ryptographic Hash Functions
Transcript of ryptographic Hash Functions
Information Security
1
UNIT – 3
Cryptographic Hash Functions: Applications of Cryptographic Hash functions, Requirements
and security, Hash functions based on Cipher Block Chaining, Secure Hash Algorithm (SHA)
Message Authentication Codes: Message Authentication Requirements, Message Authentication
Functions, Requirements for Message Authentication Codes, Security of MACs, HMAC, MACs
based on Block Ciphers, Authenticated Encryption
Digital Signatures – RSA with SHA & DSS
Cryptographic Hash Functions
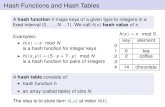
Hash functions are extremely useful and appear in almost all information security applications.
A hash function is a mathematical function that converts a numerical input value into another
compressed numerical value. The input to the hash function is of arbitrary length but output is always
of fixed length.
Values returned by a hash function are called message digest or simply hash values. The
following picture illustrated hash function
Features of Hash Functions
The typical features of hash functions are
Fixed Length Output (Hash Value)
Hash function coverts data of arbitrary length to a fixed length. This process is often
referred to as hashing the data.
In general, the hash is much smaller than the input data, hence hash functions are
sometimes called compression functions.
Since a hash is a smaller representation of a larger data, it is also referred to as a digest.
Hash function with n bit output is referred to as an n-bit hash function. Popular hash
functions generate values between 160 and 512 bits.
Efficiency of Operation
Generally for any hash function h with input x, computation of h(x) is a fast operation.
Computationally hash functions are much faster than a symmetric encryption.
Information Security
2
APPLICATIONS OF CRYPTOGRAPHIC HASH FUNCTIONS:
There are two direct applications of hash function based on its cryptographic properties.
1. Password Storage
Hash functions provide protection to password storage.
Instead of storing password in clear, mostly all logon processes store the hash values of
passwords in the file.
The Password file consists of a table of pairs which are in the form (user id, h(P)).
The process of logon is depicted in the following illustration −
An intruder can only see the hashes of passwords, even if he accessed the password. He can
neither logon using hash nor can he derive the password from hash value since hash function possesses
the property of pre-image resistance.
2. Data Integrity Check
Data integrity check is a most common application of the hash functions. It is used to generate the
checksums on data files. This application provides assurance to the user about correctness of the data.
The process is depicted in the following illustration –
The integrity check helps the user to detect any changes made to original file. It however, does
Information Security
3
not provide any assurance about originality. The attacker, instead of modifying file data, can change
the entire file and compute all together new hash and send to the receiver. This integrity check
application is useful only if the user is sure about the originality of file.
REQUIREMENTS & SECURITY:
Requirements for a hash function:
The purpose of a hash function is to produce a “fingerprint” of a file, message or other block of
data. To be useful for message authentication, a hash function H must have the following properties:
1. H van be applied to a block of data of any size
2. H produces a fixed length output.
3. H(x) is relatively easy to compute for any given x, making both hardware and software
implementations practical.
4. One-way property:- for any given value h, it is computationally infeasible to find x such that
H(x)=h. this sometimes referred to in the literature as the one way property.
5. Weak collision resistance:- for any given block x. it is computationally infeasible to find y≠x
with H(y)=H(x). this is referred as weak collision resistance.
6. Strong collision resistance:- it is computationally infeasible to find any pair (X,Y) such that
H(x)=H(y). this referred as strong collision resistance.
Security of Hash Functions:
In order to be an effective cryptographic tool, the hash function is desired to possess following
properties
Pre-Image Resistance
o This property means that it should be computationally hard to reverse a hash function.
o In other words, if a hash function h produced a hash value z, then it should be a difficult
process to find any input value x that hashes to z.
o This property protects against an attacker who only has a hash value and is trying to
find the input.
Second Pre-Image Resistance
Information Security
4
o This property means given an input and its hash, it should be hard to find a different
input with the same hash.
o In other words, if a hash function h for an input x produces hash value h(x), then it
should be difficult to find any other input value y such that h(y) = h(x).
o This property of hash function protects against an attacker who has an input value and
its hash, and wants to substitute different value as legitimate value in place of original
input value.
Collision Resistance
o This property means it should be hard to find two different inputs of any length that
result in the same hash. This property is also referred to as collision free hash function.
o In other words, for a hash function h, it is hard to find any two different inputs x and y
such that h(x) = h(y).
o Since, hash function is compressing function with fixed hash length, it is impossible for
a hash function not to have collisions. This property of collision free only confirms that
these collisions should be hard to find.
o This property makes it very difficult for an attacker to find two input values with the
same hash.
o Also, if a hash function is collision-resistant then it is second pre-image resistant.
