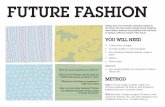
Future fashion report
-
Upload
lokeshboran -
Category
Education
-
view
572 -
download
0
description
Transcript of Future fashion report

ABSTRACT
The shopenmart.com Web site is the application that provides customers with online shopping.
Through a Web browser, a customer can browse the catalog, place items to purchase into a
virtual shopping cart, create and sign in to a user account, and purchase the shopping cart
contents by placing an order with a credit card.
The Application is a working demonstration of how to use blueprints principles in a real
application design. This document is an online guide to the design and the implementation of
the application Enterprise Applications with web technology.
Each release of the application maintains consistent design features such as separating logic and
presentation, using web component for control and web pages for presentation, using business
components, and so on. High-level design features, this document goes deeper into the
implementation details of the current application release.
This document is provided as an online-only resource so that it may be continually extended and
updated. This document begins with a description of the separate applications that the sample
application comprises, describes the modular structure of the shopenmart.com application, and
provides an in-depth description of several pieces of the modules.
Page | 1

Chapter - 1
INTRODUCTION
The FUTURE FASHION Web site is the application that provides customers with online
shopping. Through a Web browser, a customer can browse the catalog, place items to purchase
into a virtual shopping cart, create and sign in to a user account, and purchase the shopping cart
contents by placing an order with a credit card.
The Application is a working demonstration of how to use blueprints principles in a
real application design. This document is an online guide to the design and the implementation
of the application Enterprise Applications with web technology.
Each release of the application maintains consistent design features such as separating
logic and presentation, using web component for control and web pages for presentation, using
business components, and so on. High-level design features, this document goes deeper into the
implementation details of the current application release.
This document is provided as an online-only resource so that it may be continually
extended and updated. This document begins with a description of the separate applications that
the sample application comprises, describes the modular structure of the EMAT application, and
provides an in-depth description of several pieces of the modules.
Each FUTURE FASHION module has different requirements from the others. This
section describes the requirements, design, and implementation of each module.
Control module—the control module dispatches requests to business logic, controls
screen flow, coordinates component interactions, and activates user sign on and registration. The
control module is implemented by the WAF and application-specific WAF extensions.
Shopping cart module—the shopping cart tracks the items a user has selected for
purchase
Page | 2

Sign on module—the sign on module requires a user to sign on before accessing certain
screens, and manages the sign on process
Messaging module—the messaging module asynchronously transmits purchase orders
from the pet store to the OPC
Catalog module—the catalog module provides a page-based view of the catalog based on
user search criteria.
Customer module—the customer module represents customer information: addresses,
credit cards, contact information, and so on
1.1 Control Module Requirements
The control module forms the framework underlying the application, so it naturally has the
most high-level requirements. Extensibility and maintainability are prime considerations in this
module. The control module must be extensible because all real-world enterprise applications
change constantly. Because the control module plays a role in virtually every interaction, its code
must be well-structured to avoid complexity-related maintenance problems. The requirements of
the control module are:
The module must handle all HTTP requests for the application. This module controls a
Web application, and interacts with a user who sends HTTP service requests. The control module
is responsible for classifying and dispatching each of these requests to the other modules.
HTTP responses may be of any content type. Web application developers do not want to
be limited to just textual content types. The control module must also be able to produce binary
responses.
Business logic must be easily extensible. Enterprise applications are always changing and
growing as business rules and conditions change. A developer familiar with the control module
should be able easily to add new functionality with minimal impact on existing functions.
Module must provide application-wide control of look and feel. Manually editing
hundreds or dozens of user views is not a practical way to manage application look and feel. The
Page | 3

control module must provide a way for application screen layout and style to be controlled
globally.
Application must be maintainable even as it grows. The control module must be
structured so that new functions added over time do not result in a thicket of unmentionable
“spaghetti” code. It should be possible to easily understand the control of even an application
with several hundred business classes. Application-wide functionality must be easy to add. New
application requirements occasionally apply to every operation or view in an application. The
control module must be structured so that such requirements can be easily met.
Page | 4

Chapter – 2
REQUIREMENTS
2.1 TOOLS, PLATFORM & LANGUAGE TO BE USED
2.1.1 TOOLS:
FRONT-END : ASP.NET(With C# 4.0)
BACK-END : SQL SERVER 2008
2.1.2 PLATFORM:
WINDOW SERVER : WINDOWS – 2007
2.2 HARDWARE AND SOFTWARE ENVIRONMENT
2.2.1 HARDWARE ENVIRONMENT:
PROCESSOR : P-IV(1.80 GHZ)
RAM : 128 MB
STORAGE CAPACITY : 40 GB
DRIVERS : 52X24X
52X CD : 1.44 MB FDD
2.2.2 SOFTWARE ENVIRONMENT:
OPERATING SYSTEM : WINDOW 2007
RDBMS : SQL SERVER 2008
SOFTWARE : VISUAL STUDIO 2010
Page | 5

