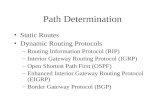
Routing Between Peers (BGP) Chapter 14. Routing Update Protocol Scope Routing update protocol was...
-
Upload
silvester-james -
Category
Documents
-
view
222 -
download
1
Transcript of Routing Between Peers (BGP) Chapter 14. Routing Update Protocol Scope Routing update protocol was...

Routing Between PeersRouting Between Peers (BGP) (BGP)
Chapter 14Chapter 14

Routing Update Protocol ScopeRouting Update Protocol Scope
Routing update protocol was used when Routing update protocol was used when Internet had single backboneInternet had single backbone Worked ok for thatWorked ok for that
Scheme does not scaleScheme does not scale Additional router traffic as number of sites growsAdditional router traffic as number of sites grows Internet routers cannot communicate directlyInternet routers cannot communicate directly
Do not share a common networkDo not share a common network Networks owned & managed by independent Networks owned & managed by independent
groupsgroups

Summary:Summary: Although it is desirable for routers to Although it is desirable for routers to
exchange routing information, it is impractical exchange routing information, it is impractical for all routers in an arbitrarily large internet to for all routers in an arbitrarily large internet to participate in a single routing update participate in a single routing update protocol.protocol.

Practical Limit on Group SizePractical Limit on Group Size
How large is “too large”?How large is “too large”? Answer depends on:Answer depends on:
Algorithm being used to exchange informationAlgorithm being used to exchange information
Capacity of the networkCapacity of the network
Details of routing protocolDetails of routing protocol Two issues:Two issues:
DelayDelay
OverheadOverhead

DelayDelay Look at Distance-Vector protocolLook at Distance-Vector protocol
To inform about a changeTo inform about a change Router receives new information Router receives new information Updates routing tableUpdates routing table Forwards information to neighborsForwards information to neighbors
In an internet with In an internet with NN routers in a linear topology routers in a linear topology NN steps are required steps are required
NN must be limited for rapid distribution of info must be limited for rapid distribution of info
OverheadOverhead More routers means more trafficMore routers means more traffic Size of messages can grow as routers and Size of messages can grow as routers and
networks increasenetworks increaseSize of messages must be limitedSize of messages must be limitedOtherwise, routing traffic not small % of total trafficOtherwise, routing traffic not small % of total traffic

Most managers follow simple heuristicMost managers follow simple heuristic For WANFor WAN
Allow a dozen routers to participate in single routing Allow a dozen routers to participate in single routing information protocolinformation protocol
For LANFor LANApproximately five times as many can participateApproximately five times as many can participate
General rule; many exceptionsGeneral rule; many exceptions Internet is not staticInternet is not static May implement May implement traffic monitoringtraffic monitoring scheme scheme
Listens to network and records statisticsListens to network and records statistics Network utilization; packets carrying routing messagesNetwork utilization; packets carrying routing messages

Extra HopsExtra Hops
Must limit routers that participate in a Must limit routers that participate in a single routing protocolsingle routing protocol Has consequencesHas consequences
Some routers will be outside the groupSome routers will be outside the group
Outsider could make a member a defaultOutsider could make a member a default
Like core/noncore router schemeLike core/noncore router scheme Routing will be suboptimalRouting will be suboptimal Do not even need a large number of routers for thisDo not even need a large number of routers for this

Suppose default for RSuppose default for R33 is R is R11
Will have non-optimal route to RWill have non-optimal route to R22
Cannot use ICMP redirect (only goes to source)Cannot use ICMP redirect (only goes to source) Extra hop problemExtra hop problem
Works correctly but is inefficientWorks correctly but is inefficient Non-participating routers must learn from Non-participating routers must learn from
participating routersparticipating routers
Figure 14.1

Autonomous System ConceptAutonomous System Concept
Just looking at mechanics of routingJust looking at mechanics of routing What are the administrative issues?What are the administrative issues? Take a different viewpointTake a different viewpoint
Do not think of as multiple independent networksDo not think of as multiple independent networks
There is a single administrative authority for allThere is a single administrative authority for all Keep internal routes consistent and viableKeep internal routes consistent and viable Pick machine to tell outside about networks insidePick machine to tell outside about networks inside

