ISSN 2395 -695X (Print) Vol. 2, Special Issue 14, May 2016 ...
Transcript of ISSN 2395 -695X (Print) Vol. 2, Special Issue 14, May 2016 ...

ISSN 2395-695X (Print)
ISSN 2395-695X (Online)
International Journal of Advanced Research in Biology Engineering Science and Technology (IJARBEST)
Vol. 2, Special Issue 14, May 2016
40
All Rights Reserved © 2016 IJARBEST
STEGNOGRAPHIC IMAGE USING
BIOMETRICS FOR REMOTE
AUTHENTICATION NAGA SOWJANYA K*, KANNAMMA R**
(M.E/CSE-II year)
*(Computer science and Engineering, Prathyusha Engineering College,Chennai
Email: [email protected])
** (Computer science and Engineering, Prathyusha Engineering College,Chennai
Email: [email protected])
ABSTRACT
In wireless communications sensitive data is frequently changed, requiring remote authentication. Remote
authentication involves the submission of encrypted data, along with visual and audio cues (facial
images/videos, human voice etc.). Nonetheless, malicious program and different attacks will cause serious
issues, particularly in cases of remote examinations or interviewing. This paper proposes a sturdy
authentication mechanism supported semantic segmentation, chaotic cryptography and knowledge
concealment. Assuming that user X needs to be remotely documented, initially X’s video object (VO) is mechanically segmental, employing a head and-body detector. Next, one amongst X’s biometric signals is encrypted by a chaotic cipher. Subsequently the encrypted signal is inserted to the most vital riffle
coefficients of the VO, victimization its Qualified Significant riffle Trees (QSWTs). QSWTs give invisibility
and vital resistance against loss transmission and compression, conditions that area unit typical in wireless
networks. Finally, the Inverse distinct riffle rework (IDWT) is applied to supply the stego-object (SO).
Experimental results, regarding: (a) security deserves of the planned cryptography theme, (b) strength to
steganalytic attacks, to numerous transmission losses and JPEG compression ratios and (c) information
measure potency measures indicate the promising performance of the planned biometrics-based
authentication theme.
Keywords — Biometrics Hiding, Steganographic System, Remote Authentication, Biometrics, QSWTs, Video
Object.
.
I. INTRODUCTION
Verification is the demonstration of affirming
reality of a trait of a datum or element. This may
include affirming the personality of a man or
programming program, following the roots of an
antiquity, or guaranteeing that an item is the thing that
it’s bundling also, naming cases to be. The two primary bearings in the verification field are sure and negative
confirmation. Positive verification is settled and it is
connected by the greater part of existing validation
frameworks. Negative confirmation has been designed
to diminish digital assaults. The contrast between the
two is clarified by the accompanying illustration: Let us
expect watchword based validation. In positive
confirmation, the passwords of all clients that are
approved to get to a framework are put away, as a rule
in a record. Accordingly the passwords space
incorporates just client’s passwords and it is typically constrained. On the off chance that wafers get the
passwords record, then their work is to recuperate the
plaintext of an extremely predetermined number of
passwords. In actuality, in negative validation the
counter secret key space is made, (hypothetically)
containing all strings that are not in the passwords
document. On the off chance that saltines get the huge

ISSN 2395-695X (Print)
ISSN 2395-695X (Online)
International Journal of Advanced Research in Biology Engineering Science and Technology (IJARBEST)
Vol. 2, Special Issue 14, May 2016
41
All Rights Reserved © 2016 IJARBEST
hostile to secret key document, their work will be much
harder. Along these lines, negative confirmation can be
presented as another layer of assurance to upgrade
existing efforts to establish safety inside systems. This
permits the present foundation to remain in place
without getting to the put away passwords or making
extra vulnerabilities. By applying a genuine esteemed
negative determination calculation, an alternate layer is
included for confirmation, keeping unapproved clients
from picking up system access.
The proposed plan is a positive validation
framework and for security reasons components from
no less than two and ideally every one of the three, of
the accompanying variables ought to be confirmed:
The proprietorship element: Something the
client has (e.g. ID card, security token, mobile
phone and so forth).
The information element: Something the client
knows (e.g., a secret word, a PIN).
The inherence variable: Something the client is
or does (e.g., unique finger impression, retinal
example, DNA grouping, face, other
biometric).
II. RELATED WORK
To condense the substance of this paper, as
opposed to existing routines specified in the past
segments, its primary commitments are broke down
beneath:
1) Biometrics-based human verification over remote
channels under flaw tolerant conventions: With the
proposed approach a few portable applications could
advantage. For instance, in a rising situation, let us
envision that a client might want to be confirmed
through her mobile phone, tablet and so forth. Her
versatile gadget has a camera, while its touch-screen
works together with a fingerprints catching application.
