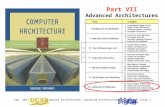
Jan. 2011Computer Architecture, Background and MotivationSlide 1 Part I Background and Motivation.
PURSUIT 2011Computer LabPURSUIT 2011Computer Lab Exploring a Framework for Developing the Future...
-
date post
21-Dec-2015 -
Category
Documents
-
view
213 -
download
0
Transcript of PURSUIT 2011Computer LabPURSUIT 2011Computer Lab Exploring a Framework for Developing the Future...

PURSUIT 2011 Computer LabPURSUIT 2011 Computer Lab
Exploring a Framework for Developing the Future
Internet: Lessons from the Y-Comm
ArchitectureGlenford Mapp
Principal Lecturer, Middlesex University

PURSUIT 2011 Computer LabComputer Lab
Outline of the Talk
• Motivation for the work
• Our approach
• Introduction to Y-Comm
• Peripheral Framework
• Areas of Work
• Conclusions

PURSUIT 2011 Computer LabComputer Lab
Motivation (looking backward)
• Originally we started with ubiquitous handover. – Fore-runner was work on the Cambridge
Wireless network which looked how you do handover between different wireless systems
• James Scott, Leo Patanapongpibul, Pablo Vidales
– YComm ended up looking at ubiquitous handover, Quality-of-Service, Security and Application environments/Service Platforms

PURSUIT 2011 Computer LabComputer Lab
Lesson -1.0• Each of these are big areas in themselves
– Can study each area on its own and that is what a lot of people are doing.
• End up with good papers but not something that you could take and build a real system
• We took the opposite viewpoint. – Try to describe the big picture first
• Develop the mechanisms but keep always keep the big picture in view

PURSUIT 2011 Computer LabComputer Lab
Lesson -0.5
• Don’t be foolish– Invent things only when you need to
• Y-Comm is not trying to invent new technologies for the sake of it
– Use standards or new technologies
• Be futuristic– Take a guess but realize you could be wrong– Allow evolution– Be conservative

PURSUIT 2011 Computer LabComputer Lab
Futuristic Assumption 1: Network Evolution
• The Internet will evolve in a physical sense• Core of the network
– Super-fast backbone (optical switching, etc)– Fast access networks (MPLS, ATM)
• Peripheral Wireless Networks– Errors due to fading, etc; not just congestion– Handover
• Consequences• Degradation of end-to-end arguments

PURSUIT 2011 Computer LabPURSUIT 2011
Internet Evolution
BACKBONE
ACCESS NETWORKS
WIRELESS NETWORKS

PURSUIT 2011 Computer LabComputer Lab
Futuristic Assumption 2: Heterogeneous Devices
• Devices will have more than one wireless interface.
• Vertical handover – switching between different network interfaces to provide seamless connectivity
• Vertical handover is good but it introduces a lot of QoS issues because the different wireless networks have different qualities of service

PURSUIT 2011 Computer LabComputer Lab
Vertical Handover (Sideffects)
• Affects your connections – Some protocols react badly with respect to
handover.
• Affects your applications– Need to think through how Quality-of-Service
affects applications
• Encapsulate these ideas in a Framework

PURSUIT 2011 Computer LabComputer Lab
Layer 5: Slow Adaptation of TCP After LAN->GPRS Handover

PURSUIT 2011 Computer LabComputer Lab
Lesson 0.0• New framework
– We need to control network interfaces generically
– Make mobility support explicit• Vertical handover can have tsunami effects
– Merge network and transport services – Make QoS support explicit
• Provide a way for applications to negotiate with the network

PURSUIT 2011 Computer LabPURSUIT 2011
The Complete Y-Comm Framework
HARDWARE PLATFORM (MOBILE NODE)
HARDWARE PLATFORM (BASE STATION)
NETWORK ABSTRACTION (MOBILE NODE)
NETWORK ABSTRACTION (BASE STATION)
VERTICAL HANDOVER
POLICY MANAGEMENT
END SYSTEM TRANSPORT
QOS LAYER
APPLICATION ENVIRONMENTS
(RE)CONFIGURATION LAYER
NETWORK MANAGEMENT
CORE TRANSPORT
NETWORK QOS LAYER
SERVICE PLATFORM
CORE NETWORKPERIPHERAL NETWORK
SAS
NTS
NAS
QBS