HASH FUNCTIONS BASED ON CIPHER BLOCK CHAINING
A number of proposals have been made for hash functions based on using a cipher block
chaining technique, but without using the secret key. One of the first such proposals was that of Rabin
[RABI78]. Divide a message M into fixed-size blocks M1, M2, Á , MN and use a symmetric encryption
system such as DES to compute the hash code G as
This is similar to the CBC technique, but in this case, there is no secret key. As with any
hash code, this scheme is subject to the birthday attack, and if the encryption algorithm is DES and only a 64
-bit hash code is produced, then the system is vulnerable.
Furthermore, another version of the birthday attack can be used even if the opponent has access to
only one message and its valid signature and cannot obtain multiple signings. Here is the scenario: We
assume that the opponent intercepts a message with a signature in the form of an encrypted hash code
and that the unencrypted hash code is m bits long.
Use the algorithm defined at the beginning of this subsection to calculate the unencrypted hash
code G.
Construct any desired message in the form Q1, Q2, ………, QN - 2.
Compute Hi = E(Qi, Hi - 1) for 1 … i … (N - 2).
Generate 2m/2 random blocks; for each block X, compute E(X, HN ,2). Generate an additional 2m/
2 random blocks; for each block Y, compute D(Y, G), where D is the decryption function correspond
ing to E.
Based on the birthday paradox, with high probability there will be an X and Y such that
E(X, HN - 2) = D(Y, G).
Form the message Q1, Q2, Á , QN - 2, X, Y. This message has the hash code G and therefore can be
Information Security
5
used with the intercepted encrypted signature.
This form of attack is known as a meet-in-the-middle
attack. A number of researchers have proposed refinements
intended to strengthen the basic block chaining
approach. For example, Davies and Price [DAVI89] describe the variation:
However, both of these schemes have been shown to be vulnerable to a variety of
attacks [MIYA90]. More generally, it can be shown that some form of birthday
attack will succeed against any hash scheme involving the use of cipher block chain-
ing without a secret key, provided that either the resulting hash code is small enough (e.g., 64 bits or less)
or that a larger hash code can be decomposed into independent subcodes
SECURE HASH ALGORITHM
Introduction:
The Secure Hash Algorithm is a family of cryptographic hash functions developed by the
NIST (National Institute of Standards & Technology).
SHA is based on the MD4 algorithm and its design closely models MD5.
SHA-1 is specified in RFC 3174.
Purpose: Authentication, not encryption.
SHA-1 logic:
o The algorithm takes a message with maximum of length of less than 264 bits.
o Produce output is 160 bits message digest.
o The input is processed 512 bits block.
Processed Steps:
Algorithm processing Steps:
Step1: Append Padding Bits
Step 2: Append Length
Step 3: Initialize MD Buffer
Step 4: Process Message in 512 bit (16-Word) Blocks
Step 5: Output
Step-1: Appending Padding Bits.
The original message is "padded" (extended) so that its length (in bits) is congruent to 448,
modulo 512. The padding rules are:
Information Security
6
The original message is always padded with one bit "1" first.
Then zero or more bits "0" are padded to bring the length of the message up to 64 bits fewer
than a multiple of 512.
Step-2: append length:
a block of 64 bits is appended to the message. This block is treated as unsigned 64 bit integers
(most significant byte first) and contains the length of the original message.
Step-3: Initialize MD buffer:
160 bit buffer is used to hold intermediate and final results of the hash function. This buffer
can be represented as five 32 bit registers (A, B,C,D,E). the register are initialized to the following 32
bit integers
Word A is initialized to: 0x67452301.
Word B is initialized to: 0xEFCDAB89.
Word C is initialized to: 0x98BADCFE.
Word D is initialized to: 0x10325476.
Word E is initialized to: 0xC3D2E1F0
Step 4: Process Message in 512 bits:
this algorithm consist 4 rounds of 20 steps each. Four rounds have similar structures, but each
uses a different primitive logical function, we refer it as f1, f2, f3 and f4. Each round takes input the
current 512 bit blocks being processed ( Yq ) and the 160 bit buffer value a ABCDE and updates the
contents of the buffer. Each round also make use of an additive constant Kt where 0 ≤ t ≤ 79 indicates
one of the 80 steps across four rounds.
The output of 4th round added to the input to the 1st round (CVq) to produce CVq+1.
Information Security
7
Step-5: output:
after all L 512 bits block have been processed, the output from the Lth stage is the 160 bit
message digest.
The behavior of SHA-1can be summarized as:
CV0=IV
CVq+1=SUM32 (CVq, ABCDEq)
MD=CVL
IV initialize value of the ABCDE buffer define in step-3
ABCDEQ output of last round of qth message block.
Lnumber of block (512 bit) in message
SUM32addition modulo 232
MD final message Digest Value.
