GUJARAT TECHNOLOGICAL UNIVERSITYWrite program to sort a given list using (a) Bubble sort (b)...
Transcript of GUJARAT TECHNOLOGICAL UNIVERSITYWrite program to sort a given list using (a) Bubble sort (b)...

GUJARAT TECHNOLOGICAL UNIVERSITY
Master of Computer Application
Subject Name : Data Structures
Subject Code : 620001
_____________________________________________________________
Objectives:
• To develop proficiency in the specification, representation, and implementation of
Data Types and Data Structures.
• To be able to carry out the Analysis of various Algorithms for mainly Time and Space
Complexity.
• To get a good understanding of applications of Data Structures.
• To develop a base for advanced computer science study.
Prerequisites:
Any programming language like C, C++
Contents:
1. Analysis of algorithms :
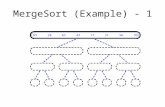
Examples of Insertion Sort, Pseudo Code Convention, Designing Algorithms -
Example of Merge Sort , Growth of Functions - Asymptotic Notation
2. Introduction to Data Structures :
Primitive Data Structures, String Manipulation & Pattern Matching , Storage
Representation of Strings , Text Handling , KWIC Indexing
3. Linear Data Structures:
Arrays, Storage Structure for Arrays, Structures & Arrays of Structures , Stack,
Applications of Stacks, Queues, Simulation, Priority Queues, Pointers & Linked
Allocation , Linked Linear Lists , Circularly Linked Linear Lists , Doubly Linked
Linear Lists, Applications of Linked Linear Lists
4. Nonlinear Data Structures:
Trees , Operations on Binary Trees , Storage Representation & Manipulation of
Binary Trees, Conversion of General Tree to Binary Trees , Sequential & Other
Representation of Trees , Application of Trees - Manipulation of Arithmetic
Expression , Multi-linked Structures - Sparse Matrices , Matrix Representation of
Graphs , Graphic Representation of List Structures , Other Representation of Graphs ,
Breadth First Search (BFS) , Depth First Search (DFS) , Spanning Trees , Garbage
Collection
www.gtucampus.com MCA(New Syllabus 2009) Sem-II 1 of 26

5. Sorting & Searching:
Introduction , Selection Sort , Bubble Sort , Merge Sort , Heap Sort , Quick Sort ,
Radix Sort , Sequential Searching , Binary Searching , Search Trees - Height
Balanced , 2-3 Trees , Weight Balanced , m-ary Trees , Trie Structures , Hash Table
Search Methods , Introduction , Hashing Functions , Collision Resolution Techniques
Main Reference Book(s):
1. "An Introduction to Data Structures with Applications", Jean-Paul Tremblay, Paul G.
Sorenson, Tata McGraw-Hill, 2nd
Edition, (2007)
2. "Introduction to Algorithm", Cormen, Leiserson, Rivest, Stein, , PHI (2003), 2nd
Edition,
3. "Design and Analysis of Algorithms" Parag Dave & Himanshu Dave, Pearson
Education (2008).
Suggested Additional Reading:
1. "Data Structures and Algorithm Analysis in C", Mark Allen Weiss, , Pearson
Education.
2. "Data Structures: A Pseudo-code Approach with C", Gilberg & Forouzan, , Cengage
Learning.
3. "Data Structures Via C++: Objects by Evolution", A. Michael Berman, , Oxford Univ.
Press (2004)
4. “Fundamentals of Data Structures in C”, Horowitz, Sahni, Anderson-Freed, ,
University Press (2nd
edition-2007)
5. "Data Structures Using C & C++", Tenenbaum, PHI.
6. "Data Structures & Algorithms" , A V Aho, J E Hopcroft, J D Ullman, , Pearson
Education (1983).
7. "Sorting & Searching - The Art of Computer Programming" D E Knuth, , Vol. 3,
Pearson Education (1998).
8. "Data structures and algorithms, concepts, Techniques and Applications" ,G. A.V.
PAI, , TMH , 1st Edition (2008)
9. “Algorithm design-foundation, analysis & internet examples”, Michel Goodrich,
Roberto Tamassia, , Wiley
Chapter wise Coverage from Main Reference Book(s):
Book-1 :
1.4, 2.1, 2.2.2, 2.2.3, 2.4, 2.5.1, 2.5.3
3.1 to 3.8, 4.1, 4.2.1, 4.2.2, 4.2.3, 4.3
5.1.1, 5.1.2, 5.1.3, 5.1.4, 5.1.5, 5.2.1, 5.3.1, 5.4.1, 5.4.2, 5.4.3, 5.4.4, 5.4.5, 5.4.6, 5.6.5
6.1.1, 6.1.2, 6.1.3, 6.1.4, 6.1.5, 6.1.6, 6.1.7, 6.2.1, 6.2.2, 6.2.3, 6.2.3.1, 6.2.3.2, 6.2.3.3,
6.2.3.4, 6.2.4, 6.2.4.1, 6.2.4.2, 6.2.4.3
www.gtucampus.com MCA(New Syllabus 2009) Sem-II 2 of 26