Autonomous SystemAutonomous System Group of networks and routers controlled by Group of networks and routers controlled by
a single administrative authoritya single administrative authorityInside AS, routers have freedomInside AS, routers have freedom
Choose own methods of propagating, discovering, Choose own methods of propagating, discovering, validating, and checking consistency or routesvalidating, and checking consistency or routes
Each assigned an autonomous system numberEach assigned an autonomous system numberWhen routers in two ASs exchange routing When routers in two ASs exchange routing information, they learn each other’s numberinformation, they learn each other’s number
Each large ISP is considered an ASEach large ISP is considered an ASRouting between major ISPs is really routing among Routing between major ISPs is really routing among autonomous systemsautonomous systems

Exterior Gateway ProtocolExterior Gateway ProtocolEGPEGP Any protocol passing reachability info between Any protocol passing reachability info between
autonomous systemsautonomous systems Currently most TCP/IP internets use Currently most TCP/IP internets use BGPBGP
Border Gateway ProtocolBorder Gateway Protocol
Four versions; current is BGP-4 (what we will use)Four versions; current is BGP-4 (what we will use)
Each AS designates a router to speak BGPEach AS designates a router to speak BGP Usually select router near “edge” of the ASUsually select router near “edge” of the AS Hence term Hence term border gatewayborder gateway or or border routerborder router

Figure 14.2Figure 14.2

BGP CharacteristicsBGP Characteristics
BGP is unusualBGP is unusual Neither pure distance-vector or pure link stateNeither pure distance-vector or pure link state
CharacteristicsCharacteristics Inter-Autonomous System CommunicationInter-Autonomous System Communication
Designed for one AS to talk to anotherDesigned for one AS to talk to another Coordination Among Multiple BGP SpeakersCoordination Among Multiple BGP Speakers
AS may have multiple routers talking to outside ASAS may have multiple routers talking to outside AS
BGP can coordinate among the routersBGP can coordinate among the routers
Ensures consistent information propagatedEnsures consistent information propagated

Propagation of Reachability InformationPropagation of Reachability InformationAllows AS to advertise destination reachable in it or Allows AS to advertise destination reachable in it or through itthrough it
AS learns such information from other ASAS learns such information from other AS Next-hop ParadigmNext-hop Paradigm
Supply next hop info for each destination (like DV)Supply next hop info for each destination (like DV) Policy SupportPolicy Support
DV protocols advertise exactly the routing table infoDV protocols advertise exactly the routing table info
BGP can implement policies from local administratorBGP can implement policies from local administrator
Distinguish between destinations reachable by systems Distinguish between destinations reachable by systems in its AS versus those advertised to other ASsin its AS versus those advertised to other ASs

Reliable TransportReliable TransportUnusual: assumes reliable transportUnusual: assumes reliable transport
Thus, uses TCP for all communicationThus, uses TCP for all communication Path InformationPath Information
Does more than specify destinations and next hopDoes more than specify destinations and next hop
Includes path informationIncludes path information
Allows receiver to learn a series of ASs along a pathAllows receiver to learn a series of ASs along a path Incremental UpdatesIncremental Updates
Conserves bandwidthConserves bandwidth
Not pass all information in each update messageNot pass all information in each update message
Exchange full information onceExchange full information once
Successive messages carry incremental changesSuccessive messages carry incremental changes

Support for Classless AddressingSupport for Classless AddressingSupports CIDR addressingSupports CIDR addressing
Non-self identifying addresses; passes mask, tooNon-self identifying addresses; passes mask, too Route AggregationRoute Aggregation
Conserves bandwidthConserves bandwidth
Send single entry to represent multiple, related Send single entry to represent multiple, related destinationsdestinations
AuthenticationAuthenticationReceiver can authenticate messagesReceiver can authenticate messages
Allows verification of a senderAllows verification of a sender

BGP Functionality and Message TypesBGP Functionality and Message Types
BGP performs 3 basic functionsBGP performs 3 basic functions Initial peer acquisition and authenticationInitial peer acquisition and authentication
Peers establish TCP connectionPeers establish TCP connection Each side sends pos/neg reachability infoEach side sends pos/neg reachability info
Advertise reachable: send next hop infoAdvertise reachable: send next hop info
Declare one or more previous destinations Declare one or more previous destinations unreachableunreachable
Ongoing verification that connections Ongoing verification that connections functioning correctlyfunctioning correctly

Figure 14.3 The five basic message types in BGP

16-octet MARKER field marks beginning of msgs16-octet MARKER field marks beginning of msgs
2-octet LENGTH field is total msg length in octets2-octet LENGTH field is total msg length in octets Min size: 19 octets (no data); max size: 4096 octetsMin size: 19 octets (no data); max size: 4096 octets
1-octet TYPE field is one of the five types1-octet TYPE field is one of the five types
Figure 14.4Figure 14.4

