How to comply with the Data Privacy Act of...
Transcript of How to comply with the Data Privacy Act of...

How to comply w i th the
Data Pr ivacy Ac t o f 2012
Module 1 - Introduction

Republic Act No. 10173
August 15, 2012
SECTION 1. Short Title. – This Act shall be known as the “Data Privacy
Act of 2012”.
SECTION. 2. Declaration of Policy. – It is the policy of the State to
protect the fundamental human right of privacy, of communication while
ensuring free flow of information to promote innovation and growth.
The State recognizes the vital role of information and communications
technology in nation-building and its inherent obligation to ensure that
personal information in information and communication systems in the
government and in the private sector are secured and protected.

Which is more valuable?
Data Money


Which is more valuable?
Data Money


Which is more valuable?
Data Money




Republic Act No. 10173 August 15, 2012
SEC. 26. (b) Accessing sensitive personal information due to
negligence shall be penalized by imprisonment ranging from three (3)
years to six (6) years and a fine of not less than Five hundred thousand
pesos (Php500,000.00) but not more than Four million pesos
(Php4,000,000.00) shall be imposed on persons who, due to negligence,
provided access to personal information without being authorized under
this Act or any existing law.
SEC. 35. Large-Scale. – The maximum penalty in the scale of penalties
respectively provided for the preceding offenses shall be imposed when
the personal information of at least one hundred (100) persons is
harmed, affected or involved as the result of the above mentioned
actions.

Agenda for Workshop
Introduction Data Protection Officer (DPO)
Privacy Impact Assessment
(PIA)
Privacy Management
Program (PMP)
Privacy and Data Protection (PDP)
Breach Management Framework
(BMF)

Sections 1-6.
Definitions and
General
Provisions
Sections 7-10.
National Privacy
Commission
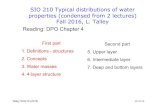
Structure of RA 10173,
the Data Privacy Act
Section 22-24.
Provisions
Specific to
Government
Section 25-37.
Penalties
Sections 11-21.
Rights of Data
Subjects, and
Obligations of
Personal
Information
Controllers and
Processors

Definitions
Personal Information
Personal information refers to any
information whether recorded in a
material form or not, from which the
identity of an individual is apparent or can
be reasonably and directly ascertained by
the entity holding the information, or
when put together with other information
would directly and certainly identify an
individual.
– RA. 10173, Section 3.g

“when put together with other information”
? #4 Pili
? 10/24/55
? Lily Ang
# 4 Pili Lily Ang 10/24/55

Definitions
Personal Information
Sensitive Personal
Information
Sensitive personal information refers to personal information:
(1) About an individual’s race, ethnic origin, marital status,
age, color, and religious, philosophical or political affiliations;
(2) About an individual’s health, education, genetic or sexual
life of a person, or to any proceeding for any offense
committed or alleged to have been committed by such
person, the disposal of such proceedings, or the sentence of
any court in such proceedings;
(3) Issued by government agencies peculiar to an individual
which includes, but not limited to, social security numbers,
previous or current health records, licenses or its denials,
suspension or revocation, and tax returns; and
(4) Specifically established by an executive order or an act of
Congress to be kept classified.
– RA. 10173, Section 3.l

“Personal Information Controllers”
those who decide what data is collected
and how it is processed (example: Bank X,
Hospital Y).
“Personal Information Processors”
those who process data as instructed by
the controllers (example: shared services,
IT vendor, external lab).
Key Definitions
PIC
PIP

Sections 1-6.
Definitions and
General
Provisions
Sections 7-10.
National Privacy
Commission
Structure of RA 10173,
the Data Privacy Act
Section 22-24.
Provisions
Specific to
Government
Section 25-37.
Penalties
Sections 11-21.
Rights of Data
Subjects, and
Obligations of
Personal
Information
Controllers and
Processors

Punishable Act Jail Term Fine (Pesos)
Access due to negligence 1y to 3y ꟷ 3y to 6y 500k to 4m
Unauthorized processing 1y to 3y ꟷ 3y to 6y 500k to 4m
Improper disposal 6m to 2y ꟷ 3y to 6y 100k to 1m
Unauthorized purposes 18m to 5y ꟷ 2y to 7y 500k to 2m
Intentional breach 1y to 3y 500k to 2m
Concealing breach 18m to 5y 500k to 1m
Malicious disclosure 18m to 5y 500k to 1m
Unauthorized disclosure 1y to 3y ꟷ 3y to 5y 500k to 2m
Combination of acts 3y to 6y 1m to 5m

