Foundation Section 1
-
Upload
gokila-rajaiah -
Category
Documents
-
view
220 -
download
0
Transcript of Foundation Section 1
-
8/3/2019 Foundation Section 1
1/95
Dr. G. A. Marin
Network Analysis: Foundation 1-1
-
8/3/2019 Foundation Section 1
2/95
1970s1970sBusiness Environment: IBM's SNA
erarc ca, or er y, re a e
Sysdef for Topology and Paths
Connection-oriented and guaranteed service at link layer
a a on y
Low-speed (unreliable) leased lines
Research Environment: TCP/IP
Distributed, disorderly, less reliable
Next hop vs fixed paths
Connectionless (data only)
Phone Companies (European): X.25 StandardConnection-oriented
SVC and PVC with Flow Control
Network Analysis: Foundation 1-2
Assumes noisy lines
-
8/3/2019 Foundation Section 1
3/95
NSFNet Backbone to Interconnect Super Computers
o c a protoco o rpanet n 1983
56 kbps backbone for 6 super computer centers
Thousands of researchers connect their subnets
Version 2 (IBM RS6000s and Fiber) ran at 448 kbps
By 1990 1.5 Mbps , ,
IBM Develops Advanced Peer-to-Peer Networking
LAN Growth Explosive
Ethernet (collisions)Token Ring (no collisions)
Novell's Netware (IPX based on XNS)
Network Analysis: Foundation 1-3
-
8/3/2019 Foundation Section 1
4/95
Internet
1990: 200,000 computers and 3,000 networks1995: multiple backbones, 100s regional nets, 10so ousan s o , m ons o os s
Doubles yearly!?
non-academics (mosaic)
NREN Gigabit Network funded by ARPA & NSF
Internet Society Founded 1992!Commercially Cisco uses IP to grow to Billions
Network Analysis: Foundation 1-4
eve ue
-
8/3/2019 Foundation Section 1
5/95
1990s1990s continuedcontinuedMIT, U Pa, IBM, Bellcore Research in
highspeed paket switchingFrame Relay Forum evolve X.25concepts for higher speed WAN lines
(1.5Mbps)ATM becomes successful in telephonybackbones (multiples of 155mbps)
DARPA Funding Next GenerationInternet
Network Analysis: Foundation 1-5multi-gigabit per second capabilities
-
8/3/2019 Foundation Section 1
6/95
oundationGoals:
Overview:
ay oun a on or
understanding how tobuild a network
Applications
Concepts & Terminology
Required services
Terminology
Network Architecture
Performance TCP/IP & OSI
Protocols and
Channel Multiplexing
Socket Interface
Performance Metrics
Network Analysis: Foundation 1-6
-
8/3/2019 Foundation Section 1
7/95
A licationsDistributed rocesses communicatin
across networkExamples: world wide web, email, FTP,
stream ng au o v eo, c atrooms
Use Application Layer Protocolsser agen mp emen s e app ca onlayer protocol: Email mail reader (e.g. outlook) Streaming audio/video media player
Network Analysis: Foundation 1-7
-
8/3/2019 Foundation Section 1
8/95
Client-server aradi mTypical network app has two
ieces: clientand serverapplicationtransport
data link
physicalClient: initiates contact with server
request
(speaks first)
typically requests service fromserver
applicationtransportnetwork
Web: client implemented inbrowser; e-mail: in mail reader
rep y
data linkphysical
provides requested service to client
e.g., Web server sends requested Web
Network Analysis: Foundation 1-8
page, mail server delivers e-mail
-
8/3/2019 Foundation Section 1
9/95
Internet Protocol Gra
Network Analysis: Foundation 1-9
-
8/3/2019 Foundation Section 1
10/95
The Web: the htt rotocol
htt : h ertext transfer
protocol Webs application layer PC running
Ex lorer
client/server model
client:browser that, ,
displays Web objects
server:Web server
Serverrunning
NCSA Webserver
response to requests
http1.0: RFC 1945
Mac runningNavigator
Network Analysis: Foundation 1-10
p . :
-
8/3/2019 Foundation Section 1
11/95
T e tt rotocol: orehtt : TCP trans ort htt is stateless
service: client initiates TCP
server maintains noinformation aboutast client re uests
to server, port 80
server accepts TCP Protocols that maintain
aside
http messages (application-layer protocol messages)
past history (state) mustbe maintained
(http client) and Web server(http server)
server c en cras es,their views of state maybe inconsistent, must be
Network Analysis: Foundation 1-11
-
8/3/2019 Foundation Section 1
12/95
http exampleSuppose user enters URLwww.someSchool.edu/someDepartment/home.index
(contains text,
references to 10
1a. http client initiates TCPconnection to http server
rocess at1b. http server at host
jpeg images)
www.someSchool.edu. Port 80is default for http server.
www.someSchool.edu waitingfor TCP connection at port 80.
accepts connection, notifying2. http client sends http request
message(containing URL) intoTCP connection socket 3. http server receives request
,messagecontaining requestedobject(someDepartment/home.index),
Network Analysis: Foundation 1-12
sen s message into sockettime
-
8/3/2019 Foundation Section 1
13/95
http example (cont.)4. http server closes TCP
5. http client receives responsemessage containing html file,dis la s html. Parsin html
connec on.
