Security@HDS - THIC · 2004-03-15 · Santa Clara CA 95050-2627 Phone: +1-408-970-7979,...
Transcript of Security@HDS - THIC · 2004-03-15 · Santa Clara CA 95050-2627 Phone: +1-408-970-7979,...

3 March 2004© 2003 Hitachi Data Systems 1
Securing and Protecting your Mission-critical Information in an Unsecure, Hostile World
Art EdmondsHitachi Data Systems Corp, 750 Central Expressway MS 3207
Santa Clara CA 95050-2627Phone: +1-408-970-7979, FAX:+1-408-562-5477
E-mail: [email protected]
Presented at the THIC Meeting at the Sony Auditorium, 3300 Zanker Rd, San Jose CA 95134-1940
March 9-10, 2004

3 March 2004
© 2003 Hitachi Data Systems
Security@HDS
Art EdmondsChief Security [email protected]
Santa Clara, California
January 22, 2004

3 March 2004© 2003 Hitachi Data Systems 3
Agenda
Overview
– Security Framework
Security Challenges
Security Standards
Security@ HITACHI Data Systems– Security Office– Philosophy– Approach– Security Implementations– Roadmap
Summary
Discussion

3 March 2004© 2003 Hitachi Data Systems 4
Security Overview
OverviewIndividuals are being held accountable for their company’s IP
Companies must meet SEC, HIPAA, and other regulatory agency requirements that govern loss or theft of data
– SEC draft for out of region disaster recovery– Check image retention for backup and online access– Personal medical records may need to be securely retained for longer than
human lifetimes (human lifespan + 30 years)
Insurance companies are increasing premiums up to 10x for those who do not have out of region disaster solutions in place
Fibre Channel Standards are being developed to meet corporate security needs that are simple yet comprehensive
– Design goals intend to leverage existing standards from IETF and existing de jure standards

3 March 2004© 2003 Hitachi Data Systems 5
Security Framework
1. Authentication
2. Authorization
3. Accounting / Audit
4. Integrity
5. Confidentiality
The order of implementation is significant and key

3 March 2004© 2003 Hitachi Data Systems 6
Data Life Cycle Management Trade Offs
Other technologies and security considerations:
Security = 20%Technology +
80% Best Practices (Human Factors)
Basic Cryptography– Public/Private keys, certificates
Non-repudiation– Hashing, WORM– CRC, checksum, Digital signature
Monitoring– Auto-detect Intrusion, Logs, Alarms
The order of security implementation steps is significant
1. Authentication– Certificates, Passwords, Biometrics
2. Access Control (Authorization)– ACL, Role or rules based
3. Accountability/Audit– Systems and activity logs
4. Integrity– Hashing,Mirrored cache, VPS,
5. Confidentiality– Encryption in-flight, at-rest
The Total Cost of Protection (TCP) determines the type and scope of the Security Solution– The security solution is also highly dependent on the value of the IP that needs protection– Data Value is also dependent on security and privacy requirements
Trade-offs: ease of doing business, ease of access to information, and cost of protection

3 March 2004© 2003 Hitachi Data Systems 7
New Customer Focus
Customer adoption well underway for …
Infrastructure consolidation
Business Continuity/Disaster recovery
Customers starting to focus on …
Moving up to the next level of consolidationfor improved efficiency and costs savings
Disaster Recovery– Offsite backup => Remote Copy– Remote Copy => Three Data Center Copy
Regulatory Compliance
Security and Privacy– Authentication, Authorization, Audit/Accounting, Integrity, Confidentiality

3 March 2004© 2003 Hitachi Data Systems 8
Enterprise Security Challenge
Ensure protection and privacy of stored data (Intellectual Property)– Explosion of sensitive data
Valued, Trusted, RegulatedAccess to data from anywhere, anytime
– Greater accessibility of storage: LAN, NAS, SAN, MAN/WAN, Internet, wireless
Distributed Storage, People, Locations, Networks, SystemsManagement Access Points
– Current security provisions in the infrastructure are insufficientFirewalls, VPNs, DMZs, proxies, VLANs and access controls (ACLs) focus on protecting internal systems from the perimeter (EDGE Security)SANs can be directly connected to the Internet via gatewaysNeed both CORE and EDGE (traditional) security

