Securing tesla broadcast protocol with diffie hellman key exchange
Lecture 7b: The Diffie-Hellman Secret Sharing Scheme Wayne Patterson SYCS 653 Fall 2009.
-
Upload
warren-benson -
Category
Documents
-
view
212 -
download
0
Transcript of Lecture 7b: The Diffie-Hellman Secret Sharing Scheme Wayne Patterson SYCS 653 Fall 2009.

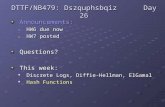
Lecture 7b:The Diffie-Hellman Secret Sharing
Scheme
Wayne PattersonSYCS 653Fall 2009

The Diffie-Hellman Key Exchange
Early in the development of the public key paradigm, a method to exchange secret or symmetric keys was devised by Whitfield Diffie and Martin Hellman, which is still in widespread use today.

The Diffie-Hellman Key Exchange
As with the RSA, this involves the difficulty of factoring large integers, or, what turns out to be equivalent, solving the so-called “discrete logarithm” problem.

Diffie-Hellman
Invented by Williamson (GCHQ) and, independently, by D and H (Stanford) (see Stamp, p. 70)
A “key exchange” algorithm
– Used to establish a shared symmetric key
Not for encrypting or signing
Security rests on difficulty of discrete log problem: given g, p, and gk mod p find k

The Diffie-Hellman Key Exchange
First, a little more on prime numbers
For every prime number p, and every number a mod p, we know by the Little Fermat Theorem that ap-1 = 1 (mod p).
Any g for which all of the exponents a, a2, …, ap-1 are distinct is called a primitive root of p, or a generator.

How to Find a Primitive Root
Not easy, but not impossible.Mathematica has it built-in.Once you find one, easy to find manyIf g is a primitive root of p, then if
GCD(m,p-1) = 1 for m < (p-1), then gm is also a primitive root of p.

Diffie-Hellman
Let p be prime, let g be a generator – For any x {1,2,…,p-1} there is n s.t. x =
gn mod pAlice selects secret value aBob selects secret value bAlice sends ga mod p to BobBob sends gb mod p to AliceBoth compute shared secret gab mod pShared secret can be used as symmetric key

Diffie-Hellman
Suppose that Bob and Alice use gab mod p as a symmetric key
Trudy can see ga mod p and gb mod pNote ga gb mod p = ga+b mod p gab mod pIf Trudy can find a or b, system is brokenIf Trudy can solve discrete log problem, then
she can find a or b

Diffie-HellmanPublic: g and pSecret: Alice’s exponent a, Bob’s exponent b
Alice, a Bob, b
ga mod p
gb mod p
Alice computes (gb)a = gba = gab mod p Bob computes (ga)b = gab mod pCould use K = gab mod p as symmetric key

Diffie-Hellman
Subject to man-in-the-middle (MiM) attack
Alice, a Bob, b
ga mod p
gb mod p
Trudy, t
gt mod p
gt mod p
Trudy shares secret gat mod p with Alice Trudy shares secret gbt mod p with BobAlice and Bob don’t know Trudy exists!

Diffie-Hellman
How to prevent MiM attack?– Encrypt DH exchange with
symmetric key– Encrypt DH exchange with public
key– Sign DH values with private key– Other?
You MUST be aware of MiM attack on Diffie-Hellman