Information Security
8
SHA-1 Compression Function:
The logic in each of the 80 steps of the processing of one 512 bit block each round is of the form
(Figure 12.6)
o A,B,C,D,E(E+f(t,B,C,D)+S5(a)+Wt+Kt),A,S30(B),C,D
o A,B,C,D,E The five words of the buffer
o t Step number; 0 ≤ t ≤ 79
o f(t,B,C,D) Primitive logical function for step t
o SK circular left shift(rotation of the 32 bit argument by k bits
o Wt a 32 bit word derived from the current 512 bit input block
o Kt an additive constant; four distinct values are used, as defined previously
o + addition modulo 232
Message Authentication Codes
MESSAGE AUTHENTICATION Message authentication is a procedure to verify that received messages come from the
alleged source and have not been altered. Message authentication may also verify sequencing
and timeliness. It is intended against the attacks like content modification, sequence
modification, timing modification and repudiation. For repudiation, concept of digital
signatures is used to counter it. There are three classes by which different types of functions
that may be used to produce an authenticator. They are:
1. Message encryption–the cipher text serves as authenticator
2. Message authentication code (MAC)–a public function of the message and a secret
key producing a fixed-length value to serve as authenticator. This does not provide a
digital signature because A and B share the same key.
3. Hash function–a public function mapping an arbitrary length message into a fixed-
A,B,C,D,E(E +f(t,B,C,D) +S5(A)+Wt+Kt),A,S30(B),C,D
Information Security
9
length hash value to serve as authenticator. This does not provide a digital signature
because there is no key.
MESSAGE ENCRYPTION:
Message encryption by itself can provide a measure of authentication. The analysis
differs for conventional and public-key encryption schemes. The message must have come
from the sender itself, because the cipher text can be decrypted using his (secret or public) key.
Also, none of the bits in the message have been altered because an opponent does not know
how to manipulate the bits of the cipher text to induce meaningful changes to the plaintext.
Often one needs alternative authentication schemes than just encrypting the message.
Sometimes one needs to avoid encryption of full messages due to legal requirements.
Encryption and authentication may be separated in the system architecture.
The different ways in which message encryption can provide authentication,
confidentiality in both symmetric and asymmetric encryption techniques is explained with the
table below:
MESSAGE AUTHENTICATION CODE
An alternative authentication technique involves the use of a secret key to generate a
small fixed-size block of data, known as cryptographic checksum or MAC, which is appended
to the message. This technique assumes that both the communicating parties say A and B share a
common secret key K. When A has a message to send to B, it calculates MAC as a function C of
key and message given as:
MAC=Ck(M)
The message and the MAC are transmitted to the intended recipient, who upon receiving
performs the same calculation on the received message, using the same secret key to generate a
new MAC. The received MAC is compared to the calculated MAC and only if they match, then:
The receiver is assured that the message has not been altered: Any alternations been
done the MAC’s do not match.
The receiver is assured that the message is from the alleged sender: No one except the
sender has the secret key and could prepare a message with a proper MAC.
If the message includes a sequence number, then receiver is assured of proper sequence
as an attacker cannot successfully alter the sequence number.
Basic uses of Message Authentication Code (MAC) are shown in the figure:
Information Security
10
There are three different situations where use of a MAC is desirable:
If a message is broadcast to several destinations in a network (such as a military control
center), then it is cheaper and more reliable to have just one node responsible to evaluate the
authenticity –message will be sent in plain with an attached authenticator.
If one side has a heavy load, it cannot afford to decrypt all messages –it will just check the
authenticity of some randomly selected messages.
Authentication of computer programs in plaintext is very attractive service as they need not be
decrypted every time wasting of processor resources. Integrity of the program can always be checked
by MAC.
MESSAGE AUTHENTICATION CODE BASED ON DES
The Data Authentication Algorithm, based on DES, has been one of the most widely used
MACs for a number of years. The algorithm is both a FIPS publication (FIPS PUB 113) and an
ANSI standard (X9.17). But, security weaknesses in this algorithm have been discovered and it is
being replaced by newer and stronger algorithms. The algorithm can be defined as using the
cipher block chaining (CBC) mode of operation of DES shown below with an initialization vector
of zero.
The data (e.g., message, record, file, or program) to be authenticated are grouped into
contiguous 64-bit blocks: D1, D2,..., DN. If necessary, the final block is padded on the right with
zeroes to form a full 64-bit block. Using the DES encryption algorithm, E, and a secret key, K, a
data authentication code (DAC) is calculated as follows:
Information Security
11
The DAC consists of either the entire block ON or the leftmost M bits of the block, with
16≤ M ≤ 64. Use of MAC needs a shared secret key between the communicating parties and also
MAC does not provide digital signature. The following table summarizes the confidentiality and
authentication implications of the approaches shown above.
HASH FUNCTION
A variation on the message authentication code is the one-way hash function. As with
the message authentication code, the hash function accepts a variable-size message M as
input and produces a fixed-size hash code H(M), sometimes called a message digest, as
output. The hash code is a function of all bits of the message and provides an error- detection
capability: A change to any bit or bits in the message results in a change to the hash code. A
variety of ways in which a hash code can be used to provide message authentication is shown
below and explained stepwise in the table.
