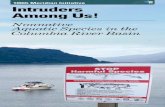
Intruders (and How to Keep Them Out) - Course Web Pages · 3 CMP S12,U ant ruz Intruders 5 Overlap...
Transcript of Intruders (and How to Keep Them Out) - Course Web Pages · 3 CMP S12,U ant ruz Intruders 5 Overlap...

1
Intruders (and How to Keep Them Out)
Intruders 2CMPS 122, UC Santa Cruz
Overview
• More on intrusions• Detecting intruders• Dealing with intruders once you’ve found them• Firewalls• Computer immunology

2
Intruders 3CMPS 122, UC Santa Cruz
Why detect intruders?
• Catch them before they cause damage◆ Plug holes◆ Watch how they do it…
• Identify damage• Collect evidence for prosecution• Deterrent
Intruders 4CMPS 122, UC Santa Cruz
Behavior
Obviously Normal Obviously Malicious

3
Intruders 5CMPS 122, UC Santa Cruz
Overlap between users & intruders
Measurablebehavior parameter
Probability densityfunction Authorized user
profile
Intruderprofile
Intruders 6CMPS 122, UC Santa Cruz
Users & intruders: the truth
Measurablebehavior parameter
Probability densityfunction
Authorized userprofile
Intruderprofile
There just aren’t that many intruders!

4
Intruders 7CMPS 122, UC Santa Cruz
Problems with false positives
• Doctor invents a new, inexpensive test for a deadlydisease that is 99% accurate
• Assume 1 in 2000 people have deadly disease (butdon’t know it yet)
• Should everyone get the test?◆ 2000 people tested◆ Expect .99 + (1999 * .01) positives◆ 21 people will be told they have disease
• If you test positive, there is about a 5% chance youhave disease◆ Higher than 1/2000, but not that high!
Intruders 8CMPS 122, UC Santa Cruz
Intrusion detection approaches
• Statistical anomaly detection◆ Produce a profile of the normal behavior of each user (or
independent of user)◆ Notice statistical deviations from that behavior
• Rule-based detection◆ Think really hard and make up rules that describe intruder
behavior◆ Hope intruders can’t read and figure out the rules also◆ Lay traps that normal users won’t trigger…

5
Intruders 9CMPS 122, UC Santa Cruz
Statistical anomaly detection
• Track events and characteristics of the system◆ Network packets (source, size, number, protocol, port)◆ Program behavior
– Which programs are run when– What arguments are given to program
◆ User behavior– Login pattern– Files accessed
• Look for “unusual” patterns◆ Need a background “level” of normal activity◆ Must account for “normal anomalies”
– Example: user decides to try a new program– Example: user works late to finish a project
Intruders 10CMPS 122, UC Santa Cruz
Attacker VictimSYN
SYN/ACK
ACK
Anomaly detection example
• Common denial of service (DoS) atttack: SYN flood• Normal TCP: SYN, SYN/ACK, ACK• DoS: SYN, SYN/ACK, ignored
◆ SYN/ACK packets queue up on victim◆ Number of queued SYN/ACK packets is limited!◆ No new connections once limit is exceeded
• Can this be detected?

6
Intruders 11CMPS 122, UC Santa Cruz
Detecting SYN floods
• Firewall (or other gateway) notices large number ofSYN packets but few ACK packets◆ Firewall isn’t actually queueing anything◆ Firewall simply observes the traffic going by
• Firewall decides that hosts behind it will crash ifmore SYN packets come in
• Firewall temporarily suspends delivery of SYNpackets
• Result: hosts are protected◆ Unfortunately, nobody can connect to those hosts while
they’re being protected◆ This is temporary, so situation will recover quickly
Intruders 12CMPS 122, UC Santa Cruz
Network intrusion detection
• Monitor activity on many hosts• Aggregate audit records to detect anomalous
behavior◆ Innocuous behavior on several (individual) hosts may
signal an intrusion◆ Example: limited (or slow) port scan across many
computers in sequence
• Managed Security Monitoring (Counterpane, Inc.)

