Entrust Crypto Health Check and Crypto Governance Consulting
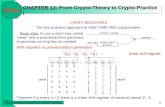
IT Security threads and solutions for Industrie 4.0 from ... · Electro-Magnetic Emission of a...
Transcript of IT Security threads and solutions for Industrie 4.0 from ... · Electro-Magnetic Emission of a...

The Trust Provider for IT Security, IT Quality and IT Infrastructure
Dirk Kretzschmar
Managing Director TÜV Informationstechnik GmbH
Beijing, September 11th, 2017
IT Security threads and
solutions for Industrie 4.0
from an independent
partner

TÜViT - Company Facts
1
TÜViT is a member of the TÜV NORD GROUP
TÜV Informationstechnik GmbH (TÜViT) – Internationally recognized consulting company and security laboratory
– Main services: IT security, IT Infrastructure, IT quality and IT certification
– IT security evaluation of IT Products, IT Systems and IT Processes
– More than 100 employees with a technical or scientific university degree
– Operating worldwide
– 40% international Business
06.09.2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP)

TÜViT – Our Principles
TÜViT - The Trust Provider for Security and Quality in Information Technology works
impartial
unbiased and
independent from
Manufacturers
Vendors
Integrators
Operators
TÜViT is a private company and does not develop, sell or integrate any products!
Special interest groups
Branches
Share holders / members
Government

IT Security on all Layers
Systems
Management
Components
ISO 27001
Standard 100 (BSI Baseline Protection)
Common Criteria / ITSEC
FIPS 140
DK / EMVCo
CA acc. SigG Technical Guidelines
ICS Security Compendium
ULD / Europrise
- Infrastructure
- Security
- Privacy
Trusted Site
Trusted Product - Security
Security Management
Evaluation of Security Software
Security Hardware
Data Centers Network / Applications
PKI’s
IoT - Industrial Control Systems
Privacy

IT Security - Accreditations
Security Management
Evaluation of Security Software
Security Hardware
Data Centers Network / Applications
PKI’s
IoT - Industrial Control Systems
Privacy
Systems
Management
Components

TÜViT: IT-Projects worldwide

Knowledge – Security Policy
– Security Management
– Risk Analyses
– Training
– eBusiness / eGovernment
– Public Key Infrastructures
– Cryptography
– Network Security
– Firewall Systems
– ICS
– Firewall Products
– OS / Databases
– Viruses / Trojans
– digital Signatures
– Authentication Methods
– Biometrics
– Random Numbers
– Time Stamps
– Smart Cards
Systems
Management
Components
Security Management
Evaluation of Security Software
Security Hardware
Data Centers Network / Applications
PKI’s
IoT - Industrial Control Systems

Knowledge
– Firewall Products
– OS / Databases
– Viruses / Trojans
– digital Signatures
– Authentication Methods
– Biometrics
– Random Numbers
– Time Stamps
– Smart Cards
Systems
Management
Components Evaluation of Security Software
Security Hardware

9
Objective:
Protection of stored/processed data against manipulation and eavesdropping
Planned for use in products with high protection requirements (passport, electronic ID, signature card, payment sector, mobile devices, pay TV, …)
Approach:
Vulnerability analysis of the implemented security mechanisms (Protection against attackers with „high attack potential“, i.e. only attackable with high effort (time, cost, equipment)
Audit of the development and production environment
Execution of penetration tests in our HW laboratory
9/6/2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP)
EVALUATION PROCEDURE

IT Security Hardware
06.09.2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP) 10

Manipulation of:
Program flow (e.g. skip commands)
Computed data (e.g. result of calculation)
Memory content (e.g. stored value)
Fault attacks
06.09.2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP) 11

Hardware security lab: Laser Fault Injection
06.09.2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP) 12

Hardware security lab: Laser Scan of a Chip
Green = Normal operation
Yellow = Sensor activated
Red = Violation caused
06.09.2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP) 13

Hardware security lab: Attacks from the back side
"normal" picture of the back side of a chip, only silicon visible
X-ray view through silicon by infrared LEDs, structures are clearly visible
06.09.2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP) 14

Electro-Magnetic Emission of a Crypto Processor
Every peak corresponds to an operation in the algorithm (left figure)
Amplitude depends on the processed data
The stronger the EM emission, the more information the signal contains
scan chip surface for optimal EM probe position (right figure)
06.09.2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP) 15

Knowledge
– eBusiness / eGovernment
– Public Key Infrastructures
– Cryptography
– Network Security
– Firewall Systems
– ICS
Systems
Management
Components
Data Centers Network / Applications
PKI’s
IoT - Industrial Control Systems

Security Services on System Level
Security Analyses
Penetration Tests in Networks
Black box Tests
White box Tests
Configuration Analyses
Conceptual Analyses
Security Audits
Forensic Investigation
Social Engineering
TÜViT Security Qualification (SQ)®
Structured Methodology to Assess the Security Level of an IT-System or IT-Installation
Scaleable and practice oriented
Results in a Certificate/Trusted Site mark for internal and external evidence
Check (Evaluation) and Confirmation according to Electronic Signature Regulations
Operation (Certification Authority Security Concepts)