file, finds 10 referenced jpegobjects
6. Steps 1-5 repeated for eachtimeof 10 jpeg objects
Network Analysis: Foundation 1-13
-
8/3/2019 Foundation Section 1
14/95
Electronic Mailoutgoing
Three ma or com onents:
user mailbox
user
user agents mail servers sim le mail transfer
useragent
mailserver
protocol: smtp
User Agent
mailserver user
agentSMTPa. .a. ma rea er
composing, editing, readingmail messages
useragent
mailserver
SMTP
e.g., u ora, u oo , e m,Netscape Messenger outgoing, incoming messages
useragent
user
Network Analysis: Foundation 1-14
agent
-
8/3/2019 Foundation Section 1
15/95
Electronic Mail: mail serversMail Servers user
mailbox contains incomingmessages (yet to be read)for user
useragent
mailserver
message queue of outgoing(to be sent) mail messages
mailserver user
agentSMTPservers to send emailmessages
useragent
mailserver
SMTP
server
server: receiving mailuseragent
Network Analysis: Foundation 1-15
agent
-
8/3/2019 Foundation Section 1
16/95
Electronic Mail: smt RFC 821 uses tcp to reliably transfer email msg from client to
server, port 25
direct transfer: sending server to receiving server
three hases of transfer
handshaking (greeting)
transfer of messages
command/response interaction
commands: ASCII text
response: status code and phrasemessages must be in 7-bit ASCII
Network Analysis: Foundation 1-16
-
8/3/2019 Foundation Section 1
17/95
Sam le smt interactionS: 220 hamburger.edu
C: HELO crepes.fr
S: 250 Hello crepes.fr, pleased to meet you
C: MAIL FROM:
S: 250 [email protected]... Sender ok
: : < o am urger.e u>
S: 250 [email protected] ... Recipient ok
C: DATA" " , .
C: Do you like ketchup?
C: How about pickles?
C: .
S: 250 Message accepted for delivery
C: QUIT
S: 221 hamburger.edu closing connection
Network Analysis: Foundation 1-17
-
8/3/2019 Foundation Section 1
18/95
:
telnet servername 25
see 220 reply from server enter HELO, MAIL FROM, RCPT TO, DATA, QUIT
commands
above lets you send email without using email client
Network Analysis: Foundation 1-18
-
8/3/2019 Foundation Section 1
19/95
s t : inal words smtp uses persistent Com arison with htt :
connections
smtp requires message(header & body) to be in 7-
http: pull email: push
bit ASCII
certain character strings
not permitted in msg (e.g.,
both have ASCIIcommand/responseinteraction status codes
CRLF.CRLF). Thus msg hasto be encoded (usually intoeither base-64 or quoted
http: each objectencapsulated in its own
pr n a e smtp server uses
CRLF.CRLF to determine
res onse msg smtp: multiple objects sent
in multipart msg
Network Analysis: Foundation 1-19
en o message
-
8/3/2019 Foundation Section 1
20/95
Foundation
Goals:
Overview:ay oun a on or
understanding how tobuild a network
Applications Concepts & Terminology
Required services
Terminology
Network Architecture
Network Software TCP/IP & OSI
Protocols and
Performance
Pa ers Socket Interface
Performance Metrics Problems
Network Analysis: Foundation 1-20Network Analysis: Foundation 1-20
-
8/3/2019 Foundation Section 1
21/95
Connectivit router workstationserver
obile
local ISP
connect computers Ma su ort a
regional ISP
strictly limited
number or many suppor sgrowth, it is said
company
.
Network Analysis: Foundation 1-21
ne wor
-
8/3/2019 Foundation Section 1
22/95
in s and Nodes, ,
computers..) some of which are directlyconnected by links.
Links (coax cable, twisted pair, fiber) are
either point-to-point or multiple access.Cooperating nodes can provide connectivity
across several direct links.
Directly connected Indirectly connected
Network Analysis: Foundation 1-22
-
8/3/2019 Foundation Section 1
23/95
Multi le Access Links and ProtocolsThree types of links: point-to-point (single wire, e.g. PPP, SLIP)
broadcast (shared wire or medium; e.g, Ethernet,, .
switched (e.g., switched Ethernet, ATM etc)
Network Analysis: Foundation 1-23
-
8/3/2019 Foundation Section 1
24/95
Network Analysis: Foundation 1-24
-
8/3/2019 Foundation Section 1
25/95
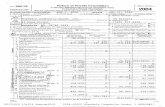
RSVP/IS-C
A working network
ISDN
PSTN
ES
ESRSVP/IS-CMSS-C
RSVP/IS-C
MSS-C
MSS-C
LAN
Token Ring
8210MSS-S
ARIS/GSMP
RSVP/IS
VLAN
DDNS-S
DHCP-S
FrameRelay
ATMOC/12, OC/48
8260/8265
HUBS
MSS-SARIS/GSMP
RSVP/IS
VLAN
DHCP
DDNS
RSVP/IS-C
MSS-C
8260/8265
HUBS MSS-S
ARIS/GSMP
RSVP/IS
VLAN
8260/8265
HUBS MSS-S
ARIS/GSMP
RSVP/IS
LAN
Public DataNetwork
X.25, X.21
8260/8265
HUBS MSS-S
ARIS/GSMP
RSVP/IS
VLAN
DHCP
DDNS
ROUTER2210/2216
ARIS
RSVP/IS
DHCP
DDNS
DHCP
DDNS
ROUTER
2210ARIS
/
RSVP/IS-C
MSS-C
Token Ring
ATM
39xx, 374X
OSA, MAE
390TCP Sprayer
HPR/IP
HPR/ATM
-
DHCP-S
Firewall
IP Sec.