Information Security
13
MESSAGE AUTHENTICATION REQUIREMENTS
Disclosure: Release of message contents to any person or process not possessing the appropriate
cryptographic key.
Traffic analysis: Discovery of the pattern of traffic between parties. In a connection-oriented
application, the frequency and duration of connections
could be determined. In either a connection-oriented or connectionless environ-
ment, the number and length of messages between parties could be determined.
Masquerade: Insertion of messages into the network from a fraudulent source. This includes the
creation of messages by an opponent that are purported to come from an authorized entity.
Also included are fraudulent acknowledgments of message receipt or non-receipt by someone
other than the message recipient.
Content modification: Changes to the contents of a message, including insertion,
deletion, transposition, and modification.
Sequence modification: Any modification to a sequence of messages between parties, including
insertion, deletion, and reordering.
Timing modification: Delay or replay of messages. In a connection-
oriented application, an entire session or sequence of messages could be a replay of some
previous valid session, or individual messages in the sequence could be delayed or replayed. In a c
onnectionless application, an individual message (e.g., data- gram) could be delayed or replayed.
Source repudiation: Denial of transmission of message by source.
Destination repudiation: Denial of receipt of message by destination.
Information Security
14
MESSAGE AUTHENTICATION FUNCTIONS Message Authentication :
A mechanism of source used to notify the integrity of message
Assures the data received are exactly as sent (i.e. contain no modification,
insertion ,deletion or replay)
Assures that identity of the sender is valid
When a hash function is used to provide message authentication, the hash
function value is often referred to as a message digest.
Authentication function is of two levels of functionality :
Lower Value produces an authenticator value used to authenticate a message.
Higher Value : indicates a receiver to verify the authenticity of message.
SECURITY OF MACs
With encryption algorithms and hash functions, we can group attacks on MACs into two
categories: brute-force attacks and cryptanalysis.
Brute-Force Attacks
A brute-force attack on a MAC is a more difficult undertaking than a brute-force attack on a
hash function because it requires known message-tag pairs. Let us see
why this is so. To attack a hash code, we can proceed in the following way. Given a fixed
message x with n-bit hash code h = H(x), a brute-force method of finding a
collision is to pick a random bit string y and check if H(y) = H(x). The attacker can
do this repeatedly off line. Whether an off-
line attack can be used on a MAC algorithm depends on the relative size of the key and the tag.
To proceed, we need to state the desired security property of a MAC algo- rithm, which can be
expressed as follows.
Computation resistance: Given one or more text-MAC pairs [xi, MAC(K, xi)],
it is computationally infeasible to compute any text-MAC pair [x, MAC(K, x)] for any new
input x |=xi.
In other words, the attacker would like to come up with the valid MAC code for a given
message x. There are two lines of attack possible: attack the key space and attack the MAC value. We
examine each of these in turn.
If an attacker can determine the MAC key, then it is possible to generate a
valid MAC value for any input x. Suppose the key size is k bits and that the attacker has one known text–
tag pair. Then the attacker can compute the n-bit tag on the
known text for all possible keys. At least one key is guaranteed to produce the cor-
rect tag, namely, the valid key that was initially used to produce the known text–tag pair. This phase of
the attack takes a level of effort proportional to 2k (that is, one
operation for each of the 2k possible key values). However, as was described earlier,
because the MAC is a many-to-one mapping, there may be other keys that produce
the correct value. Thus, if more than one key is found to produce the correct value, additional text–tag
Information Security
15
pairs must be tested. It can be shown that the level of effort drops off rapidly with each additional
text–MAC pair and that the overall level of effort is roughly 2k [MENE97].
An attacker can also work on the tag without attempting to recover the key. Here, the objective
is to generate a valid tag for a given message or to find a message that matches a given tag. In either
case, the level of effort is comparable to that for attacking the one-way or weak collision-resistant
property of a hash code, or 2n. In the case of the MAC, the attack cannot be conducted off line without
further input; the attacker will require chosen text–tag pairs or knowl- edge of the key.
Cryptanalysis
As with encryption algorithms and hash functions, cryptanalytic attacks on MAC algorithms
seek to exploit some property of the algorithm to perform some attack other than an exhaustive search.
The way to measure the resistance of a MAC algorithm to cryptanalysis is to compare its strength to
the effort required for a brute-force attack. That is, an ideal MAC algorithm will require a
cryptanalytic effort greater than or equal to the brute-force effort.
HMAC HMAC (Hash-based Message Authentication Code) is a type of a message authentication code
(MAC) that is acquired by executing a cryptographic hash function on the data (that is) to be
authenticated and a secret shared key. Like any of the MAC, it is used for both data integrity and
authentication. Checking data integrity is necessary for the parties involved in communication.