Chapter - 3
SYSTEM DEVELOPMENT METHODOLOGY
3.1 Development Process Phases:- Following phases are-
1. Initiation Phase
The initiation of a system (or project) begins when a business need or opportunity is
identified. A Project Manager should be appointed to manage the project. This business need is
documented in a Concept Proposal. After the Concept Proposal is approved, the System Concept
Development Phase begins.
2. System Concept Development Phase
Once a business need is approved, the approaches for accomplishing the concept are
reviewed for feasibility and appropriateness. The Systems Boundary Document identifies the
scope of the system and requires Senior Official approval and funding before beginning the
Planning Phase.
3. Planning Phase
The concept is further developed to describe how the business will operate once the approved
system is implemented, and to assess how the system will impact employee and customer
privacy. To ensure the products and /or services provide the required capability on-time and
within budget, project resources, activities, schedules, tools, and reviews are defined.
Additionally, security certification and accreditation activities begin with the identification of
system security requirements and the completion of a high level vulnerability assessment.
4. Requirements Analysis
Phase Functional user requirements are formally defined and delineate the requirements in terms
of data, system performance, security, and maintainability requirements for the system. All
Page | 6

requirements are defined to a level of detail sufficient for systems design to proceed. All
requirements need to be measurable and testable and relate to the business need or opportunity
identified in the Initiation Phase.
5. Design Phase
The physical characteristics of the system are designed during this phase. The operating
environment is established, major subsystems and their inputs and outputs are defined, and
processes are allocated to resources. Everything requiring user input or approval must be
documented and reviewed by the user. The physical characteristics of the system are specified
and a detailed design is prepared. Subsystems identified during design are used to create a
detailed structure of the system. Each subsystem is partitioned into one or more design units or
modules. Detailed logic specifications are prepared for each software module.
6. Development Phase
The detailed specifications produced during the design phase are translated into hardware,
communications, and executable software. Software shall be unit tested, integrated, and retested
in a systematic manner. Hardware is assembled and tested.
7. Integration and Test Phase
The various components of the system are integrated and systematically tested. The user tests the
system to ensure that the functional requirements, as defined in the functional requirements
document, are satisfied by the developed or modified system. Prior to installing and operating the
system in a production environment, the system must undergo certification and accreditation
activities.
8. Implementation Phase
The system or system modifications are installed and made operational in a production
environment. The phase is initiated after the system has been tested and accepted by the . This
Page | 7

phase continues until the system is operating in production in accordance with the defined user
requirements.
9. Operations and Maintenance Phase
The system operation is ongoing. The system is monitored for continued performance in
accordance with user requirements, and needed system modifications are incorporated. The
operational system is periodically assessed through In-Process Reviews to determine how the
system can be made more efficient and effective. Operations continue as long as the system can
be effectively adapted to respond to an organization’s needs. When modifications or changes are
identified as necessary, the system may reenter the planning phase.
10. Disposition Phase
The disposition activities ensure the orderly termination of the system and preserve the vital
information about the system so that some or all of the information may be reactivated in the
future if necessary. Particular emphasis is given to proper preservation of the data processed by
the system, so that the data is effectively migrated to another system or archived in accordance
with applicable records management regulations and policies, for potential future access.
3.2 SDLC Objectives
This guide was developed to disseminate proven practices to system developers, project
managers, program/account analysts and system owners/users throughout the DOJ. The specific
objectives expected include the following:
To reduce the risk of project failure
To consider system and data requirements throughout the entire life of the system
To identify technical and management issues early
To disclose all life cycle costs to guide business decisions
To foster realistic expectations of what the systems will and will not provide
Page | 8

To provide information to better balance programmatic, technical, management, and cost
aspects of proposed system development or modification
To encourage periodic evaluations to identify systems that are no longer effective
To measure progress and status for effective corrective action
To support effective resource management and budget planning
To consider meeting current and future business requirements
2.3 Key Principles
This guidance document refines traditional information system life cycle management
approaches to reflect the principles outlined in the following subsections. These are the
foundations for life cycle management.
Life Cycle Management should be used to ensure a Structured Approach to Information Systems
Development, Maintenance, and Operation
This SDLC describes an overall structured approach to information management. Primary
emphasis is placed on the information and systems decisions to be made and the proper timing of
decisions. The manual provides a flexible framework for approaching a variety of systems
projects. The framework enables system developers, project managers, program/account
analysts, and system owners/users to combine activities, processes, and products, as appropriate,
and to select the tools and methodologies best suited to the unique needs of each project.
1. Support the use of an Integrated Product Team
The establishment of an Integrated Product Team (IPT) can aid in the success of a project. An
IPT is a multidisciplinary group of people who support the Project Manager in the planning,
execution, delivery and implementation of life cycle decisions for the project. The IPT is
Page | 9

