Introduction IT Risk Management Chap1
-
Upload
fikri-arsyadi -
Category
Documents
-
view
223 -
download
0
Transcript of Introduction IT Risk Management Chap1

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 1/65
108/24/15
Introduction toInformationSecurity

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 2/65
208/24/15
Agenda
1. Introduction
2. In Through The Out Door
3. The Security Management Cycle4. Specic Concept! " Technology
#. Summary " $ue!tion!

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 3/65
308/24/15
%&Commerce Internet 'eality
What makes the Internet powerful
also makes it insecure
Strengths of Internet
Ubiquitous andglobal network
Rapid evolution tomeet market needs
Eas to a!!ess " open andstandard inter#a!es
Internet Weaknesses
$onstant introdu!tion o#new vulnerabilities
%ultiple entr points t&at
are !onstantl evolving
E'posure to global sour!e
o# !ber atta!k

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 4/65
408/24/15
(hat !ecurity )reeche! are youconcerned a)out*
+ Damage to data and net,or-*
+ Theft of corporate a!!et!*
+ Theft of cu!tomer data*+ Do,ntime a!!ociated ,ith DOS attac-!*
+ re!! a!!ociated ,ith attac-*
+ Internal attac-!*

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 5/65
508/24/15
(hat ri!-! are you concerneda)out*
+ /o!! of re0enue*
+ Impact on !hareholder 0alue*
+ Damage to your )rand euity image*
+ Di!ruption in )u!ine!! and !ale! proce!!e!*
+ /o!! in Cu!tomer Tru!t*

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 6/65
(08/24/15
I!!ue! rom the Out!ide&In
+ Common oal!5 6eed connecti0ity from )u!ine!! partner!
5 'emote u!er! need acce!! to o7ce application !y!tem!
5 ro0ide %MAI/ !er0ice! to !ta8
5 ro0ide (%9 !er0ice! to cu!tomer!
+ Threat!5 Intru!ion from the Internet
5 Interception of pa!!,ord!
5 Modication of !y!tem! or data
5 Denial of Ser0ice
Section
2

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 7/65)08/24/15
I!!ue! rom the In!ide&Out
+ Common oal!5 Connecti0ity to )u!ine!! partner!5 Connecti0ity to the Internet for ((( !er0ice!
5 Connecti0ity to AS for out&!ourced !er0ice!
5 Chec- and !end %MAI/+ Threat!
5 Intru!ion! from !ta8
5 Interception of pa!!,ord!
5 Modication of !y!tem! or data5 :iru!
5 :andal

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 8/65808/24/15
(hat I! Information Security*
Information security in today*s
enterprise is a + well-informed sense ofassurance that the information risksand controls are in balance.,
–Jim Anderson, Inovant (22!

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 9/65-08/24/15
(hat I! Security*
. +&e qualit or state o# being se!ure "to be #ree #rom danger,
. o be prote!ted #rom adversaries
. su!!ess#ul organiation s&ould &avemultiple laers o# se!urit in pla!e
" &si!al se!urit
" ersonal se!urit
" perations se!urit
" $ommuni!ations se!urit
" etwork se!urit

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 10/651008/24/15
(hat I! Information Security*
. &e prote!tion o# in#ormation and its !riti!alelements6 in!luding t&e sstems and &ardwaret&at use6 store6 and transmit t&at in#ormation
. ools6 su!& as poli!6 awareness6 training6edu!ation6 and te!&nolog are ne!essar
. &e $777 triangle was t&e standard based oncon#identialit6 integrit6 and availabilit
. &e $777 triangle &as e'panded into a listo# !riti!al !&ara!teristi!s o# in#ormation

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 11/651108/24/15
Critical Characteri!tic! of Information
"he value of information comes from thecharacteristics it possesses.– Availability
– Accuracy– Authenticity– #onfidentiality
– Inte$rity– %tility– &ossession

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 12/651208/24/15
6STISSC Security Model ;4<11=
6ational Security Telecommunication! and Information Sy!tem! SecurityCommittee

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 13/65

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 14/651408/24/15
Securing the Component!
' A computer can be either or both the sub*ect ofan attack and+or the ob*ect of an attack
' hen a computer is– the sub*ect of an attack, it is used as an
active tool to conduct the attack
– the ob*ect of an attack, it is the entity bein$attacked

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 15/651508/24/15
Su)>ect and O)>ect of Attac-

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 16/651(08/24/15
9alancing Security and Acce!!
' Impossible to obtain perfect security– security is not an absolute it is a process
'ecurity should be a balance between protectionand availability
' "o achieve balance, the level of security mustallow reasonable access, yet protect a$ainst
threats

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 17/651)08/24/15
9alancing Security and Acce!!