PURSUIT 2011 Computer LabComputer Lab
Y-Comm Group• Middlesex University
• Mathematical modelling of vertical handover (TBVH) and the Stream Bundle Layer for Downward QoS (Fatema Shaikh)
• Transport protocol and network architecture issues in Peripheral networks (Glenford Mapp)
• Security (Mahdi Aiash)• Mobile Services (Fragkiskos Sardis)
• University of Cambridge• Proactive knowledge- based policy mechanisms for
handover (David Cottingham)• Networking issues (Jon Crowcroft)

PURSUIT 2011 Computer LabComputer Lab
Y-Comm Group• University of Sao Paulo (ICMC San Carlos)
• Ontological services for vertical handover• SoHand Middleware (Edson Moreira and Renata Vanni)• Core Network Management (Mario Augusto)
• Federal University of San Carlos• Testbed based on IEEE 802.21
• Loughborough University• Security Framework in Y-Comm (Raphael Phan)

PURSUIT 2011 Computer LabComputer Lab
This talk
• Can’t explain everything about Y-Comm • It’s too big
• Concentrate on the Peripheral Network
• See Y-Comm Research Webpage:
• http://www.mdx.ac.uk/research/areas/software/ycomm_research.aspx

PURSUIT 2011 Computer LabPURSUIT 2011
The Peripheral Framework
APPLICATION ENVIRONMENTS LAYER
QOS LAYER
END TRANSPORT SYSTEM
POLICY MANAGEMENT LAYER
VERTICAL HANDOVER LAYER
NETWORK ABSTRACTION LAYER
HARDWARE PLATFORM LAYER

PURSUIT 2011 Computer LabPURSUIT 2011
Layer 1: Hardware Platform Layer
• Hardware Platform Layer– Defines the physical requirements for a
particular wired or wireless technology– Expanded physical layer
• Includes electromagnetic spectrum• Modulation and channel reservation algorithms
– Incompatibility issues• Two technologies may be incompatible and cannot
be used simultaneously

PURSUIT 2011 Computer LabPURSUIT 2011
Hardware Platform Layer Represented as Vertical Components
3G WLAN 802.11
WiMax802.16
UltraWideBand

PURSUIT 2011 Computer LabComputer Lab
But all this is about to change!
• Need to make more efficient use of the electromagnetic spectrum
• Cognitive Radio– A radio that is aware of and can sense its
environment, learn from its environment, and adjust its operation according to some objective function

PURSUIT 2011 Computer LabComputer Lab
Cognitive Radio (CR)• Technology
– Software Defined Radio (SDR) • Wide spectrum receiver• Do the processing in real-time
– Intelligent Signal Processing (ISP)• Allows it to detect interference and move to another part of
the spectrum
– Ideal cognitive Radio – Mitola Radio > 2030• Mitola radio uses CR as the physical layer of a
communications model• That’s why CR is part of Y-Comm

PURSUIT 2011 Computer LabPURSUIT 2011
Cognitive Radio
WIDE SPECTRUM REECIVER
SOFTWARE DEFINED RADIO
SPECTRUM MANAGEMENT
3G WLAN WiMax
INTELLIGENT SIGNAL PROCESSING
UltrawideBand

PURSUIT 2011 Computer LabComputer Lab
Layer 2: Network Abstraction layer
• Network abstraction Layer– An abstraction that allows us to define, control
and manage any wireless network on a mobile host
– Key issues: data path functions; data formats (Link-layer), turning features on and off
– Need to generate L2 triggers when a new network is detected or when an old network is no longer detectable
• Build on 802.21

PURSUIT 2011 Computer Lab
802.21: Key Services
Link Layer TriggersState Change
PredictiveNetwork Initiated
Network InformationAvailable NetworksNeighbor MapsNetwork ServicesHandover Commands
Client InitiatedNetwork Initiated
Vertical Handovers
802.21 uses multiple services to Optimize Vertical Handovers
802.21 MIH Function
Protocol and Device Hardware
Applications (VoIP/RTP)
Connection Management
WLAN Cellular WMAN
L2 Triggers and Events
Information Service
Mobility Management Protocols
Smart Triggers
Information Service
Handover Messages
Handover Management
Handover Policy
Handover Messages IE
EE
80
2.2
1IE
TF
802.21 Overview

PURSUIT 2011 Computer LabComputer Lab
Layer 3: Vertical Handover Layer
• Layers that define the mechanism for vertical handover.
• Support for different types– Network-based – Client-based