DDNS-S
DHCP-S
Firewall
IP Sec.
RSVP/IS-C
MSS-C
BUT COMPLEXITY!AS/400
SP-2
MSS-C
---------ARIS/GSMP
RSVP/IS
IPSEC
Network Analysis: Foundation 1-25
-
8/3/2019 Foundation Section 1
26/95
Ter inolo
organized systematically to forward dataas it moves from source to destination.
Circuit Switched: establishes a circuit
from entry point to exit point of network,and analog or digital data moves alongcircuit with strict timing.
ac et w tc e : o es n networ sendiscrete blocks or packets of information
Network Analysis: Foundation 1-26
.
-
8/3/2019 Foundation Section 1
27/95
Ter inoloOne ho : acket moves across a network from one
node to a node directly connected. Eachmovement is a hop toward the destination.
ore-an - orwar : ac e s rece ve n sentirety, is stored and processed in an
intermediate node, and is then forwarded to anadjacent node.
Virtual Circuit: A store-and-forward network that
-end-to-end connection that guarantees certainquality of service.
Network Analysis: Foundation 1-27
-
8/3/2019 Foundation Section 1
28/95
Host: a node that uses the network (outside thenetwork)
Switch: a node that implements the network (inside thenetwork
Internetwork: A set of independent networks that areinterconnected
networks
Address: a byte string that identifies a node
network based on source and destination addresses.
Unicast and Multicast Addresses: addresses assigned to
Network Analysis: Foundation 1-28
.
-
8/3/2019 Foundation Section 1
29/95
oundationGoals:
Overview:
ay oun a on or
understanding how tobuild a network
ApplicationsConcepts & Terminology
Required services
Terminology
Network Architecture
Performance TCP/IP & OSI
Protocols and
Papers
Problems Socket Interface Performance Metrics
Network Analysis: Foundation 1-29
-
8/3/2019 Foundation Section 1
30/95
Networ Arc itecture Is the blue rint that uides the desi n and
implementation of a type of network. The blueprint follows a philosophy that falls
e ween sen an pray an guaran ee .
Generally includes a layer reference model.
protocols and various layers.
May include applets to be used by user-layer
applications. Treats user, designer, and service provider
.
-
8/3/2019 Foundation Section 1
31/95
i erin Pers ectivesA lication ro rammer cares mostl about
the services that the network provides(and the cost for those services). oss o a a Error-free delivery?
Network designer cares that networkresources are used efficiently and
a ocate to users air y.Network provider wants ease of
Network Analysis: Foundation 1-31
.
-
8/3/2019 Foundation Section 1
32/95
Networ arc itecture
Connectivity Re uired service levels
Robustness in case of failures
Fairness to users Cost-effective solutions
Again: A network architecture is a
uepr n or a way o u ng a ne worthat will satisfy all its requirements.
Network Analysis: Foundation 1-32
, , ,
-
8/3/2019 Foundation Section 1
33/95
-
8/3/2019 Foundation Section 1
34/95
La ers Services ProtocolsLa ers Services ProtocolsLayers: offer services to higher layers
that are requested by parameters beingpassed to service access points (SAPs).
Services: A set of primitives
o erations that a la er can erform forits users
Protocol: is a set of rules overnin the
format and meaning of frames, packets,or ms s exchan ed b eer entities.
Network Analysis: Foundation 1-34
Protocols implement the services.
-
8/3/2019 Foundation Section 1
35/95
La er O ver viewPhysical Layer: Transmits bit s over comm channel. Howto r epresent bit s and ensure reception. (Physical mediumlies lo icall below .
Data Link Layer: Takes raw t ransmission facilit y and
transfor ms to line free of undetected t ransmission er ror s.Sends data frames. Retransmits if needed. Flow controlusua y prov e .
N etwork Layer : Gets packets from source to dest inat ionacross a network. Provides rout ing, network congest ioncontr ol call admission net - net i/f erha s account into suppor t net mgt .
Transpor t Layer : Accept data from session layer ,segmentat ion & reassembly if needed, pass to networkayer , assure a p eces arr ve sa e y a o er en . rsend-to-end layer . Mult iplexing, flow control
Network Analysis: Foundation 1-35
-
8/3/2019 Foundation Section 1
36/95
Session Layer: Provides enhanced services tocertain applications over those provided bytransport layer. Synchronization as example.
resen a on ayer: rov es a onafunctions such as translation among different
character numerical and bit-strinrepresentations.
Application Layer: Supports protocols needed
y app ca ons suc as ne wor v r ua erm na,file format conversions, electronic mail, remoteob entr etc.
Network Analysis: Foundation 1-36
-
8/3/2019 Foundation Section 1
37/95
TCP/IP & Course ReferenceTCP/IP & Course ReferenceModelsModels
Application Layer Application Layer
Transport Layer Transport Layer
Network Layer Internet Layer
Data Link LayerrData Link LayerrData Link Layer
Host-to-network
Network Analysis: Foundation 1-37
Physical Layerr
-
8/3/2019 Foundation Section 1
38/95
Networks Interconnected by IP Routers
-
8/3/2019 Foundation Section 1
39/95
TCP/IP Application LayerTCP/IP Application Layer
Contains all higher level protocolsnc u ng:
Telnet virtual terminal protocol
SMTP Simple Mail Transfer Protocol
HTTP World-Wide-Web page trasfer protocol
Network Analysis: Foundation 1-39
-
8/3/2019 Foundation Section 1
40/95
TCP/IP Layer OverviewTCP/IP Layer Overview
Internet Layer: Heart of the Internet architecture. Hostsinsert packets into IP network that travel independentlyto destination (over distinct subnets). Implements the IP
(Internet Protocol) "protocol." Routing and networkcon estion avoidance are ke issues.