Book-2
2.1, 2.2, 2.3, 3.1
Book -3
4.4, 4.5
Accomplishments of the student after completing the Course:
• Ability to decide the appropriate data type and data structure for a given problem.
• Ability to select the best algorithm to solve a problem by considering various problem
characteristics, such as the data size, the type of operations, etc.
• The algorithms as referred above would include various operations on Queues, Stacks, Linked
Lists, Trees, Graphs, Sorting, Searching, Hash tables
• Ability to compare algorithms with respect to time and space complexity
www.gtucampus.com MCA(New Syllabus 2009) Sem-II 3 of 26

GUJARAT TECHNOLOGICAL UNIVERSITY
Master of Computer Application
Subject Name : Programming Skills II(DS)
Subject Code : 620002
_____________________________________________________________
NOTE : Implement the program in ‘ C/C++’.
1. Write a program to perform the following operations on a stack.
(Implement the stack using array and linked list both)
i) PUSH
ii) POP
iii) ISEMPTY
iv) ISFULL
v) PEEP
2. Write a program to convert an infix arithmetic expression (parenthesize /
unparenthesized) into postfix notation.
3. Write a program to evaluate a postfix expression.
4. Write a program to perform the following operation on a simple queue. (Implement the
queue using array)
(a) Insert an element (b) Remove an element
5. Write a program to perform the following operations on a simple queue.
(implement the queue using linked list)
(a) Insert an element (b) Remove an element
6. Write a program to perform the following operation on a circular queue.
(implement the queue using array)
(a) Insert an element (b) Remove an element
7. Write a program to perform the following operations on a priority queue.
(a) Insert an element (b) Remove an element
www.gtucampus.com MCA(New Syllabus 2009) Sem-II 4 of 26

8. Write a Program to implement Double ended queue (Input Restricted/Output restricted)
9. (a) Write a program to create a singly linked list in LIFO fashion.
(b) Write a program to create a singly linked list in FIFO fashion.
(c) Write a program to create a sorted singly linked list.
(d) Cursor Implementation (Array implementation ) Of Linked List.
(e) Write program perform the following operations on a singly linked list.
1. Insert an element
2. Delete an element
3. Find the sum of elements of the list
4. Count number of the nodes in the linked list
5. Search a given elements in the linked list.
6. Reverse the linked list.
7. Make a copy of the given linked list
8. Concatenate two linked list
9. Merge two linked list.
10. Find the union of the two given linked list
11. Find the intersection of the two given linked list.
10. Write a program to add two polynomials in two variables.
11. Write a program to subtract two polynomials in two variables.
12. Write a program to multiply two polynomials in two variables.
13. Write a program to implement sparse Matrix ( using Array & Linked-List)
14. (a) Write a program to create a sorted doubly linked list.
(b) Write a program to create a doubly linked list in LIFO fashion.
(c) Write a program to create a doubly linked list in FIFO fashion.
(d) Write a program perform the following operations on a doubly linkedList.
1. Insert an element
2. Delete an element
3. Find the sum of element of the list
4. Count number of the nodes in the linked list
5. Search a given element in the linked list.
www.gtucampus.com MCA(New Syllabus 2009) Sem-II 5 of 26

6. Reverse the linked list
7. Make a copy of the given linked list
8. Concatenate two linked listed.
9. Merge two linked list.
10. Find the union of the two given linked list.
11. Find the intersection of the two given linked list.
15.Write a program to swap two adjacent nodes by pointers (and not the data) of
(a) Singly linked list (b) Doubly linked list
16. Write a program to create a binary search tree and print it’s elements in inorder (write
iterative code).
17. Write a program to create a binary search tree and print it’s elements in preorder (write
iterative code).
18. Write a program to create a binary search tree and print it’s elements in postrder (write
iterative code).
19. Write a program to delete an element from a binary search tree.
20. Write a program to make another copy of a given binary search tree.
21. Write a program to count no of leaf nodes in a given binary tree.
22. Write a program to search an element in a given binary search tree.
23. Write a program to Generate Min-heap and Max-heap (Insertion and Deletion )
24. Write a program for Insertion of a node in m-way tree (B-Tree/B+-Tree)
25. Write a program to create an inordered threaded binary tree. Traverse the tree in inorder.
26. Write a program to create a graph in a adjacency matrix. Generate path matrix from the
given matrix.
27. Write a program to create a graph in a adjacency list structure.
(Node directory structure) traverse it in DFS.
28. Write a program to create a graph in a adjacency list structure.
(Node directory structure) traverse it in BFS.
29. Write a program to implement find shortest path using Dijkastra’s algorithm
30. Write a program to find minimal spanning tree for a given graph using
a. Prims algorithm
b. Kruskal’s algorithm
www.gtucampus.com MCA(New Syllabus 2009) Sem-II 6 of 26