HTTPS, SFTP, FTPS, and other transfer protocols use HMAC. The cryptographic hash function may
be MD-5, SHA-1, or SHA-256. Digital signatures are nearly similar to HMACs i.e they both employ a
hash function and a shared key. The difference lies in the keys i.e HMACs use symmetric key(same
copy) while Signatures use asymmetric (two different keys).
History
Processes and decisions pertinent to business are greatly dependent on integrity. If attackers
tamper this data, it may affect the processes and business decisions. So while working online over the
internet, care must be taken to ensure integrity or least know if the data is changed. That is when
HMAC comes into use.
Applications
Verification of e-mail address during activation or creation of an account.
Authentication of form data that is sent to the client browser and then submitted back.
HMACs can be used for Internet of things (IoT) due to less cost.
Whenever there is a need to reset the password, a link that can be used once is sent without
adding a server state.
It can take a message of any length and convert it into a fixed-length message digest. That is
even if you got a long message, the message digest will be small and thus permits maximizing
bandwidth.
Working of HMAC
Information Security
16
HMACs provides client and server with a shared private key that is known only to them. The
client makes a unique hash (HMAC) for every request. When the client requests the server, it hashes
the requested data with a private key and sends it as a part of request. Both the message and key are
hashed in separate steps making it secure. When the server receives request, it makes its own HMAC.
Both the HMACS are compared and if both are equal, the client is considered legitimate.
Formula for HMAC:
HMAC = hashFunc(secret key + message)
There are three types of authentication functions. They are message encryption, Message
authentication code, and hash functions. Major difference between MAC and hash (HMAC here) is the
dependence of a key. In HMAC we have to apply the hash function along with a key on the plain text.
The hash function will be applied to the plain text message. But before applying, we have to compute
S bits and then append it to plain text and after that apply hash function. For generating those S bits we
make use of a key that is shared between the sender and receiver.
Using key K (0 < K < b), K+ is generated by padding O’s on left side of key K until length
becomes b bits. The reason why it’s not padded on right is change(increase) in the length of key. b bits
because it is the block size of plain text. There are two predefined padding bits called ipad and opad.
All this is done before applying hash function to the plain text message.
ipad - 00110110
opad - 01011100
Now we have to calculate S bits
K+ is EXORed with ipad and the result is S1 bits which is equivalent to b bits since both K+
and ipad are b bits. We have to append S1 with plain text messages. Let P be the plain text message.
S1, p0, p1 upto Pm each is b bits. m is the number of plain text blocks. P0 is plain text block and b is
plain text block size. After appending S1 to Plain text we have to apply HASH algorithm (any variant).
Information Security
17
Simultaneously we have to apply initialisation vector (IV) which is a buffer of size n-bits. The result
produced is therefore n-bit hashcode i.e H( S1 || M ).
Similarly, n-bits are padded to b-bits And K+ is EXORed with opad producing output S2 bits. S2 is
appended to the b-bits and once again hash function is applied with IV to the block. This further
results into n-bit hashcode which is H( S2 || H( S1 || M )).
Advantages
1. HMACs are ideal for high-performance systems like routers due to the use of hash functions
which are calculated and verified quickly unlike the public key systems.
2. Digital signatures are larger than HMACs, yet the HMACs provide comparably higher
security.
3. HMACs are used in administrations where public key systems are prohibited.
Disadvantages
HMACs uses shared key which may lead to non-repudiation. If either sender or receiver’s key
is compromised then it will be easy for attackers to create unauthorized messages.
MACs BASED ON BLOCK CIPHERS : DAA & CMAC
We begin with an older algorithm, the Data Authentication Algorithm (DAA), which is now
obsolete. Then we examine CMAC, which is designed to overcome the deficiencies of DAA.
Data Authentication Algorithm
The Data Authentication Algorithm (DAA), based on DES, has been one of the
most widely used MACs for a number of years. The algorithm is both a FIPS publi-
cation (FIPS PUB 113) and an ANSI standard (X9.17). However, as we discuss sub- sequently, security
weaknesses in this algorithm have been discovered, and
it is being replaced by newer and stronger algorithms.
The algorithm can be defined as using the cipher block chaining (CBC) mode of
operation of DES (Figure 6.4) with an initialization vector of zero. The data (e.g., mes-
sage, record, file, or program) to be authenticated are grouped into contiguous 64-bit
blocks: D1, D2, .... , DN. If necessary, the final block is padded on the right with zeroes to form a full 64-
bit block. Using the DES encryption algorithm E and a secret key K,
a data authentication code (DAC) is calculated as follows (Figure 12.7).
Information Security
18
The DAC consists of either the entire block ON or the leftmost M bits of the block, with
16 <= M <= 64.
Cipher-Based Message Authentication Code (CMAC)
As was mentioned, DAA has been widely adopted in government and industry.