composed of qualified empowered individuals from all appropriate functional disciplines that
have a stake in the success of the project. Working together in a proactive, open communication,
team oriented environment can aid in building a successful project and providing decision
makers with the necessary information to make the right decisions at the right time.
2. Each System Project must have a Program Sponsor
To help ensure effective planning, management, and commitment to information systems, each
project must have a clearly identified program sponsor. The program sponsor serves in a
leadership role, providing guidance to the project team and securing, from senior management,
the required reviews and approvals at specific points in the life cycle. An approval from senior
management is required after the completion of the first seven of the SDLC phases, annually
during Operations and Maintenance Phase and six-months after the Disposition Phase. Senior
management approval authority may be varied based on dollar value, visibility level,
congressional interests or a combination of these.
The program sponsor is responsible for identifying who will be responsible for formally
accepting the delivered system at the end of the Implementation Phase.
3. A Single Project Manager must be Selected for Each System Project
The Project Manager has responsibility for the success of the project and works through a
project team and other supporting organization structures, such as working groups or user
groups, to accomplish the objectives of the project. Regardless of organizational affiliation, the
Project Manager is accountable and responsible for ensuring that project activities and decisions
consider the needs of all organizations that will be affected by the system. The Project Manager
develops a project charter to define and clearly identify the lines of authority between and within
the agency’s executive management, program sponsor, (user/customer), and developer for
purposes of management and oversight.
4. A Comprehensive Project Management Plan is Required for Each System Project
Page | 10

The project management plan is a pivotal element in the successful solution of an
information management requirement. The project management plan must describe how each life
cycle phase will be accomplished to suit the specific characteristics of the project. The project
management plan is a vehicle for documenting the project scope, tasks, schedule, allocated
resources, and interrelationships with other projects. The plan is used to provide direction to the
many activities of the life cycle and must be refined and expanded throughout the life cycle.
5. Specific Individuals must be assigned to Perform Key Roles throughout the Life Cycle
Certain roles are considered vital to a successful system project and at least one individual
must be designated as responsible for each key role. Key roles include program/functional
management, quality assurance, security, telecommunications management, data administration,
database administration, logistics, financial, systems engineering, test and evaluation, contracts
management, and configuration management. For most projects, more than one individual should
represent the actual or potential users of the system (that is, program staff) and should be
designated by the Program Manager of the program and organization
Page | 11

Chapter - 4
FEASIBILITY STUDY
A feasibility study is conducted to select the best system that meets performance requirement.
This entails an identification description, an evaluation of candidate system and the selection of
best system for he job. The system required performance is defined by a statement of constraints,
the identification of specific system objective and a description of outputs.
The key considerations in feasibility analysis are:
1. Economic Feasibility:
2. Technical Feasibility:
3. Operational Feasibility:
4.1 Economical feasibility
It looks at the financial aspects of the project. It determines whether the
management has enough resources and budget to invest in the proposed system and the estimated
time for the recovery of cost incurred. It also determines whether it is worth while to invest the
money in the proposed project. Economic feasibility is determines by the means of cost benefit
analysis. The proposed system is economically feasible because the cost involved in purchasing
the hardware and the software are within approachable. The personal cost like salaries of
employees hired are also nominal, because working in this system need not required a highly
qualified professional. The operating-environment costs are marginal. The less time involved
also helped in its economical feasibility. It was observed that the organization has already using
computers for other purpose, so that there is no additional cost to be incurred for adding this
system to its computers.
The backend required for storing other details is also the same database that is Sql. The
computers in the organization are highly sophisticated and don’t needs extra components to load
the software. Hence the organization can implement the new system without any additional
expenditure. Hence, it is economically feasible
Page | 12