PURSUIT 2011 Computer LabComputer Lab
Client-Based Handover
• More scalable for heterogeneous networks– Mobile node can monitor the status of all its
network interfaces via the network abstraction layer
– Can take into account other factors such as the state of TCP connections
• Don’t want to do a handover during the start and termination of TCP connections

PURSUIT 2011 Computer LabPURSUIT 2011
Lesson 1.0 handover is complicated
HANDOVER
IMPERATIVE ALTERNATIVE
REACTIVE PROACTIVE
KNOWLEDGE-BASED MODEL-BASED
NETPREF
USERPREF CONTEXT
SERVICES
UNANTICIPATED ANTICIPATED

PURSUIT 2011 Computer LabComputer Lab
Layer 4: Policy Management layer
• Decides if, when and where vertical handover should occur.
• Must be able to deal with all cases of handover– Reactive done– Proactive – most favourable but hard

PURSUIT 2011 Computer LabPURSUIT 2011
Reactive Policy: PROTON
HANDOVER EXECUTION LAYER
INPUT/OUTPUT LAYER
POLICY LAYER (PONDER)
WLAN GPRS LAN
L2 Triggers
HIGHER LAYERSInterface Information

PURSUIT 2011 Computer LabComputer Lab
Layer 4: Proactive Policies
• Proactive Policy Management– The mobile node can know or estimate the network
state at a given point before it arrives at that point– Proactive Policies allow us to maximize the use of
available channels provided you know the amount of time a channel will be available.
– That time is known as: • Time before vertical handover (TBVH)• Can significantly reduce packet loss during all vertical
handovers

PURSUIT 2011 Computer LabComputer Lab
Layer 4: Proactive policies
• Proactive policies can themselves be divided into 2 types
• Proactive knowledge-based systems– Knowledge of which local wireless networks
are operating at a given location and their strengths at that point
– We also need a system to maintain the integrity, accessibility and security of that data

PURSUIT 2011 Computer LabComputer Lab
Proactive Policies
• Knowledge-based approach
• Gather a database of the field strengths for each network around Cambridge
• Need to maintain the database and also know how the results might be affected by seasonal effects

PURSUIT 2011 Computer Lab
Knowledge-Based Policy Management (Cambridge)

PURSUIT 2011 Computer LabComputer Lab
Proactive Policies – Modelling Approach (Middlesex)
• Using a simple mathematical model• Define a radius at which handover should
occur• Find out how much time I have before I hit
that circle, given my velocity and direction• Calculate TBVH
• Used simulation (OPNET)• Can be used in the real world as well as in
simulation

PURSUIT 2011 Computer LabPURSUIT 2011
The Model-Based Handover
Threshold Circle coverage
Real coverage
Exit coverage
Exit threshold circle
Handover threshold circle

PURSUIT 2011 Computer Lab
Predictive Mathematical Model for TBVH(Simple Case)
• Introduction of additional functionality to Base Station at network boundary (BBS).
• Distance between MS and BBS derived from location
co-ordinates or
• Estimated TBVH
)log(10 lRSSdB
v
xdxdrTBVH
cossin 222
Movement of MS under BBS coverage (upward vertical handoff)
BBS
MS
r
dz
x

PURSUIT 2011 Computer Lab
Simulation and Results
TBVH simulation in OPNET Modeler:

PURSUIT 2011 Computer Lab
A
B
C
S
T
NET A
NET B
NET C
Combining Transport and Communications to determine the optimum handover

PURSUIT 2011 Computer Lab
A
H1
C1
C2B
Y1Z1
E1
Y2
Z2
C
Y3
Z3
H3
E2
E3
S
TH2
Analysis shows that it is possible to calculate these key points with some degree
of accuracy

PURSUIT 2011 Computer LabComputer Lab
This is getting interesting
• Because we can not only work out TBVH
• You can also calculate the amount of time a mobile node will be in a given network
• Try to optimize handovers when networks overlap– Depends on the velocity (affects the exit
radius) and adaptation time