Who is liable?
Sec. 22. The head of each government agency or
instrumentality shall be responsible for complying with the security requirements mentioned herein…
Sec. 34. Extent of Liability. If the offender is a corporation, partnership or any juridical person, the penalty shall be imposed upon the responsible officers, as the case may be, who participated in, or by their gross negligence, allowed the commission of the crime.


2016 Series (issued)
Circular 16-01 Gov’t Agencies
Circular 16-02 Data Sharing
Circular 16-03 Breach Mgmt
Circular 16-04 Rules Procedure
2017 Series
The Obligations which must be complied
with by PICs and PIPs
Advisory 17-01 DPO Guidelines
Advisory 17-02 PDS Guidelines
Advisory 17-03 PIA Guidelines
Data Privacy Act of 2012
IRRs (promulgated 2016)
Circular 17-01 Registration

Pillar 1: Commit to Comply:
Appoint a Data Protection Officer (DPO) Legal Basis: Sec. 21 of the DPA, Section 50 of the 50, Circular 16-01, and
Advisory 17-01
Sec. 21 (b) The personal
information controller shall
designate an individual or
individuals who are accountable
for the organization’s compliance
with this Act.

Pillar 1: Commit to Comply:
Appoint a Data Protection Officer (DPO) Legal Basis: Sec. 21 of the DPA, Section 50 of the 50, Circular 16-01, and
Advisory 17-01

Pillar 2: Know Your Risks:
Conduct a Privacy Impact Assessment (PIA) Legal Basis: Sec. 20(c) of the DPA, Section 29 of the IRR, Advisory 17-03
Sec. 20 (c) “The determination of the appropriate level of
security under this section must take into account the nature
of the personal information to be protected, the risks
represented by the processing, the size of the organization
and complexity of its operations, current data privacy best
practices and the cost of security implementation.”
How will you know what are “the risks represented by the
processing”?

Program,
Process, or
Measure
Privacy
Risk Benefit Controls
Impact
Assessment
X.1
X.2
X.3
X.25
Privacy risk is the probability that the activity involving data will result in harm, or a
loss of the rights and freedoms of an individual.
Controls may be applied in order to reduce
severity, likelihood, and magnitude of the privacy risk.
High Low Unacceptable
Medium Medium High Unreasonable
Low High Low Acceptable
High High ? ? Medium High Medium Acceptable

WHO should participate in the PIA?
Those involved in the Information Life Cycle
Collection
Use
Storage Sharing
Disposal

Privacy Risk Map
Slight
Stressful
Major
Extreme
Nil Low Med High
I
M
P
A
C
T
PROBABILITY

Pillar 2: Know Your Risks:
Conduct a Privacy Impact Assessment (PIA) Legal Basis: Sec. 20(c) of the DPA, Section 29 of the IRR, Advisory 17-03

Pillar 3: Write Your Plan:
Create Your Privacy Management Program (PMP) Legal Basis: Sec. 11-15 of the DPA, Sections 21-23 and 43-45 of the IRR,
Circulars 16-01 and 16-02

“Transparency” – no surprises in how the
data collected is being processed
“Legitimate purpose” – required by law
and not contrary to public morals
“Proportionality” – collect only what’s
needed and commensurate to the benefits
Principles

Pillar 3: Write Your Plan:
Create Your Privacy Management Program (PMP) Legal Basis: Sec. 11-15 of the DPA, Sections 21-23 and 43-45 of the IRR,
Circulars 16-01 and 16-02