3 March 2004© 2003 Hitachi Data Systems 9
Storage Concentrates Data Exposure
StorageNetworks
Switches,TransportNodes
Applications
ApplicationServers
DataStorage
Management
ManagedServices
Consolidation Vaulting
“Data“Data--atat--Rest”Rest”
“Data“Data--inin--Flight”Flight”
Access PointsAccess PointsCampus,Campus,
MAN/WAN,MAN/WAN,Wireless, InternetWireless, Internet
Access PointsAccess PointsCampus,Campus,
MAN/WAN,MAN/WAN,Wireless, InternetWireless, Internet
Firewalls, VPNs, IDS,Antivirus,
AuthenticationAuthentication
Disaster Recovery
NEW
CORE SECURITY
EDGE SECURITY

3 March 2004© 2003 Hitachi Data Systems 10
Standards Bodies Security Activities
The spirit of the Storage Industry security effort is to leverage existing technology
Fibre Channel Security Protocol (FC-SP: ANSI/T11)– Security Infrastructure
Certificate (PKI)Password-based (CHAP, FCPAP. Operator-administered)
– AuthenticationSLAP/FCAP/ . . .CHAP/FCPAP/ . . .DH-CHAP
– Authorization & Access ControlFabric-Wide Security PoliciesPort Binding (Nx_Port to Nx_Port by WWN)
– Integrity & ConfidentialityESP (RFC 2406), IKEv2, . . .

3 March 2004© 2003 Hitachi Data Systems 11
Fabric Security Architecture
PKI // Password Administration // Shared-Secret Administration
FCAP // FCPAP // DH-CHAP
Fabric Asymmetry / Fabric-wide Security Policies (ACLs)
ESP (Encapsulating Security Payload)Confidentiality
Policy Distribution (Signatures / HMACs / ESP)
Integrity
Authorization(Access Control)
Authentication
Security Infrastructure

3 March 2004© 2003 Hitachi Data Systems 12
Fibre Channel Security Standards Status
Industry focus is on authentication, session integrity, and policy distribution
Fibre Channel Security Protocols (FC-SP) ANSI Standard
– Fibre Channel Security Standard due by June, 2004 (ANSI/T11 FC-SP)
– Expect security implementations to appear 1HCY2004
SNIA Storage Management Initiative Specification (SMI-S)
– SMI-S 1.0.2 due in March 2004. Some authentication built-in:
SSL 3.0 (MANDATORY)
http password
Port numbers now correct in Security Section
– Expect full security implementations to appear in SMI-S 1.1 (December 2004)

3 March 2004© 2003 Hitachi Data Systems 13
Security Office
The Security Office is comprised of members of the various Hitachi R&D teams. These resources come from RSD, SSD, SDL, SNSL, and HDS.
Mission Statement
The HITACHI Security Office is chartered with constantly improving the security of existing products and defining best practices. The long-term direction is to build security technology into new products from design through delivery.

3 March 2004© 2003 Hitachi Data Systems 14
Outline of Security Office Guiding Principles
Constantly solicit customer requirements and feedback with regards to storage security.
A key focus is to protect the management interfaces of storage networks.
Propose and advise to Hitachi R&D groups product designs that include storage security technology.
Increase security of information residing within or transiting through storage networks.
Provide mechanisms that protect customer information residing in our storage arrays as well as information in-transit between our storage arrays.
Work closely with and actively contribute to standards groups that are developing security for storage and data center environments.
Lead the efforts to implement storage security standards in Hitachi products.
Follow Industry and Government regulatory compliance trends related to storage security.
Encourage Security Industry best practices. Work with Partners, SNIA, T11, FCIA, etc.
Work with storage networking partners to understand and deploy end-to-end security solutions.

3 March 2004© 2003 Hitachi Data Systems 15
HDS Security Philosophy
Security is built into products from beginning of design design process
Leverage existing security standards & technologiestechnologies
Work with other vendors to ensure end-to-end securitysecurity– Information stored on HDS storage products (at-rest
rest data)– Information sent to users and other data centers (in-
(in-flight data)

3 March 2004© 2003 Hitachi Data Systems 16
HDS Security Approach
Identify potential security threat vectors
Rank threats
Verify highest risks
Mitigate risks– The real security focus: minimize the damage from a malicious penetration of
penetration of your company’s assets
Document corrective measures– Communicate security vulnerabilities and their fixes
Conduct ongoing stress tests– HDS uses nessus scan tool from nessus.org