31. Write program to sort a given list using
(a) Bubble sort
(b) Selection sort
(c) Insertion sort
(d) Shell Sort
(e) Quick sort
(f) Merge sort
(g) Radix sort
(h) Heap sort
(i) Topological sort
32. Write program to search an element in a given list using
(a) Linear search
(b) Binary search (iterative/ recursive)
33. Write a Program to merge two given sorted arrays
34. Hashing and Collision Resolution
a. Linear Probing
b. Quadratic Probing
c. Double Hashing
d. Separate Chaining using Linked List
e. Rehashing
www.gtucampus.com MCA(New Syllabus 2009) Sem-II 7 of 26

GUJARAT TECHNOLOGICAL UNIVERSITY
Master of Computer Application
Subject Name : Object Oriented Concepts and Programming (OOCP)
Subject Code : 620003
_____________________________________________________________
Objectives:
The programming for small devices like mobile phones, networking devices like routers, coding
for graphics and multimedia, requires efficient coding as well as object oriented programming.
The C++ language fits perfectly as a tool for this type of work. How this important language is to
be mastered and how to use this knowledge in building efficient and flexible code is one of the
prime requirements today. The course presented here is targeting to enable the student to master
such skills. Aim of the course is to enable students to
1. Differente between procedural and object oriented programming.
2. Learn C++ as a language and various features of it.
3. Learn Object Oriented principles and their application using C++.
Prerequisites:
1. Knowledge of C language
2. Programming concepts including algorithm building and logic
Contents :
1. Introduction to C++, Overview of Core C++ Language, Classes and Objects Identifiers and constants (Literals), Keywords, Data Types, The Operators, New Casting
Operators, typeid and throw, The Conditional structures and Looping Constructs, , The
Difference between struct and class in C++,The difference between Union and Class, Static Data
members of a class, Pointer to objects and pointer to members of class, The local classes,
Assigning Objects
2. Functions
Introduction, The inline function, Default Arguments to the function,Functions with object as
parameters,Call by reference and return by reference, Prototyping and Overloading, Friend
functions, Const and Volatile functions, Static functions, Private and Public functions, Function
Pointers, Adding C functions to the C++ program
3. Constructors and Destructors
Introduction to constructors, The explicit constructors, Parameterized constructors, Having
multiple constructors, Constructors with default arguments, Dynamic Initialization, Constructor
with dynamic allocation, copy constructors, The member initialization list, destructors
www.gtucampus.com MCA(New Syllabus 2009) Sem-II 8 of 26

4. Operator Overloading and User Defined Conversions
Introduction, Unary Operators, Binary Operators, Using Friends as operator functions,
Overloading other Operators, The need for user defined conversion, Four different cases where
user defined conversions are needed, Comparison of both the methods of conversion
5. Templates
Function Templates, Non Generic (Non Type) Parameters in Template functions, Template
function and specialization, Overloading a template function, Using Default Arguments, Class
Templates, Classes with multiple generic data types, Static data members, Primary and Partial
Specialization, The Export Keyword, The other use of typename
6. Inheritance
The need, Defining derived class using single base class, Derivation using public, private and
protected access modifiers, The implementation of inheritance in the C++ object model, The
Access Control, The Access Declaration, The multiple-inheritance, Abstract classes, Composite
objects (container objects)
7. Runtime polymorphism and Run Time Type Identification
Compile Time and Runtime Polymorphism, Pointers to Objects, This pointer, Compatibility of
Derived and base class pointers, The subobject concept, Virtual functions, Static invocation of
virtual function, Default arguments to virtual functions, Virtual destructors, Pure virtual
functions, Run Time Type Identification
8. Exception Handling
Introduction, Need for Exception handling, Components of exception handling mechanism,
rethrowing an exception , Terminate and Unexpected functions, Drawbacks of exception
handling approach, The exception Class
9. IO Streams
Need for streams, Advantages of using C++ I/O over C IO, The C++ Predefined streams,
Formatting IO, Formatting using ios members, Manipulators, Creating our own manipulator
10. Using Files for IO
Why IO is special, Text and binary streams, Opening and closing files, Dealing with text files
Dealing with binary files, Providing Random Access using seek, IO Modes, Handling Errors
11. Namespaces
Introduction and need, Use the using syntax, Defining namespaces, Extending the namespace,
Unnamed namespaces, Nested Namespaces, Namespace aliases, The std namespace, The Koenig
lookup, Overhead with namespaces
12. The Standard Template Library
The STL (Standard Template Library) Introduction, Generic Programming , Generic Software
Components, Generic Algorithms, Iterators, Containers, Algorithms
www.gtucampus.com MCA(New Syllabus 2009) Sem-II 9 of 26

