Seminar Report on Zero Coin
-
Upload
akshay-chavan -
Category
Documents
-
view
222 -
download
0
Transcript of Seminar Report on Zero Coin

Sinhgad Technical Education Society’s
NBN Sinhgad School of Engineering
Pune – 411041.
Seminar Report
On
Zero Coin: Anonymous Distributed E–Cash from Bitcoin
Submitted By
Akshay Chavan 21
Department of Computer Engineering
Bachelor of Engineering (Computer Engineering)
University of Pune
Year 2013 -2014
NBN Sinhgad School Of Engineering,Pune Page 1

CERTIFICATE
This is to certify that the following student of T.E. Computer, NBN
Sinhgad School of Engineering, Ambegaon (Bk), Pune.
“ChavanAkshayBalasaheb”
Has successfully completed the Seminar and Technical
Communication report on
“Zero Coin: Anonymous Distributed E–Cash from Bitcoin”
in the partial fulfillment of the requirements for the completion of
T.E. in Computer Engineering in 2013-14 as prescribed by the
University of Pune.
Prof. Parag. S. Kulkarni. Dr. Rajesh Prasad.
Seminar Guide Head of Department
Department of Computer Engineering
DrS.D.Markande
Principal
NBN Sinhgad School of Engineering
Pune – 411041.
NBN Sinhgad School Of Engineering,Pune Page 2

ACKNOWLEDGEMENT
I with great gratitude wish to all, who have made it possible to
complete this seminar with success. For enriching me with valuable
knowledge, for plenty of precious and vast experience that I was able
to receive.
I would also like to express our deepest and sincere gratitude to my
internal guide Prof. Parag. S. Kulkarni, for his dynamic and
valuable guidance and keen interest in my seminar work. I am
grateful to him for his constant encouragement in the fulfillment of
the seminar work.
This seminar topic cannot be considered complete without
mentioning our H.O.D. Dr Rajesh Prasad and our Principal Dr.
S.D. Markande. They have always been supportive and helpful
throughout the course of our Bachelor of Engineering.
Last but not the least; we would also like to thank all the staff
members and all our colleagues for their valuable suggestions and
support.
AkshayChavan
(T.E. Computer Engineering)
NBN Sinhgad School Of Engineering,Pune Page 3

Department of Computer Engineering
Seminar Approval Sheet for T.E. Students
Seminar Topic: - Zero Coin
“An Anonymous Distributed E–Cash from Bitcoin“
Seminar Guide: - Prof. Parag.S.Kulkarni
Sr. no Details Date Remarks Sign
1. Initial Discussion of topic
with guide
1-02-14 Yes
2. Discussion of zero draft Contents Appropriate format Presentation
11-02-1412-02-1421-02-14
Done
3. Final approval of seminar
report by guide
13-02-14 Approved
4. Any other comments 13-02-14 Good topic
chosen
Roll no Name of student
21 AkshayChavan
NBN Sinhgad School Of Engineering,Pune Page 4

LIST OF DIAGRAMS
Diagrams Included:
Diagram 1: Two example block chains.Chain (a) Chain (b………...9
Diagram 2: Example Bitcoin Transactions…………………………11
Diagram 3: Bitcoin………………………………………………….17
Diagram 4: Zerocoin performance as a function parameter size.......20
Diagram 5: Performance of Zerocoin Algorithms………………….25
NBN Sinhgad School Of Engineering,Pune Page 5

TABLE OF CONTENTS
COVER PAGE………………………………………………….....I
CERTIFICATE…………………………………………………... II
ACKNOWLEDGEMENT............................................................. III
APPROVAL SHEET……………………………………………...IV
LIST OF DIAGRAMS…………………………………………….V
1.INTRODUCTION……………………………………………….7
1.1 Abstract
1.2 Background
1.3 Literature Survey
2.DECENTRALIZATION………………………………………..12
2.1 Decentralized E-cash
2.2 Decentralized E-cash from Strong R.S.A
2.3 Integrating with Bitcoin
3. ANONYMITY&PERFORMANCE……………………………18
3.1 Real world security and Parameter choice
3.2 Performance
4.BASIC UTILIZATION & RESEARCH……………………….25
4.1 Advantages & Disadvantages
4.2 Previous Work
5.APPLICATIONS………………………………………………...27
6.RESEARCH AND FUTURE SCOPE………………………….28
7.APPENDIX………………………………………………………29
NBN Sinhgad School Of Engineering,Pune Page 6

8. CONCLUSION……………….................................................30
9.BIBLIOGRAPHY…………………….........................................31
NBN Sinhgad School Of Engineering,Pune Page 7

