Protecting your Physical Security Perimeter (PSP)
Transcript of Protecting your Physical Security Perimeter (PSP)

May 24, 2016
1
Protecting your Physical Security Perimeter (PSP)
Steven KellerLead Compliance Specialist - [email protected]

Discussion Topics• PSP Under CIP V3
• PSP Under CIP V5 Revision (High and Medium)– Requirements of your PSP
– 1 PSP
– 2 PSPs
– Two Factor authentication
2

PSP under V3• PSP Requirements under V3
– Create a Plan
– “Six-wall” border: The physical, completely enclosed (“six-wall”) border
surrounding computer rooms, telecommunications rooms, operations centers, and other locations in which Critical Cyber Assets are housed and for which access is controlled.
– Identification of Access Points
– Physical Access Controls
– Physical Access Control Systems
– Monitoring and Logging
3

PSP under V5 Revisions• PSP Requirements under V5 Revision
– New definition of Physical Security Perimeter: The physical border surrounding locations in which BES Cyber
Assets, BES Cyber Systems, or Electronic Access Control or Monitoring Systems reside, and for which access is controlled.
– Similar Controls under V3 Logging and Monitoring
Controls to restrict access to BES Cyber Assets
Alerting to unauthorized access
4

CIP-006-5/6 Part 1.2
• Part 1.2 requires the entity to “utilize at least one physical access control to allow unescorted physical access into each applicable Physical Security Perimeter to only those individuals who have authorized unescorted physical access.”
• Applicable to Medium Impact BES Cyber Systems with External Routable Connectivity and their associated Electronic Access Control or Monitoring System (EACMS) and Protected Cyber Asset (PCA)
5

CIP-006-5/6 Part 1.3
• The Part requires the entity to “where technically feasible, utilize two or more different physical access controls (this does not require two completely independent physical access control systems) to collectively allow unescorted physical access into Physical Security Perimeters to only those individuals who have authorized unescorted physical access.”
• Applicable to High Impact BES Cyber Systems and their associated EACMS and PCAs
6

Sample PSP Facility
7

Sample PSP Facility
8
DAF
E
B
C

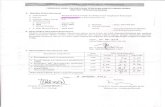
Scenario of Access defined.
Building Zone 1 Zone 2 Zone 3 Zone 4
James X X
George X X
Frank X X X X X
Allen X X
9
The four zones configured in the Physical Access Control System are:1. Rooms A and D 2. Room B3. Room C4. Rooms E and F

PSP Zoned Access under CIP-006-5/6
10
DAF
E
B
C

Recap of the PSPs
11
• The three PSPs that must be defined are– Rooms A and D
– Room B
– Room C

Low Impact PSP
12
• Physical Security Controls: Each Responsible Entity shall control physical access, based on need as determined by the Responsible Entity, to (1) the asset or the locations of the low impact BES Cyber Systems within the asset and (2) the Low Impact BES Cyber System Electronic Access Points (LEAPs), if any
• Does not require a logging and access controls systems as high/medium
• Simple as a locked door or a chained fence

How not to Protect your PSP
13

Helpful Resources
• NERC V5 Page
• SPP RE CIP V5 Guidance Page– Contains links to:
NERC Version 5 Transition Home Page
FERC CIP Version 5 Filings
SPP RE presentations, webinars, and videos
14

SPP RE CIP Team• Kevin Perry, Director of Critical Infrastructure Protection
(501) 614-3251
• Shon Austin, Lead Compliance Specialist-CIP(501) 614-3273
• Steven Keller, Lead Compliance Specialist-CIP(501) 688-1633
• Jeremy Withers, Senior Compliance Specialist-CIP(501) 688-1676
• Robert Vaughn, Compliance Specialist II-CIP(501) 482-2301
• Sushil Subedi, Compliance Specialist II-CIP(501) 482-2332
15












![Protecting Soft Targets: A Case Study and Evaluation of ... · “providing special attention to perimeter security and access control issues.” [29]Having a clearly defined˙ perimeter](https://static.fdocuments.in/doc/165x107/5f460aa2cd720149687e2628/protecting-soft-targets-a-case-study-and-evaluation-of-aoeproviding-special.jpg)