Main Reference Book:
1. Programming with ANSI C++ by Bhushan Trivedi, Oxford University Press
Suggested Additional Reading:
1. Object Oriented programming with C++ by E. Balagurusamy, TMH
2. Complete Reference C++ by Herbert Schildt McGraw Hill Publications
3. Computer Science- A Structured approach using C++ by Forouzan ,Gilburg, THOMSON
Books
4. Object Oriented programming in C++ by Robert Lafore, Pearson Education
5. C++ FAQs by Pearson Education
6. C++ Primer by Stanley Lippmann, Pearson Education
7. The C++ Programming Language by Bjarne Stroustrup, Pearson Education
8. Effective C++ by Scott Mayer Addison Wesley
Chapter-wise coverage from main reference book :
Chapters : 1,2,3,4,5,6,7,8,9,10,11,12,13,14,16.
Accomplishments of the student after completing the course :
1. He/She should be able to understand and appreciate the Object Oriented approach of
programming
2. He/She should be aware of the working and architectural model of C++.
3. He/She should be able to solve problems given to him/her using C++ with keeping
balance between efficiency and flexibility
www.gtucampus.com MCA(New Syllabus 2009) Sem-II 10 of 26

GUJARAT TECHNOLOGICAL UNIVERSITY
Master of Computer Application
Subject Name : Programming skills-III (OOCP)
Subject Code : 620004
_____________________________________________________________
Programs based on following topic should be carried out during practical hours.
Practicals based on implementing classes.
Practicals based on static members.
Practicals based on function overloading.
Practicals based on type conversion.
Practicals based on operator overloading.
Practicals based on inheritance.
Practicals based on runtime polymorphism.
Practicals based on templates.
Practicals based on exception handling.
Practicals based on runtime type identification.
Practicals based on console I/O.
Practicals based on file handling.
Following list is just a sample guide line.
(1) Write a program which illustrates the use of scope resolution operator.
(2) Define a class to represent a bank account. Include the following members :
DATA MEMBERS MEMBER FUNCTIONS
------------------------ ------------------------------
Name of depositor (1) To assign initial values
Account Number (2) To Deposit the amount
Type of Account (3) To withdraw an amount after checking the
Balance amount in account
(4) To display name and balance
www.gtucampus.com MCA(New Syllabus 2009) Sem-II 11 of 26

Write C++ program to handle 10 customers. Situation when withdrawal is not
possible must be handled through exceptions handling feature of C++.
(3) Demonstrate the use of static variables in a class by using it to count the number of
objects created in the program
.
(4) Write a program that calculates the value of m raised to power n for both int and double
data types. (Use the concept of function overloading)
(5) Write a class to represent a vector. Include member functions to perform the following
1. To create the vector
2. To modify the value of a given element
3. To multiply by a scalar value
4. To display the vector in the form(10,20,30...)
(6) Define a class Car. Add data members as Make, Color, Size, and Cost. Write member
functions for reading values and printing values of car. Define one more class as
CarCollection. CarCollection contains array of cars. CarCollection class should
contain member functions as Add, delete, modify and replace. Collection is to be
defined as friend of Car class. Use Exception Handling techniques to handle errors.
(7) Overload all the four arithmetic operators to operate on a vector class and also the
overload the * operator to multiply scalar values to the vector class. Overload the >>
operator to input a vector and the << operator to display the vector in the form
(10,20,.....). Also overload the [] operator to access the indivisual member of the
vector. Use Dynamic memory allocation to achieve the solution. Write appropriate
constructor and destructure for the class.
(8) Write a menu driven program that can perform the following functions on strings. (Use
overloaded operators where possible). (Do not use predefined string class )
1. Compare two strings for equality (== operator)
2. Check whether first string is smaller than the second (<= operator)
3. Copy the string to another
4. Extract a character from the string (Overload [])
5. Reverse the string
6. Concatenate two strings (+ operator)
www.gtucampus.com MCA(New Syllabus 2009) Sem-II 12 of 26

(9) Overload subscript operator [] for a array class.
(10) Overload function call operator () to allow the more common form of double array
subscripting. Instead of saying x[row][column] for an array of objects, overload the
function call operator to allow the alternate form x(row, column)
(11) Define a singly linked list class, which is a made up objects of node class. Provide
addition, deletion of nodes, with operator overloading.
(12) Define a matrix class, which allows addition, subtraction, multiplication with another
matrix, multiplication with a scalar value, and inverse of a matrix( Use operator
overloading). Use dynamic constructors and destructors for allocation and de
allocation of memory.
(13) Construct a class distance having member variables int feets and int inches.Design
the class to make it possible :
(i) To convert this class into the basic data type int which will represent the total no. of
inches of the class.
(ii) To convert a basic data type int to distance class
(iii) To convert distance class to length class having member variables int meters and int
centimeters
Write a C++ program to test your class.
(14) Define a class Employees. Also define classes of MaleEmp and FemaleEmp
inheriting from that. Define classes Officers, Clercks and peons again inheriting
from Employee class. Define an array which contains 10 different types of
employees. Define a function ReadDetails() in all above classes. All array elements
should be able to be accessed in the same routine irrespective of their type.
(15) Consider a class network of fig . The class master derives information from both
account and admin classes which in turn derived derive information from the class
person. Define all the four classes and write a program to create , update and
display the information contained in master objects.
www.gtucampus.com MCA(New Syllabus 2009) Sem-II 13 of 26