CHAPTER 1
INTRODUCTION
1.1 ABSTRACT
Bitcoin is the first e-cash system to see widespread adoption. While Bitcoin offers the
potential for new types of financial interaction, it has significant limitations of regarding
privacy. Specifically, because the Bitcoin transaction log is completely public, users' privacy
is protected only through the use of pseudonyms. In this paper we propose Zerocoin, a
cryptographic extension to Bitcoin that augments the protocol to allow for fully anonymous
currency transactions. Our system uses standard cryptographic assumptions and does not
introduce new trusted parties or otherwise change the security model of Bitcoin. We
detail Zerocoin's cryptographic construction, its integration into Bitcoin, and examine its
performance both in terms of computation and impact on the Bitcoin protocol.
Published in:
Security and Privacy (SP), 2013 IEEE Symposium on
Date of Conference:
19-22 August 2013
Page(s):397 - 411
ISSN:1081-6011
E-ISBN:978-0-7695-4977-4
Print ISBN:978-1-4673-6166-8
INSPEC Accession Number:13597242
Conference Location:Digital Object Identifier:Berkeley, CA10.1109/SP.2013.34
NBN Sinhgad School Of Engineering,Pune Page 8

1.2 BACKGROUND
Digital currencies have a long academic pedigree. As of yet, however, no system
from the academic literature has seen widespread use. Bitcoin, on the other hand, is a viable
digital currency with a market capitalization valued at more than $100 million [1] and
between $2 and $5 million USDin transactions a day [2]. Unlike many proposed digital
currencies, Bitcoin is fully decentralized and requires no central bank or authority. Instead,
its security depends on a distributed architecture and two assumptions: that a majority of its
nodes are honest and that a substantive proof-ofworkcandeter Sybil attacks. As a
consequence, Bitcoinrequires neither legal mechanisms to detect and punish doublespending
nor trusted parties to be chosen, monitored, orpoliced. This decentralized design is likely
responsible forBitcoin’s success, but it comes at a price: all transactions are public and
conducted between cryptographically .While relatively few academic works have considered
theprivacy implications of Bitcoin’s design [2, 3], the preliminaryresults are not encouraging.
In one example, researcherswere able to trace the spending of 25,000 bitcoins that were
allegedly stolen in 2011 [3, 4]. Although tracking stolen coinsmay seem harmless, we note
that similar techniques could also be applied to trace sensitive transactions, thus violating
users’ privacy. Moreover, there is reason to believe that sophisticated results from other
domains (e.g., efforts to deanonymizesocial network data using network topology [5]) will
soon be applied to the Bitcoin transaction graph. Since all Bitcoin transactions are public,
anonymous transactions are necessary to avoid tracking by third parties even if we do not
wish to provide the absolute anonymity typically associated with e-cash schemes. On top of
such transactions, one could build mechanisms to partially or explicitly identify participants
to authorized parties (e.g., law enforcement). However, to limit this information to authorized
parties, we must first anonymize the underlying TheBitcoin community generally
acknowledges the privacy weaknesses of the currency. Unfortunately, the available
mitigations are quite limited. The most common recommendation is to employ a laundry
service which exchanges different users’ bitcoins. Several of these are in commercial
operation today [6, 7]. These services, however, have severe limitations: operators can steal
funds, track coins, or simply go out of business, taking users’ funds with them. Perhaps in
NBN Sinhgad School Of Engineering,Pune Page 9

recognition of these risks, many services offer short laundering periods, which lead to
minimal transaction volumes and hence to limited anonymity.
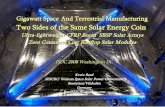
Figure 1: Two example block chains. Chain (a) illustrates a normal Bitcoin transaction
history, with each transaction linked
to a preceding transaction. Chain (b) illustrates a Zerocoin chain. The linkage between mint
and spend (dotted line) cannot be determined from the block chain data.
The first and most basic contribution of my work is to recognize that Bitcoin answers all of
these concerns, providing us with a backing currency, a bulletin board, and a conditional
currency redemption mechanism. Indeed, the core of the Bitcoin protocol is the decentralized
calculation. In this paper we propose Zerocoin, a cryptographicextension to Bitcoin that
augments the protocol to allowfor fully anonymous currency transactions. Our system uses
standard cryptographic assumptions and does not introducenew trusted parties or otherwise
change the security model ofBitcoin. We detail Zerocoin’s cryptographic construction, its
integration into Bitcoin, and examine its performance both interns of computation and impact
on the Bitcoin protocol.
NBN Sinhgad School Of Engineering,Pune Page 10

1.3 LITERATURE SURVEY
In this section we provide a short overview of the Bitcoinprotocol. For a more
detailed explanation, we refer the reader to the original specification of Nakamoto [15] or to
the summary of Barber et al. [2].The Bitcoin network. Bitcoin is a peer-to-peer network of
nodes that distribute and record transactions, and clients used to interact with the network.
The heart of Bitcoin is the block chain, which serves as an append-only bulletin board
maintained in a distributed fashion by the Bitcoinpeers. The block chain consists of a series
of blocks connected ina hash chain.3 Every Bitcoin block memorializes a set of transactions
that are collected from the Bitcoinbroadcastnetwork. Bitcoin peers compete to determine
which node willgenerate the next canonical block. This competition requireseach node to
solve a proof of work based on identifyingspecific SHA-256 preimages, specifically a block
B suchthatSHA256 (SHA256 (B)) = (0_|| {0, 1}256−_).4 the value_ is selected by a periodic
network vote to ensure that on
Average a block is created every 10 minutes. When a peer generates a valid solution, a
process known as mining, it broadcasts the new block to all nodes in the system. If the block
is valid (i.e., all transactions validate and a valid proof of work links the block to the chain
thus far), then the new block is accepted as the head of the block chain.
Process thenrepeats.Bitcoin provides two separate incentives to peers that mine requires a
non-trivial computational investment) entitles the creator to a reward, currently set at 25
BTC.5 Second, nodes who mine blocks are entitled to collect transaction fees from every
transaction they include. The fee paid by a given transaction is determined by its author
(though miners may exclude transactions with insufficient fees or prioritize high fee
transactions).Bitcoin transactions.A Bitcoin transaction consists of a set of outputs and
inputs. Each output is described by the tuple (a, V) where a is the amount, denominated in
Satoshi (one bitcoin = 109 Satoshi), and V is a specification of who is authorized to spend
that output. This specification, denoted scriptPubKey, is given in Bitcoin script, a stack-based
non- Turing-complete language similar to Forth. Are simply a reference to a previous
transaction output, 6as well as a second script, scriptSig, with code and datathat when
combined with scriptPubKey evaluates to true.Coinbase transactions, which start off every
NBN Sinhgad School Of Engineering,Pune Page 11