The result of the feasibility study is a formal proposal. This is simply report-a formal document
detailing the nature and the scope of the proposed solution. The proposals summarize what is
known and what is going to be done. Three key considerations are involved in the feasibility
analysis: economic, technical and operational behavior.
4.2 Technical Feasibility: Technical feasibility center around the existing computer system
hardware etc. and to what extent it can support the proposed addition. For example, if the current
computer is operating at 80% capacity - an arbitrary ceiling – then running another application
could over load the system or require additional hardware. This involves financial consideration
to accommodate technical enhancements. If the budget is a serious constraint then the project is
judged not feasible.
4.3 Operational Feasibility: It is common knowledge that computer installations have
something to do with turnover, transfers, retraining and changes in employee job status.
Therefore, it is understandable that the introduction of a candidate system requites special efforts
to educate, sell, and train the staff on new ways of conducting business.
4.4 C h o i c e o f P l a t f o r m ?
In any organization a lot of data is generated as result of day-to-day operations. In the
past, all kind of data – be it business of a company. Since the task was performed
manually, it was time consuming and error prone. With the advent of computer, the task
of maintaining large amount of data has undergoes a sea change. Today computer system
have become so user friendly that even first time users can create their own application
with the help of tools such as MS-Access, Fox-Pro and SQL Server. These tools are very
visual and hence user friendly. They provide a point and click environment for building
applications that can interact with large amount of data
Technical Feasibility
It is a measure of the practically of a specific technical solution and the availability of
technical resources and expertise
The proposed system uses Java as front-end and Sql server 2003 as back-end tool.
Oracle is a popular tool used to design and develop database objects such as table
views, indexes.
Page | 13

The above tools are readily available, easy to work with and widely used for
developing commercial application.
Hardware used in this project are- p4 processor 2.4GHz, 128 MB RAM, 40 GB
hard disk, floppy drive. This hardware was already available on the existing computer system.
The software like Sql Server 2003, iis,.net framework and operating system WINDOWS-XP’
used were already installed On the existing computer system. So no additional hardware and
software were required to purchase and it is technically feasible. The technical feasibility is in
employing computers to the organization. The organization is equipped with enough computers
so that it is easier for updating. Hence the organization has not technical difficulty in adding
this system.
Operational Feasibility
The system will be used if it is developed well then be resistance for users that
undetermined
No major training and new skills are required as it is based on DBMS model.
It will help in the time saving and fast processing and dispersal of user request and
applications.
New product will provide all the benefits of present system with better performance.
Improved information, better management and collection of the reports.
User support.
User involvement in the building of present system is sought to keep in mind the user
specific requirement and needs.
User will have control over their own information. Important information such as pay-
slip can be generated at the click of a button.
Behavioral Feasibility
People are inherent to change. In this type of feasibility check, we come to know if the
newly developed system will be taken and accepted by the working force i.e. the people who will
use it.
Page | 14

Chapter - 5
DATA FLOW DIAGRAM
5.1 Overview
DFD is an important tool used by system analysts. The main merit of DFD is that it can
provide an over view of what data a system would process, what transformation of data are done,
what files are used and where the result flows. The graphical representation of the system makes
it a user and analyst. DFDs are structured in such a way that starting from a simple diagram
which provides a broad overview at a glance, there can be expanded to a hierarchy of diagrams
giving to more and more details
• Square: -Source or destination of data (External or Internal)
• As the name suggested does not fall within system boundary, hence
they are defined as source or destination of data.
• Rounded rectangle/Circle: Process
This can be defined at place where transformation of data takes place; this
transformation includes additional modification deletion or accumulation of
data.
Open ended rectangle/parallel lines, data store.
Page | 15

Data flow can take place:
1. Between process
2. File to process
3. External entity to process
4. Process to external entity
5. Process to file
Information Flow of Data for Testing
Fig. 5.1 Work Flow of Future Fashion
Page | 16
TestingDebu
g
Reliability
Model
Evaluation
Test ResultsSoftware Configuration
Test Configuration
Expected Results
Corrections
Error RateData
Information Flow of Data Testing

DFD
0’s Level
Fig. 5.2. 0’s Level DFDFig. 5.2. 0’s Level DFD
1st Level
Fig. 5.3. 1- Level DFD
Page | 17
LOGINUser
PURCHASE
Data Base

2nd Level
Fig. 5.4. 2nd Level DFD
ER-DIGRAM OF Shopenmart.comER-DIGRAM OF Shopenmart.com
Fig. 5.5. E-R Diagram
Page | 18
LOGINUser
PURCHASE
CREDIT CARD VERIFICATIOnnN
ORDER GENERATE
ORDER GENERATE

Module Details of Future Fashion
Database Module: - Table Entity Relationship of Future Fashion
Fig. 5.6. Table Entity Relationship
Page | 19

Chapter - 6
TABLE STRUCTURES
Table 6.1 Login
Table 6.2 Order Details
Table 6.3 Payment
Table 6.4 Product
Page | 20