(16) Create a base class called shape. Use this class to store two double type values that
could be used to compute the area of figures. Derive three specific classes
calledtriangle, rectangle and circle from the base shape. Add to the base class, a
member function get_data( ) to initialize base class data members and another
member function display_area( ) to compute and display the area of figures.Make
display_area( ) as a virtual function and redefine this function in derived classes to
suit their requirements. Using these three classes design a program that will accept
dimensions of a triangle or rectangle interactively and store it in one array . After
having read all the input display the area of all the figures whose area has been read
in the program. Remember the two values given as input will be treated as lengths
of two sides in the case of rectangle and as base and height in case of triangle. In
case of circle only one value should be accepted which will be taken as the radius
and the default value of the next parameter should be 0.
Person
code
name
Admin
Experience
Account
pay
Master
name
code
exp.
pay
www.gtucampus.com MCA(New Syllabus 2009) Sem-II 14 of 26

(17) ABC publishing company markets both book and audio cassette versions of its
work. Create a class called publication that stores the title( a string) and price( type
float) of a publication. From this class derive two classes : book , which adds a page
count (type int); and tape, which adds playing time in minutes (type float). Write a
main program that reads both book and tape information in one array. When the
user has finished entering data for all books and tapes, displays the resulting data
for all the books and tapes entered. Also count no of book and cassette entries in the
array using runtime identification feature of C++.
(18) There are two classes Emp and Employee. Emp is defined in the payroll department
containing details about employee id and details about his/her payment. Employee
is a Human resource department class containing only basic salary details and full
personal details like name of spouse, number of children, previous experience of an
employee etc. Add code in the Emp class such that, conversion from one type of
employee object into another is possible. While converting, items which are not
here in the source class (like No. of children when source class is Employee) should
take a default value.
(19) Define a class Result which contains the result of an MCA written test. It should
take merit list from a file and display on the screen such that at a time only ten
candidates information is printed on the screen. The headings should be displayed
using a manipulator. All the information should be aligned with the headings.
(20) Write a C++ program that displays a student object read from a file backwards.
(21) Use an Employee Class to write records of employee to a file. Include a menu that
will allow the user to select any of the following features
a. Add a new record.
b. Modify an existing record.
c. Retrieve and display an entire record for a given
name.
d. Generate a complete list of all names, addresses
and telephone numbers.
e. End of the computation.
(22) Write a program that returns the size in bytes of a file entered on the command line.
www.gtucampus.com MCA(New Syllabus 2009) Sem-II 15 of 26

(23) You are the owner of a hardware store and need to keep an inventory that can tell
you what different tools you have , how many of each you have in hand, and the
cost of each one. Write a program that initializes the random access file
"hardware.dat" to one hundred empty records, lets you input data concerning each
tool, enable you to list all your tools, and lets you update any information in the
file. The tool identification should be the record number. The file must contain
following information for each tool
record_no tool_name quantity cost
(24) A file contains name and phone numbers. Name contains only one word and names
and telephone numbers are seperated by white spaces. Write a program which will
include a menu driven functionality for the above file
(a) Display 2 column output with names left justified and
phone numbers right justified.
Name Phone
Ram 56789125
Shyam 34565432
Rahim 23456789
Joseph 67213148
(b) Determine the telephone number of a person.
(c) Determine the name if the telephone number is known.
(d) Update the telephone number.
(e) Prefix all the telephone numbers by 2.
(25) Write a program that stores and displays the records of the customer from a file The
following information for account of the customer is to be stored. Account no,
account type, name, old balance,new balance, last payment, date of last
payment.Also display the current account status by comparing current payment and
previous balance. Also calculate the current balance by subtracting the current
payment from the previous balance.
www.gtucampus.com MCA(New Syllabus 2009) Sem-II 16 of 26

(26) Write a program that swaps each character pair in a text file. For example, if the
file contains "1234", then after the program in run, the file will contain "2143".
(27) Write a program that reads a text file and creates another file that is identical except
that sequence of consequtive blank spaces is replaced by single space.
(28) Use Employee and EmpCollection classes. Employee class contains details about
employee and EmpCollection contains collection of employees in form of an array.
Provide GetSubordinates friend function which returns an object of EmpCollection
class which contains details of subordinates of a manager. The employee object
describing manager is to be passed as a parameter. All the information about
employees are to be stored in the files EmployeeFile and EmployeeCollectionFile.
Next run of the program should read that file and should store final list of
Employees and Employee Collections to again the same files.
(29) Define a class Person. Have data members as name of the person, names of parents
of the person, gender, age, and an array containing list of interests. Provide
functions FindFather, FindMother, FindUndle and FindAunty functions, all of
which returns the object of person class. Provide access using function pointer for
all these functions. The program should take all information about persons from a
file Person. The answers to all queries should also be stored in separate files.
(30) Write a template function called find(). This function searches an array for an object.
It returns either the index of the matching object (if one is found) or -1 if no match
is found.
(31) Write a object oriented program to implement a generic Stack. Incorporate all the
possible operation on Stack in the program. Rework stack class so that stack
overflows are handled as exceptions.
(32) Write a program to create template class called "Safearray". Rules for this class are
as follows :
(1) Size is equal to 100
(2) Index from 0 to size -1
(3) If array is sought outside bound the program aborts
(4) Function safeput() is used to assign value to an array element.
(5) Function safeget() is used to return the array element.
www.gtucampus.com MCA(New Syllabus 2009) Sem-II 17 of 26

