Hammertoss: A proof of concept in C#
-
Upload
salvatore-saeli -
Category
Internet
-
view
127 -
download
4
Transcript of Hammertoss: A proof of concept in C#

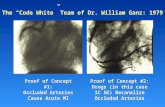
Hammertoss A proof of concept in C#
Introspection Analysis of the Malware Behavior
Salvatore Saeli aka Jabex

https://www2.fireeye.com/rs/848-DID-242/images/rpt-apt29-hammertoss.pdf
2
The HAMMERTOSS reference is available at URL

3
Injection Steganography

The injection technique implants the data to hide in the insignificant part of the carrier file, which is normally ignored by operating systems and software applications.
Steganography by injection exploits the EOF section and injects secret data after the EOF marker which eventually has no side effect on the carrier file and is often disregarded by the execution environment.
HAMMERTOSS uses JPEG file image.
4

JPEG data are byte streams, always storing 16-bit word values in big-endian format. JPEG data in general is stored as a stream of blocks, and each block is identified by a marker value.
5

6
SOI Marker
EOI Marker
The first two bytes of every JPEG stream are the Start Of Image (SOI) marker values FFh D8h.
All JPEG data streams end with the End Of Image (EOI) marker values FFh D9h.

7
Relation between hash tag and cryptography algorithm

8
APT29 tweet a URL and a hashtag.
The URL directs HAMMERTOSS to a webpage containing an image or images.
The hashtag provides A. a number representing a location within the image file
and B. characters for appending to an encryption key to
decrypt instructions within the image ==> it is a salt??

9
PBKDF1 as specified in PKCS#5 and RFC_2898 provides Key Derivation and Key Strengthening.
The parameters of the function are a hash function (such as SHA-1), a password, a salt, an iteration count and the length of the derived key to be returned.
The standard PBKDF1 will just calculate the hash of password concatenated with salt, and then hash the hash value that is returned by the previous step iteration count minus one times.

10
Using PBKDF1 obtain a implementation of AES 256 bit with salt, where salt has a variable lenght (from 4 byte to 8 byte).

11
The appended data is encrypted, so even if detected, the investigator would be unable to decrypt the data without key material from two sources: the malware binary and the current tweet.

12
InternetExplorer.Application COM Object

13
HAMMERTOSS uses the InternetExplorer.Application COM Object to visit the URL and to obtain the stegaimage. If a instance of this object run as privileged user, the process copies all items in the visited web page into IE user’s cache.

14
C:\Users\jabex\AppData\Local\Microsoft\Windows\Temporary Internet Files
C:\Users\jabex\AppData\Local\Microsoft\Windows\Temporary Internet File\Content.IE5\I6CX7FXR\lena[1].jpg
IE cache Logic Path
IE cache Real Path

15
HAMMERTOSS searches the cache for any images at least as large as the offset specified in the tweet, it locates the encrypted data, and it decrypts the data using a key comprised of hard-coded data from the malware binary appended with the characters from the tweet.

16
To get entries from user’s Internet Explorer cache, the process uses the DllImport C# mechanism to make a system call to wininet.dll win32 Api

17
The GitHub repository of C# POC is available at URL
https://github.com/jabex/hammertoss

18
Uploader class
The Uploader class check a JPEG image for SOI and EOI makers. If the check have successful, the process encrypts the payload and appends it to JPEG image.
After that, it create a hashtag from a random salt and the original size of input image.

19
tDiscoverer class
This part of POC must run as privileged user!
The tDiscoverer class creates a instance of InternetExplorer.Application COM object, makes a HTTP GET request to web page, and put all page’s content into IE user’s cache.
After that, the process searches into cache entries all JPEG images at least as large as the offset specified in the hashtag.

20
tDiscoverer class
From all images obtained in previous step, the process selects the image where at [offset - 2 byte] it matches EOI marker.
Finally, the process decrypts the data using encryption password appended with the characters (salt) that it has obtained from the hashtag and it executes the commands.

21
THE END