block and payits creator, do not include a transaction input.To send d bitcoins to Bob, Alice
embeds the hash7 of.
Transaction inputs
3For efficiency reasons, this chain is actually constructed using a hash
Tree, but we use the simpler description for this overview.
4Each block includes a counter value that may be incremented until the
Hash satisfies these requirements.
5The Bitcoin specification holds that this reward should be reduced every
Few years, eventually being eliminated altogether.
Input:
Previous tx: 030b5937d9f4aaa1a3133b...
Index: 0
scriptSig: 0dcd253cdf8ea11cdc710e5e92af7647...
Output:
Value: 5000000000
ScriptPubKey: OP_DUP OP_HASH160
a45f2757f94fd2337ebf7ddd018c11a21fb6c283
OP_EQUALVERIFY OP_CHECKSIG
Figure 2: Example Bitcoin transaction. The output script specifies that the redeeming party
provide a public key that hashes to the given value and that the transaction is signed with the
corresponding private key.
Bob’s ECDSA public key pkb, the amount d, and some scriptinstructions in
ScriptPubKey as one output of a transactionwhose referenced inputs total at least d bitcoins
(see Figure 2).Since any excess input is paid as a transaction fee to the nodewho includes it in
a block, Alice typically adds a secondoutput paying the surplus change back to herself. Once
the6This reference consists of a transaction hash identifier as well as an index into the
transaction’s output list.7A 34 character hash that contains the double SHA-256 hash of the
key and some checksum data. 8Individual recipients are free to disregard this advice.
However, this could make them vulnerable to double-spending attacks as described by
Karameet al. [16].
NBN Sinhgad School Of Engineering,Pune Page 12

CHAPTER 2
DECENTRALIZATION
2.1 DECENTRALIZED E – CASH
Our approach to anonymizing the Bitcoin network uses a form of cryptographic e-cash. Since
our construction does not require a central coin issuer, we refer to it as a decentralized e-cash
scheme. In this section we define the algorithms that make up a decentralized e-cash scheme
and describe the correctness and security properties required of such a system.Notation.Let λ
represent an adjustable security parameter let poly (・) represent some polynomial function,
and let ν(・) , represent a negligible function. We use C to indicate the set of allowable coin
values. Definition 3.1 (Decentralized E-Cash Scheme): A decentralized e-cash scheme
consists of a tuple of possibly randomized algorithms (Setup, Mint, Spend, Verify). •
Setup(1λ) → params. On input a security parameter, output a set of global public parameters
paramsand a description of the set C.
• Mint(params) → (c, skc). On input parametersparams, output a coin c C∈ , as well as a
trapdoorskc. • Spend(params, c, skc,R,C) → (π, S). Given string R {∈ 0, 1}∗, and an
arbitrary set of coins C, output a coin spend transaction consisting of a proof π and serial
number S if c ∈ C C⊆ . Otherwise output• Verify(params, π, S,R,C) → {0, 1}. Given
params, ⊥.and a set of coins C, output 1 if C C ⊆ and (π, S,R) is valid. Otherwise output 0.
We note that the Setup routine may be executed by a trusted party. Since this setup occurs
only once and does not produce any corresponding secret values, we believe that this
relaxation is acceptable for real-world applications. Some concrete instantiations may use
different assumptions. Each coin is generated using a randomized minting algorithm. The
serial number S is a unique value released during the spending of a coin and is designed to
prevent any user from spending the same coin twice. We will now formalize the correctness
and security properties of a decentralized e-cash scheme. Each call to the Spend algorithm
can include an arbitrary string R, which is intended to store transaction-specific information
(e.g., the identity of a transaction recipient). Correctness. Every decentralized e-cash scheme
NBN Sinhgad School Of Engineering,Pune Page 13