Y. New
technologies and
standards
Z. New legal
requirements
X. Continuing
Assessment and
Development Regular PIA
Review Contracts
Internal
Assessments
Review PMP
Accreditations
V. Trainings
and
Certifications
W. Security
Clearance
VIII. MANAGE HR
U. Third Parties; Legal Basis for
Disclosure
Data Sharing
Agreements
Cross Border
VII. THIRD
PARTIES
T. Data Breach
Management; Security Policy
Data Breach Response
Team
Incident Response
Procedure
Document
Breach Notification
VI. BREACHES IX. CONTINUITY X. PRIVACY
ECOSYSTEM
G. Privacy Notice
H-O. Data Subject
Rights
P. Data Life Cycle
A. Choose a DPO B. Register
C. Records of
processing
activities
D. Conduct PIA
I. GOVERNANCE II. RISK
ASSESSMENT III. ORGANIZATION IV. DAY TO DAY
Q. Organizational
R. Physical
S. Technical Data Center
Encryption
Access Control Policy
V. DATA
SECURITY
E. Privacy Management
Program
F. Privacy Manual
THE NPC DATA PRIVACY ACCOUNTABILITY AND COMPLIANCE FRAMEWORK

Pillar 4: Be Accountable:
Implement your Privacy & Data Protection (PDP) Measures Legal Basis: Sec. 16-18 and 38 of the DPA and Sections 17-24, 34-37 of the IRR and
Circular 16-04

Sections 16-18. Rights of Data Subjects
Right to be informed
Right to object
Right to access
Right to correct/rectify
Right to block/remove
Right to data portability
Right to file a complaint
Right to be indemnified

Pillar 4: Be Accountable:
Implement your Privacy & Data Protection (PDP) Measures Legal Basis: Sec. 20.a-e, 22 and 24 of the DPA, Sections 25-29 of the IRR,
Circular 16-01

Pillar 5: Be Prepared:
Regularly exercise your Breach Reporting Procedures Legal Basis: Sec. 20.f and 30 of the DPA, Sections 38-42 and 57 of the IRR, Circular 16-
03
IRR Sec. 38 (a) The Commission and affected
data subjects shall be notified by the PIC
within seventy-two (72) hours upon knowledge
of, or when there is reasonable belief by the
PIC or PIP that, a personal data breach
requiring notification has occurred.

Pillar 5: Be Prepared:
Regularly exercise your Breach Reporting Procedures Legal Basis: Sec. 20.f and 30 of the DPA, Sections 38-42 and 57 of the IRR, Circular 16-
03

Pillar 6: Registration
Who should register?
Personal Information Controllers and
Personal Information Processors who:
– employ more than 250 persons
– process sensitive personal information of at least 1,000
individuals
– belong to sectors identified by the NPC where:
• the processing carried out is likely to pose a risk to the rights and
freedoms of data subjects, and
• the processing is not occasional
– are service providers to government.

Pillar 6: Registration

Designating a DPO is the first essential step
towards compliance. You cannot register your
systems with the NPC unless you have a
DPO. You cannot report your compliance
activities unless you go through your DPO.

What happens if you don’t comply?
Sec. 7. Functions of the National Privacy Commission (b) Receive complaints, institute investigations, facilitate or enable
settlement of complaints through the use of alternative dispute resolution
processes, adjudicate, award indemnity on matters affecting any personal
information, prepare reports on disposition of complaints and resolution of
any investigation it initiates, and, in cases it deems appropriate, publicize
any such report…
(c) Issue cease and desist orders, impose a temporary or permanent ban
on the processing of personal information, upon finding that the processing
will be detrimental to national security and public interest;
(d) Compel or petition any entity, government agency or instrumentality to
abide by its orders or take action on a matter affecting data privacy;
(i) Recommend to the Department of Justice (DOJ) the prosecution and
imposition of penalties specified in Sections 25 to 29 of this Act;

When should you comply?
Yesterday. Obligations in the DPA and the IRR.
September 2017. Additional Requirements in the IRR:
Registration of Data Processing Systems and Automated
Processing, 72-hour Breach Notification, Annual Incident
Reporting
October 2017. (for Government Agencies only) Additional
security requirements in Circular 16-01.

Compliance
Commitment to Comply
Capacity to Comply


Workshops to deliver the
message and build capacity
-Generic guidance and frameworks (facebook.com/ privacy.gov.ph)
-Updates on new standards and/or
circulars (www.privacy.gov.ph)
-When requested, advice on specific
matters ([email protected])
In Closing: How the NPC can help

End of Module 1.
Any questions?