[BELL00] demonstrated that this MAC is secure under a reasonable set of security
criteria, with the following restriction. Only messages of one fixed length of mn bits
are processed, where n is the cipher block size and m is a fixed positive integer. As a simple example,
notice that given the CBC MAC of a one-block message X, say T = MAC(K, X), the adversary
immediately knows the CBC MAC for the two- block message X || (X { T) since this is once again T.
Black and Rogaway [BLAC00] demonstrated that this limitation could be overcome using
three keys: one key of length K to be used at each step of the cipher block chaining and two keys of
length n, where k is the key length and n is the cipher block length. This proposed
construction was refined by Iwata and Kurosawa so that the two n-bit keys could be derived
from the encryption key, rather than being provided separately [IWAT03]. This refinement,
adopted by NIST, is the Cipher-based Message Authentication Code (CMAC) mode of oper- ation for
use with AES and triple DES. It is specified in NIST Special Publication 800-38B.
First, let us define the operation of CMAC when the message is an
integer multiple n of the cipher block length b. For AES, b = 128, and for triple DES, b = 64.
The message is divided into n blocks (M1, M2, . . . , Mn). The algorithm makes use of a k-bit
encryption key K and an n-bit constant, K1. For AES, the key
size k is 128, 192, or 256 bits; for triple DES, the key size is 112 or 168 bits. CMAC is
calculated as follows (Figure 12.8).
Information Security
19
If the message is not an integer multiple of the cipher block length, then the final block is
padded to the right (least significant bits) with a 1 and as many 0s as necessary so that the final block
is also of length b. The CMAC operation then pro- ceeds as before, except that a different n-bit
key K2 is used instead of K1.
The two n-bit keys are derived from the k-bit encryption key as follows.
where multiplication ( . ) is done in the finite field GF(2n) and x and x2 are first- and second-
order polynomials that are elements of GF(2n). Thus, the binary representa- tion of x consists of n -
2 zeros followed by 10; the binary representation of x2 con- sists of n - 3 zeros followed by 100. The
finite field is defined with respect to an irreducible polynomial that is lexicographically first among all
such polynomials with the minimum possible number of nonzero terms. For the two approved block
sizes, the polynomials are x64 + x4 + x3 + x + 1 and x128 + x7 + x2 + x + 1.
Information Security
20
To generate K1 and K2, the block cipher is applied to the block that consists entirely of 0 bits. The first
subkey is derived from the resulting cipher text by a left
shift of one bit and, conditionally, by XORing a constant that depends on the block size. The second
subkey is derived in the same manner from the first sub key. This property of finite
fields of the form GF(2n).
AUTHENTICATED ENCRYPTION By far the oldest and perhaps also the best-known goal of cryptographic methods is the
protection of secrecy, or confidentiality, of data. This goal is achieved by employing encryption
techniques. Decryption can only be performed by someone possessing the right decryption key.
Of far greater relevance in most commercial applications is the protection of the correctness, or
authenticity, of data. This goal is achieved by means of digital signatures, or message authentication
codes (MACs). Both digital signatures and MACs compute a tag, which can be seen as a kind of
checksum computed over the message and using a secret key. Without the secret key, it is not possible
to compute a valid tag - hence all modifications applied to the data after the computation of the tag can
be detected easily.
Separation of the concepts confidentiality and authenticity is relatively new. Historically,
cryptographers believed that by using a strong encryption algorithm, they could ensure the authenticity
of data as well. And indeed, when we are talking about human-readable messages, this assumption is
justified. However, in the case of digital input data, both theory and practice have shown that the two
goals are quite different.
Hence, next to encryption algorithms, cryptographers developed authentication algorithms. For
example, the CBC-MAC algorithm operates by 'encrypting' the message with a block cipher in the
Cipher Block Chaining (CBC) mode of operation, and then outputs the last block of ciphertext
(possibly truncated) as tag. There are many variants on this scheme, most of them attempting to solve
the problems that arise when a legacy block cipher like the DES is used as the underlying block cipher.
When using the AES, even the simplest CBC-MAC construction is secure.
When the length of the message to be protected is relatively large compared to the block length
of the block cipher, the performance of the authentication step can be improved by using alternative
constructions. Most widely used is HMAC, which produces a tag by hashing a message and a key
together, operating at the speed of the underlying hash algorithm (e.g. SHA-256).
For applications that need to protect both confidentiality and authentication, the most
straightforward approach is to process the input twice: once to encrypt the data and once to compute
the authentication tag. This is called making two passes over the data. Recently, this approach has lost
its appeal, for several reasons. The first observation that can be made is that there seems to be room for
performance optimizations. Implementations may use the CBC mode of operation both for encryption
and authentication, and it may appear a bit odd to run essentially the same process twice, each time
with a different key. Secondly, and more importantly, there is the issue of ordering. Should we first
encrypt the message and subsequently authenticate the ciphertext, or should we authenticate the
message and subsequently encrypt both message and tag, or should we apply both in parallel on the
message? Thirdly, can we use any encryption algorithm together with any authentication algorithm, or
should we worry about mutual side-effects?