In the event that the sign quality is low, mistaken
parcels might touch base at the collector. Along these
lines as plan like the proposed in required.
2) Automatic extraction of semantically significant
video objects for inserting the scrambled biometric
data: The greater part of the current plans doesn’t consider semantically significant VOs as hosts, yet an
entire picture. The proposed plan offers some
conceivable points of interest. Firstly, the plan gives an
auxiliary reciprocal confirmation instrument on the off
chance that when the individual under confirmation is
likewise caught by the camera. Along these lines her
face and body is transmitted together with another
biometric highlight for conceivable twofold validation.
Besides, in each late exchange, the general structural
engineering can store the most recent example pictures
of one’s face and body. This could help in cases of half breed remote validation, when both a machine and a
human remotely validate a man. The machine can
verify the unique mark and the human can confirm the
face (like the teller does in a bank). Another point of
preference needs to do with more proficient
transmission capacity utilization, particularly in the
previously stated instance of cross breed remote
validation. A picture more often does not just contain
semantically important data additionally foundation
squares. Then again, keeping in mind the end goal to
conceal a particular measure of data, a host with
legitimate limit ought to be chosen. In the event that the
host is a picture, at that point unessential pieces will
likewise be transmitted, involving profitable data
transmission. Despite what might be expected, when
the host is a semantic VO, all transmitted data is
significant to the validation errand. To wrap things up,
the proposed plan takes into consideration more
effective rate control and can better face activity clogs.
For instance, in an average steganographic calculation
which utilizes pictures, if activity clog happens, all
picture obstructs (with the exception of those that
contain shrouded data) would be presumably
considered of equivalent significance. On the other
hand, the proposed plan is content-mindful. If there
should be an occurrence of activity blockage, the rate
control instrument could dispose of obstructs from the
body area that don't likewise contain covered up data,
rather than disposing of face territories.
3) Chaotic figure, which works like a one-time
cushion, to scramble biometric identifiers:
Symmetric encryption is speedier, in this manner in
contemporary frameworks a key of size 2n bits is
created and it is traded between the conveying
elements, utilizing open key cryptography. Be that as it

ISSN 2395-695X (Print)
ISSN 2395-695X (Online)
International Journal of Advanced Research in Biology Engineering Science and Technology (IJARBEST)
Vol. 2, Special Issue 14, May 2016
42
All Rights Reserved © 2016 IJARBEST
may, despite the fact that extensive keys are thought to
be sheltered, it has been demonstrated that any figure
with the ideal mystery property must use keys with
adequately the same prerequisites as one-time cushion
keys. For our situation, biometric identifiers are
scrambled by a disorderly figure, which works like a
one-time cushion in wording of key-size, subsequent to
the produced key has size equivalent to the size of the
information to be encoded. Tumultuous frameworks are
useful for such sorts of errands, since they display an
interminable number of insecure circles, consequently
an interminable number of various qualities.
Advancement of the turbulent figure relies on upon its
starting conditions what's more, the encoded
estimations of the biometric identifiers and in this
manner just the beginning conditions ought to be traded
between the conveying substances. In the proposed plan
this trade is likewise performed by consolidating open
key cryptography.
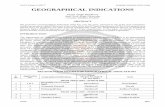
III. SYSTEM OVERVIEW
The proposed remote human confirmation plan
over remote channels under misfortune tolerant
transmission conventions plans to guarantee: (a) power
against interpreting, clamor and pressure, (b) great
encryption limit, and (c) simplicity of execution. For
this reason we: (an) utilize wavelet based
steganography, (b) encode biometric signs to take into
consideration normal confirmation, (c) include a
Chaotic Pseudo-Random Bit Generator (C-PRBG) to
make the keys that trigger the entire encryption to build
security, and (d) the scrambled biometric sign is
covered up in a VO, which can dependably be
recognized in present day applications that include
video chatting. The general structural engineering and
information stream of the proposed plan is shown in 1.
At first the biometric sign is encoded by joining a
turbulent pseudo-arbitrary piece generator what's more,
a disarray driven figure, taking into account blended
input what's more, time variation S-boxes (see likewise
Fig. 2). The utilization of such an encryption system is
defended subsequent to,
1) Mayhem presents affectability to beginning
conditions.
2) A C-PRBG factually works exceptionally
well as a one-time cushion generator,
3) Usage of famous open key encryption
systems, for example, RSA or El Gamal,can't give
suitable encryption.