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 18/651808/24/15
9ottom ?p Approach
' ecurity from a $rass-roots effort– systems administrators attempt to improve thesecurity of their systems
' ey advanta$e – technical e/pertise of theindividual administrators
' eldom works since it lacks critical features0
– participant support
– or$ani)ational stayin$ power

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 19/651-08/24/15
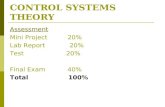
Approache! to Security Implementation
C%O
CO CIO COO
CISO :&6et,or-!:&Sy!tem!
!ecuritymanager
net,or-manager
!y!tem!manager
!ecurityadmin
net,or-admin
!y!tem!admin
!ecuritytech
net,or-tech
!y!tem!tech
FIGURE 1-7 Approaches to Security Implementation
Top-down approach Bottom-up approach

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 20/652008/24/15
Top&do,n Approach
' Initiated by upper mana$ement0– issue policy, procedures, and processes
– dictate the $oals and e/pected outcomes of the pro*ect
– determine who is accountable for each re1uired action
' &luses0
– stron$ upper mana$ement support
– dedicated champion
– dedicated fundin$– clear plannin$
– chance to influence or$ani)ational culture

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 21/652108/24/15
Top&do,n Approach
' ay also involve a formal development strate$yreferred to as a systems development life cycle
– ost successful top-down approach

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 22/652208/24/15
So ,hat can )e done*
+Security is a process5A !tructured methodology ,ill help@

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 23/652308/24/15
Security I! A roce!!Section
3
udit 9 Risk
ssessment
oli! 9
:esign
ntegration 9
:eploment
dministration9 raining
Emergen!
Response 9
Re!over %onitor 9
Resonse

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 24/652408/24/15
Audit " 'i!- A!!e!!ment
+ Audit5 'e0ie,! the !ecurity !tatu!5 Compare! to internal and eternal !tandard!5 Operational admini!trati0e and technical
+ 'i!- A!!e!!ment5 $uantie! the lia)ility5 Ac-no,ledge! threat! and 0ulnera)ilitie!5 Can deri0e a BB 0alue
X=

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 25/65
2508/24/15
olicy De0elopment
+ 'euirement! for net,or- and information !ecurity
+ olicy 5 0! 5 o!ture5 (hat are the goal! o)>ecti0e! and !tandard! for !ecurity*5 o, far ,ill you go )efore you thro, it all out the ,indo,*
+ Committee! may )e nece!!ary for larger organiation! to re0ie,
+ There are many ,ay! to gather the information5 ormal5 Informal
Actual Security Practice
Security Policy

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 26/65
2(08/24/15
The roce!! 5 9riti!h StandardEEFF

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 27/65
2)08/24/15
De!ign
+ (ith policy in hand the de!ign can !tart5 De!ign !hould )e )a!ed upon reuirement! and !tandard!5 Mu!t a good )alance of !imple and complete
+ Mu!t )e a,are of many need!5 6et,or-ing5 Application!5 ?!er!
+ Security !y!tem! rapidly )ecome mi!!ion critical5 lan for high a0aila)ility
+ 9e !ure to ;de!ign* for u!er training and a,arene!!

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 28/65
2808/24/15
De!ign Mu!t Con!ider A&I&C

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 29/65
2-08/24/15
Integration " Deployment
+ Integration of !ecurity !y!tem! i! comple
+ May change many a!pect! of )oth net,or- and application!
+ Mu!t )e thoroughly te!ted
+ Don*t ru!h !ecurity !y!tem! integration5 May yield a multi&!tage proce!!5 Do not compromi!e5 Gno, in ad0ance ,hat ;done* mean!

