaCons
Standard UST comes with a simple and effecCve soVware simple and effecPve soVware that allows
ü access to the private secure area of the memory card
ü file and folders encrypCon with simple drag and drop
ü basic key management funcCons
Professional soVware tools include
ü UST Test Toolkit ü RNG Test tool ü Custom developed tools and SW for specific requirement

UST Security Suite UST Security Suite is the simple and effective software that allows
ü access to the private secure area of the memory
card
ü file and folders encryption with simple drag and drop
ü basic key management functions

UST Off-‐line EncrypCon/DecrypCon • Drag and Drop your files
• Secure Documents will recognize the crypto acPon automaPcally
• Select the encrypPon key from your internal UST Keys Database
• Your keys will never come out of your UST device
• Auto Key generaPon using FIPS 140-‐2 random noise generator
Off-‐line crypto opera3ons allow you to protect any files stored on internal or
external media

UST Test Toolkit UST Test Tool kit allows professional users and developers to test and verify internal HW funcPons.

RNG Test Tool allows professional users and developers to test and verify internal Random Noise Generator performances and FIPS compliance. Random stream export funcCon for external test or use within custom applicaCons.
UST RNG Test Tool

SlingSecure Custom tools and SW SlingSecure cryptographic functions can be exported to the Host Custom Algorithms and FuncCons
ü Tool Suite for custom algorithms and funcCons design
Off-‐line EncrypCon/DecrypCon ü SlingSecure devices can be used as a secure engine
to encrypt/decrypt files and documents on the Host System
Crypto Libraries ü Internal security funcCons can be exported and
used on the Host System by means of specific crypto libraries

SlingSecure Service & Support SlingSecure products are backed up by the support of the engineering and design team for ü Cost effecCveness ü Smooth system integraCon
ü Timely soluCon delivery The high level service & support for all SlingSecure View products allows the Customer to reach the desired result with the best cost to performance raPo

Contacts
SlingSecure InternaPonal
30' Kenilworth/1 Sir Augustus Bartolo Street
Ta' Xbiex, Malta