7
Intruders 13CMPS 122, UC Santa Cruz
Network intrusion detection example
• Intruder wants to break into any computer atcompany X
• Rapid port scan on a single computer is easilydetected◆ Computer knows that its ports are being scanned◆ Security system on computer notifies someone
• Solution: scan computer sequentially◆ No individual computer is scanned rapidly◆ Many computers are scanned in a short time
• Protection: firewall that examines all packets◆ Notices sequential port scan because firewall sees all port
scan packets destined for any computer◆ Firewall takes action against the intruder
Intruders 14CMPS 122, UC Santa Cruz
Network intrusion detection example
• User / password guessing attack• Single computer may impose limits for login
◆ At most n outstanding login attempts at any time◆ At least m seconds between login attempts for a given user
• Multiple computers (with the same users /passwords) may not have such limits◆ Try different users on different computers at the same time◆ All you need is one successful user / password pair…

8
Intruders 15CMPS 122, UC Santa Cruz
Network intrusion detection solution?
• All of these attacks come from one IP address (or smallrange)
• Solution (?): check for network-type attacks coming from asmall set of IP addresses◆ Protects hosts from attacks originating in a single place◆ Doesn’t stop distributed attacks!
• Intruders often come from many different IP addresses◆ First, hijack many other computers to help
– Often, computers with little useful stuff, but poorly protected◆ Second, run a distributed attack from these computers
• Much harder to detect and deal with◆ No single set of IP addresses to “blame”◆ Activity often looks like normal (if a bit irregular) operation
Intruders 16CMPS 122, UC Santa Cruz
Rule-based intrusion detection
• Similar to anomaly-based detection◆ Anomaly-based uses shades of gray◆ Rule-based is usually black and white
– If this is done, it’s an intrusion• Most helpful when security system knows more
about the system than the intruder◆ Example: set up fake user accounts and passwords
– Make them more than one character different from “real” usernames
◆ If someone attempts to log into a fake account severaltimes, it’s probably an intruder
• This can be detected regardless of how distributedthe attack is

9
Intruders 17CMPS 122, UC Santa Cruz
Rule-based intrusion detection example
• Simple rule: all data sent to the SMTP (mail) portmust be textual, and must have line length < 80◆ Allows most normal email to go through
– Take care to encode mail with MIME to follow rules◆ Prevents most stack-smashing attacks against sendmail
• This rule can be enforced by the firewall◆ Examines packets as they go by◆ Knows enough about SMTP to reconstruct incoming data◆ Tests for maximum line length (simple test)◆ Doesn’t test for
– Unknown user– Use of your SMTP host for mail forwarding– Sending large email messages to clog the mailbox
Intruders 18CMPS 122, UC Santa Cruz
Rule-based intrusion detection example
• Simple rule: incoming HTTP packets may not contain Javaapplets◆ Prevents malicious Web pages from coming in◆ Can be done without detailed knowledge of Web page structure
– Simply recognize HTML that encapsulates Java• Can easily be done by firewall that knows a bit of HTTP• Problem: can’t tell the difference between “good” and “bad”
Java◆ Prevents users from accessing sites with useful Java!◆ May be too restrictive: users will find a way to circumvent
• Instead, try to recognize incoming Java known as malicious• Perhaps also try to recognize attacks by keeping signatures of
Java files that have come in recently◆ Prevent “repeat offenders”…

10
Intruders 19CMPS 122, UC Santa Cruz
Firewalls: detecting and stopping intruders
• Intrusion detection & prevention is hard!◆ Difficult to do well◆ Difficult to even detect an intrusion, particularly when it
affects multiple computers• One solution: use a firewall• Firewall goals
◆ All traffic between internal network and external network(Internet) must pass through the firewall
◆ Only “authorized” traffic is allowed to pass (more on thisin a bit)
◆ Firewall itself is immune to penetration– This can be easier for a firewall because it doesn’t allow general-
purpose logins– May not have a full operating system…
Intruders 20CMPS 122, UC Santa Cruz
Firewall techniques
• Service control◆ Determine which services can be accessed◆ Disallow those that might be risky
• Direction control◆ Control the direction in which certain services are available◆ Network Address Translation may help with this…
• User control◆ Control access to services based on user◆ Requires that users authenticate themselves somehow
• Behavior control◆ Disallow dangerous behaviors◆ Example: filter email for viruses◆ Example: allow only certain types of HTTP requests