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 30/65
3008/24/15
Admini!tration " Training
+ Support !ta8 mu!t )e a,are of change! due to!ecurity
+ ro0ide technical training for !upport !ta8
+ re0entati0e maintenance i! -ey
+ Chec- for ne, 0ulnera)ilitie! often andremediate
+ Change! ,ill impact u!er )a!e5 /ea0e time and )udget for training5 Continue ,ith a,arene!! campaign

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 31/65
3108/24/15
%mergency 'e!pon!e "'eco0ery
+ 6o !ecurity !olution i! perfect5 A hac-er only ha! to )e right once5 lan for the i!!ue! in ad0ance
+ Con!ider di8erent !cenario!5 6et,or- or application !y!tem! compromi!e
5 Inappropriate relea!e of information
5 :iru! out)rea-
+ Should )e part of the )u!ine!! continuityplan!
+ Document and practice

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 32/65
3208/24/15
Monitoring " 'e!pon!e
+ (ant an +ADT, of the Internet5 :igilant !ecurity analy!t! monitor the net,or- and
!y!tem! on a all&day all&night )a!i!5 Automated intelligent proce!!e! com)ined ,ith
eperience and >udgment to diagno!e !ecurityepo!ure!
5 Out!ourced monitoring !upplement! internal !ecuritymea!ure!
+ De0elop 'e!pon!e rocedure!5 (ho ,ill re!pond*5 (hat ,ill they do*
+ o, far are you ,illing to go*5 ro!ecution*5 Chain of e0idence5 See- legal ad0ice immediately

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 33/65
3308/24/15
$ue!tion!
+ I! there e0er a perfectly !ecure net,or-*
+ I! !ecurity a product or proce!!*

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 34/65
3408/24/15
Important ImplementationConcept!
+ Acce!! Control
+ Authentication
+ %ncryption
+ :6
+ Anti&:iru! Screening
+ ?'/ Content Screening
+ Intru!ion Detection
+ Secure Me!!aging
udit 9 Risk
ssessment
oli! 9:esign
ntegration 9
:eploment
dministration9 raining
Emergen!
Response 9Re!over %onitor 9
Resonse

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 35/65
3508/24/15
Acce!! Control
+ Separatenet ,or-ed!y!tem!
+ ate,ay H ire,all
+ ard,are Soft,are to enforcepolicie!
+ rotect multiple net,or-!5 In!ide5 Out!ide5 DMJ
+ Conguration i! 0ital5 Addre!! policy5 :alidation te!ting5 Maintenance

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 36/65
3(08/24/15
Type! of ire,all!
+ ac-et ilter
+ roy+ Stateful In!pection
+ y)rid
Chicago
InternetInternet
CorporateHQ network
Policy-based
Management Console

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 37/65
3)08/24/15
Authentication
+ elp! pre!er0e condentiality
+ 'euired for non&repudiation
+ elp! the generation of audit trail!
+ Categorie!5 Something the u!er -no,! &assword5 Something the u!er ha! & To!en5 Something the u!er i! 5 Biometric
+ 6eed ;2= of the ;3= to )e +Strong,
+ (ithout authentication you are !hooting inthe dar-@

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 38/65
3808/24/15
Type! of Strong Authentication
+ To-en %ample!5 Time !ynchronou!5 Challenge 'e!pon!e5 Smart Card!
+ 9iometric %ample!5 ingerprint5 and or inger eometry5 alm attern or and :ein attern5 :oice or acial 'ecognition5 'etinal or Iri! Scanning
5 9ody Odor5 D6A5 Signature :erication5 Gey!tro-e Dynamic!

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 39/65
3-08/24/15
%ncryption
+ %ncode! the data or tran!mi!!ion5 ayload 0! channel
+ Mu!t !hare information ;-ey!= to !et thi! up
+ (hen to encrypt*
5 If you data i! !en!iti0e5 If you tran!mit o0er pu)lic net,or-!
+ 6eed more proce!!ing capa)ility to encrypt H de&encrypt
+ If you encrypt log! and !creening may not ,or-
+ SS/ SS IS%C encryption are common and u!eful