Information Security
21
In order to solve these matters, cryptographers have been looking with increased interest at a
different approach: the use of authenticated encryption modes. Here, a block cipher is used in a special
mode of operation, which simultaneously provides confidentiality and authentication. The most
efficient authenticated encryption modes provide authentication at a negligible additional cost
compared to encryption only. These modes all appear to be patented or patent-pending. The second
class of authenticated encryption modes offers no performance advantages compared to separate
encryption and authentication passes, but still solves the ordering issue and avoids worrying about
side-effects.
Digital Signatures
Digital signatures are the public-key primitives of message authentication. In the physical
world, it is common to use handwritten signatures on handwritten or typed messages. They are used to
bind signatory to the message. Similarly, a digital signature is a technique that binds a person/entity to
the digital data. This binding can be independently verified by receiver as well as any third party.
Digital signature is a cryptographic value that is calculated from the data and a secret key known only
by the signer.In real world, the receiver of message needs assurance that the message belongs to the
sender and he should not be able to repudiate the origination of that message. This requirement is very
crucial in business applications, since likelihood of a dispute over exchanged data is very high.
Model of Digital Signature
As mentioned earlier, the digital signature scheme is based on public key cryptography. The
model of digital signature scheme is depicted in the following illustration −
The following points explain the entire process in detail −
Each person adopting this scheme has a public-private key pair.
Generally, the key pairs used for encryption/decryption and signing/verifying are different. The
private key used for signing is referred to as the signature key and the public key as the
verification key.
Signer feeds data to the hash function and generates hash of data.
Hash value and signature key are then fed to the signature algorithm which produces the digital
signature on given hash. Signature is appended to the data and then both are sent to the verifier.
Information Security
22
Verifier feeds the digital signature and the verification key into the verification algorithm. The
verification algorithm gives some value as output.
Verifier also runs same hash function on received data to generate hash value.
For verification, this hash value and output of verification algorithm are compared. Based on
the comparison result, verifier decides whether the digital signature is valid.
Since digital signature is created by ‘private’ key of signer and no one else can have this key;
the signer cannot repudiate signing the data in future.
Digital Signature Requirements
1. The signature must be a bit pattern that depends on the message being signed.
2. The signature must use some information unique to the sender to prevent both forgery and
denial.
3. It must be relatively easy to produce the digital signature.
4. It must be relatively easy to recognize and verify the digital signature.
5. It must be computationally infeasible to forge a digital signature, either by constructing a new
message for an existing digital signature or by constructing a fraudulent digital signature for a
given message.
6. It must be practical to retain a copy of the digital signature in storage.
Approaches for Digital Signature:
Direct Digital Signature
Arbitrated Digital Signature
Direct Digital Signature:
The term direct digital signature refers to a digital signature scheme that involves only the
communicating parties (source, destination).
The validly of scheme depends on the security of the sender’s private key.
The sender later wishes to deny sending a particular message by claiming the private key was lost or
stolen or some other reason.
There is chance in stole the private key of a sender at some time T.
Arbitrated Digital Signature:
In this every signed message from a sender X to a receiver Y goes first to an arbiter A, who subjects
the message and its signature to a number of tests to check it origin and content. The message is then
dated and sent to Y.
This process is an indication that has been verified to the satisfaction of the arbiter.
By this process, it solves the direct Digital signature problem.
Sender X,
Arbiter A,
Receiver Y,
X construct message M and compute hash value H(M) then X transmitted “M+ Digital
Signature” to A.
Signature consists identity “IDx of X +hash value” of all encrypted using KXA (it is common
shared key between Sender X and Arbiter A).
A A decrypts the signature & checks the hash value to validate the message. Then transmit it
to Y by encryption it with KAY (it is common shared key between Arbiter A and Receiver Y).
the message include IDx and M & time Stam.
Y Decrypt it by using KAY
XA: M||EKXA[IDx||H(M)]
AY: EKAY[IDx||M|| EKXA[IDx||H(M)]||T]
Information Security
23
DIGITAL SIGNATURE STANDARD The National Institute of Standards and Technology (NIST) has published Federal Information
Processing Standard FIPS 186, known as the Digital Signature Standard
(DSS). The DSS makes use of the Secure Hash Algorithm (SHA) described in Chapter 12 and presen
ts a new digital signature technique, the Digital
Signature Algorithm (DSA). The DSS was originally proposed in 1991 and revised
in 1993 in response to public feedback concerning the security of the scheme. There
was a further minor revision in 1996. In 2000, an expanded version of the standard
was issued as FIPS 186-2, subsequently updated to FIPS 186-3 in 2009. This latest
version also incorporates digital signature algorithms based on RSA and on elliptic
curve cryptography. In this section, we discuss the original DSS algorithm.