must satisfy the following correctness requirement. Let params←Setup(1λ) and (c, skc) ←
Mint(params). Let C C⊆ be any valid set of coins, where |C| ≤ poly(λ), andassign(π, S) ←
Spend(params, c, skc,R,C). The scheme
iscorrect if, over all C, R, and random coins used in the above algorithms, the following
equality holds with probability 1 − ν(λ): Verify(params, π, S,R,C {∪ c}) = 1 Security. The
security of a decentralized e-cash system is defined by the following two games: Anonymity
and Balance. We first describe the Anonymity experiment, which ensures
that the adversary cannot link a given coin spend transaction(π, S) to the coin associated with
it, even when the attackerprovides many of the coins used in generating the spend
transaction. Definition 3.2 (Anonymity): A decentralized e-cash scheme Π = (Setup, Mint,
Spend, Verify) satisfies the Anonymity requirement if every probabilistic polynomialtime
(p.p.t.) adversary A = (A1,A2) has negligible advantage in the following experiment.
Anonymity(Π,A, λ)params← Setup(1λ) For i {∈ 0, 1}: (ci, skci) ← Mint(params) C,R,
z)←A1(params, c0, c1); b ← {0, 1} ((π, S) ← Spend(params, cb, skcb,R,C {∪ c0, c1})
Output: b_ ←A2(z, π, S)
We define A’s advantage in the above game as|Pr[ b= b_ ] − 1/2|. The Balance property
requires more consideration. Intuitively, we wish to ensure that an attacker cannot spend
more coins than she mints, even when she has access to coins and spend transactions
produced by honest parties. Our definition is reminiscent of the “one-more forgery”
definition commonly used for blind signatures. We provide the attacker with a collection of
valid coins and an oracleOspendthat she may use to spend any of them.9 Ultimately A must
produce m coins and m+1 valid spend transactions such that no transaction duplicates a serial
number or modifies a transaction produced by the honest oracle. Definition 3.3 (Balance): A
decentralized e-cash scheme
Π = (Setup, Mint, Spend, Verify) satisfies the Balance property if ∀N ≤ poly(λ) every p.p.t.
adversary A has negligible advantage in the following experiment. Balance(Π,A,N,
λ)params← Setup(1λ) For i = 1 to N: (ci, skci) ← Mint(params)
Output: (c_1, . . . , c_ m, S1, . . . , Sm, Sm+1)←AOspend(·,·,·)(params, c1, . . . , cN) 9We
provide this functionality as an oracle to capture the possibility that the attacker can specify
arbitrary input for the value C.
NBN Sinhgad School Of Engineering,Pune Page 14

2.2DECENTRALIZED E – CASH FROM STRONG RSA
In this section we describe a concrete instantiation of adecentralized e-cash scheme. We first
define the necessarydecentralized e-cash scheme. We first define thee
necessarycryptographicingredients.A. Cryptographic Building BlocksZero-knowledge proofs
and signatures of knowledge.Ourprotocols use zero-knowledge proofs that can be
instantiated
using the technique of Schnorr [18], with extensions due to e.g., [19, 20, 21, 22]. We convert
these into non-interactiveproofs by applying the Fiat-Shamir heuristic [23]. In thelatter case,
we refer to the resulting non-interactive proofsassignatures of knowledge as defined in [24].
When referring to these proofs we will use the notation ofCamenisch and Stadler [25]. For
instance, NIZKPoK{(x, y) :h = gx ∧ c = gy} denotes a non-interactive zero-knowledgeproof
of knowledge of the elements x and y that satisfy bothh= gxand c = gy. All values not
enclosed in ()’s areassumed to be known to the verifier. Similarly, the extensionZKSoK[m]
{(x, y) : h = gx ∧ c = gy} indicates a signatureof knowledge on message m.Accumulators. Our
construction uses an accumulator basedon the Strong RSA assumption. The accumulator we
usewas first proposed by Benaloh and de Mare [10] and laterimproved by Baric and
Pfitzmann [11] and CamenischandLysyanskaya [12]. We describe the accumulator using
thefollowing algorithms:
• AccumSetup(λ) → params. On input a security parametersample primes p, q (with
polynomial dependence on,the security parameter), compute N = pq, and sample aseed value
u ∈ QRN, u _= 1. Output (N, u) as params.•Accumulate(params,C) → A. On input params
(N, u) and a set of prime numbers C ={c1, . . . , ci | c ∈ [A, B]},10 compute the accumulator
Aasuc1c2···cn mod N.10See Appendix A for a more precise description. •
GenWitness(params, v,C) → w. Oninputparams(N, u), a set of prime numbers C as
described above,and a value v ∈ C, the witness w is the accumulationof all the values in C
besides v, i.e., w =Accumulate(params,C\ {v}).• AccVerify(params,A, v, ω) → {0, 1}. On
inputparams(N, u), an element v, and witness ω, computeA_ ≡ ωvmod N and output 1 if and
only if A_ = A,vis prime, and v ∈ [A, B] as defined previously.For simplicity, the description
above uses the full calculationofA. Camenisch and Lysyanskaya [12] observe that
theaccumulator may also be incrementally updated, i.e., givenan existing accumulator
NBN Sinhgad School Of Engineering,Pune Page 15