AREAS

IT Security Services Provider for IS revision , IS Consulting, and Penetration testing
penetration test experts accredited
by German BSI (federal office of
information technology security)
Largest Trust Services Provider in
Germany who is accredited by the
BSI to perform penetration tests
06.09.2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP) 19

Customer Objectives
Client objectives:
1. Improving security of technical systems
2. Identifying vulnerabilities
3. Having IT security confirmed by an external third party
4. Improving security of organizational and personnel infrastructure
The result of an IT penetration test is more than just a list of existing vulnerabilities, but suggest specific solutions for their elimination
06.09.2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP) 20

Cyber Security: Methods of manipulating or damaging IT systems and of preparing an attack on IT systems
21
Network-bases attacks
using penetration
testing
Social Engineering
Circumvention of
physical security
measures

Example: OWASP (Open Web Application Security Project) Top 10
Injection
Broken Authentication and Session Management
Cross-Site Scripting (XSS)
Insecure Direct Object References
Security Misconfiguration
Sensitive Data Exposure
Missing Function Level Access Control
Cross-Site Request Forgery (CSRF)
Using Components with Known Vulnerabilities
Unvalidated Redirects and Forwards
06.09.2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP) 22

Knowledge
Systems
Management
Components
– Security Policy
– Security Management
– Risk Analyses
– Training
Security Management

ISO 27001
Information security risk evaluation
Management of Information Security
ISMS and Implementation
ISMS Operation ISO 20000
IT Service Management Efficiency
ISO 22301
enterprise security
continuity management 24
Management System Certification

25
Data Center Audit & Certification
Trusted Site Infrastructure (TSI)
Trusted Site Energy Efficiency
(TSe2)

Data Center Security: Trusted Site Infrastructure (TSI) – Certification Program
26
• Quality label for state of the art data centers
• Goals: Availability & Reliability
• Focus: data center’s mission critical infrastructure
• Criteria: Trusted Site Infrastructure catalogue

Our Services – Trusted Site Infrastructure
trainings
workshops
evaluation of design documents
certification of data centers and alarm receiving centers
energy efficiency
commissioning
pre-audits
gap - analysis Commissioning
Co
nstru
ction
Datacenter Life Cycle
Design
Op
erat
ion

06.09.2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP) 28
TSI Criteria Catalogue as test and evaluation basis
Trusted Site Infrastructure (TSI) as de-facto-standard
German Engineering
Continuous development and enhancement (2002 until today)
NEW: TSI V4.0 (incl. EN 50600)
14 years experience and Know-How
Marked Leader DACH
International Growth

06.09.2017 29
TSI International
TÜViT TSI Evaluation and Certification Projects
UK
US
LUX
Iran
UK
South Africa
A CH ES
UAE Saudi Arab
Singapore
Thailand
China
GER
© TÜV Informationstechnik GmbH (TÜV NORD GROUP)

Internet of Things From dedicated protected networks to communication using the public Internet
06.09.2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP) 30

Industrie 4.0 represents a complete new approach of the industry: - Products are controling their own production process - Raw material sends their construction plans to the production plant - Workpieces are becoming an active control component in the future factory
06.09.2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP) 31

06.09.2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP) 32
Methods of Productions are changing: Decentralized production: 3D Printer

06.09.2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP) 33
Industrie 4.0 Scope

System-Solutions and smart Products
Active Systems - predefined automatic reactions to changes - efficient and fast, But not intelligent
Intelligent Systems when the control of data processing does apply the 3 layer model of cognitive sciences: 1. active Control -> Reaction to Change 2. associative Control -> Conditioning (stimulation-reaction-pattern) 3. cognition -> plan, adjust objectives, learn, capability to self optimization
Cyber-Physical Systems Intelligente Systems which are communication using the Internet and do cooperate adaptive -> systems self adaptation to changes robust -> deal with situations, which haven‘t been preprogrammed by developer forward looking -> future conditions, influences and reactions can be anticipated based on experiences and new perceptions

Industrie 4.0 – Definition and Principles
Industrie 4.0 is use of internet technology for communication between human, mashine and products. Objective is the increase of quality, cost- and resources efficiency, flexibility, capability of change as well as robustness in volatile markets
Technological basis are cyber-physische systeme (CPS) and the „Internet of Things“.
Network: Capability of mashines, devices, sensors and human to connect and communicate via the Internet.
Information transparency: Capability of information systems to enrich digital models with sensor data, to create a virtual image of the real worls.
Technical Assistence: Assistent systems which process data to get to substantial decisions and solve upcoming problems in time.
Dezentral Decisions: Capability of cyber-physical systems to create autonomous decistions.
Principles