PURSUIT 2011 Computer LabPURSUIT 2011
Vertical Handover
POLICY MANAGEMENT LAYERDECISION HANDOVER
(BASE-STATION, 3G, QOS, TBVH)
GPSLocation,
Speed, direction
Connections (QoS)
VERTICAL HANDOVER LAYERACQUIRE RESOURCES
( 3GCHAN, BASE-STATION, QOS)
NETWORK MANAGEMENT LAYERSend to Mobile
TOPOLOGY, RESOURCES, QoS
TBVH New QoSNew IP
RECONFIGURABLE LAYERACQUIRE CHANNEL
(3G, BASE-STATION, QOS)
NETWORK ABSTRACTION LAYERBASE-STATION
CHANNEL ACQUIRED
DO IT
NETWORK ABSTRACTION LAYERDATA CHANNNEL = 3G
3G=ACTIVE WLAN=PASSIVE WiMAX= PASSIVE
3G WLAN WiMax 3G WLAN WiMax
Done
DO IT
L2 eventsMedia Info
CORE NETWORKPolling

PURSUIT 2011 Computer LabComputer Lab
Lessons 2.0: We need to move to Location-based Information infrastructure
• Leads to better handover– Leads to a much better use of network
infrastructure– It needs to tell the mobile node about
individual networks• Power of the transmitter, where the access points
are located.
– It also needs to know about the relationships between the individual networks.

PURSUIT 2011 Computer LabComputer Lab
Layer 5: End User Transport System
• Specifies how data is routed to individual hosts and transport protocols for error correction, reliability and Quality-of-Service requirements– Encompasses Layer 3 and Layer 4 in the OSI model
• Different approaches– Keep the same protocols as in the core network– Keep TCP/IP, but modify TCP– Don’t modify TCP but try to get it to respond more
quickly to network outages– Try a completely new protocol suite

PURSUIT 2011 Computer LabComputer Lab
Layer 5: The case for a new transport Infrastructure
• A new transport system could be more suited for wireless networking
• Do all machines have to have an IP address to use the Internet?
• No.. Look at Network Address Translation (NAT)• Translation is done between a private address and
port to a global address and port at the NAT server

PURSUIT 2011 Computer LabComputer Lab
Layer 5: Continued
• A global IP address in the case of NAT is really being used as an endpoint in the core network
• So we can use another network scheme in the peripheral network once we can specify how we map it to TCP/IP or UDP/IP in the core network

PURSUIT 2011 Computer Lab
Y-Comm’s view of the Future
PERIPHERALWIRELESSNETWORK
CORE NETWORK
PERIPHERALWIRELESSNETWORK
Core EndpointsIn Access Network
QoS, Secure Connection

PURSUIT 2011 Computer LabComputer Lab
View corresponds with other ideas
• Faster LAN systems– Optimize DNS, streaming video from local
caches
• Integrate protocol with applications– Tuneable transport– Remove the user/kernel limitations
• Use as a local signalling protocol– Encapsulates TCP packets

PURSUIT 2011 Computer LabPURSUIT 2011
Simple Protocol
PK_TYPE Flags CHKSUM
TOTAL_LEN PBLOCK TBLOCK
PRI CB
SYNC_NO WINDOW_SIZE
MESS_SEQ_NO MESS_ACK_NO
DEST_ID SRC_ID

PURSUIT 2011 Computer LabComputer Lab
The Simple Protocol• DEST_ID (16) – identifying remote end• SRC_ID (16) – from source end• PK_TYPE (4) - packet type• PRI (2) - supports 4 priority levels• CB (2) – supports ECN• CHKSUM (16) – sixteen bit checksum• TOTAL_LEN (16) – total packet length• PBLOCK (8) – the present block• TBLOCK (8) – the total number of blocks• MESS_SEQ_NO (16) – last message sent• MESS_ACK_NO (16) – last message received• SYNC_NO (8) – the last ACK received• WINDOW_SIZE (24) – the window size

PURSUIT 2011 Computer LabComputer Lab
Lesson 3.0: Local support is now essential to the Future
Internet
• Presence of heterogeneous networks
• Support for mobility
• Need for local signalling
• Need for local transports – Don’t need to change TCP
• Need for local knowledge
• Can’t ignore that any more

PURSUIT 2011 Computer LabComputer Lab
Heterogeneous Networking and Multi-homing
• Because devices will have several interfaces, there will be multi-homing issues
• Solutions such as Mobile IP which depend on Home and Care-of-Addresses are not scalable
• SCTP helps but works on the transport level only
• Need to look at the network addressing scheme

PURSUIT 2011 Computer LabComputer Lab
Does IPv6 help?Look at the IPv6 Address Format

PURSUIT 2011 Computer LabComputer Lab
Advantages of IPv6
• Uses a global Interface_ID so it is very easy to construct a new address using auto-configuration– So I don’t need a foreign agent– Since the Interface_ID does not change if I do
a horizontal handover, it is easier for the network infrastructure to work out what is going on
• Does not help with vertical handover