3 March 2004© 2003 Hitachi Data Systems 17
Security Threat Discovery/Deployment Process
Discovery(CSO)
Test(RSD/SSD)
External / InternalSources
(Hitachi, Microsoft, Sec URL)
CountermeasurePlanning
(RSD/SSD)
Development(RSD/SSD)
Analysis(CSO)
QA(RSD/SSD)
Deployment(HDS)
PM
(1)
(3) (2)
Support Staff(San Diego)
Patches & softwareUpgrades
(3) Notification of formalcountermeasure (ECN)
t
Security ExploitDiscovered
(1) Initial notificationof Security Exploit
∆ t
ThreatAnalysis
(2) Notification ofinterim countermeasure (EN)
Development, Test, QA
Notify Customer BaseDeploy
CountermeasurePlanning

3 March 2004© 2003 Hitachi Data Systems 18
HDS Strategic Initiatives - Security is an Integral Part
Secure messagingInterchanges
Data Life Cycle Management - Data Cost of OwnershipData Life Cycle Management - Data Cost of Ownership
InfrastructureInfrastructure
SecuritySecurity
ComplianceCompliance
Fixed ContentFixed Content Business ContinuityBusiness Continuity Utility EnablementUtility Enablement

3 March 2004© 2003 Hitachi Data Systems 19
Security @HITACHI Data Systems (1)
Formation of Corporate Security Office with HDS/RSD/SD/SDL/SNSL/SSD– Constantly improve security of existing products– Include security features into roadmap for all phases of future products
development cycle
Best Practices– Harden SVP Hardware & Software
Recommended Security Patches (MicroSoft, CERT, etc.)Patch Management & Software Upgrade (ongoing)
– Standard Software Upgrades & MaintenanceWin2k SP3, SP4, SPx, …Apache 1.3.27 (SSL support)Others
Antivirus engine protection of Management Interface, eNAS, & iSCSI– Symantec 8.0 LiveUpdate
Perform regular security scans (nessus.org scan tool) on all products

3 March 2004© 2003 Hitachi Data Systems 20
Security @HITACHI Data Systems (2)
Best Practices (cont’d)– Security Exploit Threat Analysis, Countermeasures Development, and Risk
Mitigation
– Utilize 3rd Party Security Audit TeamCigital
– HiTrack (now)– Remote Copy (FCP, FCIP, iFCP, iSCSI)– MAN/WAN & Internet links
– Developing Professional Services Delivery ModulesBest PracticesSecurity Enhancements to Existing EcosystemsISO 17799, DHS, GSC RPI

3 March 2004© 2003 Hitachi Data Systems 21
Security @HITACHI Data Systems (3)
Standard Certification BodiesPreparing for ISO/IEC 15408 (Common Criteria)
– D/R
– Remote Copy
– DLCM
– Interfaces:
Fibre Channel: FCP, FICON
IP: (eNAS, iSCSI, etc.)
Multiple Data Center Extenders: FCIP, iFCP, iSCSI (with Encryption)
– Hardware and Storage Applications
Timeframe: In next release of HITACHI hardware products
NCSC ‘Orange Book’ B-level Security
Full INCITS/ANSI/T11.3 FC-SP Implementation
SMI-S 1.0.2 Development and Implementation

3 March 2004© 2003 Hitachi Data Systems 22
Security @HITACHI Data Systems (4)
Standards Organizations, Consortia, and Other Organizational InvolvementSNIA– Security Technical Working Group (TWG) (Co-Chair)
Define security technology for other SNIA TWGsSNIA SMI-S 1.0.2SNIA SMI-S 1.1
– SNIA CTP (Conformance Test Program)INCITS/ANSI/T11 Fibre Channel Protocols– T11.3 FC-SP (Fibre Channel Security Protocols Officer)
Global Security Consortium– Co-developing Risk Preparedness Index (RPI)– Membership includes:
HDS: First & Only Storage CompanyBig 4 (Deloitte & Touche, Ernst & Young, KPMG, PWC) Large Insurers & Re-insurers (AIG)
Department of Homeland Security– Working closely with Secretary Tom Ridge and his Staff