11
Intruders 21CMPS 122, UC Santa Cruz
Secure area
Firewall: packet filter
• Filter each packet as it goesthrough
• Apply a set of rules◆ Discard or accept packet
depending on rule matches• Rules based on
◆ IP addresses◆ Protocol◆ Port number◆ Packet content?
• Must set default policy◆ Accept◆ Discard
• Rules can modify thepolicy for particular packets
Internet
Firewall
Internalnetwork
Intruders 22CMPS 122, UC Santa Cruz
Packet filtering rules: example
Allow ssh in both directions*22***Allow
Allow outbound HTTPS*443**Our hostAllow
Default policy is to block**Our net**Deny
Default is to block outgoing****Our netDeny
Except from our mail server*25**MailhostAllow
Disallow outgoing email…*25**Our netDeny
Allow outbound web*80**Our netAllow
Allow inbound web*80www**Allow
Allow inbound email*25Mailhost**Allow
CommentFlagsPortDestPortSrcAction

12
Intruders 23CMPS 122, UC Santa Cruz
Limitations to packet filtering
• Packet filtering is nice, but there are limits
• Firewall can only filter on individual packet contents◆ Can’t see the entire session◆ Allows intruder to break up attack to sneak it in◆ Can’t respond to attacks that involve breaking a protocol,
such as SYN floods• May be vulnerable to address spoofing
◆ Packet has incorrect return address• Better solution: allow firewall to filter on entire
sessions, not just individual packets
Intruders 24CMPS 122, UC Santa Cruz
Stateful Packet Inspection (SPI)
• Keep track of history of packets◆ Allow filtering and actions based upon history!
• Example: inbound packets to “user” ports (>1024)◆ Must allow some of them for any protocol to work◆ SPI: only allow them if an outgoing connection on that port was
previously requested– This is more secure!
• Example: SYN floods◆ TCP connection is set up by three way handshake◆ Attack: do only the first of three, leaving lots of “open” connections◆ Solution: firewall times out unfinished handshakes
• Example: distributed port scan◆ Look for vulnerable network ports◆ Firewall sees lots of activity to similar ports on different machines

13
Intruders 25CMPS 122, UC Santa Cruz
Application-level gateway (proxy server)
• Only proxy server can talk to external network• Run applications on proxy server that relay
information between inside and outside◆ Example: HTTP proxy◆ Example: mail server
• Monitor proxy server for attacks◆ Log all traffic in and out◆ Attacks still possible, but only against a single machine◆ Response: disable the single point of entry
• Makes security easier: single point to secure• Drawbacks
◆ Slower: two back-to-back circuits◆ Need a proxy for every protocol!
Intruders 26CMPS 122, UC Santa Cruz
Circuit-level gateway (SOCKS)
• Proxy server requires one proxy per application• Circuit gateway does its work at the TCP level
◆ Each outgoing connection is made to the SOCKS server◆ SOCKS server establishes a separate TCP connection to
the outside server• Advantages
◆ Simpler than using a separate proxy for each service◆ Other advantages of proxy server (monitoring, etc.)
• Drawbacks◆ May require changes on client side◆ Still somewhat slow: SOCKS server acts as relay