Make necessary provisions so the program terminates
gracefully when unsafe action is attempted.
(33) Use Time class to provide overloaded -. Here the time query is also to be recorded
in file. Use C text file to store the query. If a calling function provides expression
Time1 – Time2, then operator – function should throw an exception if Time2 is a
later time then Time1. Before throwing exception, though, the operator – function
should close the file.
(34) Design a manipulator to provide the following output specifications for printing
float values
(i) 15 column width
(ii) Right justified
(iii) 2 digits precision
(iv) Filling unused spaces with +.
(v) Showing trailing zeros.
(35) Create an input manipulator called skipchar() that reads and ignores the ten
characters from the input stream. Create an output manipulator called sethex()
that sets output to hexadecimal and turns on the uppercase and showbase flags.
Also create an output manipulator called rest() that undoes the charges made by
sethex().Write a driver program to test the manipulators.
(36) Write a C++ program to demonstrate creation of user defined manipulator
(i) unparameterised
(ii) with one parameter
(iii) with two parameters
(iv) with three parameters
(37) Write C++ program to test the following
(a) Name spaces in all possible ways
(b) Dynamic_cast, const_cast, reinterpret_cast
(c) Run Time Type Identification
(d) const function
(e) const object
www.gtucampus.com MCA(New Syllabus 2009) Sem-II 18 of 26

(f) bool
(g) mutable
(h) explicit
(i) pointer to member functions
(j) Namespace
..... and other new features in C++
(38) Write a C++ program to demonstrate use of all the string function provided in
inbuilt String class of C++.
www.gtucampus.com MCA(New Syllabus 2009) Sem-II 19 of 26

GUJARAT TECHNOLOGICAL UNIVERSITY
Master of Computer Application
Subject Name : Computer Oriented Numerical Methods
Subject Code : 620005
_____________________________________________________________
Objectives:
With the current deployment of computer technology and tools, it is very important to
develop efficient algorithms for solving problems in science, engineering, technology,
insurance & banking. Thus, the objective of this course is to enable students to obtain an
intuitive and working understanding of numerical methods for the basic problems of
numerical analysis and gain experience in the implementation of numerical methods
using a computer. They would also gain an appreciation of the concept of error in these
methods and the need to analyze and predict it.
Prerequisites: Basic knowledge of functions, logarithmic, trigonometric and
exponential functions, graph of a function, polynomials, and roots of a polynomial,
differentiation and integration, differential equations, simultaneous equations.
Contents:
1. Computer Arithmetic
2. Iterative Methods for finding roots:
Bisection
False Position
Secant Method Discuss convergence only
Newton Raphson without derivation
Successive Approximation
Birge Vieta Method
Descarte’s rule of sign
3. Interpolation and Approximation
(a) Polynomial interpolation : Lagrange, forward difference, backward difference,
divided difference interpolation, Error Estimates, Cubic Spline interpolation , Inverse
interpolation.
(b) Approximation : Least square Curve fitting: Linear Regression and Non linear
Regression, Approximation of Functions by Taylor series , Chebyshev
Approximation, Chebyshev Economization .
4. Numerical Differentiation & Integration
Differentiation
Integration - Trapezoidal, Simpson’s 1/3 & 3/8 rules, Gauss Quadrature formulas
www.gtucampus.com MCA(New Syllabus 2009) Sem-II 20 of 26