Transport Layer: End-to-end peer protocol as in OSI.Protocol (TCP) and User Datagram Protocol (UDP).TCP is reliable and connection-oriented. Supports
'
as flow control. UDP is unreliable and connectionless.Used with aps that do their own thing or voice or video
Network Analysis: Foundation 1-40
...
-
8/3/2019 Foundation Section 1
41/95
Hybrid Model
this course.
Network Analysis: Foundation 1-41Network Analysis: Foundation 1-41
-
8/3/2019 Foundation Section 1
42/95
Two major models for layer
serv ces Connection-oriented service
Like the telephone network. End-to-end agreements made before user
ra c ows. Greater complexity and greater reliability
Like the post office network. Each letter (packet) moves independently
roug e ne wor . Simpler and reliability can be improved with
hi her-la er services like re istered mail.
Network Analysis: Foundation 1-42Network Analysis: Foundation 1-42
-
8/3/2019 Foundation Section 1
43/95
Internet trans ort rotocols servicesTCP service: UDP service: connection-oriented:setup
required between client,server
unreliable data transferbetween sending andreceivin rocess
re ia e transportbetweensending and receiving process
flow control:sender wont
does not provide:connection setup,
reliabilit , flow control,
congestion control:throttlesender when networkoverloaded
congestion control, timing,or bandwidth guarantee
does not provide:timing,minimum bandwidthguarantees
Q: why bother? Why isthere a UDP?
Network Analysis: Foundation 1-43
-
8/3/2019 Foundation Section 1
44/95
Example NetworksExample Networks
System Network Architecture (SNA)
IBM's networking architecture used by 10,000+business networks
Mainframe model of computing...hierarchical- -
(APPN) architecture
Novell NetwarePredominant PC-based networkarchitecture...client/server model...downsizing
Pro rietar rotocol stack derived from
XNS...similarities to IPIPX uses 10-byte vs 4-byte (IP) addresses
Network Analysis: Foundation 1-44
e wor ore ro oco orconnection-oriented transport
-
8/3/2019 Foundation Section 1
45/95
Exam le Networks continuedExam le Networks continued
ARPANET
Funded b Advanced Research Pro ects A enc(ARPA) in early 60s as command/control network
Introduction of packet-switching (vs-
Hosts connected to subnet of IMPs (Interface Msg
ProcessorsIncredible growth
Led to invention of TCP/IP model in 1974 (Vinter o a n
Protocols integrated into Berkeley UNIX (by BBN)and rovided free with UNIX license...ex losive!
Network Analysis: Foundation 1-45
-
8/3/2019 Foundation Section 1
46/95
Designed by National Science Foundation as highspeedsuccessor to ARPANET for university access
rs connec e sx supercompu er cen ers: an ego,Boulder, Champaign, Pittsburgh, Ithaca, Princeton
First TCP/IP WANEventually 20 regional networks connected to backbone
In 1990 ANS (Advanced Networks and Services) took overand renamed ANSNET...45 mbps links & first step towards
commercializationIn 1995 ANSNET sold to AOL and regional networks wentto commercial service
Network Analysis: Foundation 1-46
-
8/3/2019 Foundation Section 1
47/95
In mid-80s this collection of IP-based networks" "
Growth exponential
Defn: Machine on Internet if runs TCP/IP, has IP@, and sends IP packets to other internet hosts
Internet Society founded in Jan 1992
-
millions of non-academic users to Internet in early90s (web pages, links, ubiguitous URLs)
Network Analysis: Foundation 1-47
-
8/3/2019 Foundation Section 1
48/95
X .25 NetworksX .25 Networks
A standard developed by CCITT (now ISO) in 1970s
Physical layer is X.21 - mostly analog RS-232 used instead
Network layer handles addressing, flow-control, delivery
User establishes a "virtual circuit" and sends max 128byte packets reliably and in order.
,
Flow control ensures fast sender does not swampreceiver
- .
is used (PAD)Terminal - X.28 - PAD - X.29 standards also defined.
Network Analysis: Foundation 1-48
.
-
8/3/2019 Foundation Section 1
49/95
Frame RelaFrame Rela
Also connection-oriented standaard for moving bitsgenerally across a public network.
Takes advantage of fact that leased lines are now fast,
digital, reliable --> simple protocols.
.
Frames can be up to 1600 bytes and carry a number (dlci)identifying the virtual circuit.
ontract w t carr er or an average serv ce
burst allowed as in SMDS
Generally operates at T1 (1.5mbps) or above
FR determines start and end of frame, detects sometransmission errors, discards bad frames.
Network Analysis: Foundation 1-49
.
-
8/3/2019 Foundation Section 1
50/95
BISDN Architecture - ATMBISDN Architecture - ATM
- envisioned for universal networking...
