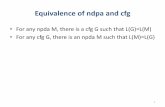
1 Equivalence of PDA, CFG Conversion of CFG to PDA Conversion of PDA to CFG.
More CFG Static Single Assignmentcode transformations – Primarily due to explicit & simplified...
Transcript of More CFG Static Single Assignmentcode transformations – Primarily due to explicit & simplified...

More CFGStatic Single Assignment
ECE 5775High-Level Digital Design Automation
Fall 2018

▸ HW 1 due next Monday (9/17)
▸ Lab 2 will be released tonight (due 9/24)
▸ Instructor OH cancelled this afternoon
1
Announcements

▸ More on control flow analysis – Dominance frontier
▸ Dataflow analysis – static single assignment (SSA)– SSA Definition– PHI node (F-node) placement– Code optimizations with SSA
2
Outline

▸ What becomes a leader statement of a basic block? (three cases)
▸ Does a node strictly (or properly) dominate itself?
▸ Does a predecessor of a node B always dominate B?
▸ Suppose A that dominates all of B’s predecessors. Does A always dominate B?
3
Revisiting Control Flow Analysis

Review: Finding Loops
▸ Loop identification algorithm– Find an edge B®H where H dominates B;
This edge is called a back-edge
– Find all nodes that (1) are dominated by H and (2) can reach B through nodes dominated by H; add them to the loop • H and B are naturally included
4

5
Finding Loops (1)
1
2
3
5 6
8
9 10
Find all back edges in this graphand the natural loop associated with each back edge
(9,1)4
7

6
Finding Loops (1)
1
2
3
5 6
8
9 10
Find all back edges in this graphand the natural loop associated with each back edge
(9,1) Entire graph4
7

7
Finding Loops (2)
1
2
5 6
8
9 10
Find all back edges in this graphand the natural loop associated with each back edge
(9,1) Entire graph(10,7)
3
4
7

Intuition of Dominance Relation
8
Imagine a source of lightat the entry node, and thatthe edges are optical fibers
To find which nodes are dominated by a given node, place an opaque barrier at that node and observe which nodes become dark
1
2
5 6
8
9 10
3
4
7
entry

9
Finding Loops (2)
1
2
3
4
7
5 6
8
9 10
Find all back edges in this graphand the natural loop associated with each back edge
(9,1) Entire graph(10,7)

10
Finding Loops (2)
1
2
3
4
7
5 6
8
9 10
Find all back edges in this graphand the natural loop associated with each back edge
(9,1) Entire graph(10,7) {7,8,10}

(7,4)
11
Finding Loops (3)
1
2
3
4
5 6
8
9 10
Find all back edges in this graphand the natural loop associated with each back edge
(9,1) Entire graph(10,7) {7,8,10}
7

(7,4)
12
Finding Loops (3)
1
2
3
4
7
5 6
8
9 10
Find all back edges in this graphand the natural loop associated with each back edge
(9,1) Entire graph(10,7) {7,8,10}

13
Finding Loops (3)
1
2
3
4
7
5 6
8
9 10
Find all back edges in this graphand the natural loop associated with each back edge
(9,1) Entire graph(10,7) {7,8,10}(7,4) {4,5,6,7,8,10}

Static Single Assignment
▸ Static single assignment (SSA) form is a restricted IR where– Each variable definition has a unique name– Each variable use refers to a single definition
▸ SSA simplifies data flow analysis & many compiler optimizations – Eliminates artificial dependences (on scalars)
• Write-after-write• Write-after-read
14

SSA within a Basic Block
▸ Assign each variable definition a unique name▸ Update the uses accordingly
x = read()x = x * 5x = x + 1y = x * 9
x0 = read()x1 = x0 * 5x2 = x1 + 1y = x2 * 9
15
×
+
×
5
x1
x0
x2
1
9
yOriginal code SSA form
Corresponding data flow graph

SSA with Control Flow
▸ Consider a situation where two control-flow paths merge– e.g., due to an if-then-else statement or a loop
x = read()if (x > 0)
y = 5else
y = 10x = y
y = 5 y = 10
x = y
x = read()if (x > 0)
y0 = 5 y1 = 10
x1 = y
x0 = read()if (x0 > 0)
should this be y0 or y1?
16

Introducing ϕ-Node
▸ Inserts special join functions (called ϕ-nodes or PHI nodes) at points where different control flow paths converge
y0 = 5 y1 = 10
y2 = ϕ(y0, y1)x1 = y2
if (x0 > 0) Note: ϕ is not an executable function!To generate executable code from this form, appropriate copy statements need to be generated in the predecessors (in other words, reversing the SSA process for code generation)
17