PURSUIT 2011 Computer LabComputer Lab
Pressure for Change• Mobile Systems
– Efficient Vertical Handover (Y-Comm)
• Multi-path TCP– Allowing TCP to use all the device interfaces to
transfer data• IETF, Jon Crowcroft, Cambridge
• Pressure to optimize network resources– Switches and routers have limited memory, etc.
• Internet of Things– Networking should be based around devices
themselves not the interfaces they use

PURSUIT 2011 Computer LabComputer Lab
Different Approach
• Split the IP address into 2 distinct parts– Node_ID : identifies the device
• Independent of the number of Interfaces the device has
• Given when the device was created; burnt into device;
• Recycled when the device is no longer used
– Location_ID: identifies which network the device is using. A multi-homed device will have several Location_IDs

PURSUIT 2011 Computer LabComputer Lab
Proposed IP Address Format
LOCATION_ID NODE_ID
127 063

PURSUIT 2011 Computer LabComputer Lab
History behind this• First proposed by LIN Group in Japan (2000-
2001)• Some work done at AT&T Labs on supporting
this paradigm– Mapp and Fraser (2001)
• Led to the development of EUI-64– Evolve the Ethernet Mac Address into a Node_ID
• Current work on ILNP lead by Saleem Bhatti from St Andrews

PURSUIT 2011 Computer LabComputer Lab
Why is this good?• Node_ID allows the networking
infrastructure to know that network interfaces are co-located
• Optimize network resources– In the core network we could use the
Node_ID as a general guide to where the device is located. Use the Location_ID to choose which particular local network to use to forward the packet to that device
– Refinement of HMIPv6

PURSUIT 2011 Computer LabComputer Lab
Additional Help is needed
• Some observations– It would be good to know that the device is
stationary in a given network• Cache the Location_ID directly in the routing table
– Good for servers as they are stationary
– Reduce the visibility of servers• Need to reduce DDoS attacks
– Support of using different interfaces• Multicast, broadcast, local any-cast, etc.

PURSUIT 2011 Computer LabComputer Lab
So we are proposing to modify to address format
LOCATION_ID NODE_ID
0 12763
NODE_IDLOCATION_ID
1270 55 63
NETADMIN

PURSUIT 2011 Computer Lab
NODE_ID =Global Node Identifier (EUI-64)
0 63
NETADMIN = INFMSF S
0 8
LOCATION_ID = SUBNET
0 55
GLOBAL ROUTING PREFIX
39
NEW STRUCTURES

PURSUIT 2011 Computer LabComputer Lab
SF- Scope Field
• Introduced by the Y-Comm Group– Ring-based Security model
• Aimed at protecting servers by reducing access to them
• Servers act within a defined network scope– Only entities within that scope can access the
server– If you are outside the scope, your packet is
blocked by the network infrastructure

PURSUIT 2011 Computer LabComputer Lab
Scope Field – 2 bits• 00 - Only processes on the same machine
can use this server• Location_ID must be the loop-back address
• 01 - Only processes on the same LAN can access the server
• Location_ID must be the same LAN as server
• 10 – Only processes on the same Admin Domain can access the server
• Location_ID must be site-address
• 11 – Server is globally accessible

PURSUIT 2011 Computer LabComputer Lab
Other bits in the NetAdmin Field
• S – indicates that the device is stationary with regard to a given network – Physically stationary – Servers– Relatively stationary as determined by a
location system
• M – indicates that Node_ID is being used as a multicast address, this allows multicast packets to be sent on network

PURSUIT 2011 Computer LabComputer Lab
Interface_IDs can make a comeback
• Interface_IDs banished from the New address format– Means we will have to map the Location_ID to
the Interface_ID before we could send a packet on a given network. Slow performance
• Other observation– Bluetooth and other short range systems do
not need a Location_ID (network) and Interface_ID might be better

PURSUIT 2011 Computer LabComputer Lab
Re-Introduce it by indirectlyINF field (4 bits)
• An interface can be uniquely represented within the address format by using an interface number– Controlled by the device.
• Map interface # to MAC address• Give special meaning to certain values
– 0 – any-cast – packet is sent on any available network interface of the mobile device
– 0xF – broadcast packet is sent on all available network interfaces of the mobile device
– 0x1 – called the primary interface