Encryption calculations consolidate symmetric
and open key cryptography. Then again the security of
these calculations depends, in principle, on the trouble
of rapidly factorizing substantial numbers or settling the
discrete logarithm issue, and, by and by, on the trouble
of recording acoustic spreads from PCs amid operation.
However both levels (hypothetical and down to earth)
might be tested by late advances in number hypothesis,
conveyed figuring and acoustic cryptanalysis.
Specifically on December 12, 2009, Kleinjung et al. [1]
have calculated the 768-piece, 232-digit number RSA-
768 by the number field strainer. The number RSA-768
RSA-768 by the number field strainer. The number
RSA-768 was taken from the RSA Challenge list. The
creators likewise
Finger print
captured
Video
conference
image
vEncryptiont
Capture
Human
Face
Encrypted
image Hiding
module
Stegno
objectDB COMPRESSION
DECRYPTION
DECOMPRESSION
COMPA
RE
MAKE
PAYMENTPURCHASE
USER
USER
MATCH
MISMATCH
Fig. 1: Data flow in the proposed scheme
was taken from the RSA Challenge list. The creators
likewise asserted that it is not preposterous to expect
that 1024-piece RSA module can be considered well
inside of the following decade and have prescribed to
eliminate the utilization of 1024-piece RSA inside of
the following three to four years. Moreover in its SP

ISSN 2395-695X (Print)
ISSN 2395-695X (Online)
International Journal of Advanced Research in Biology Engineering Science and Technology (IJARBEST)
Vol. 2, Special Issue 14, May 2016
43
All Rights Reserved © 2016 IJARBEST
800-57 report [2] NIST says that utilization of 1024-
piece RSA is belittled through to the end of this year
and refused hence, unequivocally on the grounds that it
is helpless to being broken. 2048-piece RSA, in
examination, is affirmed until 2030 and denied from
that point. Obviously the previously stated references
imply that if somebody has recorded our scrambled
correspondence with 1024-piece RSA and factorization
of 1024-piece is fulfilled inside of this decade, and then
our information from the past could be uncovered. Then
again, with respect to acoustic cryptanalysis, Genkin et
al. [3] portray another acoustic cryptanalysis key
extraction assault, appropriate to GnuPGs current
execution of RSA. The assault can remove full 4096-
piece RSA unscrambling keys from smart phones
(different models), inside of 60 minutes, utilizing the
sound produced by the PC amid the decoding of some
picked cipher texts.
4) Private-key mass encryption calculations:
For example, Triple- DES or Blowfish, correspondingly
to confused calculations, are more suitable for
transmission of a lot of information. Right now both
calculations are viewed as secure enough when
executed effectively, be that as it may, because of the
many-sided quality of their inward structure, they can't
be succinctly and unmistakably clarified, so that to
empower location of conceivable cryptanalytic
vulnerabilities, if any. Specifically, defective executions
might make both calculations unreliable (e.g. meet-in-
the-center assault for Triple-DES [4] or brilliantly
powerless keys assault for Blowfish [5]). Besides the
FAQ for GnuPG2 prescribes that Blowfish ought not to
be utilized to scramble records that are bigger than 4
Gb.A short time later, a head-and-self-perception of the
biometric sign's proprietor is broke down and the host
VO is naturally extricated in view of the strategy
proposed in [6].Next a DWT-based calculation is
proposed for concealing the scrambled biometric signal
to the host VO. The proposed calculation conceals the
scrambled data into the biggest worth QSWTs of
vitality productive sets of sub bands. Contrasted with
other related plans, the joined methodology has the
accompanying favorable circumstances [7]:
(a)It is a standout amongst the most proficient
calculations of writing that encourages vigorous
covering up of outwardly conspicuous.
(b) It is progressive and has multi-resolution
qualities.
(c)The installed data is difficult to identify by
the human visual framework (HVS), and it is among the
best known systems with respect to survival of
shrouded data after picture pressure.
At first the extricated host article is deteriorated
into two levels by the distinguishable 2-D wavelet
change, giving three sets of sub bands (HL2, HL1),
(LH2, LH1) and (HH2, HH1). A short time later, the
pair of sub bands with the most astounding vitality
substance is distinguished and a QSWTs methodology
is joined [8] with a specific end goal to choose the
coefficients where the scrambled biometric sign ought
to be thrown. At long last, the sign is needlessly
installed to both sub bands of the chose pair, utilizing a
non-straight vitality versatile insertion methodology.