14
Intruders 27CMPS 122, UC Santa Cruz
Bastion host
• Where are proxy servers or circuit gateways run?• Separate servers?
◆ Need to secure each server against intrusion◆ Need to monitor all servers…
• Single server?◆ Put all of the outside services in one place◆ Watch that computer very carefully!
• This single server is often called a bastion host• Bastion host can have simpler, more secure code
◆ Proxies are often smaller than full servers◆ Proxies need not perform disk access◆ Proxies don’t permanently store any sensitive data◆ Proxies can run as normal users (not root)
Intruders 28CMPS 122, UC Santa Cruz
Using firewalls & bastion hosts: guidelines
• Important: a single line of defense is not enough!◆ It’s difficult to get through a firewall, but not impossible◆ Multiple lines of defense can slow down an attacker
– Allow him to be detected– Allow the network to be cut off before there’s further damage
• Configure multiple lines of defense so that they’re moredifficult than just one
• Protect more important resources with more defenses• Use diverse types of firewalls and bastion hosts!
◆ Three firewalls of the same model may be no harder to compromisethan one firewall
• Disallow logins, particularly from the outside world◆ It’s more difficult to get access to a serial line than to a Web browser
interface◆ Single-purpose OS is more difficult to get into

15
Intruders 29CMPS 122, UC Santa Cruz
Secure area
Basic firewall & bastion host configuration
• Traffic controlled by firewall• Drawbacks
◆ Firewall has to do a lot of work◆ Bastion host can be bypassed◆ Compromises hard to deal with: isolation is difficult
Internet Firewall
Web server
Bastion host
Privatenetwork
Intruders 30CMPS 122, UC Santa Cruz
Secure areaDemilitarized zone
One firewall, two zones
• Traffic still controlled by firewall• Traffic between private network and outside must go through
bastion host◆ Must compromise both firewall and bastion host to intrude
• Bastion host and Web server are in a demilitarized zone• Critical resources kept in secure area
Internet Firewall
Web server
Bastion host
Privatenetwork

16
Intruders 31CMPS 122, UC Santa Cruz
Secure areaDemilitarized zone
Two firewalls, three zones
• Similar to previous configuration• Addition: firewall between bastion host and private network
◆ Allows for more filtering◆ Must now break into two firewalls as well as bastion host
• Private network doesn’t know about Internet• Internet doesn’t know about private network
Internet Firewall1
Web server
Bastion host
PrivatenetworkFirewall2
Intruders 32CMPS 122, UC Santa Cruz
Honeypots
• To keep the system safe, set up resources that an attacker can(relatively easily) get a hold of
• Make sure that these resources can’t lead to further breakins• Example: fake user & shell
◆ Set up fake user names & passwords with rewritten shell◆ Ensure that these user names are easier to break into
– Simpler passwords– Remote shell
◆ Make fake data available to shell, perhaps using chroot()◆ Install fake programs such as ls and telnet/ssh to track what the
intruder is doing– Programs appear to work, but provide false data
• Keep the intruder on the system as long as possible to tracewhere he’s coming from!

17
Intruders 33CMPS 122, UC Santa Cruz
More honeypots
• Rather than simply having fake accounts, haveentire fake machines◆ Systems are cheap!◆ Intruders may not know that these systems aren’t useful◆ Install lots of interesting (but fake) data on the computers
• This mechanism can work wonders if the false datais ever leaked…◆ Excellent way to figure out who’s getting the data
“stolen” from your computer system◆ Makes intruders happy because they think they’ve won
Intruders 34CMPS 122, UC Santa Cruz
Jails and sandboxes
• Honeypots are nice, but how can we ensure that no real damage is done?• Have the OS (or virtual machine) restrict what a user can do
◆ Restrict calls that read or write the file system– Disable writes, or limit them to a particular area– Change the root directory
◆ Limit the ability to create new processes or allocate memory◆ Limit the programs that are available
• Have the OS (or virtual machine) do more checks on activity inside thesandbox or jail◆ May slow down users in the jail◆ Not such a big deal because such users are typically outsiders
• Overhead of jails and sandboxes may be worth it for general use,particularly now that CPU time is becoming free