Anit is possible to add an elementxand produce a new accumulator value An+1 by
computingAn+1 = Axnmod N. We make extensive use of thisoptimization in our practical
implementation.Camenisch and Lysyanskaya [12] show that the accumulatorsatisfies a strong
collision-resistance property if theStrong RSA assumption is hard. Informally, this
ensuresthat no p.p.t. adversary can produce a pair (v, ω) such thatv / ∈ C and yet AccVerifyis
satisfied. Additionally, theydescribe an efficient zero-knowledge proof of knowledge that
a committed value is in an accumulator. We convert this intoa non-interactive proof using the
Fiat-Shamir transform andrefer to the resulting proof using the following
notation:NIZKPoK{(v, ω) : AccVerify((N, u),A, v, ω) = 1}.
B. Our Construction
We now describe a concrete decentralized e-cash scheme.Our scheme is secure assuming the
hardness of the StrongRSA and Discrete Logarithm assumptions, and the existence
of a zero-knowledge proof system.
We now describe the algorithms:
• Setup(1λ) → params. On input a security parameterrunAccumSetup(1λ) to obtain the
values (N, u). Next
generate primes p, q such that p = 2wq + 1 for w ≥ 1.
Select random generators g, h such that G = _g_ =
_h_ and G is a subgroup of Z
q ∗ . Output params=
(N, u, p, q, g, h).
• Mint(params) → (c, skc). Select S, r ← Z
q ∗ and
computec ← gShrmod p such that {c prime | c ∈[A, B]}.11 Set skc= (S, r) and output (c, skc).
• Spend(params, c, skc,R,C) → (π, S). If c / ∈ C
output⊥. Compute A ← Accumulate((N, u),C) and
ω← GenWitness((N, u), c,C). Output (π, S) where π
comprises the following signature of knowledge:12
π = ZKSoK[R]{(c,w, r) :
AccVerify((N, u),A, c, w) = 1 ∧ c = gShr}• Verify(params, π, S,R,C) → {0, 1}.
NBN Sinhgad School Of Engineering,Pune Page 16

2.3 INTEGRATING WITH BITCOIN
While the construction of the previous section gives an overview of our approach, we have
yet to describe how our techniques integrate with Bitcoin. In this section we address
the specific challenges that come up when we combine a decentralized e-cash scheme with
the Bitcoin protocol. The general overview of our approach is straightforward. To mint a
zerocoinc of denomination d, Alice runs Mint (params) → (c, skc) and stores skcsecurely.13
She then embeds c in the output of a Bitcoin transaction that spends d + fees classical
bitcoins. Once a mint transaction has been accepted into the block chain, c is included in the
global accumulator A, and the currency cannot be accessed except through a Zerocoin spend,
i.e., it is essentially placed into escrow.
Key Features :
a) Transactions.
b) Timestamp Server.
c) Proof-of-Work.
d) Network.
e) Incentive.
f) Reclaiming Disk Space.
g) Simplified Payment Verification.
h) Combining and Splitting Value.
i) Privacy.
j) Calculations.
k) Bitcoin, the system: the abstract protocol first introduced
l) By Nakamoto in the original publication [14];
m) bitcoins or BTC, the currency unit;
n) bitcoind, the reference implementation. Written by
o) Nakamoto as a proof-of-concept implementation,
p) bitcoind still remains the most used Bitcoin client.
NBN Sinhgad School Of Engineering,Pune Page 17

Figure 3: Bitcoin
Bitcoin is a digital currency that unlike traditional currencies does not rely on a centralized
authority. Instead Bitcoin relies on a network of volunteers that collectively implement a
replicated ledger and verify transactions. In this paper we analyze how Bitcoin uses a multi-
hop broadcast to propagate transactions and blocks through the network to update the ledger
replicas. We then use the gathered information to verify the conjecture that the propagation
delay in the network is the avoided as they are symptomatic for inconsistencies among the
replicas in the network. We then show what can be achieved by pushing the current protocol
to its limit with unilateral changes to the client’s behavior.
NBN Sinhgad School Of Engineering,Pune Page 18

CHAPTER 3
ANONYMITY & PERFORMANCE
3.1 REAL WORLD SECURITY AND PARAMETER CHOICE
A. Anonymity of Zerocoin
Definition 3.2 states that given two Zerocoin mints and onespend, one cannot do much better
than guess which mintedcoin was spent. Put differently, an attacker learns no morefrom our
scheme than they would from observing the mintsand spends of some ideal scheme.
However, even an idealscheme imposes limitations. For example, consider a casewhereN
coins are minted, then all N coins are subsequentlyspent. If another coin is minted after this
point, the size ofsince it is clear to all observers that the previous coins havebeen used. We
also stress that — as in many anonymitysystems — privacy may be compromised by an
attacker whomints a large fraction of the active coins. Hence, a lowerbound on the anonymity
provided is the number of coinsminted by honest parties between a coin’s mint and its
spend.An upper bound is the total set of minted coins.We also note that Zerocoin reveals the
number of mintedand spent coins to all users of the system, which providesa potential source
of information to attackers. This is incontrast to many previous e-cash schemes which reveal
thisinformation primarily to merchants and the bank. However,
we believe this may be an advantage rather than a loss,since the bank is generally considered
an adversarial party inmost e-cash security models. The public model of Zerocoinactually
removes an information asymmetry by allowing usersto determine when such conditions
might pose a problem.Lastly, Zerocoin does not hide the denominations used ina transaction.
In practice, this problem can be avoided bysimply fixing one or a small set of coin
denominations andexchanging coins until one has those denominations, or by
simply using Zerocoin to anonymizebitcoins.
B. Parameters
Generally, cryptographers specify security in terms of a single, adjustable security parameter
λ. Indeed, we have used this notation throughout the previous sections. In reality,
NBN Sinhgad School Of Engineering,Pune Page 19