3 March 2004© 2003 Hitachi Data Systems 23
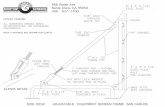
Current Security Implementation Status (Prototype @ FALL 2003 SNW)
Linux, NT, Solaris Servers
Digital Certificate
FCAP or DH-CHAP
DH-CHAP
Brocade DemoFCAP = Fibre Channel Authentication Protocol (ANSI T11.3 FC-SP)
DH-CHAP = Diffie-Hellman Challenge Handshake Authentication Protocol (ANSI T11.3 FC-SP)
Emulex LP9002 HBA
SNIA Security Demo
McData
Decru Encryption Appliance
RAID Array
No security
Stronger Security
RADIUS Server
CHAP(null DH)
Sun/qLogic SANbox
Brocade
Local or RADIUS key
qLogic HBAs
No security
The unsecured‘LAST MILE’
Good Security(also for iSCSI)
CHAP = Challenge Handshake Authentication Protocol(ANSI T11.3 FC-SP)

3 March 2004© 2003 Hitachi Data Systems 24
Summary
Disaster RecoveryStorage Area Management
(Standardized, single window pane for heterogeneous ecosystem)
CORE SECURITY
EDGE SECURITY
End-to-End Security
Data Lifecycle Management (DLCM)
End-to-End Secure, Business Continuance = PROTECTION (Data Replication + protection(D/R)) +
LOWER COST, SIMPLER MANAGEMENT (Single Management Interface) +
TIME-BASED & CONTEXT-BASED VALUATION OF DATA (DLCM) +
SECURE, CONFIDENTIAL, PROTECTED DATA INTERCHANGES
(Authentication, Authorization, Accounting/Audit, Integrity, Confidentiality & Privacy)

3 March 2004
© 2003 Hitachi Data Systems
Additional Materials
Art EdmondsChief Security [email protected]
Santa Clara, California
January 22, 2004

3 March 2004© 2003 Hitachi Data Systems 27
Trends of the IT Network
Car Navigation
InternetFirst Stage
Second Stage
Third Stage
Main Frame
PC
Server
)))
Note PC
Server
Note PCPDACellular
Phone
MultimediaKiosk
HomeAppliance
TV/STB
PC
DVD/HDD Recorder
Home Server
DVD Cam
UbiquitousNetwork
UbiquitousUbiquitousNetworkNetwork
OpenNetworkOpen
NetworkClosedNetworkClosedNetwork

3 March 2004© 2003 Hitachi Data Systems 28
Ubiquitous Network Environment
Town Access Point
Computing Resource
IPv6 インターネットIPv6 Internet
Home Network
Personal Area Network
WirelessSpot
ITS
Service Provider
Broadcasting

3 March 2004© 2003 Hitachi Data Systems 29
Partner / Competitor Activities
ANSI / T11.3 FC-SP– HBA and switch partners expect to implement authentication part of standard
by the end of 1HCY04 (DH-CHAP, null-DH-CHAP, FCAP)
– Competitive storage vendors are expected to implement authentication components of FC-SP 1.0 by the end of 2004
– Cisco / Andiamo expects to release DH-CHAP in Q4CY03 (OS 1.3 release)

3 March 2004© 2003 Hitachi Data Systems 30
Partner Security Deployments - Fall 2003 SNW
Brocade– SFOS Platform (2003)– FCAP– PKI– DH-CHAP (Secret, Security Association (SA), hash)
Emulex– DH-CHAP (LP9002 FCP HBA shown at Brocade Expo booth)
McData– Prototype CHAP (null DH)– SNW Interop Lab with Decru, RADIUS server, qLogic SANbox, qLogic
HBA, MTI RAID array (no security)
qLogic– Prototype CHAP (null DH)– FCP HBA and SAN switch

3 March 2004© 2003 Hitachi Data Systems 31
Standards Bodies Actions
ANSI / T11.3 FC-SP– Letter Ballot (public comment) February 2004– Expected ratification in June 2004– Partial implementation (DH-CHAP/FCAP/FCPAP) E1HCY04– Full Implementation (Authentication, Authorization, Audit/Accounting, Integrity,
Confidentiality/Privacy) by December 2004HBASwitchesStorage (DH-CHAP, IKEv2?)
SMI-S 1.0.1– HTTPS/SSL– Server-side certificates– Demo is planned for Spring 2004 SNW
DoD 5015.2-STD (Records Management & DLCM) (Introduced September 2003)
ISO 17799 (New)– Department of Homeland Security, DoD– Defines ten (10) areas of security compliance (best practices)

3 March 2004© 2003 Hitachi Data Systems 32
Security Office Focus
End-to-end security is a key focus
Vision:–R&D Security culture: Security technology built-in from the start