06.09.2017 36
Industrie 4.0 – Definition and Principles
Focus of Industrie 4.0 is
Product Development
Production
New description how development processes, production processes product lines, mashines/tools, field devices and the products themselfs are conditioned and how is their function
For Components – mashine or product – not only the function for information and communication are interesting
For the simulation of a system the complete mashine with their cabeling, linear accelerator or mechanical construction are to be considered
They are part of the reality without beeing capable for active communication
Their information are requiring a virtual representace

06.09.2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP) 37
Industry 4.0 Overview
Vertical (integration and networked production systems) Horizontal integration of value chain networks
Digital integration of engineering throughout the whole value chain

Reference Architecture Model describes Industrie 4.0
Industrie 4.0 Component Every „thing“ needs a virtualization shell to get embedded into the Industrie 4.0 world. Produkt-ID, Spezification, Data Sheet, SETUP, Operation data
RAMI 4.0 RAMI-is solution area for Industrie 4.0. All aspects and descriptions of this new technology can be localiced an visualized systmatically.
3 Dimensions of the Model
Architectur -> based on 6 layers
from real „things“ Industrie 4.0 Components
up to business processes
Product Life Cicle
Development, Production, Sales, Service
Hyrarchie
Product
Pyramid of Automization
[ Sensor/Acktor, Control (HMI), MES, ERP ]
Interconnecion – Connected World

06.09.2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP) 39
Hierarchy Levels

© TÜV Informationstechnik GmbH
Reference Architecture Model Industrie 4.0 (RAMI)
Laye
rs

06.09.2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP) 42
Industry 4.0 Component
Functions
Virtual representation (data)
Capability of communication
Type / Instance
„Thing“ / Entity

06.09.2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP) 43
Industrie 4.0 Component
Physical things
Thing Thing
Thing
Management Shell virtual representation technical functionality
Industry 4.0 component
Manifest Recource manager Condition monitoring Component management Erosion data Manual Setup Operation data /Conditions Data Sheet

all „things“ have an Internet (IP) address
all „things“ communicate using the Internet
all „things“ reach all internet connected entities
all „things“ can be reached by all those entities
all generated data transfer can be listened to
Internet of things – the new quality
06.09.2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP) 44

Functional Safety and Security
45 06.09.2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP)

IT Security and IT Safety
Security SECURITY Security Safety SAFETY Safety
Hazards by IT
Protection of man
Threats by man
Protection of IT
Security4Safety 06.09.2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP) 46

Information Communication Technology
Application Unit Sensoren
Information Unit Datenhaltung
Management Unit Anzeige Software Entscheidungsfindung
Integration communication protocol unit
06.09.2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP) 47

06.09.2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP) 48
Reference Architecture Model Industrie 4.0 (RAMI)

„Critical Infrastructures”
Transport / Traffic
Aviation
Navy
Railway
Road Traffic
Logistics
Energy
Electricity
Gas
Oil
IT&T
Telecommunication
Information Technology
Finance &
Insurance
Banks
Brokerage
Insurance Companies
Financial Services
Water Water Supply
Sewerage
Government
Administration
Parliament
Justice
Emergency & Rescue
Food Food Production
Food Trade
Sectors & Branches
49 © TÜV Informationstechnik GmbH – Member of TÜV NORD Group 06.09.2017
Health
Medical Care
Drugs / Vaccine
Laboratories
Media and Culture
Broadcast (TV and
Radio), printed and
electronic media
Monuments

Energy - Today Extra High Voltage High Voltage Medium Voltage Low Voltage
Legend: Transformer Station
Coal Plant Nuclear Power Plant
Extra High Voltage 220 or 380 kV
M/HH
~600 MVA HH/M
~600 MVA
M/HH
~200 MVA
Hydro-Electric Plant
High Voltage 110 kV
Medium Sized Power Plant Industrial
Power Plant
Industrial
Consumer
M/H
~30 MVA
H/M
~40 MVA
H/M
bis ~150 MVA
Medium Voltage 1-50 kV
M/M
bis ~150 MVA
M/N
bis ~5 MVA
M/N
bis ~5 MVA
400/230 Volt City Network
City Power Plant M/N
~2 MVA
Industrial Consumer
Feed-In
Transmission Line
Low Voltage
M/N
ca. ~0,5 MVA
400/230 Volt Rural
Network
M/N
ca. ~0,4 MVA
400/230 Volt
Wind Farm Farm
06.09.2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP) 50

Energy - Today
Energy Backend Control System
06.09.2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP) 51

06.09.2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP)

Our services – IT Security
IT Security Common Cr iter ia
Web Application Security
Security Lab Cyber Secur ity
N e t w o r k S e c u r i t y F I P S - 1 4 0 - 2
Data Center Secur i ty
IT Security Smart Grid
Pe n e t ra t i o n Te s t i n g
Biometr ics
I T - G r u n d s c h u t z ISO 27001 DataPrivacy
I S O 2 2 3 0 1
A u to m o t i v e S e c u r i t y Mobi le Secur i ty
Crit ical infrastructure
S e c u r i t y 4 S a fe t y
06.09.2017 © TÜV Informationstechnik GmbH (TÜV NORD GROUP) 53