- integrated networking* voice, video, data, and image in the same
- scaleable in distance* LAN, MAN, WAN
- scaleable in bandwidth* 1.5 Mbps to several Gbps
Network Analysis: Foundation 1-50
-
8/3/2019 Foundation Section 1
51/95
MotivationsMotivations
Why connection oriented?- prov ng serv ce guaran ees requ re
resourcesto be reserved in the network
- simpler network management
Why fixed size cells?- efficient switching- hardware switching
Why small size cell?- mainly for voice
Network Analysis: Foundation 1-51
-
8/3/2019 Foundation Section 1
52/95
Connection-Oriented vsConnection-Oriented vsConnectionlessConnectionless
Connection-Oriented
Path created (fixed) from transmission site to
Intermediate nodes set aside resources for the
new connectionConnection may be allocated a given transmissionrate (r bps).
connection (if needed for connection type)If no path can be found having r bps on all links,
Network Analysis: Foundation 1-52
ca s reec e .
C ti lC ti l
-
8/3/2019 Foundation Section 1
53/95
ConnectionlessConnectionless
Session setup without reservingw w .
First-come, first-served and noper ormance guaran ees c angng now .
No call-admission decision. All usersaccep e connec e .
Packet waits in queue if needed to be
transm tte on next n .Advantage is that data can be sent
Network Analysis: Foundation 1-53
without any connection-setup protocols.
E x am p le P ro toc o l G rap h
-
8/3/2019 Foundation Section 1
54/95
E x am p le P ro toc o l G rap h
F T P H T T P V id eo T F T P
IP
A T MEtherne t O the r N e tArch
Network Analysis: Foundation 1-54
N ote : O ne a rch itec tu re m ayr ide on top o f an other .
-
8/3/2019 Foundation Section 1
55/95
Internet a s: a lication, trans ort rotocols
Application Underlying
e-mail
smtp [RFC 821]
TCP
Webfile transfer
streamin multimedia
http [RFC 2068]ftp [RFC 959]
ro rietar
TCPTCP
TCP or UDP
remote file serverInternet telephony
(e.g. RealNetworks)NFSproprietary
TCP or UDPtypically UDP
(e.g., Vocaltec)
Network Analysis: Foundation 1-55
-
8/3/2019 Foundation Section 1
56/95
oundationGoals:
Overview:
ay oun a on or
understanding how tobuild a network
Applications
Concepts & Terminology
Required services
Terminology
Network Architecture
Performance TCP/IP & OSI
Protocols and
Channel Multiplexing
Socket Interface Performance Metrics
Network Analysis: Foundation 1-56Network Analysis: Foundation 1-56
-
8/3/2019 Foundation Section 1
57/95
Per or ance bandwidtBandwidth . .
3000Hz) Bandwidth of a communication link means the
- - . .Ethernet is 100 million-bits-per-sec)
Throu h ut Usually implies achievable performance for the
data unit of interest (user data,packet,etc.)., , .
Depends on input rate to the channel Influenced by protocol and protocol data unit
Network Analysis: Foundation 1-57
over ea .
-
8/3/2019 Foundation Section 1
58/95
Per or ance dela
the start and end of an event of interest. Retrievin data from a disk Sending a frame on an ethernet link
Sending an IP datagram across the Internet.
Measured in time (e.g. 24 milliseconds tosend a packet from US east to west coast.)
May be interested in one-way or in RTT(round-trip-time).
Network Analysis: Foundation 1-58
L k D l T P
-
8/3/2019 Foundation Section 1
59/95
Link Dela = ueue+Transmit+Pro a ate time
ueue time is time a acket/bit waits tobegin transmission from a node
Transmit time
Propagation time
Size (bits)/Bandwidth (bits per sec)
Propagation speed
stance m, m, eet, m es ropagat on pee
8 sec3.33
in a cable in fiber
82.3 10 m/sec82 10 m/sec
m
( )sec4.35 kn
( )sec5 km
Network Analysis: Foundation 1-59
-
8/3/2019 Foundation Section 1
60/95
i le Per or ance xa leHow lon does it take to send a 1000 b te
frame over a 1000km 100 Mbps link fromthe time transmission begins to the timeframe is received (no queueing delay)?
Ans. Bandwidth should be bps so we mustconvert ytes to its. en we ivi e ybandwidth and add propagation delay.
bitsbyte 61000 bytes 8
ransm ss on me sPropagation time is
6 bitssec
sec sec.100 10
= =
33
8 meterssec
1000 10 meters4.348 10 sec=4.348 ms
2.3 10
=
ota time is . ms.
Network Analysis: Foundation 1-60
Problem
-
8/3/2019 Foundation Section 1
61/95
Problem
Calculate the latency (from first bit sent to last bit received) of the following:
10-Mbps Ethernet with a single store-and-forward switch in the path and a packet
size of 5,000 bits. Assume that each link introduces a propagation delay of 10 s
and that the switch begins retransmitting immediately after it has finished receivingthe packet.
10-Mbps
10x10-6 sec 10x10-6 sec
65,000 bits1. Transmit: 500 10 sec.=
6
6
6
bits10 10
sec2. Propagate last bit on first link 10 10 sec.
5,000 bits3. Transmit: 500 10 sec.
=
=
Total 1.02 ms.
=
Network Analysis: Foundation 1-61Network Analysis: Foundation 1-61
s10 10sec
4. Propagate last bit on second link 10 1
= 60 sec.
