E-Seminar - Ciscoupstream and downstream connection speeds. Finally, Ethernet to the Home, Building...
Transcript of E-Seminar - Ciscoupstream and downstream connection speeds. Finally, Ethernet to the Home, Building...

E-S
emin
ar
Remote Access
Internet Technology SolutionSeminar

3 Welcome
4 Objectives
5 Todays Business Applications
6 Defined
7 Remote Access Uses
8 Requirements
9 Comparison
10 Architecture
11 Components
12 Conclusion
Remote Access
Internet Technology SolutionSeminar

3 of 12
Welcome to the Technology E-seminar on Remote Access technologies
In today’s networked economy, many companies want to give their
employees, customers or partners, remote access to a part or all of their
network. This way, authorised users can access the internal company
resources and use various business applications.
To support these requirements, Remote Access Technologies are available, in
a variety of ways.
Remote Access Seminar
Welcome

4 of 12
In this seminar, we will discuss the technical aspects of the different Remote
Access solutions
At the end of the seminar, you will have a good understanding about what
exactly Remote Access is about, and which business processes and solutions
can benefit from this technology
You will also learn which Remote Access Solutions exist and how they are
compared to each other
Finally, we will discuss the technical requirements of implementing Remote
Access Solutions at your company
Remote Access Seminar
Objectives

5 of 12
Companies today automate more and more of their business applications
and processes. These business solutions, such as E-Commerce, Supply
Chain Management and E-Procurement, enable companies to stay
competitive, to increase their productivity, and to reduce their costs.
Many of these business applications are first created and implemented for
the company’s Intranet. However, also external users, such as customers,
mobile employees, partners and suppliers, may need to have access to these
applications from outside the company Intranet. With today’s Internet-
based Business Solutions, remote access has become a crucial business
requirement.
Remote Access Seminar
Todays business applications

6 of 12
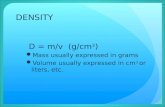
So what do we understand by Remote Access?
Remote Access refers to any technology that enables a company to connect
users in locations which are geographically dispersed. It usually is a simple
connection, between an individual user, or a very small branch office, and a
central network.
There are different types of Remote Access technologies
Traditionally, remote access was mostly accomplished by analog Dial-up
connections, using modem technology
A digital an slightly faster way of access is obtained through ISDN, standing
for Integrated Service Digital Network
Recently, broadband access technologies, such as Cable and DSL have
emerged, bringing high-speed network access to the remote user. DSL, or
Digital Subscriber Line, is commonly available in its ADSL form:
Asymmetric Digital Subscriber Line. "Asymmetric" refers to different
upstream and downstream connection speeds.
Finally, Ethernet to the Home, Building or Business, generally abbreviated as
ETTx, brings Ethernet connectivity, over fibre, to residential users and small
business offices located in apartment blocks, multi-tenanted business
buildings and hotels.
Remote Access Seminar
Defined

7 of 12
Remote access technologies allow companies to enable their employees to
telework for a part or all of their time, while giving them similar network
access as in the office
External users such as customers or preferred partners, could be given
access to certain company databases or special applications, for instance for
commercial interactions.
For companies who have small branch offices, with local networks which
should be connected to the main office, the high-bandwidth access methods
of DSL, Cable and Ethernet-to-the-Home could be interesting. These
methods allow voice, video and other critical applications to be run between
the different sites within the network.
Remote Access Seminar
Remote Access Uses

8 of 12
The requirements of a remote access solution for a company may vary,
depending on the size of the remote office as well as the application
requirements and performance expectations of their users.
First, connectivity is key: easy connections and consistency are crucial to
companies relying on remote access. Customers, employees and partners
should connect seamlessly, as if they are in company headquarters.
Secondly, the remote connection should be reliable: users count on the
ability to log in and to remain connected at an expected level of
performance.
As companies and users discover the flexibility of remote access, security
becomes a higher priority. A security solution usually consists of a
combination of hardware solutions such as Firewalls, and software solutions
such as access control lists, passwords, and Triple A: Authentication,
Authorization, and Accounting methods. Please refer to the Technology E-
Seminar on Network Security for more details about these technologies.
Finally, a company has to make a decision on bandwidth requirements for
remote users and offices, depending on the business applications that are
used over these connections.
Remote Access Seminar
Requirements