5.
a) Matrix : Introduction to Matrix, types of matrices, transpose of a matrix, matrix
multiplication, Eigen values and Eigen vectors, Power method.
b) Solution of Simultaneous Linear Equations: Naïve Gauss Elimination, Gauss
Elimination with pivoting, Gauss-Seidel method.
c) Solution Of Ordinary Differential Equations: Taylor series, Runge-Kutta 2nd
order, 3rd
order, 4th
order, Predictor Corrector methods : Milne Simpson &
Adam’s Moulton method
Main Reference Books :
1. Numerical Methods for Engineers by Steven C Chapra & Raymond P Canale,
Fifth Edition, Tata McGraw Hill Publication, Special Indian Edition.
2. Computer Oriented Numerical Methods by Dr. N Datta, Vikas Publication.
Suggested Additonal Reading :
1. “Numerical Methods with Programs in C” by T Veerarajan &
T Ramachandran, Second Edition, Tata McGraw Hill Publication.
2. “Numerical Methods” by V. Rajaraman, Third Edition, Prentice-Hall India Pvt.
Ltd.
3. “Numerical Methods with C++ Programming” by R M Somasundaram & RM
Chandrasekaran, Prentice-Hall India Pvt. Ltd.
4. “Applied Numerical Analysis by C F Gerald & P O Wheatley”, Seventh Edition,
Pearson Education Asia, New Delhi
5. “Elementary Numerical Analysis” by Atkinson & Han ,Wiley India Edition
6. “Numerical Methods ” by Dr. V. N. Vedamurthy & Dr. N.Ch. S.N. Iyengar, Vikas
Publication.
7. “Numerical Analysis” by Richard L. Burden, J. Douglas Faires, Cengage
Publication.
8. “ Numerical Methods” Srimanta Pal, Oxford University Press.
Chapter wise Coverage from the main reference books :
1 : From Book # 1 � Chp. 2 , Chp. 3 section 3.3 & section 3.4
2 : From Book # 1 � Chp. 4 , Chp. 5 upto subsection 5.3.2, Chp. 7 only section 7.1
(Case study)
From Book # 2 � Chp. 5 pages 118 – 123 (also refer suggested reading Bk # 1)
www.gtucampus.com MCA(New Syllabus 2009) Sem-II 21 of 26

3: From Book # 1 � Chp. 12 section 12.1 except subsection 12.1.3, section 12.2,
Chp. 13 only section 13.1 except 13.1.4, section 13.2,
subsection 13.6.3 & subsection 13.6.4, Chp. 14 only section 1
From Book # 2 � Chp. 2 pages 17 – 23, 28 – 31 & 3
4 : From Book # 1 � Chp. 16 upto subsection 16.2.4,Chp. 17 section 17.3 except
subsection 17.3.3, Chp. 18 only section 18.3
From Book # 2 � Chp. 3 pages 53 – 62
5: From Book # 1 � Chp. 8 upto section 8.4, Chp. 10 only section 10.2
Chp. 20 section 20.1 & section 20.3 upto 20.3.3
Chp. 21 only section 21.2.4
From Book # 2 � Chp. 6 pages 127 – 130 & 144 - 149
Accomplishments of the student after completing the course :
� Solve linear and non-linear algebraic equations, perform operations of calculus, fit
curves, and solve differential equations using a computer
� Appreciate problems due to rounding errors and convergence
www.gtucampus.com MCA(New Syllabus 2009) Sem-II 22 of 26

GUJARAT TECHNOLOGICAL UNIVERSITY
Master of Computer Application
Subject Name : Database Management Systems – II
Subject Code : 620006
_____________________________________________________________
Objectives: This course is intended to give students knowledge of how RDBMS is
managed. It will prepare a theoretical as well as practical background of RDBMS.
Prerequisites: Database designing and retrieving using SQL and PL/SQL
Contents:
1. Transaction Processing and Concurrency control
Transaction concepts : Transaction execution and Problems, Transaction execution
and control with SQL, Transaction properties, Transaction log, Concurrency control,
Locking methods for concurrency control, Timestamp methods for concurrency
control, Optimistic methods for concurrency control (Read phase, validation phase,
Write phase), Deadlock handling – detection and resolution
2. Database backup and Recovery
Need of Database backup, Database backup techniques, Types of Database failures,
Types of Database recovery (Forward recovery, Backward recovery, Media
recovery), Recovery techniques (Deffered Update, Immediate update, Shadow
Paging, Checkpoints), Buffer management.
3. Implementing Security in Databases
Security & integrity threats, Defense mechanisms, Statistical database auditing &
control, Granting/revoking of privileges using SQL
4. Introduction to Other Databases
Overview of parallel databases, Overview of Distributed databases, Overview of
Object oriented databases
5. Relational Algebra
Basic operators (Select, project, union, set, difference, Cartesian product and
rename)
www.gtucampus.com MCA(New Syllabus 2009) Sem-II 23 of 26