-
8/3/2019 Foundation Section 1
62/95
ProbleTwo nodes, A and B, are separated by 2000km and are connectedby a fiber 10 Mbps point-to-point link. Suppose that node A transmits
1,000 packets per second to node B and that each packet is 1,000 bytes
long. Also assume that each packet is delayed for 1 ms in node A.
. at s t e e ay t at eac pac et exper ences rom arr va at to
arrival at B?
.
The ratio of these two quantities determines link "utilization" usually
defined as:
, where is utilization, is throughput (bps) andc =
Network Analysis: Foundation 1-62
. .
-
8/3/2019 Foundation Section 1
63/95
olutionThe link delay is given by:
8
sec
8,000 2,0001 10 2.0 10 m
bits kmd qt tt pd ms Mbps= + + = + +
2 6
6 8
80 10 2 100.001sec sec sec 0.0118sec 11.8 .
10 10 2 10
ms
= + + = =
The bandwidth of the link is 10 .Mbps
Node A transmits 1000 pps with each packet 8,000 bits 8.0Mbps; thus,the throughput is 8Mbps. The utilization is clearly 0.8 (notice NO dimension).
Network Analysis: Foundation 1-63
-
8/3/2019 Foundation Section 1
64/95
at causes ueue dela at A
pointers from entry port to exit port onthe switch.
Some delays are possible due to the
communication protocol being used. Also, there may be a waiting line formingbecause the transmitter is busy at the
exact moment t at a pac et s rea y totransmit. (Well consider this later.)
Network Analysis: Foundation 1-64
Bit Length (previous example)
-
8/3/2019 Foundation Section 1
65/95
Bit Length (previous example)
Propagation Speed:
Note: One bit has length just as one packet does.
82.0 10 / secm
6Bandwidth:
8
6.BitLength 20
BandWidth 10 10meters
bitbps
= = =
2,000,000mThis implies that 100,000 bits can be20m/bit =
Network Analysis: Foundation 1-65
held or "stored" on this link at one time.
ela Bandwidt Product
-
8/3/2019 Foundation Section 1
66/95
ela -Bandwidt Product
,
length 20m fitting on the 2,000 km fiber.This can be directl com uted usin
( )
66
8
2 1010 10
metersdelay bandwidth bps
=
-100,000 .bits=
many bits sender must transmit beforefirst bit arrives at receiver.
Network Analysis: Foundation 1-66
Per or ance Ter inolo
-
8/3/2019 Foundation Section 1
67/95
Per or ance Ter inolo
B byte
6
b bit
MB and Mb mega-byte and mega-bit.The "mega" commonly means 10 for network bandwidth (Mbps).
20The "mega" commonly means 2 for computer file sizes.
KB and Kb kilo-b3
yte and kilo-bit
The "kilo" commonly means 10 for network bandwidth (Kbps).
10
3
The "kilo" commonly means 2 for computer file sizes.
BUT in this class we will always use 10 for kilo an 6d 10 for mega. It makes arithmetic easier.
Network Analysis: Foundation 1-67
Per or ance Ter continued
-
8/3/2019 Foundation Section 1
68/95
Per or ance Ter continued
round-trip time and equals 2 times total one-way delay (latency).RTT
Latency means delay and, in this class, we will always specify delay of something in particular.
for example, latency between first bit sent and last bit received for a file transfer.
Throughput refers to the rate at which data (bits) in which we are interested move from sender
to receiver. We may be interested in all bits. We may be interested only in data bits (minus headers).
We ma or ma not enalize throu h ut for retransmissions in case of errors. Such conditions mustbe specified in any given problem. (Or must be clear because no mention is made of headers or
retransmisions...)
Network Analysis: Foundation 1-68
File Transfer and the Train Model
-
8/3/2019 Foundation Section 1
69/95
File Transfer and the Train Model
Suppose that a file is to be transferred from A to B over a km fiber link of bps. The
total size of the file is bytes. HOWEVER, the file cannot be transmitted in a single packet;it must be di
d bw
fsvided into packet that have a maximum size of bytes. How long does it take tops
transfer the entire file? (Here we have no concerns about errors in transmission.)
Example: Suppose a file is to be transferred over a 3000 km link of 155 Mbps. File size
.
Network Analysis: Foundation 1-69
Train Model Solution
-
8/3/2019 Foundation Section 1
70/95
Train Model Solution
A Bn begin1
12n + 1 transfer time
n 2 1 + 1 prop delay
First packet arrives after transfer time + propagation delay (1st train car).
1 packets (cars) remain and one will arrive for each new interval of transfer time.
TOTAL transfer time will be one propag
n
ation delay plus ( ).n transfertime
Network Analysis: Foundation 1-70
ile Trans er or ula
-
8/3/2019 Foundation Section 1
71/95
ile Trans er or ula
File transfer time where:tf pd n tt = +
number of packetsfs
nps
=
bits
(bytes) 8byte
transfer time
ps
tt
=
sec
m
bw
8kmpropagation delay m
2 10pd =
Network Analysis: Foundation 1-71
ile Trans er xa le
-
8/3/2019 Foundation Section 1
72/95
ile Trans er xa leWe were given a link length (distance) of 3000 km, a bandwidth of 155 Mbps, a file size
6
.