Contrasts between the first and the stego-object are
subtle to the human visual framework (HVS), while
biometric signs can be recovered even under pressure
and transmission misfortunes.
IV. CONFUSED ENCRYPTION
Blowfish is a symmetric-key block cipher,
designed in 1993 by Bruce Schneier and included in a
large number of cipher suites and encryption products.
Blowfish provides a good encryption rate in software
and no effective cryptanalysis of it has been found to
date.
Algorithm
Blowfish has a 64-bit block size and a variable
key length from 32 bits up to 448 bits. It is a 16-round
Feistel cipher and uses large key-dependent S-boxes. In
structure it resembles CAST-128, which uses fixed S-
boxes.

ISSN 2395-695X (Print)
ISSN 2395-695X (Online)
International Journal of Advanced Research in Biology Engineering Science and Technology (IJARBEST)
Vol. 2, Special Issue 14, May 2016
44
All Rights Reserved © 2016 IJARBEST
Fig.2. the Feistel structure of Blowfish
The diagram to the left shows Blowfish's
encryption routine. Each line represents 32 bits. There
are five subkey-arrays: one 18-entry P-array (denoted as
K in the diagram, to avoid confusion with the Plaintext)
and four 256-entry S-boxes (S0, S1, S2 and S3).Every
round r consists of 4 actions: First, XOR the left half
(L) of the data with the r th P-array entry, second, use
the XORed data as input for Blowfish's F-function,
third, XOR the F-function's output with the right half
(R) of the data, and last, swap L and R.The F-function
splits the 32-bit input into four eight-bit quarters, and
uses the quarters as input to the S-boxes. The S-boxes
accept 8-bit input and produce 32-bit output. The
outputs are added modulo 232
and XORed to produce
the final 32-bit output.After the 16th round, undo the
last swap, and XOR L with K18 and R with K17
(output whitening).Decryption is exactly the same as
encryption, except that P1, P2... P18 are used in the
reverse order. This is not so obvious because xor is
commutative and associative. A common
misconception is to use inverse order of encryption as
decryption algorithm (i.e. first XORing P17 and P18 to
the cipher text block, then using the P-entries in reverse
order.Blowfish's key schedule starts by initializing the
P-array and S-boxes with values derived from the
hexadecimal digits of pi, which contain no obvious
pattern (see nothing up my sleeve number). The secret
key is then, byte by byte, cycling the key if necessary,
XORed with all the P-entries in order. A 64-bit all-zero
block is then encrypted with the algorithm as it stands.
The resultant ciphertext replaces P1 and P2. The same
ciphertext is then encrypted again with the new
subkeys, and the new ciphertext replaces P3 and P4.
This continues, replacing the entire P-array and all the
S-box entries. In all, the Blowfish encryption algorithm
will run 521 times to generate all the subkeys - about
4KB of data is processed.Because the P-array is 576
bits long, and the key bytes are XORed through all
these 576 bits during the initialization, many
implementations support key sizes up to 576 bits. While
this is certainly possible, the 448 bits limit is here to
ensure that every bit of every subkey depends on every
bit of the key,as the last four values of the P-array don't
affect every bit of the ciphertext. This point should be
taken in consideration for implementations with a
different number of rounds, as even though it increases
security against an exhaustive attack, it weakens the
security guaranteed by the algorithm. And given the
slow initialization of the cipher with each change of
key, it is granted a natural protection against brute-force
attacks, which doesn't really justify key sizes longer
than 448 bits.
IV. CONCEALING THE ENCRYPTED
BIOMETRIC SIGNAL
A. Embedding Process
Let size of cropped image is Mc×Nc where
Mc≤ M and Nc≤N and Mc=Nc. i.e. Cropped region must be exact square as we have to apply DWT later on
this region. Let S is secret data. Here secret data
considered is binary image of size a×b.
a) Algorithm for embedded process
1) Step1: While video conferencing held on,
individual’s image is captured and sends for further processing. From the captured image, it can be cropped
to get cropped image (M*N).

ISSN 2395-695X (Print)
ISSN 2395-695X (Online)
International Journal of Advanced Research in Biology Engineering Science and Technology (IJARBEST)
Vol. 2, Special Issue 14, May 2016
45
All Rights Reserved © 2016 IJARBEST
Fig.3. Flowchart for embedding process
2) Step2: With the help of cropped image, apply skin
detection image. This will produce mask image that
contains skin and non skin pixels.
3) Step3: Encrypt the cropped image and apply the
DWT.
4) Step4: Embed the cropped image with biometric
signal and perform IDWT.