9 of 12
Let’s make a quick comparison of the most common remote access
technologies available today.
The traditional analog dial-up connection is available everywhere you have
a phone connection. At present, the fastest analog modems operate at 56
kilo-bits-per-second. This technology is cheap for limited use, but slow
compared to other technologies.
An ISDN line costs slightly more than a regular telephone line, and offers a
digital connection at a speed up to 128 kilo-bits-per-second. With ISDN,
remote connections are made more quickly, and the service is more reliable
than analog connections. Furthermore, ISDN usually allows phone, fax or
data traffic to happen simultaneously.
ADSL and Cable technologies offer theoretical speeds up to 10 mega-bits-
per-second. These speeds vary in upstream and downstream directions –
downstream is from the remote network to the user, upstream from the user
to the remote network. The actual bandwidth available depends on your
local Service Provider.
ADSL uses the existing public telephone network, but does not interfere
with phone communications. "Cable" makes use of the existing cable TV
infrastructure, and may therefore not be available everywhere.
Ethernet-to-the-Home, finally, is increasingly offered by Service Providers in
metropolitan areas. It delivers Ethernet LAN speed in both directions, at 10
to 100 Megabits-per-second.
Remote Access Seminar
Comparison

10 of 12
So how does Remote Access work? Depending on the technology, a remote
access connection is established as follows.
In the case of analog dial-up, a user connects from his remote location to
the central office network using the Public Switched Telephone Network, or
PSTN. This connection can either be established directly from the user’s
computer, or through a router with dial-up capabilities.
Similarly, in the case of ISDN or a DSL, a router, usually with firewall
technology, is connected to the PSTN, or to a backbone network of a
Service Provider, which delivers a secure and private connection to the
central office network, for instance through the use of VPN technology.
The connection of the remote office to the central office could also happen
over the public Internet, in which case use of appropriate security
technologies will be required.
In the case of Cable, the cable router has an "always-on" connection
through the Cable network of the Cable Service Provider.
With Ethernet-to-the-home, such "always-on" link happens over a fibre
optics network. Again, in the case of permanent connections, VPN and
security technologies can guarantee secure and private connectivity.
At the central office, incoming connections are handled by either access
servers, firewalls and routers, depending on the remote access technology
used.
Remote Access Seminar
Architecture

11 of 12
Let’s zoom in to the individual components of a remote access solution.
In case a small local network exists at the remote office, use of a local
router is recommended, as it separates the local LAN from the remote
network and keeps local network traffic local. It uses the remote
connection only when requested, and usually contains firewall or VPN
software, to allow for secure remote connections.
For the company headquarters site, a variety of routers and switches exists
today, to be able to handle any type of access mechanism, whether it
involves ISDN, DSL, Cable, Ethernet or optical technologies.
In the case of dial-up connections, Access Servers are used to concentrate
dial connections coming in from the different remote users. An Access
Server receives the incoming connection from each user that wants access to
the network, verifies its username and password, and performs the necessary
steps to authenticate and authorise each user.
When remote users use permanent connections, such as DSL, cable or
Ethernet-to-the-home, user authentication and authorisation will be handled
by a separate management system.
Finally, security solutions, such as a separate hardware Firewall, are
available to protect the company from intruders and unwanted traffic on
the internal network.
Remote Access Seminar
Components

12 of 12
To summarise: Internet-based business applications have made remote access
to an essential business requirement.
A variety of remote access solutions is available to every company,
depending on its specific needs with respect to bandwidth, reliability, and
ease-of-use. Several remote access technologies are available at different
performance and cost levels.
In any remote access scenario, network security can be guaranteed through
the use of VPN and firewall technologies.
Remote Access Seminar
Conclusions