Rc6 algorithm
-
Upload
chethan-chetu -
Category
Technology
-
view
140 -
download
4
Transcript of Rc6 algorithm

Internal Guide
Kavyashree Madam
Project Institution
RV-VLSI
The Group Anand P. T (1yd06ec002)
Chethan A. S
(1yd10ec033)
Gireesh K. G
(1yd10ec021)
Shree Yogeesh

Today’s Importance of secure communication systems.
Requirement of efficient cryptographic algorithm.
Numerous cryptographic algorithm
RC6 algorithm -> strong for immunities towards hacking.
Wide use of RC6, necessity of high performance design.
Concentration on less delay and logic blocks.
Primitives roles of the algorithm -> Multipliers & shifters.
Hence implementation of effective multipliers & shifters.
Studies suggest a desire on Vedic multiplier & barrel shifter.
FPGAs with highly attractive hardware options.

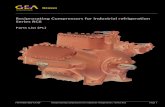
RC6 is a symmetric key block cipher derived from RC5.
Block size of 128 bits.
Flexibility of key size.
No key separation.
Operators involved are simple in function favourably.
High speed with minimal code memory.
provides a solid well tuned margin for security against well known
differential & linear attacks.
Max potential for parallelism when multiple streams are
processed.

RC6 ENCRYPTION
Plain
Text
Round
keys
Start_E
Reset
Clock
Memory
Vedic
Multiplier
Plain
Text
ReadyBarrel
Shifter
Arithmetic
& Logical
Operators
RC6 DECRYPTION
Memory
Vedic
Multiplier
Barrel
Shifter
Arithmetic
& Logical
Operators
RC6
CRYPTOGRAPHY

64 bit plain text.
Key length is16 bit.
QUESTA SIM for simulation and ALTERA Quartus II for
synthesis.
Hardware implementation on Altera DE2-115 board.

RC6 algorithm basic operations.
1. a + b :integer addition modulo 2w
2. a - b :integer subtraction modulo 2w
3. a ^ b :bitwise exclusive-or of w-bit words
4. a x b :integer multiplication modulo 2w
5. a <<< b :rotate the w-bit word a to the left by the amount
given by the least significant lgw bits of b
6. a >>> b :rotate the w-bit word a to the right by the amount
given by the least significant lgw bits of b




START
Is RESET=1?
Transfer data for Encryption
Is complete byte
transferred=1?
B = B + S [0], D = D + S [1]
for i = 1 to r do
{
t = (B _ (2B + 1)) <<< log w
u = (D _ (2D + 1)) <<<log w
A = ((A _ t) <<<u) + S [2i]
C = ((C _ u) <<<t) + S [2i+ 1]
(A; B; C; D) = (B; C; D; A)
}
A = A + S [2r + 2], C = C + S [2r + 3]
NO
YES
YES
YES
STOP

START
Is Ready_e=1?
Transfer data for Decryption
Is complete byte
transferred=1?
C = C - S [2r + 3], A = A - S [2r + 2]
for i = r downto 1 do
{
(A; B; C; D) = (D; A; B; C)
u = (D * (2D + 1)) <<<log w
t = (B *(2B + 1)) <<<log w
C = ((C – S [2i + 1])>>>t) _ u
A = ((A – S [2i])>>>u) _ t
}
D = D – S [1], B = B – S [0]
NO
NO
YES
YES
YES
STOP



It is clear that by application of Vedic method reduces power consumption by using less number of logic elements.
Hence layout area is reduced and high speed of computation is achieved.
Conventional
method
Vedic method
Total thermal
power dissipation
70.01mv 67.00mv
Core static
thermal power
dissipation
51.77mv 51.77mv
I/O thermal power
dissipation
18.23mv 15.23mv

Advantages
1) Fast and flexible
2) Secure
3) Support 32/64 bit processor
Disadvantages
1) Inter multiplications on rotations.
2) Not universally practical.

Internet E-Commerce.
Mobile telephone networks.
Bank automated teller machines.
Digital rights managements to restrict the use of copyrights
material.
Military applications.
Secured audio & videos transmission with high security.

Among various available popular cryptographic algorithms, it is
seen that RC6 provides batter security & high performance.
RC6 is a compact and simple block cipher.
Our studies reveal that multiplication and shifters are the major
bottlenecks as far as speed of the RC6 cipher is concerned.
Nevertheless, up to a great extent this high performance was
tackled using Vedic multiplier & barrel shifter in our design.
Consequently, the highest Speed/Area ratio can be achieved in
the same.

It can be worked with higher number of plain text bits & key
for real time operations.
In this project encryption/decryption cannot start until key
schedule algorithm is completely executed & all sub keys are
generated.
In algorithm it is seen that keys are needed faster than they are
generated.
So with extension to this thesis try to start process with key
already generated and parallel generate rest of keys.

THANK YOU