5) Step5: Finally stegno cropped image was produced
and stored in database.
b) Algorithm for extraction process
1) Step1: Load stegno image from database
2) Step2: Perform Skin detection image and crop image
(M*N).
3) Step3: Perform DWT method and finally decrypt
image.
4) Step4: finally original image has been retrieved.
Fig.4.Flowchart of extraction process
V. REMOTE SERVER AUTHENTICATION
In the module, remote server authentication is
going to be performed. If user wants to access the
application means he/she has to give his face and
biometrics to the server. Server will match face with
every face on the database. If server identified the
matched face means, server will extract the fingerprint
from that image. After extracting, server checks the
face and biometrics into the matched face and
biometrics. If both are matches only server will
authenticate the user.
VI.SIMULATION RESULTS
In this section we demonstrate simulation
results for proposed scheme.This have been
implemented using MATLAB 7.0. A 24 bit color image
is employed as cover image of size 356×356,

ISSN 2395-695X (Print)
ISSN 2395-695X (Online)
International Journal of Advanced Research in Biology Engineering Science and Technology (IJARBEST)
Vol. 2, Special Issue 14, May 2016
46
All Rights Reserved © 2016 IJARBEST
(a) (b)
(c)
Fig.5. (a) Original image (b) Biometric signal
(c) Watermarked image
VII. CONCLUSION
The proposed method, with the exception of
giving results that are indistinct to the human visual
framework, it additionally yields a stego-object that can
oppose diverse sign contortions, and steganalytic
assaults. Trial assessment and nitty gritty hypothetical
security investigation outline the execution of the
proposed framework as far as security. The understood
NIST tests were connected to the encoded biometric
signals to check the vigor of the proposed clamorous
encryption plan. A progression of steganalytic assaults
were moreover connected, utilizing condition of-
workmanship steganalysis devices. Results show that
the utilization of QSWTs gives abnormal amounts of
vigor, keeping in the meantime the simplicity of usage
and the similarity to surely understand and generally
utilized picture and video pressure norms. In future
research, the impacts of pressure and portable
transmission of other shrouded biometric signals (e.g.
voice or iris) ought to additionally be inspected.
REFERENCES
[1] T. Kleinjung, K. Aoki, J. Franke, A. K. Lenstra, E.
Thom´e, J. W. Bos,P. Gaudry, A. Kruppa, P. L.
Montgomery, D. A. Osvik, H. Te Riele,A. Timofeev,
and P. Zimmermann, “Factorization of a 768-bit rsa
modulus,” in Proceedings of the 30th Annual
Conference on Advances in Cryptology. Springer-
Verlag, 2010, pp. 333–350.
[2] E. Barker, W. Barker, W. Burr, W. Polk, and M.
Smid, “Recommendation for key management part 1:
General (revision 3),” in NIST Special Publication 800-
57. Computer Security, Computer Security
Division,Information Technology Laboratory, National
Institute of Standards and Technology Gaithersburg,
MD 20899-8930, Jul. 2012.
[3] D. Genkin, A. Shamir, and E. Tromer, “Rsa key
extraction via low-bandwidth acoustic cryptanalysis,”
in Cryptology ePrint Archive, Report 2013/857, 2013.
Available:http://www.cs.tau.ac.il/%7Etromer/papers/ac
oustic-20131218.pdf.
[4] S. Murdoch, M. Bond, and R. J. Anderson, “How
certification systems fail: Lessons from the ware
report,” IEEE Security and Privacy, vol. 10, no. 6, pp.
40–44, Nov. 2012.
[5] O. Kara and C. Manap, “A new class of weak keys
for blowfish,”in Proceedings of the 14th International
Conference on Fast Software Encryption. Springer-
Verlag, 2007, pp. 167–180.
[6] N. D. Doulamis, A. D. Doulamis, K. S. Ntalianis,
and S. D. Kollias, “An efficient fully-unsupervised
video object segmentation scheme using an adaptive
neural network classifier architecture,” IEEE
Transactions on Neural Networks, vol. 14(3), pp. 616–630, 2003.
[7] M.-S. Hsieh, D.-C. Tseng, and Y.-H. Huang,
“Hiding digital watermarks using multiresolution
wavelet transform,” IEEE Transactions on Industrial
Electronics, vol. 48(5), pp. 875–882, 2001.
[8] K. S. Ntalianis, N. D. Doulamis, A. D. Doulamis,
and S. D. Kollias, “Automatic stereoscopic video
object-based watermarking using qualified significant
wavelet trees,” in Proceedings of the IEEE International
Conference on Consumer Electronics. IEEE, 2002, pp.
188–189.