18
Intruders 35CMPS 122, UC Santa Cruz
What if an intrusion is detected?
• Do nothing◆ Not a good idea, particularly if data is at risk
• Log intruder’s actions to a “safe” computer◆ Print out messages on the “console”◆ Console is a serial line connected to another computer not attached to
any network– Standalone computer records serial line inputs for later perusal (virtual
printer)– May be possible to break in via serial line, but not easy
• Contact system administrator (email and/or page)◆ System administrator can track down the attacker◆ System administrator can monitor what attacker is doing
• Shut down system◆ May shut down intruder’s processes instead, but this may not go far
enough• Do several of the above
Intruders 36CMPS 122, UC Santa Cruz
Tell someone about the intrusion!
• Contact system administrator (email and/or page)◆ System administrator can track down the attacker◆ System administrator can monitor what attacker is doing◆ System administrator can shut down the system…
• Shut down system◆ May shut down intruder’s processes instead, but this may
not go far enough◆ Shut down has two main advantages
– Intruder can’t do any further damage to this system– Intruder can’t use the system as a launching pad for further attacks
◆ Shut down disadvantage: your users are inconvenienced– May not be necessary for many attacks

19
Intruders 37CMPS 122, UC Santa Cruz
Countermeasures
• The intruder’s gotten in; now what?• Actively “observe” him
◆ Lay traps on the fly◆ Correct all (or some) of the changes he makes◆ Ensure that no critical resources are being affected
• Look to see what’s been changed◆ Modification times of files
– Can easily be spoofed!– Not necessarily helpful
◆ Secure hash of files– Harder to fake these, if the hash program is run from CD– “Expected” hash values ought to be on CD too…
Intruders 38CMPS 122, UC Santa Cruz
Forensic analysis
• After an attack has happened, analyze what went on◆ Figure out what’s been damaged◆ Learn how the attack worked to prevent it (and similar
attacks) from happening again• Tell the world about it!
◆ Keeping it secret may save (your) face◆ Keeping it secret will certainly harm others
– Nobody else knows about how to defend against the intrusion– Others may have more information on how the intruder works

20
Intruders 39CMPS 122, UC Santa Cruz
Recovering from an attack
• Restore files from a backup◆ You do have a backup, don’t you?◆ Ensure that the backup doesn’t have compromised files…
• Reinstall as much as you can◆ Unlikely that the install CD has compromised files, but…◆ It’s certainly possible—Micro$oft has shipped CDs with
viruses on them!• Use a file system that doesn’t overwrite in place
◆ Many file systems support “snapshots”◆ Use the most recent snapshot that wasn’t damaged
Intruders 40CMPS 122, UC Santa Cruz
Sample attack
• Lots of books discuss hackers and their exploits◆ Firewalls and Internet Security: Repelling the Wily Hacker,
Cheswick, Bellovin, and Rubin◆ Practical Unix & Internet Security, Garfinkel, Schwartz, and Spafford◆ The Cuckoo’s Egg, Stoll
• Sample exploit from Repelling the Wily Hacker

21
Intruders 41CMPS 122, UC Santa Cruz
An Evening with Berferd
• Excerpted from Repelling the Wily Hacker
• Attack occurred in 1991• Intruder broke into a little-used system• Attack didn’t cause much damage because
◆ System was largely unused◆ Attack was caught in time◆ Hacker wasn’t all that skilled
Intruders 42CMPS 122, UC Santa Cruz
First step: get the password file
• Hacker connected to sendmail◆ Asked it to send him the password file◆ File sent to user on another computer he had hacked
– Covers his tracks somewhat◆ Goal: crack some passwords to log into the system
• Responses◆ Sysadmin decided to send him the real password file◆ Sysadmin logged the attack
• Password file quickly moved to France!◆ Another sysadmin notified the original sysadmin