BGP OPEN MessageBGP OPEN Message
Sent when peers establish TCP connectionSent when peers establish TCP connection Declare autonomous system numberDeclare autonomous system number Establish other operating parametersEstablish other operating parameters Contains header plus:Contains header plus:
Value for Value for hold timerhold timer Max # seconds between receipt of 2 successive messagesMax # seconds between receipt of 2 successive messages

VERSION VERSION is protocol version (4)is protocol version (4)HOLD TIME HOLD TIME is time to wait for a message from senderis time to wait for a message from sender
Receiver has timer; if expires, assumes sender no longer availableReceiver has timer; if expires, assumes sender no longer available
IDENTIFER IDENTIFER is IP address is IP address (must pick one if have multiple)(must pick one if have multiple)Last field optionalLast field optional
Authentication, capability negotiation, future: larger AS #’sAuthentication, capability negotiation, future: larger AS #’s
Get OPEN, send KEEPALIVE, then exchange infoGet OPEN, send KEEPALIVE, then exchange info
Figure 14.5Figure 14.5

BGP UPDATE MessageBGP UPDATE Message
OPEN and ACK, then exchange infoOPEN and ACK, then exchange info After peers create TCP connectionAfter peers create TCP connection
Use Use UPDATEUPDATE to advertise to advertise New destinations that are reachableNew destinations that are reachable Withdraw previous advertisementsWithdraw previous advertisements

Two parts: withdrawn destinations and new destinationsTwo parts: withdrawn destinations and new destinations
Length fields specify size of fields that followLength fields specify size of fields that follow If no destinations for that part, length is zeroIf no destinations for that part, length is zero
Discuss Discuss path attributespath attributes soon…. soon….
Figure 14.6Figure 14.6

Compressed Mask-Address Compressed Mask-Address PairsPairs
New and withdrawn destination fields New and withdrawn destination fields contain a list of IP addressescontain a list of IP addresses
Have to accommodate classless addressingHave to accommodate classless addressing Need address mask as wellNeed address mask as well
BGP uses compressed representationBGP uses compressed representation Does not actually send a bit maskDoes not actually send a bit mask Reduces message sizeReduces message size

Mask info encoded in single octet preceding addressMask info encoded in single octet preceding address Contains integer; specifies number of bits in the maskContains integer; specifies number of bits in the mask Mask bits are assumed to be contiguousMask bits are assumed to be contiguous
Address only contains octets covered by the maskAddress only contains octets covered by the mask LEN 8 or less: one address octet followsLEN 8 or less: one address octet follows 9 to 16: two; 17 to 24: three; 25 to 32: four9 to 16: two; 17 to 24: three; 25 to 32: four LEN can be zeroLEN can be zero
No address octet follows – corresponds to default routeNo address octet follows – corresponds to default route
Figure 14.7Figure 14.7

BGP Path AttributesBGP Path Attributes
BGP not pure distance-vector protocolBGP not pure distance-vector protocol Advertises more than next hopAdvertises more than next hop
Additional info is in the Additional info is in the path attributespath attributes field field Can specify:Can specify:
Next hop for advertised destinationsNext hop for advertised destinations
List of autonomous systems along the destination pathList of autonomous systems along the destination path
Whether path info learned from other AS or derived Whether path info learned from other AS or derived from within sender’s ASfrom within sender’s AS

Path attributes apply to all destinations in msgPath attributes apply to all destinations in msg If need different attributes for some destinations, If need different attributes for some destinations,
must send separate update messagemust send separate update message
Path attributes important for 3 reasonsPath attributes important for 3 reasons Allows receiver to check for routing loopsAllows receiver to check for routing loops
Sender can specify exact path thru ASs to destinationSender can specify exact path thru ASs to destination
If any AS appears twice, there is a loopIf any AS appears twice, there is a loop Allows receiver to implement policy constraintsAllows receiver to implement policy constraints
Ex: not want to send thru untrusted ASEx: not want to send thru untrusted AS Allows receiver to know source of all routesAllows receiver to know source of all routes
Info from inside AS or another ASInfo from inside AS or another AS
Collected by exterior, or interior, gateway protocolCollected by exterior, or interior, gateway protocol

Path attributes field contains list of itemsPath attributes field contains list of items Each item consists of triple:Each item consists of triple:
((typetype, , lengthlength, , valuevalue))
TypeType is 2 octets is 2 octets
LengthLength field 1 or 2 octets field 1 or 2 octets
Type field used to get size of length field; length field Type field used to get size of length field; length field used to get size of used to get size of valuevalue field field
Variable field sizes minimize space neededVariable field sizes minimize space needed

Figure 14.8 (a) The two-octet type field that appears before each BGP attribute path item, and (b) the meaning of each flag bit.
Figure 14.9 The BGP attribute type codes and the meaning of each.