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 40/65
4008/24/15
:6
+ :irtual ri0ate 6et,or-+ :6 K %ncryption Authentication
+ 'emote Acce!!5 Secure connecti0ity for remote and mo)ile u!er!
+ Intranet5 Secure connecti0ity ,ithin the corporate net,or- or
)et,een multiple !ite!+ %tranet
5 Secure connecti0ity for cu!tomer! !upplier! and -ey)u!ine!! partner!
+ olicy i! !o 0ery important..5 :6 may ma-e the net,or- /%SS !ecure5 Gno, eactly ,hat you need to connect to
Customers
PartnersVPN-1 Gateway VPN-1 Gateway
InternetInternetRemote Site
Mobile
User
VPN-1VPN-1
SecuRemoteSecuRemote

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 41/65
4108/24/15
Content Screening
+ Anti:iru! Screening5 %mail and (e) page! for maliciou! code H content
+ ?'/ Content Screening5 (e) page! for content that doe! not meet policy
need!+ %mail Scanning
5 Search for -ey ,ord! or attachment!

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 42/65
4208/24/15
Intru!ion Detection
+ Acti0ely monitor! tra7c on net,or- and -ey!er0er!
+ Threat !ignature! are matched !ome,hat li-eA: !y!tem!
+ 'e!pon!e! may )e pa!!i0e or acti0e
+ Can range from !mall to large !cale5 ome )road)and lin-! ;DS/HCa)le=
5 Internet connection at the o7ce
5 Internal net,or- !egment! at the o7ce+ Output i! u!eful need to ,atch it

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 43/65
4308/24/15
Me!!aging
+ %mail may )e the mo!t important applicationyou ha0e5 Don*t ta-e it for granted it need! to )e protected
5 Ta-e control of your D6S record!
5 Scan for 0iru! and 0andal!
+ Geep !y!tem current5 /ot! of 0ulnera)ilitie! in email
5 roacti0e rather than reacti0e
+ repare for !ignature! and encryption
5 %mail me!!age! can ea!ily )e !poofed5 All mail !hould )e digitally !igned
5 %ncryption may )e nece!!ary for !en!iti0e content
5 Complicated if your company !can! mail for content

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 44/65
4408/24/15
$ue!tion!
+ (hy ,ould you ,ant to authenticate!omeone*
+ (ould you encrypt patient data if !ent o0er
the Internet*

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 45/65
4508/24/15
Technology %0ol0e! 'apidly
VPN
PKI
Scanning
Intrusion
Detection
Anti
virus
URL filtering
Authentication
Scanning
Accesscontrol
Firewall

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 46/65
4(08/24/15
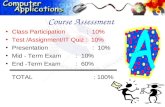
Admini!tration " Training
+ Sta8 S-ill !et
+ (or-load
udit 9 Risk ssessment
oli! 9
:esign
ntegration 9
:eploment
dministration
9 raining
Emergen!
Response 9Re!over %onitor 9
Resonse

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 47/65
4)08/24/15
Security Admini!trator S-ill Set
+ 'euire! comprehen!i0e technical -no,ledge5 Soft,are Application!
5 Operating Sy!tem!
5 /ocal Area 6et,or-ing
5 (ide Area 6et,or-ing5 Admini!tration
5 Security Tool! and Techniue!
+ 6eed for Training

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 48/65
4808/24/15
Security Admini!trator (or-load
' A hi$h volume of data to monitor– "ypical company e/ample
' 3 locations, 4 employees
' 2 e/tranet connections
' 546 of lo$s info to read 7AI89
" #B$% #B "% #B
Router &o'sFirewa((
&o's
Ser)er &o's

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 49/65
4-08/24/15
Security Management Cycle
udit 9 Risk
ssessment
oli! 9:esign
ntegration 9:eploment
dministration9 raining
Emergen!
Response 9Re!over %onitor 9
Resonse

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 50/65
5008/24/15
(hy Security*
' Information security performs four importantfunctions for an or$ani)ation0
– &rotects the or$ani)ation*s ability to function
– :nables the safe operation of applicationsimplemented on the or$ani)ation*s I"systems
– &rotects the data the or$ani)ation collectsand uses
– afe$uards the technolo$y assets in use atthe or$ani)ation

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 51/65
5108/24/15
rotecting the A)ility to unction
' ana$ement is responsible
' Information security is
– a mana$ement issue– a people issue
' #ommunities of interest must ar$ue for
information security in terms of impact and cost

