Pc zombie, spim, ramsomware, spam, phishing y scam investigacíon 03 semana 08
Help! Why Phishing Works What is Phishing? I think I’ve been … · 2014. 9. 26. · Phishing is...
Transcript of Help! Why Phishing Works What is Phishing? I think I’ve been … · 2014. 9. 26. · Phishing is...

SUSPICIOUS ACTIVITY REPORTING
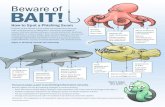
Why Phishing Works
•Weareeasilyenticed—wetrustknownbrands/logos
•Lackofusereducationandawareness
•LackofInformationAssuranceknowledgeandwarningindicators
•Visuallydeceptivetext
•Imagemasking
•ImagemimickingWindows
What is Phishing?Phishingisanattemptbyanindividualorgrouptosolicitpersonalinformationfromunsuspectingusersbyemployingsocialengineeringtechniques(i.e.,manipulatingpeopleintoperformingactionsordivulgingconfidentialinformation).Phishingemailsarecraftedtoappearasiftheyweresentfromalegitimateorganizationorknownindividual.Theseemailsoftenattempttoattractuserstoclickonalinkthatwilltaketheusertoafraudulentwebsitethatappearslegitimate.Theuserthenmaybeaskedtoprovidepersonalinformation,suchasaccountusernamesandpasswordsthatcanfurtherexposethem,theirnetwork,andtheirunittofuturecompromises.
Inordertofullyunderstandphishingandhowitcanimpactyouandyourunit,youshouldbeawarethattherearedifferenttypesofphishing:
Phishingisusuallyane-mailsenttoalargegroupofpeoplethatattemptstoscamtherecipients.Thepeoplethemessageissenttooftendonothaveanythingincommon.
Spear phishingisamessagesenttoasmaller,moreselectgroupoftargetedpeopleortoasingleindividual.
Whaling or whale phishingisahighlypersonalizedmessagesenttoseniorexecutives,high-levelofficials,ortheirpersonalexecutivestaffmembers.
Help! I think I’ve been
Phished!Anti Phishing Quick Reaction Drill
• Changeyourpasswordimmediatelyattherealwebsite:
• Typethewebsitenameinyourbrowser’saddressbar.
• Signintoyouraccountandclickthe“userprofile”or“changepassword”link.
• Followthewebsite’sinstructionstochangeyouraccountinformationandpassword.
• Clickthe“contactus”linkfoundonmostwebsitesandinformthemaboutthephishingattackyoujustexperienced.
• Ifyouareusingagovernmentcomputer,contactyourlocalInformationAssuranceOfficerandservicingNetworkEnterpriseCenter(NEC).
Recognizing & Avoiding Email Scams:http://www.us-cert.gov/reading_room/emailscams_0905.pdf
Report Phishing Attacks to Your Local Information Assurance Officer and your servicing Network
Enterprise Center (NEC)

SUSPICIOUS ACTIVITY REPORTING
Why Phishing Works
• Weareeasilyenticed—wetrustknownbrands/logos
• Lackofusereducationandawareness
• LackofInformationAssuranceknowledgeandwarningindicators
• Visuallydeceptivetext
• Imagemasking
• ImagemimickingWindows
What is Phishing?Phishingisanattemptbyanindividualorgrouptosolicitpersonalinformationfromunsuspectingusersbyemployingsocialengineeringtechniques(i.e.,manipulatingpeopleintoperformingactionsordivulgingconfidentialinformation).Phishingemailsarecraftedtoappearasiftheyweresentfromalegitimateorganizationorknownindividual.Theseemailsoftenattempttoattractuserstoclickonalinkthatwilltaketheusertoafraudulentwebsitethatappearslegitimate.Theuserthenmaybeaskedtoprovidepersonalinformation,suchasaccountusernamesandpasswordsthatcanfurtherexposethem,theirnetwork,andtheirunittofuturecompromises.
Inordertofullyunderstandphishingandhowitcanimpactyouandyourunit,youshouldbeawarethattherearedifferenttypesofphishing:
Phishingisusuallyane-mailsenttoalargegroupofpeoplethatattemptstoscamtherecipients.Thepeoplethemessageissenttooftendonothaveanythingincommon.
Spear phishingisamessagesenttoasmaller,moreselectgroupoftargetedpeopleortoasingleindividual.
Whaling or whale phishingisahighlypersonalizedmessagesenttoseniorexecutives,high-levelofficials,ortheirpersonalexecutivestaffmembers.
Help! I think I’ve been
Phished!Anti Phishing Quick Reaction Drill
•Changeyourpasswordimmediatelyattherealwebsite:
•Typethewebsitenameinyourbrowser’saddressbar.
•Signintoyouraccountandclickthe“userprofile”or“changepassword”link.
•Followthewebsite’sinstructionstochangeyouraccountinformationandpassword.
•Clickthe“contactus”linkfoundonmostwebsitesandinformthemaboutthephishingattackyoujustexperienced.
•Ifyouareusingagovernmentcomputer,contactyourlocalInformationAssuranceOfficerandservicingNetworkEnterpriseCenter(NEC).
Recognizing & Avoiding Email Scams:http://www.us-cert.gov/reading_room/emailscams_0905.pdf
Report Phishing Attacks to Your Local Information Assurance Officer and your servicing Network
Enterprise Center (NEC)