Additional operators (Set interaction, Natural Join, Division and Assignment
operator),
Insert, Update, Delete operators.
6. Query Processing and Optimization
Overview, Query interpretation, Equivalence of expressions, Algorithm for
executing query operations, Heuristics of Query, Optimization cost estimation of
queries, Basic query optimization strategies:Selection operation, Sorting, Join
operation
Main Reference books :
1. “Database Systems:Concepts, Design and Applications”, S. K. Singh., Pearson
Education, (2006),ISBN: 978-81-7758-567-4.
2. “Database System Concepts”, Silberscatz, Korth, Sudarshan, Fifth Edition,
McGraw Hill International Edition, ISBN: 007-124476-X.
3. “An Inroduction to Database Systems”, C.J.Date, A. Kannan, S. Swaminathan,
Pearson Education, Eighth Edition,(2006),ISBN: 978-81-7758-556-8
Suggested Additional Reading:
1. “Fundamentals of Database Systems”, Elmsasri, Navathe, , Pearson Education ,
Fifth Edition (2008), ISBN: 978-81-317-1625-0
2. Database Management Systems, Ramakrishnan, Gehrke, , McGraw Hill, Third
Edition.
3. “Database Systems: Design, Implementation and Management”, Peter Rob,
Carlos Coronel, Cengage Learning , Seventh Edition(2007)ISBN-13:978-81-315-
0319-5 .
Chapter wise Coverage from the main reference book(s):
Book No. 1: Chapters – 4, 11,14,15,17,18
Book No. 2: Chapters-- 15,16,17
Accomplishments of the student after completing the course:
Knowledge of handing multiple transactions effectively, query processing and query
optimization concepts.
www.gtucampus.com MCA(New Syllabus 2009) Sem-II 24 of 26

GUJARAT TECHNOLOGICAL UNIVERSITY
Master of Computer Application
Subject Name : Theory of Computation
Subject Code : 620007
_____________________________________________________________
Objectives:
• Understanding and development of theoretical models of computations and their
analysis.
• The models of computations include (i) Finite Automata (and Regular Languages), (ii)
Push Down Automata (and Context-free Languages), (iii) Turing Machine (and their
Languages).
• The aim of analysis is to identify and prove the capabilities and limitations of particular
models
• of Computations.
Prerequisites:
Knowledge of (a) Discrete Mathematics (b) Mathematical Induction and Structural Induction is
desirable.
Contents:
1. Introduction, Sets , Logic , Functions , Relations , Languages , Proofs Mathematical
Induction , Strong Principle of Mathematical Induction , Recursive Definitions ,
Structural Induction
2. Regular Languages & Regular Expressions, Finite Automata (FA), Distinguishing
Strings w.r.t. Language , Union, Intersection, & Compliment of Languages
3. Non-deterministic Finite Automata (NFA), NFA with Null-Transitions, Kleene's
Theorem
4. A Criterion for Regularity, Minimal Finite Automata, Pumping Lemma for Regular
Languages
5. Introduction to Context-Free Grammar (CFG) , Regular Grammars , Derivation (Parse)
Trees & Ambiguities , An Unambiguous CFG for Algebraic Expressions , Simplified
Forms & Chomsky Normal Forms
6. Introduction to Push Down Automata (PDA), Deterministic PDA (DPDA), PDA
corresponding to a Given CFG , CFG Corresponding to a Given PDA , Parsing
7. The Pumping Lemma for CFG , Intersection & Complement of CFGs , Decision
Problems Involving CFGs
www.gtucampus.com MCA(New Syllabus 2009) Sem-II 25 of 26

8. Turing Machine (TM) Definition & Examples, Computing a Partial Function with a TM
9. Recursive Enumerable & Recursive Languages, Enumerating a Language, Context-
Sensitive Languages & Chomsky Hierarchy
Note:
1. Only those proofs which use Induction are included in the syllabus. In case of other
theorems and Lemmas, proof may be omitted. However, the purpose, importance and
applications of all theorems and Lemmas must be discussed.
Main Reference Book:
"Introduction to Languages and the Theory of Computation", John C. Martin, Tata McGraw-
Hill, (2003), 3rd
Edition, ISBN: 007049939X
Suggested Additional Reading:
1. "Elements of the Theory of Computation", Harry Lewis & Christos H. Papadimitriou,
EEE (PHI), 2nd
Edition ,ISBN-978-81-203-2233-2.
2. " Theory of Computation”, Michael Sipser, ", Cengage Learning(2007), ISBN-13: 978-
81-315-0513-7
3. “ Introduction to Automata Theory, Languages, and Computation ”, Hopcroft, Motwani
& Ullman, Pearson Education, 3rd
Edition, (2008), ISBN: 978-81-317-2047-9
Chapterwise Coverage from main reference book(s) :
Chapters : 1.1-1.5, 2.1-2.5, 3.1-3.5, 4.1-4.3, 5.1-5.3, 6.1-6.6, 7.1-7.6, 8.1-8.3,
9.1-9.2, 10.1-10.2,10.4.
Accomplishment of Students after Studying this Course :
• Ability to distinguish between Regular Expressions and Non-regular Expressions.
• Ability to develop FA for a given regular language and vice versa (i.e. to develop a
regular language from a given FA).
• Ability to use Pumping Lemma to optimize FA.
• Understanding of CFG with its potential to describe a big set of non-regular languages
using finite number of production rules.
• Ability to develop Push Down Automata for a given CFG.
• Understanding of Turing Machine and their languages, with a good feel of the enhanced
and bigger set of languages supported by Turing Machine.
www.gtucampus.com MCA(New Syllabus 2009) Sem-II 26 of 26