22
Intruders 43CMPS 122, UC Santa Cruz
Second step: try to log in
• Checked to ensure that target user wasn’t logged in• Attempted to use sendmail to add a new account
with no password◆ Sendmail is very insecure (getting better, but still…)◆ Solution: sysadmin made the machine seem slow so he
could keep up in real time◆ Login succeeds because it was allowed to do so
• At this point, sysadmin monitoring attack in realtime
Intruders 44CMPS 122, UC Santa Cruz
Third step: do damage
• Get copies of configuration files to see what servicesare active
• Modify daemons (finger, inetd) to more hacker-friendly versions
• Fortunately, all of this took place in a jail that thesysadmin set up!◆ Easier to clean up◆ Hacker’s activities studied in detail◆ Little damage to the real system, which wasn’t all that
important anyway

23
Intruders 45CMPS 122, UC Santa Cruz
Fourth step: catch the perpetrator
• This proved to be very difficult◆ Attack could come from anywhere in the world◆ Tracing an attack after the fact can be difficult, if not impossible◆ Some information from timing of the attack
• Fortunately, call tracing went on during the attack◆ Calls traced back to Netherlands eventually◆ Dutch phone company refused to trace—not illegal to hack in the
Netherlands!• Prosecution was even more difficult
◆ Hacking not illegal in the Netherlands, so nearly impossible toextradite
◆ Article published in the New York Times◆ Hackers exchanged email about the attack (collected by Dutch
professor tracking hackers)◆ No legal action ever taken…
Intruders 46CMPS 122, UC Santa Cruz
Challenges in intrusion detection
• The first thing a smart intruder will do is tamperwith the intrusion detection system!◆ Cover his tracks◆ Prevent a warning
• Few activities are either obviously normal orobviously malicious◆ Intruders take steps to avoid being noticed◆ Regular users may do intruder-like things
– I’ve tried to use sudo on machines where I’m not authorized
• False positives dilemma◆ Crying “wolf” too often makes the system useless

24
Intruders 47CMPS 122, UC Santa Cruz
Immunology
• Study of biological viruses• Applicable to computer science
◆ Computer viruses may act like biological ones◆ Lessons from biology may be relevant
• How do biological viruses work?
Intruders 48CMPS 122, UC Santa Cruz
Biological inspiration
• Biological systems are incredibly resilient• Most humans survive ~80 years• Before medical advances, most still would survive
~30 years• Operate in a hostile, unpredictable environment• No way to reboot, reinstall operating system,
upgrade software, etc.• Human genome:
◆ 3 Billion base pairs = 6 Gb = 750 MB◆ (Human genome project says 3GB ??)

25
Intruders 49CMPS 122, UC Santa Cruz
An Overview of the Immune System.© 1997 Steven A Hofmeyr
Immune systems
• Lymphocytes recognizepathogens by binding.◆ Proteins have distinctive
shapes.• Binding is approximate
◆ Sometimes match wrongthings
– Reject organ transplants– Destroy own cells (I’m very
familiar with this one)◆ Tradeoff between
overactivity and underactivity– Overactive: auto-immune
disorders– Underactive: diseases not
detected
Intruders 50CMPS 122, UC Santa Cruz
Receptor diversity
• Need to recognize all foreign intruders, but DNAcan’t know about all possible intruders
• Gene segments are randomly combined to formdifferent receptors◆ About 108 – 1012 different receptors

26
Intruders 51CMPS 122, UC Santa Cruz
Affinity maturation
• B-cells in bone marrow –most effective cellsreproduce more quickly
An Overview of the Immune System.© 1997 Steven A Hofmeyr
Intruders 52CMPS 122, UC Santa Cruz
Can computers do this?
• Programs identified by sequences of system calls• Build a database of normal patterns (how?)• Receptors recognize unusual patterns• Enough unusual patterns is considered an intrusion

27
Intruders 53CMPS 122, UC Santa Cruz
Fatal flaws?
• Might work okay if no one important is using it• Will it work if an attacker knows about it and is
deliberately constructing an attack to avoiddetection?◆ Do biological viruses evolve to mimic host proteins?
• Biological diversity: many organisms, so virusesmust specialize
• Computers don’t have such diversity◆ Majority of computers run Windoze◆ Majority of computers have x86 processors◆ Result: viruses specific to x86/Windoze are rampant◆ Viruses specific to MS Office/Outlook also common