SUSPICIOUS ACTIVITY REPORTING
Why Phishing Works
• Weareeasilyenticed—wetrustknownbrands/logos
• Lackofusereducationandawareness
• LackofInformationAssuranceknowledgeandwarningindicators
• Visuallydeceptivetext
• Imagemasking
• ImagemimickingWindows
What is Phishing?Phishingisanattemptbyanindividualorgrouptosolicitpersonalinformationfromunsuspectingusersbyemployingsocialengineeringtechniques(i.e.,manipulatingpeopleintoperformingactionsordivulgingconfidentialinformation).Phishingemailsarecraftedtoappearasiftheyweresentfromalegitimateorganizationorknownindividual.Theseemailsoftenattempttoattractuserstoclickonalinkthatwilltaketheusertoafraudulentwebsitethatappearslegitimate.Theuserthenmaybeaskedtoprovidepersonalinformation,suchasaccountusernamesandpasswordsthatcanfurtherexposethem,theirnetwork,andtheirunittofuturecompromises.
Inordertofullyunderstandphishingandhowitcanimpactyouandyourunit,youshouldbeawarethattherearedifferenttypesofphishing:
Phishingisusuallyane-mailsenttoalargegroupofpeoplethatattemptstoscamtherecipients.Thepeoplethemessageissenttooftendonothaveanythingincommon.
Spear phishingisamessagesenttoasmaller,moreselectgroupoftargetedpeopleortoasingleindividual.
Whaling or whale phishingisahighlypersonalizedmessagesenttoseniorexecutives,high-levelofficials,ortheirpersonalexecutivestaffmembers.
Help! I think I’ve been
Phished!Anti Phishing Quick Reaction Drill
•Changeyourpasswordimmediatelyattherealwebsite:
•Typethewebsitenameinyourbrowser’saddressbar.
•Signintoyouraccountandclickthe“userprofile”or“changepassword”link.
•Followthewebsite’sinstructionstochangeyouraccountinformationandpassword.
•Clickthe“contactus”linkfoundonmostwebsitesandinformthemaboutthephishingattackyoujustexperienced.
•Ifyouareusingagovernmentcomputer,contactyourlocalInformationAssuranceOfficerandservicingNetworkEnterpriseCenter(NEC).
Recognizing & Avoiding Email Scams:http://www.us-cert.gov/reading_room/emailscams_0905.pdf
Report Phishing Attacks to Your Local Information Assurance Officer and your servicing Network
Enterprise Center (NEC)

User Awareness•Mostphishingattemptsareforidentitytheft,butphishingisalsobeingusedtogainaccesstoonlinebanking,federal,andDoDinformation
• PhishingAttackscanbegearedtocollectpersonalinformationsuchas:SSN,mother’smaidenname,dateofbirth,passwords,creditcardnumbers,etc.
• Phishingemailsnotonlyattempttotrickyouintogivingoutsensitiveinformation,butalsocanincludemalicioussoftware
•MalicioussoftwarecanbevirusesandothercomputercodedesignedtoallowahackertouseyourcomputerforillegalInternetactivity,ortoaccessyourunit’snetworktogatherDoDinformation
•Maliciouscodemaycaptureyourkeystrokesorcaptureyourpersonalandworkfilesandsendthemtopeoplewithoutyourknowledge
How Phishing Works
Protect Yourself and Your Organization
DO
• Watchoutforphishing
• Deletesuspiciousemails
• ContactyourInformationAssuranceOfficeroryourservicingNetworkEnterpriseCenter(NEC)ifyouhavequestionsaboutemails
• Reportanypotentialincidents
DO NOT • Opensuspiciousemails
• Clickonsuspiciouslinksinemailsorpop-upwindows
• Calltelephonenumbersprovidedinsuspiciousemails
• Discloseanyinformation