however, there are three distinct security choices for Zerocoin which affect either the
system’s anonymity, its resilience to counterfeiting, or both.
These are:
1) The size of the Schnorr group used in the coin
commitments.
2) The size of the RSA modulus used in the accumulator.
3) λzkp, the security of the zero-knowledge proofs.
Commitments.Because Pedersen commitments are information theoretically hiding for any
the group used does not affect the long term anonymity of Zerocoin. The security of the
commitment scheme does, however, affect counterfeiting: an attacker who can break
the binding property of the commitment scheme can mint a zerocoin that opens to at least
two different serial numbers, resulting in a double spend. As a result, the Schnorr group must
be large enough that such an attack cannot be feasibly mounted in the lifetime of a coin. On
the other hand, the size of the signature of knowledge π used in coin spends increases linearly
with the size of the Schnorr group. One solution is to minimize the group size by announcing
fresh parameters for the commitment scheme periodically and forcing old zerocoins to expire
unless exchanged for new zerocoins minted under the fresh parameters.18 Since
all coins being spent on the network at time t are spent with the current parameters and all
previous coins can be converted to fresh ones, this does not decrease the anonymity
of the system. It does, however, require users to convert old zerocoins to fresh ones before
the old parameters expire. For our prototype implementation, we chose to use 1024 bit
parameters on the assumption that commitment parameters could be regenerated periodically.
We explore the possibility of extensions to Zerocoin that might enable smaller groups
in Section IX.Accumulator RSA key.Because generating a new accumulator
requires either a new trusted setup phase or generating a new RSA UFO [26], we cannot re-
key very frequently. As a result, the accumulator is long lived, and thus we truly need
long term security. Therefore we currently propose an RSA key of at least 3072 bits. We note
that this does not greatly affect the size of the coins themselves, and, because the proof
of accumulator membership is efficient, this does not havea large adverse effect on the
overall coin spend proof size.Moreover, although re-keying the accumulator is expensive,
NBN Sinhgad School Of Engineering,Pune Page 20

it need not reduce the anonymity of the system since the newparameters can be used to re-
accumulate the existing coinset and hence anonymize spends over that whole historyZero-
knowledge proof security λzkp. This parameter affectsthe anonymity and security of the zero-
knowledge proof.Italso greatly affects the size of the spend proof. Thankfully,As such, a
dishonest party would haveto expend roughly 2λzkp effort to forge a single coin or couldlink
a single coin mint to a spend with probability roughly1
2λzkp . As such we pick λzkp= 80 bits.
.
NBN Sinhgad School Of Engineering,Pune Page 21

3.2 PERFORMANCE
We consider the scenario of an attacker trying to generate an alternate chain faster than the
honest
chain. Even if this is acc
omplished, it does not throw the system open to arbitrary changes, such
as creating value out of thin air or taking money that never belonged to the attacker. Nodes
are
not going to accept an invalid transaction as payment, and honest nodes will never accept a
block
containing them. An attacker can only try to change one of his own transactions to take back
money he recently spent.
The race between the honest chain and an attacker chain can be characterized as a Binomial
Random Walk. The success event is the honest chain being extended by one block,
increasing its
lead by +1, and the failure event is the attacker's chain being extended by one block, reducing
the
gap by -1.
The probability of an attacker catching up from a given deficit is analogous to a Gambler's
Ruin problem. Suppose a gambler with unlimited credit starts at a deficit and plays
potentially an
infinite number of trials to try to reach breakeven. We can calculate the probability he ever
reaches breakeven, or that an attacker ever catches up with the honest chain, as follows [8]:
p = probability an honest node finds the next block
q = probability the attacker finds the next block
qz= probability the attacker will ever catch up from z blocks behind
qz={ 1 if p≤q
q/ pz if pq}
6
Identities Transactions Trusted
Third Party Counterparty Public
NBN Sinhgad School Of Engineering,Pune Page 22

Identities Transactions Public
New Privacy Model
Traditional Privacy Model
Given our assumption that p > q, the probability drops exponentially as the number of blocks
the
attacker has to catch up with increases. With the odds against him, if he doesn't make a lucky
lunge forward early on, his chances become vanishingly small as he falls further behind.
We now consider how long the recipient of a new transaction needs to wait before being
sufficiently certain the sender can't change the transaction. We assume the sender is an
attacker
who wants to make the recipient believe he paid him for a while, then switch it to pay back to
himself after some time has passed. The receiver will be alerted when that happens, but the
sender hopes it will be too late.
The receiver generates a new key pair and gives the public key to the sender shortly before
signing. This prevents the sender from preparing a chain of blocks ahead of time by working
on
it continuously until he is lucky enough to get far enough ahead, then executing the
transaction at
that moment. Once the transaction is sent, the dishonest sender starts working in secret on a
parallel chain containing an alternate version of his transaction.
The recipient waits until the transaction has been added to a block and z blocks have been
linked after it. He doesn't know the exact amount of progress the attacker has made, but
assuming the honest blocks took the average expected time per block, the attacker's potential
progress will be a Poisson distribution with expected value:
=z q
p
To get the probability the attacker could still catch up now, we multiply the Poisson density
for
each amount of progress he could have made by the probability he could catch up from that
point:
Σk
NBN Sinhgad School Of Engineering,Pune Page 23