BGP KEEPALIVE MessageBGP KEEPALIVE Message
Peers periodically exchange KEEPALIVE msgsPeers periodically exchange KEEPALIVE msgs Test network connectivityTest network connectivity Verify both peers still functioningVerify both peers still functioning
Message is only header; no dataMessage is only header; no data Total size is 19 octetsTotal size is 19 octets

Reasons for KEEPALIVE messagesReasons for KEEPALIVE messages Using TCPUsing TCP
TCP does not continually test endpointsTCP does not continually test endpoints
TCP TCP willwill report if cannot deliver message report if cannot deliver message Conserve bandwidthConserve bandwidth
Used to exchange routing info for connectivity testUsed to exchange routing info for connectivity test
Large routing messages wasted bandwidthLarge routing messages wasted bandwidth
Recall Recall hold timerhold timer Maximum time to wait without receiving a msgMaximum time to wait without receiving a msg Hold timer can be zeroHold timer can be zero
Means no KEEPALIVE messages usedMeans no KEEPALIVE messages used If greater than zeroIf greater than zero
KEEPALIVE interval should be 1/3 of hold timerKEEPALIVE interval should be 1/3 of hold timer
KEEPALIVE interval will never be less than 1 secondKEEPALIVE interval will never be less than 1 second Nonzero hold timer cannot be less than three secondsNonzero hold timer cannot be less than three seconds

Information from the Receiver’s PerspectiveInformation from the Receiver’s Perspective
An Exterior Gateway Protocol must do An Exterior Gateway Protocol must do more than propagate routing informationmore than propagate routing information Must make sure info is correct from outside viewMust make sure info is correct from outside view Two issuesTwo issues
PolicyPolicy Router inside AS may be able to reach destinations that Router inside AS may be able to reach destinations that
outside routers are prohibited from reachingoutside routers are prohibited from reaching
Optimal routesOptimal routes Router must advertise next hop that is optimal from the Router must advertise next hop that is optimal from the
outsider’s perspectiveoutsider’s perspective

RR22 must report reachability to networks 1 through 4 must report reachability to networks 1 through 4
Next hop: Net 1 thru RNext hop: Net 1 thru R11; Net 3 & 4 thru R; Net 3 & 4 thru R33; Net 2 thru R; Net 2 thru R22
Figure 14.10
Example of an autonomous system. Router R2 runs BGP and reports information from the outsider’s perspective, not from its own routing table.

Key Restriction of EGPsKey Restriction of EGPs
Seen that exterior protocols may advertise Seen that exterior protocols may advertise a subset of the networks they can reacha subset of the networks they can reach
More fundamental limitation imposed on More fundamental limitation imposed on exterior routing:exterior routing: They cannot communicate or interpret distanceThey cannot communicate or interpret distance Even if the distance metrics are availableEven if the distance metrics are available

Cannot transmit or compare route costsCannot transmit or compare route costs Unless the routes come from within same ASUnless the routes come from within same AS See why BGP labels origin of routing infoSee why BGP labels origin of routing info
Get advertisement from two different ASsGet advertisement from two different ASs
Have no way to compare the costs of the twoHave no way to compare the costs of the two
Advertisement only says that an AS provides a pathAdvertisement only says that an AS provides a path
BGP cannot be used as a routing algorithmBGP cannot be used as a routing algorithm Router may learn of two paths to same networkRouter may learn of two paths to same network Cannot know which is shorterCannot know which is shorter
No info about cost of routes across intermediate ASsNo info about cost of routes across intermediate ASs BGP is BGP is reachabilityreachability protocol, not routing protocol protocol, not routing protocol

AS does not include distance metric in infoAS does not include distance metric in info Must only advertise routes traffic should followMust only advertise routes traffic should follow Receiver can implement policy constraintsReceiver can implement policy constraints
But cannot choose a least cost routeBut cannot choose a least cost route
Restriction has surprising consequencesRestriction has surprising consequences