SSA in a Loop
▸ Insert ϕ-nodes in the loop header block
x = 0 i = 1 while (i<10) {
x = x+ii = i+1
}
if (i < 10)
Outsidex = x + 1i = i + 1
x = 0i = 1
x1 = ϕ(x0, x2)i1 = ϕ(i0, i2)if (i1 < 10)
Outsidex2 = x1 + 1i2 = i1 + 1
x0 = 0i0 = 1
18

ϕ-Node Placement
▸ When and where to add ϕ-nodes?– If two control paths A à C and B à C
converge at a node C, and both A and B contain assignments to variable X, then ϕ-node for X must be placed at C • We often call C a join node or
convergence point• Can be generalized to more than two
converging control paths
▸ Objective: Minimize the number of ϕ-nodes– Need to compute dominance frontier
sets
19
x1 = ϕ(x0, x2)i1 = ϕ(i0, i2)if (i1 < 10)
Outsidex2 = x1 + 1i2 = i1 + 1
x0 = 0i0 = 1

Dominance Frontier
▸ A basic block F is in the dominance frontier set (DF)of basic block B if and only if– B does NOT strictly dominate F– B dominates some predecessor(s) of FIf above two conditions hold, F Î DF(B)
▸ Intuitively, the basic blocks in the dominance frontier set of B are almost strictly dominated by B
▸ Useful for efficiently computing the SSA form
20

21
Dominance Frontier and SSA
B0
B1
B2 B3
B4
B6
B7
B5
Area dominated by B3
▸ B7 is in the dominance frontier set of B3– B3 does not dominate B7,
but dominates one of its predecessors (i.e., B6)
▸ For each variable definition in B3, a ϕnode is needed in B7– B7 is the destination of
some edge(s) leaving an area dominated by B3

DF(B)–1776671
22
Example: Dominance Frontiers
B0
B1
B2 B3
B4
B6
B7
B5
CFG
B01234567
Dominance frontiers of B
▸ F is in the dominance frontier set (DF) of B iff– B does NOT strictly dominate F– B dominates some predecessor(s) of FIf above two conditions hold, F Î DF(B)

23
Iterative ϕ-Node InsertionB DF0 -1 12 73 74 65 66 77 1
b =c =
c =
b =
a =b =c =B0
B1
B2 B3
B4
B6
B7
B5
a = ϕ(…)b = ϕ(…)c = ϕ(…)
c = ϕ(…)
a = ϕ(…)b = ϕ(…)c = ϕ(…)
a =
• a is defined in 0, 3 => need ϕ in 7, then a defined in 7=> need ϕ in 1
• b is defined in 0, 2, 6=> need ϕ in 7then b defined in 7 => need ϕ in 1
• c is defined in 0,2,5=> need ϕ in 6,7then c defined in 7=> need ϕ in 1

▸ SSA form simplifies data flow analysis and many code transformations– Primarily due to explicit & simplified (sparse) def-use
chains
▸ Here we show two simple examples – Dead code elimination– Loop induction variable detection
24
SSA Applications

Dead Code in CDFG
▸ Dead code is either– Unreachable code– Definitions never used
▸ Dead statements?
x = a + by = c + d
x = a – b
z = z + 1
y = c – d z = x + y
f(x, y)
B1
B2
B4
B5
B6
25

26
Dead Code Elimination with SSA
x1 = a + by1 = c + d
x2 = a – b
z2 = z1 + 1
x3 = ϕ(x1, x2)y2 = c – d
z1 = x3 + y2
f(x3, y2)
B1
B2
B3
B4
B5
x1 = a + b
x2 = a – b
x3 = ϕ(x1, x2)y2 = c – d
f(x3, y2)
Iteratively remove unused definitions: remove y1, z2 (and B4) à then remove z1

▸ An induction variable is a variable that
– Gets increased or decreased by a fixed amount (loop invariant) on every iteration of a loop (basic induction variable)• i = i + c
– or is an affine function of another induction variable (mutual induction variable)• j = a * i + b
27
Loop Induction Variables

▸ Find basic loop induction variable(s)1. Inspect back edges in the loop
2. Each back edge points to a ϕ node in the loop header, which may indicate a basic induction variable
3. ϕ is a function of an initialized variable and a definition in the form of “i + c” (i.e., increment operation)
28
Identifying Basic Loop Induction Variable
i1 = ϕ(0, i2)if (i1 < 10)
Outsidei2 = i1 + 1
…

▸ Importance of compilers– Essential component of SoC software development flow– Essential component of high-level synthesis
▸ A good intermediate representation (IR) enables efficient and effective analysis and optimization– Dominance relation helps effective CFG analysis– SSA form facilitates efficient IR-level optimization
29
Summary

▸ These slides contain/adapt materials developed by– Prof. Scott Mahlke (UMich)
30
Acknowledgements