=0
∞ k e−
k!
{⋅ q/ pz−k if k≤z
1 if kz}
Rearranging to avoid summing the infinite tail of the distribution...
1−Σ
k =0
zk e−
k! 1−q/ pz−k
Converting to C code...
#include <math.h>
doubleAttackerSuccessProbability(double q, int z)
{
double p = 1.0 - q;
double lambda = z * (q / p);
double sum = 1.0;
int i, k;
for (k = 0; k <= z; k++)
{
doublepoisson = exp(-lambda);
for (i = 1; i <= k; i++)
poisson *= lambda / i;
sum -= poisson * (1 - pow(q / p, z - k));
}
return sum;
}
NBN Sinhgad School Of Engineering,Pune Page 24

NBN Sinhgad School Of Engineering,Pune Page 25

CHAPTER 4
BASIC UTILIZATION & RESEARCH
4.1 ADVANTAGES & DISADVANTAGES
Advantages :
No third part interference.
Worldwide Coverage.
Null or Low transaction fees.
No upper limits on transfer accounts.
Disadvantages :
Trusted parties are required for Laundry operations.
No assurance that your money will be returned.
They are to be trusted blindly.
4.2 PREVIOUS WORK
A. E-Cash and Bitcoin
Electronic cash has long been a research topic for cryptographers. Many cryptographic e-
cash systems focus on user privacy and typically assume the existence of a semitrusted coin
issuer or bank. E-cash schemes largely break down into online schemes where users have
contact with a bank or registry and offline schemes where spending can occur even without a
network connection. Chaum introduced the first online cryptographic e-cash system [30]
based on RSA signatures, later extending this work to the offline setting [31] by de-
anonymizing users who double-spent. There is a general assumption that a majority of the
Bitcoin nodes are honest, but anyone can join a node to the Bitcoin network, and anyone can
get the entire transaction graph. An overview of Bitcoin and some of its shortcomings was
presented by Barber et. al. in [2].
NBN Sinhgad School Of Engineering,Pune Page 26

B. Anonymity
Numerous works have shown that “pseudonymized” graphs can be re-identified even under
passive analysis. Narayanan and Shmatikov [5] showed that real world social networks can
be passively de-anonymized. Similarly, Backstromet al. [37] constructed targeted attacks
against anonymizedsocial networks to test for relationships between vertices.Previously,
Narayanan and Shmatikov de-anonymizedusersin the Netflix prize data set by correlating
data fromIMDB [38].Bitcoin itself came into existence in 2009 and is now beginning to
receive scrutiny from privacy researchers. Deanonymization techniques were applied
effectively to Bitcoineven at its relatively small 2011 size by Reid and Harrigan [3].Ron and
Shamir examined thegeneral structure of the Bitcoinnetwork graph [1] after its nearly 3-fold
expansion. Finally, we have been made privately aware of two other early-stage
efforts to examine Bitcoin anonymity.
NBN Sinhgad School Of Engineering,Pune Page 27

CHAPTER 5
APPLICATIONS
APPLICATIONS OF ZEROCOIN
1. Online Shopping.
2. Web Design and Development.
3. Servers.
4. Café Restaurants, Bars and Lodges Hotels.
5. Medical legal & Safe Services.
6. Wellness & Fitness.
7. Price Redundancy.
8. Stock Exchanges.
9. Anonymous Money Transfer.
10. Drone Shipment.
11. E – Commerce Speedy System.
12. Purchase of Lowcost Goods.
13. Encryption & Security.
NBN Sinhgad School Of Engineering,Pune Page 28