1. BGP does not provide for simultaneous use of 1. BGP does not provide for simultaneous use of multiple pathsmultiple paths
Can advertise multiple paths to a given networkCan advertise multiple paths to a given network But all traffic from one AS to another takes one pathBut all traffic from one AS to another takes one path
Outside AS use only one return path even if source Outside AS use only one return path even if source divides traffic among two or more pathsdivides traffic among two or more paths Delay and throughput between pair is asymetricDelay and throughput between pair is asymetric
2. BGP does not support load sharing on routers 2. BGP does not support load sharing on routers between arbitrary autonomous systemsbetween arbitrary autonomous systems
Two ASs may have multiple routers connecting themTwo ASs may have multiple routers connecting themWould like to balance traffic among the routersWould like to balance traffic among the routersBGP only allows dividing the load by networkBGP only allows dividing the load by network ASs can partition themselves into multiple subsetsASs can partition themselves into multiple subsets
Does not support more general load sharingDoes not support more general load sharing

3.3. If two or more WANs are interconnected at If two or more WANs are interconnected at multiple points, BGP alone is inadequate for multiple points, BGP alone is inadequate for optimal routingoptimal routing
– Special case of #2Special case of #2– Managers must manually configure which networks are Managers must manually configure which networks are
advertised by each exterior routeradvertised by each exterior router
4.4. Must have agreement on consistent scheme Must have agreement on consistent scheme for advertising reachabilityfor advertising reachability
– All autonomous systems must agreeAll autonomous systems must agree– BGP alone will not guarantee global consistencyBGP alone will not guarantee global consistency

Internet Routing ArchitectureInternet Routing Architecture
Routing information must be globally Routing information must be globally consistentconsistent Individual protocols may not guaranteeIndividual protocols may not guarantee
Such as BGPSuch as BGP
Only handles exchange between pairs of routersOnly handles exchange between pairs of routers Originally, core systems guaranteed consistencyOriginally, core systems guaranteed consistency
At any time, had exactly one path to each destinationAt any time, had exactly one path to each destination Cores went awayCores went away
No single mechanism available as a replacementNo single mechanism available as a replacement
No central mechanism to validate routes and No central mechanism to validate routes and guarantee global consistencyguarantee global consistency

Current routing architectureCurrent routing architecture Major ISPs connect to the Internet at Network Major ISPs connect to the Internet at Network
Access Points (NAP)Access Points (NAP)Also known as Also known as Internet Exchange PointsInternet Exchange Points (IXPs) (IXPs)
Engage in private peeringEngage in private peering Relationship is upstream, downstream, or transitRelationship is upstream, downstream, or transit
Use Use Routing RegistriesRouting Registries Helps assure routes are validHelps assure routes are valid Holds info about which ISPs own which blocks of addressesHolds info about which ISPs own which blocks of addresses But, many exist; no way to validate the registriesBut, many exist; no way to validate the registries
Black holes happenBlack holes happen Given address is not reachable from all parts of InternetGiven address is not reachable from all parts of Internet
Routing cannot be flawless without a centralized, Routing cannot be flawless without a centralized, authoritative registryauthoritative registry

BGP Notification MessageBGP Notification Message
NOTIFICATION messages are used for NOTIFICATION messages are used for control or when errors occurcontrol or when errors occur Errors are permanentErrors are permanent Sends NOTIFICATION message, closes TCP Sends NOTIFICATION message, closes TCP
connectionconnection

Figure 14.11Figure 14.11
Figure 14.12Figure 14.12

Figure 14.13Figure 14.13

SummarySummaryRouters must be partitioned into groupsRouters must be partitioned into groups Else volume of routing traffic intolerableElse volume of routing traffic intolerable Connected Internet composed of ASsConnected Internet composed of ASs
Each AS has single administrative authorityEach AS has single administrative authority
AS must advertise reachability informationAS must advertise reachability information
Border Gateway Protocol (BGP)Border Gateway Protocol (BGP) Most widely used EGPMost widely used EGP 5 message types (open, update, notification, 5 message types (open, update, notification,
keepalive, refresh)keepalive, refresh) Uses TCP, but has Uses TCP, but has keepalivekeepalive mechanism mechanism

Each ISP assigned to separate ASEach ISP assigned to separate AS Main boundary among ASs occur at IXPMain boundary among ASs occur at IXP
Peering occurs at these pointsPeering occurs at these points ISP uses BGP to communicate with peersISP uses BGP to communicate with peers
Advertise reachability of networks that can be reached Advertise reachability of networks that can be reached through itthrough it
Learn about networks in other ISPsLearn about networks in other ISPs Routing registries existRouting registries exist
Aid in validating advertisementsAid in validating advertisements
Problems can still occur because of no centralized, Problems can still occur because of no centralized, authoritative controlauthoritative control