PURSUIT 2011 Computer LabComputer Lab
INF • Support for pseudo/virtual interfaces
– Add features such as security • OpenSSL, FreeSwan, provides IPSec services
• Applications can query interfaces on a device– Master locator– Map interfaces #s to Quality-of-Service (QoS)
parameters
• Bluetooth and other point-to-point system could use the INF only and not bother with the Location_ID

PURSUIT 2011 Computer LabComputer Lab
Lesson 4.0: Can’t ignore multi-homing any longer
• Crucial for heterogeneous networking
• Need to concentrate on devices and not their interfaces
• Need to think about keeping it flexible and efficient
• Urgent

PURSUIT 2011 Computer LabComputer Lab
Layer 6: QoS Layer
• QoS is the most dynamically changing component in heterogeneous networking
• Applications running on heterogeneous devices need support to handle this
• Two Concepts of QoS– Downward QoS– Upward QoS

PURSUIT 2011 Computer LabComputer Lab
Layer 6: Downward QoS
• Mainly to support legacy applications
• The application specifies a minimum QoS and the QoS layer does the mapping between the QoS that the application requires and the QoS that is currently available - but is dynamically changing

PURSUIT 2011 Computer LabComputer Lab
Layer 6: Upward QoS• For applications that should adapt to
changes in QoS, e.g. Multimedia services, etc– The QoS layer therefore signals the
application using an event mechanism to indicate changes in the available QoS
– Applications can specify routines that will be called when the events occur
• Similar to the X Window System

PURSUIT 2011 Computer LabPURSUIT 2011
QoS Layer
APPLICATION LAYER
QOS LAYER
END TRANSPORT LAYER
POLICY MANAGEMENT LAYER
DOWNWARD QOS
APPLICATION LAYER
QOS LAYER
END TRANSPORT LAYER
POLICY MANAGEMENT LAYER
UPWARD QOS

PURSUIT 2011 Computer LabComputer Lab
Lesson 5.0 Make QoS the real interface to the network
• Applications should not really have to know about TCP or any other protocol
• Replace transport protocols on the fly
• Allow applications to adapt if they can

PURSUIT 2011 Computer LabComputer Lab
Last area: Security
• Security is part of Quality-of-Service
• QoSS – specify security as part of QoS– Changes in security are regarded as changes
in the QoS
• Security needs to be on different levels and involves both Core and Peripheral Frameworks
• Allow several layers

PURSUIT 2011 Computer LabPURSUIT 2011
The Y-Comm Framework showing its Security Levels- New Security Level
HARDWARE PLATFORM (MOBILE NODE)
HARDWARE PLATFORM (BASE STATION)
NETWORK ABSTRACTION (MOBILE NODE)
NETWORK ABSTRACTION (BASE STATION)
VERTICAL HANDOVER
POLICY MANAGEMENT
END SYSTEM TRANSPORT
QOS LAYER
APPLICATION ENVIRONMENTS
(RE)CONFIGURATION LAYER
NETWORK MANAGEMENT
CORE TRANSPORT
NETWORK QOS LAYER
SERVICE PLATFORM
CORE NETWORKPERIPHERAL NETWORK
SAS
NTS
NAS
QBS

PURSUIT 2011 Computer LabComputer Lab
Security in Y-Comm• Network Architecture Security (NAS)
• Security dealing with the deployment and management of different wireless technology
• Managed from the Policy and Management layers
• Network Transport Security (NTS)– Security dealing with end-to-end transport through Y-Comm
• Done at Layer 5, NAT, IPSec, etc
• QoS Based Security (QBS)– Look at QoS Issues
• Looks at SLAs, prevents overloading• Looks at Denial of Service Attacks
• Service and Application Security (SAS)– Security dealing with running applications and
deploying services• AAAC, ACLs, User-based security

PURSUIT 2011 Computer LabComputer Lab
Lesson 6: Security needs to consider the effect of an open Architecture
• Security needs to be part of the communications system
• Also needs to be part of QoS
• Security is about protecting entities and not just data– Concept of Security models
• Connection• Ring-based• Vertical Handover

PURSUIT 2011 Computer LabComputer Lab
Lesson 7: New business models
• Y-Comm is doomed to failure
• No academic funding – Not about TCP/IP– Not interested in tinkering around the edges
• No industry funding– Y-Comm will destroy the revenue streams of
current mobile providers– They will not put money in unless we show
them how they are going to make money

PURSUIT 2011 Computer LabComputer Lab
Any Questions?