Total file transfer time is as follows:
100 10 b tes
1500 byten = , 7 pkts
s
bits1500 bytes 8
byte
=
= =6
6
. .bits155 10
sec
3 10 meters15 ms.
meterspd
= =
sec
66,667 0.077 15 5.148 seconds.tf
= + =
Network Analysis: Foundation 1-72
oundation
-
8/3/2019 Foundation Section 1
73/95
oundation
Goals:
Overview:ay oun a on or
understanding how tobuild a network
Applications
Concepts & Terminology
Required services
Terminology
Network Architecture
Performance TCP/IP & OSI
Protocols and
Channel Multiplexing
Socket Interface
Performance Metrics
Network Analysis: Foundation 1-73Network Analysis: Foundation 1-73Network Analysis: Foundation 1-73
Abstract Com m unication Channel
-
8/3/2019 Foundation Section 1
74/95
Server
Client
Network Analysis: Foundation 1-74
ulti le Access rotocols
-
8/3/2019 Foundation Section 1
75/95
ulti le Access rotocols
single channel shared by multiple nodes (two or more)
on y one no e can en ucce u y a a me
multiple access protocol: distributed al orithm that determines how stations share
channel, i.e., determine when station can transmit communication about channel sharing must use channel itself!
what to look for in multiple access protocols: synchronous or asynchronous information needed about other stations robustness e. ., to channel errors
performance
Network Analysis: Foundation 1-75
Multi le Access Protocols: a taxonom
-
8/3/2019 Foundation Section 1
76/95
Three broad classes:
divide channel into smaller pieces (time slots,
frequency)
a oca e p ece o no e or exc us ve use
Random Access
recover from collisions
Takin turns
tightly coordinate shared access to avoid collisions
Network Analysis: Foundation 1-76
oa : e c en , a r, s mp e, ecen ra ze
Channel Partitionin TDMA
-
8/3/2019 Foundation Section 1
77/95
access to channel in "rounds" each station gets fixed length slot (length = pkt trans
time) in each round unused slots go idle example: 6-station LAN, 1,3,4 have pkt, slots 2,5,6 idle TDM (Time Division Multiplexing): channel divided into
,
cycle users and at light load. FDM (Frequency Division Multiplexing): frequencysubdivided.
Network Analysis: Foundation 1-77
Channel Partitionin FDMA
-
8/3/2019 Foundation Section 1
78/95
FDMA: frequency division multiple access
each station assigned fixed frequency band
unused transmission time in frequency bands goe
example: 6-station LAN, 1,3,4 have pkt,frequency bands 2,5,6 idle
cy
bands
frequ
en
Network Analysis: Foundation 1-78
Rando Access rotocols
-
8/3/2019 Foundation Section 1
79/95
When node has acket to send transmit at full channel data rate R.
no a prioricoordination among nodes
wo or more rasnm ng no es -> co s on ,
random access MAC protocol specifies:
how to detect collisions how to recover from collisions (e.g., via delayed
retransmissions)
slotted ALOHA ALOHA
Network Analysis: Foundation 1-79
CSMA and CSMA/CD
lotted Alo a
-
8/3/2019 Foundation Section 1
80/95
time is divided into e ual size slots = kt trans. time
node with new arriving pkt: transmit at beginning ofnext slot
if collision: retransmit pkt in future slots withprobability p, until successful.
Network Analysis: Foundation 1-80
Success (S), Collision (C), Empty (E) slots
What channel service does an a need?
-
8/3/2019 Foundation Section 1
81/95
Data loss
Bandwidth. .,
tolerate some loss other apps (e.g., file
some apps (e.g.,
multimedia) requireminimum amount otrans er, te net require100% reliable data
transfer
bandwidth to beeffective
Timing some apps (e.g.,
o er apps e as capps) make use ofwhatever bandwidth
,
interactive games)require low delay to be
they get
Network Analysis: Foundation 1-81
e ec ve
-
8/3/2019 Foundation Section 1
82/95
file transfer-
no loss elastic
no
Web documentsreal-time audio/video
loss-tolerantloss-tolerant
elasticaudio: 5Kb-1Mb
video:10Kb-5Mb
noyes, 100s msec
stored audio/videointeractive games
financial apps
loss-tolerantloss-tolerantno loss
same as abovefew Kbps upelastic
yes, few secsyes, 100s msecyes and no
Network Analysis: Foundation 1-82
Co on ailures
-
8/3/2019 Foundation Section 1
83/95
Burst error
Link failure
Network Analysis: Foundation 1-83
ailure xa le:
-
8/3/2019 Foundation Section 1
84/95
Suppose that two nodes, A and B, are connected by a communication link and
.
the probability of an error in the packet is .e In this case, transmission fails
and the packet must be retransmitted. What is the expected number of transmissions
per packet?
Let 1 2 ... to re resent the number of the first successful transmissiX = on.
[ ] [ ]
(What do we call ?) What is the probability that 1? (Write this as
1 .) What is 2 ? (Recall the idea of independent events.)
X X
P X P X
=
= =
[ ]What is , for any positive integer ?
: Return to thi
P X k k
NOTE
=
s after review of introductory probability.
Network Analysis: Foundation 1-84
olution
-
8/3/2019 Foundation Section 1
85/95
( ) ( )1The random variable has a geometric distribution and 1 ,
for 1,2,
k
X X p k e e
k
=
=
( )1 21
1 1The expected number of transmissions is 1 .
11
k
k
eke e
ee
=
= =
Network Analysis: Foundation 1-85
Expected Number of Hops in Linear Network
Suppose that the nodes 1,2, , are connect in a straight line asn
-
8/3/2019 Foundation Section 1
86/95
1 2 3 1 .