User Awareness•Mostphishingattemptsareforidentitytheft,butphishingisalsobeingusedtogainaccesstoonlinebanking,federal,andDoDinformation
• PhishingAttackscanbegearedtocollectpersonalinformationsuchas:SSN,mother’smaidenname,dateofbirth,passwords,creditcardnumbers,etc.
• Phishingemailsnotonlyattempttotrickyouintogivingoutsensitiveinformation,butalsocanincludemalicioussoftware
•MalicioussoftwarecanbevirusesandothercomputercodedesignedtoallowahackertouseyourcomputerforillegalInternetactivity,ortoaccessyourunit’snetworktogatherDoDinformation
•Maliciouscodemaycaptureyourkeystrokesorcaptureyourpersonalandworkfilesandsendthemtopeoplewithoutyourknowledge
How Phishing Works
Protect Yourself and Your Organization
DO
• Watchoutforphishing
• Deletesuspiciousemails
• ContactyourInformationAssuranceOfficeroryourservicingNetworkEnterpriseCenter(NEC)ifyouhavequestionsaboutemails
• Reportanypotentialincidents
DO NOT • Opensuspiciousemails
• Clickonsuspiciouslinksinemailsorpop-upwindows
• Calltelephonenumbersprovidedinsuspiciousemails
• Discloseanyinformation

User Awareness•Mostphishingattemptsareforidentitytheft,butphishingisalsobeingusedtogainaccesstoonlinebanking,federal,andDoDinformation
• PhishingAttackscanbegearedtocollectpersonalinformationsuchas:SSN,mother’smaidenname,dateofbirth,passwords,creditcardnumbers,etc.
• Phishingemailsnotonlyattempttotrickyouintogivingoutsensitiveinformation,butalsocanincludemalicioussoftware
•MalicioussoftwarecanbevirusesandothercomputercodedesignedtoallowahackertouseyourcomputerforillegalInternetactivity,ortoaccessyourunit’snetworktogatherDoDinformation
•Maliciouscodemaycaptureyourkeystrokesorcaptureyourpersonalandworkfilesandsendthemtopeoplewithoutyourknowledge
How Phishing Works
Protect Yourself and Your Organization
DO
• Watchoutforphishing
• Deletesuspiciousemails
• ContactyourInformationAssuranceOfficeroryourservicingNetworkEnterpriseCenter(NEC)ifyouhavequestionsaboutemails
• Reportanypotentialincidents
DO NOT • Opensuspiciousemails
• Clickonsuspiciouslinksinemailsorpop-upwindows
• Calltelephonenumbersprovidedinsuspiciousemails
• Discloseanyinformation

SUSPICIOUS ACTIVITY REPORTING
Why Phishing Works
•Weareeasilyenticed—wetrustknownbrands/logos
•Lackofusereducationandawareness
•LackofInformationAssuranceknowledgeandwarningindicators
•Visuallydeceptivetext
•Imagemasking
•ImagemimickingWindows
What is Phishing?Phishingisanattemptbyanindividualorgrouptosolicitpersonalinformationfromunsuspectingusersbyemployingsocialengineeringtechniques(i.e.,manipulatingpeopleintoperformingactionsordivulgingconfidentialinformation).Phishingemailsarecraftedtoappearasiftheyweresentfromalegitimateorganizationorknownindividual.Theseemailsoftenattempttoattractuserstoclickonalinkthatwilltaketheusertoafraudulentwebsitethatappearslegitimate.Theuserthenmaybeaskedtoprovidepersonalinformation,suchasaccountusernamesandpasswordsthatcanfurtherexposethem,theirnetwork,andtheirunittofuturecompromises.
Inordertofullyunderstandphishingandhowitcanimpactyouandyourunit,youshouldbeawarethattherearedifferenttypesofphishing:
Phishingisusuallyane-mailsenttoalargegroupofpeoplethatattemptstoscamtherecipients.Thepeoplethemessageissenttooftendonothaveanythingincommon.
Spear phishingisamessagesenttoasmaller,moreselectgroupoftargetedpeopleortoasingleindividual.
Whaling or whale phishingisahighlypersonalizedmessagesenttoseniorexecutives,high-levelofficials,ortheirpersonalexecutivestaffmembers.
Help! I think I’ve been
Phished!Anti Phishing Quick Reaction Drill
• Changeyourpasswordimmediatelyattherealwebsite:
• Typethewebsitenameinyourbrowser’saddressbar.
• Signintoyouraccountandclickthe“userprofile”or“changepassword”link.
• Followthewebsite’sinstructionstochangeyouraccountinformationandpassword.
• Clickthe“contactus”linkfoundonmostwebsitesandinformthemaboutthephishingattackyoujustexperienced.
• Ifyouareusingagovernmentcomputer,contactyourlocalInformationAssuranceOfficerandservicingNetworkEnterpriseCenter(NEC).
Recognizing & Avoiding Email Scams:http://www.us-cert.gov/reading_room/emailscams_0905.pdf
Report Phishing Attacks to Your Local Information Assurance Officer and your servicing Network
Enterprise Center (NEC)