Table 6.5 Stock
Table 6.6 User Details
Page | 21

Chapter - 7
SNAPSHOT
Fig. 7.1. Login page
Fig. 7.2. Home page
Page | 22

Fig. 7.3. Ladies skirt Page
Fig. 7.4. Ladies sleveless skirt page
Page | 23

Fig. 7.5. Tie page
Fig. 7.6. Marriage page
Page | 24

Fig. 7.7. Kids Wears Page
Fig. 7.8. Diamond Rings page
Page | 25

Chapter - 8
MAINTENANCE
Maintenance of the project is very easy due to its modular design and concept any modification
can be done very easily. All the data are stored in the software as per user need & if user wants to
change he has to change that particular data, as it will be reflected in the software everywhere.
Some of the maintenance applied is: -
(1) BREAKDOWN MAINTENANCE: -
The maintenance is applied when an error occurs & system halts and further processing
cannot be done .At this time user can view documentation or consult us for rectification & we
will analyze and change the code if needed. Example: - If user gets a error “report width is larger
than paper size” while printing report & reports can not be generated then by viewing the help
documentation & changing the paper size to ‘A4’ size of default printer will rectify the problem.”
(2) PREVENTATIVE MAINTENANCE: -
User does this maintenance at regular intervals for smooth functioning (Operation) of
software as per procedure and steps mentioned in the manual. Some reasons for maintenance are:
-
(a) Error Correction: - Errors, which were not caught during testing, after the system has,
been implemented. Rectification of such errors is called corrective maintenance.
(b) New or changed requirements: - When Organization requirements changes due to
changing opportunities.
(c) Improved performance or maintenance requirements: -Changes that is made to improve
system performance or to make it easier to maintain in the future are called preventive
maintenance. Advances in technology (Adaptive maintenance): - Adaptive maintenance includes
all the changes made to a system in order to introduce a new technology.
Page | 26

SECURITY MEASURES:-
The security measures imposed in the software are: -
• A login password is provided in the software. User must login to activate the application.
• User cannot change the password. To change password he must contact the administrator.
• The user/password are given through SQL Server2000. If this is installed on NT 4.0 then it is
highly secured. If it is installed on Windows 98, then run in degraded mode.
• Data security, correctness integrity is checked up before saving, update or delete if errors
found the procedure is aborted.
• A primary key & foreign key concept is implemented for avoiding incorrect data entry or
intentional or accidental delete or modification of data.
• When user tries to delete the data then this first check for its reference used by other data, if
found the deletion aborted.
• I am also providing various securities at user level or at forms.
• I am giving security at LAN with the help of status of user.
Page | 27

CONCLUSION
On the basis of the work done in dissertation entitled “Shopmart.com”, the following conclusions
emerge from the development.
1. This project has achieved the objective of replacing/augmenting the conventional system
of arranging manpower as could be conducted by a typical telecom dept.
2. The development of this package has been achieved by using C#.NET, which is very
conductive to develop the package with regard to time and specific need to the user.
3. This package is highly user friendly, required an optimal minimal input from user while
providing highly relevant and focused outputs.
4. Fully automated, avoiding human intervention. Hence it provides a very rapid cost
effective alternative to the conventional manual operation/procedures; the visual outputs
are more reliable than the audio forms of manual communication.
5. The system can further extended as per user and administrative requirements to
encompass other aspects of connection management for telecom dept.
6.6. It is connected with the internet for easily retrieved data about different types ofIt is connected with the internet for easily retrieved data about different types of
products, newly launched products can be easily added into the site using database.products, newly launched products can be easily added into the site using database.
7.7. All the information can be easily accessed the Customer like their details, order status,All the information can be easily accessed the Customer like their details, order status,
stock, Transaction.stock, Transaction.
8.8. It can be modify and the others details can be easily provided to customer.It can be modify and the others details can be easily provided to customer.
9.9. Report on the different basis will be easily created on the demand.Report on the different basis will be easily created on the demand.
LIMITATIONS: -
This project does not Edit the date of connection or store the date of transfer in
case of connection transfer.
System date for the project is like as backbone for the human, i.e. proposed
system is depends on system date so it must be correct.
Cannot be connected to the Internet.
Page | 28

There are some inherent problems like time, finance etc. to elaborate further
study.
REFERENCES
1. Apress - Real World ASP.NET Best Practices McGraw-Hill.
2. Wrox-“ASP.NET 2.0 with C# .NET 2005- Professional
3. Mridula Parihar-“ASP.NET Bible”
4. Andrew Trolsen-“A Comprehensive Guide to C# and the .NET platform”
5. “School.com”,http://www.w3c.school.com
6. en.wikipedia.org/wiki/Active_Server_Pages
7. www.learn asp .com/
8. www. asp -india.com/
Page | 29