Also suppose that a randomly chosen packet is equally likely to
n n
belong to the communication of any of the possible pairs.
What is the expected number of hops for each packet transmitted?
To begin with we consider the case of 3 nodes (2 nodes is trivial).
( )
We define the random variable for 1,2 if a random
packet travels hops from source to destination.
H k k
k
= =
Ther
( ) ( ) ( )
e are 3 ways to choose two nodes (source & destination) for
communication - 1,2 , 1,3 , 2,3 . These give us two routes that
are 1 hop 1 2, 2 3 and one route that is two hops 1 3 .
Because a random packet is eq
( ) ( )
ually likely to be traveling any of
2 1the 3 routes, we have 1 and 2 .
3 3 p H p H = = = =
Network Analysis: Foundation1-86
( )Answer: 1 2 .3 3 3
E H = + =i i
E(hops) in a Linear Network General Case
In general there are routes of length for 1,2,..., 1. (HW: proven k k k n =
-
8/3/2019 Foundation Section 1
87/95
this assertion by induction on the number of nodes 2.) We can check
this quickly by noting that
n
1 1 1n n n
number of routes of length( ) ( )1 1 1
. The2
last expression equals , which is the total ways to pick pairs from nodes.2
k k k
k n k k
n n
= = =
= = =
From this it follows that the probability that a random packet is on a route
( )( )
( )( )
of
2length is .
1 1
n kn kk p H k
n n n n
= = =
2
( ) ( )1
1
We can now find the expected number of hops asn
k
E H k p H k
=
= = i
( )
( ) ( ) ( ) ( ) ( )( ) ( ) ( )
1 1 1 12
1 1 1 1
2 2 2 2
1 1 1 1
1 1 2 12 2 2 1 1
n n n n
k k k k
n k nk k n k k k
n n n n n n n n
n n n n nn n n
= = = =
= = =
+
i
Network Analysis: Foundation1-87
( ) ( ).
1 2 1 6 3 3n n n n
Multi lexin exam le continues
-
8/3/2019 Foundation Section 1
88/95
place of node A and are sharing the10Mbps link to B. Actual traffic is 8 Mbps.
A2
A10
Network Analysis: Foundation1-88
Recall TDMA and FDMA
-
8/3/2019 Foundation Section 1
89/95
FDMAExample:
timeTDMA
frequency
Network Analysis: Foundation 1-89time
Consider node A1
-
8/3/2019 Foundation Section 1
90/95
-
node A1 is assigned the first time slot from each second. If incoming
traffic is evenl distributed amon all in ut nodes, then each
node will use 80% of its assigned 1 Mbps channel and total
channel utilization will remain at 0.8.
If all traffic is originating at node A1, then no more than
1 Mbps of total traffic can be sent to B even though link
utilization would only be 0.08.
Network Analysis: Foundation 1-90
Recall lotted Alo a
-
8/3/2019 Foundation Section 1
91/95
time is divided into e ual size slots = kt trans. time
node with new arriving pkt: transmit at beginning of
next slot if collision: retransmit pkt in future slots with
probability p, until successful.
Network Analysis: Foundation 1-91
Success (S), Collision (C), Empty (E) slots
Slotted Aloha Throu h ut Anal sis
-
8/3/2019 Foundation Section 1
92/95
Recall throughput implies the number of packets per unit time
that successfully cross the network. To make tractable, we
assume that each workstartion transmits the same length packet" "every me an we a e e s o me o e equa o pac e
transmission time. We also take this to be our "unit time."
of all arrivals at these stations has a Poisson distribution with
mean arrival rate of per unit time (or slot-time length). We
make the simplifying assumption that the sum of all arrivals plusretransmissions (due to "collisions") has a Poisson distribution
Network Analysis: Foundation 1-92
with mean arrival rate of per unit time.
lotted Alo a Continues
Suppose any terminal begins transmitting a packet What is the
-
8/3/2019 Foundation Section 1
93/95
Suppose any terminal begins transmitting a packet. What is the
probability that the packet transmits successfully? In slotted Aloha
success occurs if no other terminal got a packet ready for transmission
during the previous slot, that is, if there are no other arrivals
during unit time. Let be a random variable (RV) that gives
the number of arrivals plus retransmissions in unit time. has
X
X
[ ]k
,
= . The probability of no "other" arrivals during!
eP X k
k
=
[ ]the slot prior to our given transmission is 0 = . Because
the rate of transmission attempts is p
P X e
=
er unit time and the probability
Network Analysis: Foundation 1-93
of success (for a given attempt) is , then the throughput must
be .
e
e
ax rouput n ure o aax roupu n ure o a
-
8/3/2019 Foundation Section 1
94/95
ax rouput n ure o aax roupu n ure o a
Network Analysis: Foundation 1-94
From Tanenbaum Com uter NetworksA large population of ALOHA users manages to generate 50 requests/sec
-
8/3/2019 Foundation Section 1
95/95
A large population of ALOHA users manages to generate 50 requests/sec
(including orginals plus retransmissions). Time is slotted in units of 40 ms.
(a) What is the probability of success in the first attempt?
(b) What is the probability of exactly collisions and then a success?k
1000For a : There are 25 slots er second. The load is 2 frames/slot.=
40
Success o 2
2 2
ccurs if no other transmission so that prob of success is .
k
s e
=
=
2
For (c): The throughput is 2e 0.27 frames per slot (assuming slottedALOHA).
=
Network Analysis: Foundation 1-95