The DSS Approach
The DSS uses an algorithm that is designed to provide only the digital signature function.
Unlike RSA, it cannot be used for encryption or key exchange. Nevertheless, it is a public-key
technique.
Figure 13.3 contrasts the DSS approach for generating digital signatures to that used with RSA.
In the RSA approach, the message to be signed is input to a hash function that produces a secure hash
code of fixed length. This hash code is then encrypted using the sender’s private key to form the
signature. Both the mes- sage and the signature are then transmitted. The recipient takes the message
and produces a hash code. The recipient also decrypts the signature using the sender’s public key. If
the calculated hash code matches the decrypted signature, the signa- ture is accepted as valid. Because
only the sender knows the private key, only the sender could have produced a valid signature.
The DSS approach also makes use of a hash function. The hash code is pro-
vided as input to a signature function along with a random number k generated for
this particular signature. The signature function also depends on the sender’s private key (PRa) and a set
of parameters known to a group of communicating principals.
We can consider this set to constitute a global public key (PUG).1 The result is a signature
consisting of two components, labeled s and r.
Information Security
24
At the receiving end, the hash code of the incoming message is generated. This plus the signature
is input to a verification function. The verification function also
depends on the global public key as well as the sender’s public key (PUa), which is paired with the
sender’s private key. The output of the verification function is a
value that is equal to the signature component r if the signature is valid. The signa-
ture function is such that only the sender, with knowledge of the private key, could
have produced the valid signature.
The Digital Signature Algorithm
The DSA is based on the difficulty of computing discrete logarithms (see Chapter 8) and is based
on schemes originally presented by ElGamal [ELGA85] and Schnorr [SCHN91].
Figure 13.4 summarizes the algorithm. There are three parameters that are pub-
lic and can be common to a group of users. A 160-bit prime number q is chosen. Next, a prime number p is
selected with a length between 512 and 1024 bits such that q divides (p -
1). Finally, g is chosen to be of the form h(p - 1)/q mod p, where h is an integer between 1 and (p - 1) with
the restriction that g must be greater than 1.2 Thus, the global public-
key components of DSA have the same for as in the Schnorr signature scheme.
With these numbers in hand, each user selects a private key and generates a
public key. The private key x must be a number from 1 to (q - 1) and should be cho-
sen randomly or pseudorandomly. The public key is calculated from the private key
as y = gx mod p. The calculation of y given x is relatively straightforward. However,
given the public key y, it is believed to be computationally infeasible to determine x,
which is the discrete logarithm of y to the base g, modp .
Information Security
25
To create a signature, a user calculates two quantities, r and s, that are func- tions of the public
key components (p, q, g), the user’s private key (x), the hash code of the message H(M), and an
additional integer k that should be generated randomly or pseudo-randomly and be unique for each
signing.At the receiving end, verification is performed using the formulas shown
in Figure 13.4.The receiver generates a quantity v that is a function of the public key com-
ponents, the sender’s public key, and the hash code of the incoming message. If this quantity matches the
r component of the signature, then the signature is validated.
Figure 13.5 depicts the functions of signing and verifying.The structure of the algorithm, as revealed in
Figure 13.5, is quite interesting. Note that the test at the end is on the value r, which does not depend
on the message at all. Instead, r is a function of k and the three global public-key
components. The multiplicative inverse of k (mod q) is passed to a function that also has as inputs
the message hash code and the user’s private key. The structure of this function is such that the
receiver can recover r using the incoming message and signature, the public key of the user, and the
global public key. It is certainly not obvious from Figure 13.4 or Figure 13.5 that such a scheme would
work. A proof is provided in Appendix K. Given the difficulty of taking discrete logarithms, it is
infeasible for an opponent to recover k from r or to recover x from s.
Another point worth noting is that the only computationally demanding task
in signature generation is the exponential calculation gk mod p. Because this value does not depend on
the message to be signed, it can be computed ahead of time.


























![Evolving Hash Functions using Genetic Algorithmsajiips.com.au/papers/V4.1/V4N1.4 - Evolving Hash Functions using... · hash function called "PKP Hash" by Peter.K.Pearson [5] that](https://static.fdocuments.in/doc/165x107/5e3486a76e7276290f0add90/evolving-hash-functions-using-genetic-evolving-hash-functions-using-hash.jpg)
![Programmable Hash Functions in the Multilinear Setting · Programmable hash functions. Programmable hash functions (PHFs) have been proposed in [18] as an abstraction of random oracles](https://static.fdocuments.in/doc/165x107/5f5aea052abf7142511471b2/programmable-hash-functions-in-the-multilinear-setting-programmable-hash-functions.jpg)