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 52/65
5208/24/15
%na)ling Safe Operation
' ;r$ani)ations must create inte$rated, efficient,
and capable applications
' ;r$ani)ation need environments that safe$uardapplications
' ana$ement must not abdicate to the I"
department its responsibility to make choicesand enforce decisions

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 53/65
5308/24/15
rotecting Data
' ;ne of the most valuable assets is data
' ithout data, an or$ani)ation loses its record of
transactions and+or its ability to deliver value to itscustomers
' An effective information security pro$ram isessential to the protection of the inte$rity andvalue of the or$ani)ation*s data

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 54/65
5408/24/15
Safeguarding Technology A!!et!
' ;r$ani)ations must have secure infrastructureservices based on the si)e and scope of theenterprise
' Additional security services may have to beprovided
' ore robust solutions may be needed to replace
security pro$rams the or$ani)ation has out$rown

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 55/65
5508/24/15
Threat!
' ana$ement must be informed of the variouskinds of threats facin$ the or$ani)ation
'A threat is an ob*ect, person, or other entity thatrepresents a constant dan$er to an asset
' 6y e/aminin$ each threat cate$ory in turn,mana$ement effectively protects its information
throu$h policy, education and trainin$, andtechnolo$y controls

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 56/65
5(08/24/15
Categories of hreat !"amples
<. Acts of human error or failure Accidents, employee mistakes
2. #ompromises to intellectual property &iracy, copyri$ht infrin$ement
4. 7eliberate acts of espiona$e or trespass %nauthori)ed access and+or data collection=. 7eliberate acts of information e/tortion 6lackmail of information disclosure
3. 7eliberate acts of sabota$e or vandalism 7estruction of systems or information
>. 7eliberate acts of theft Ille$al confiscation of e1uipment or information
?. 7eliberate software attacks @iruses, worms, macros, denial-of-service
5. orces of nature ire, flood, earth1uake li$htnin$
B. 7eviations in 1uality of service fromservice providers
&ower and AC service issues
<. "echnical hardware failures or errors :1uipment failure
<<. "echnical software failures or errors 6u$s, code problems, unknown loopholes
<2. "echnolo$ical obsolescence Anti1uated or outdated technolo$ies
Threat! to Information Security
T*B&E +-1 Threats to Information Security4
Act! of uman %rror or ailure

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 57/65
5)08/24/15
Act! of uman %rror or ailure

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 58/65
5808/24/15
Shoulder Surng
- l

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 59/65
5-08/24/15
ac-er role!
> -

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 60/65
(008/24/15
Tro>an or!e Attac-!
A - ' li i

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 61/65
(108/24/15
Attac- 'eplication
#ector $escription
I& scan and attack Infected system scans random or local ran$e of I& addresses and tar$ets anyof several vulnerabilities known to hackers or left over from previous e/ploitssuch as #ode Ded, 6ack ;rifice, or &oi)on6o/
eb browsin$ If the infected system has write access to any eb pa$es, it makes all ebcontent files (html, asp, .c$i, and others! infectious, so that users who browseto these pa$es become infected
@irus :ach infected machine infects certain common e/ecutable or script files on allcomputers to which it can write with virus code that can cause infection
hares %sin$ vulnerabilities in file systems and the way many or$ani)ations confi$urethem, it copies the viral component to all locations it can reach
ass mail 6y sendin$ e-mail infections to addresses found in the infected system*saddress book, copies of the infection are sent to many users whose mail-readin$ pro$rams automatically run the pro$ram and infect other systems
imple Cetworkana$ement&rotocol (C&!
In early 22, the C& vulnerabilities known to many in the I" industry werebrou$ht to the attention of the multi vector attack community.
T*B&E +-+ Attack Replication Vectors
D i l f S i Att -

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 62/65
(208/24/15
Denial of Ser0ice! Attac-
I S

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 63/65
(308/24/15
I Spoong
M i th Middl Att -

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 64/65
(408/24/15
Man&in&the&Middle Attac-

7/23/2019 Introduction IT Risk Management Chap1
http://slidepdf.com/reader/full/introduction-it-risk-management-chap1 65/65
&anks <ou