CHAPTER 6
RESEARCH & FUTURE WORK
Zerocoin is a distributed e-cash scheme that provides strong user anonymity and coin
security under the assumption that there is a distributed, online, append-only transaction
store. We use Bitcoin to provide such a store and the backing currency for our scheme. After
providing general definitions, we proposed a concrete realization based on RSA
accumulators and non-interactive zero-knowledge signatures of knowledge. Finally, we
integrated our construction into Bitcoin and measured its performance Our work leaves
several open problems. First, although our scheme is workable, the need for a double-discrete
logarithm proof leads to large proof sizes and verification times. We would prefer a scheme
with both smaller proofs and greater speed. This is particularly important when it comes to
reducing the cost of third-party verification of Zerocoin transactions. There are several
promising constructions in the cryptographic literature, e.g., bilinear accumulators, mercurial
commitments [13, 39] . Second, Zerocoin currently derives both its anonymity and security
against counterfeiting from strong cryptographic assumptions at the cost of substantially
increased computationalcomplexity and size. As discussed in section VI-B, anonymity is
relatively cheap, and this cost is principallydriven by the anti-counterfeiting requirement,
manifestingitself through the size of the coins and the proofs used.InBitcoin, counterfeiting a
coin is not computationallyprohibitive, it is merely computationally costly, requiring theuser
to obtain control of at least 51% of the network. Thisprovides a possible alternative to our
standard cryptographicassumptions: rather than the strong assumption that computingdiscrete
logs is infeasible, we might construct ourscheme on the weak assumption that there is no
financialincentive to break our construction as the cost of computinga discrete log exceeds
the value of the resulting counterfeitcoins.For example, if we require spends to prove that
freshand random bases were used in the commitments for the corresponding mint transaction
(e.g., by selecting the bases for the commitment from the hash of the coin serial number and
proving that the serial number is fresh), then it appearsFinally, we believe that further
research could lead todifferenttradeoffs between security, accountability, andanonymity. A
common objection to Bitcoin is that it canfacilitate money laundering by circumventing
legally bindingfinancial reporting requirements.
NBN Sinhgad School Of Engineering,Pune Page 29

CHAPTER 7
APPENDIX
APPENDIX OF ZEROCOIN AND ITS SHORT IDEA :
ZERO-KNOWLEDGE PROOF CONSTRUCTION
The signature of knowledge π = ZKSoK[R]{(c,w, r) :AccVerify((N, u),A, c, w) = 1 ∧c =
gShr} is composed of two proofs that (1) a committed value c is accumulated and (2) that c is
a commitment to S. The former proof is detailed in [41, §3.3 and Appendix A]. The latter is a
double discrete log signature of knowledge that, although related to previous work [21,
§5.3.3], is new (at least to us). A proof of its security can be found in the full version of this
paper. It is constructed as follows: Given y1 = gaxbzhw.
Let l ≤ k be two security parameters and H :
{0, 1}∗→ {0, 1}kbe a cryptographic hash function.
Generate 2l random numbers r1, . . . ,rland
v1, . . . ,vl. Compute, for 1 ≤ i ≤ l, ti= gaxbrihvi.
The signature of knowledge on the message m is
(c, s1, s2, . . . , sl, s_
1, s_
2, . . . , s_
l), where:
c = H(m_y1_a_b_g_h_x_t1_ . . . _tl)
and
ifc[i] = 0 then si= ri, s
_
i = vi;
elsesi= ri− z, s
_
i = vi− wbri−z;
NBN Sinhgad School Of Engineering,Pune Page 30

CHAPTER 8
CONCLUSION
CONCLUSION :
Zerocoin gives boost to Digitization of Money.
The Basic objective is to avoid problems regarding privacy.
Best way it can provide utilization of single Currency.
Zerocoin generates various E – Cash schemes.
Makes scale to Large Networks.
Still much updates and advancement is needed for laundary operators.
Ciphered text should be used in broader sense pf working method.
Generally have wide scope in near future and can be implemented globally.
Best Anonymity ever provided by anu E – Cash schemes.
NBN Sinhgad School Of Engineering,Pune Page 31

BIBLIOGRAPHY
REFERENCES :
[1] D. Ron and A. Shamir, “Quantitative Analysis of the FullBitcoin Transaction
Graph,” Cryptology ePrint Archive, Report2012/584, 2012,
http://eprint.iacr.org/.
[2] S. Barber, X. Boyen, E. Shi, and E. Uzun, “Bitter to better– how to make bitcoin
a better currency,” in FinancialCryptography 2012, vol. 7397 of LNCS, 2012,
pp. 399–414.
[3] Zerocoin by mathewIanMiers, Christina Garman, Matthew Green, Aviel D.
RubinThe Johns Hopkins University Department of Computer Science,
Baltimore, USA{imiers, cgarman, mgreen, rubin}@cs.jhu.edu
[4] A.A. Ross, K. Nandakumar, and A.K. Jain, Handbook of Multibiometrics,
Springer, 2006.
[5] R. Cappelli et al., “Fingerprint Image Reconstruction from Standard Templates,”
IEEE Trans. Pattern Analysis and Machine Intelligence, Sept. 2007, pp. 1489-
1503.
[6] Bradbury, Danny (7 June 2013). "How anonymous is
Bitcoin?". CoinDesk (CoinDesk Ltd.). Retrieved 8 February 2014.
[7] www.zerocoin.org
[8] http://twitter.com/zerocoin_mathew.green
[9] www.bitcoinchannel.com/cryptocurreny
NBN Sinhgad School Of Engineering,Pune Page 32

NBN Sinhgad School Of Engineering,Pune Page 33












![ChallengeCoinUSA Challenge Coins that ROCK by Challenge Coin … · 2018. 1. 20. · CHALLENGE COIN USA COIN TEMPLATE COIN SIZE: 1.75"C] ART DETAILS: Please use this coin template](https://static.fdocuments.in/doc/165x107/5ff9c3994e904915c47dc15f/challengecoinusa-challenge-coins-that-rock-by-challenge-coin-2018-1-20-challenge.jpg)