What Should I Look For in a Church?: Compassion that’s ...… · April)5)&6,2014))))) ...
CONTROL SYSTEMS AND CYBER SECURITY 2600 MEETING JUNE 6,2014 MICHAEL TOECKER Mikhail Turcher, big...
-
Upload
mavis-eaton -
Category
Documents
-
view
213 -
download
1
Transcript of CONTROL SYSTEMS AND CYBER SECURITY 2600 MEETING JUNE 6,2014 MICHAEL TOECKER Mikhail Turcher, big...

CONTROL SYSTEMSAND CYBER SECURITY
2600 MEETING JUNE 6,2014M I C H A E L T O E C K E R
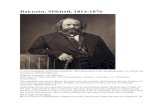
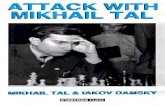
Mikhail Turcher, big fanci pantsie

CYBER
SECURITY
OVERVIEW
MO
DU
L E 1
Ooooh… Cybah Cybah Cybah Overfuncher!

BASICS
Control Systems are computing systems that monitor and control physical processes
We’re talking powerplants, locomotives, water treatment, building operations, and stuff like that
Uses things called Programmable Logic Controllers, Remote Terminal Units take in signals from things like pumps, valves, motors, etc
Basi….. Sknnnnzzzz….

Electro-Mechanical Logic
Pneumatic Logic
Programmable Logic
Distributed ControlSystem
Evolution of Control Systems
Dis presentation needs more goats

HUMAN INTERACTIONTHEN AND NOW
Buttons, Levers, Paper Trend Plotters, Annunciators, all linked to Relays and Actuators through
Electronic or Pneumatic Communications utilizing
Relay/Ladder Logic
Computer Systems and Displays, linked to Digital
Process Controllers through High Speed Ethernet Based
networks utilizing Field Programmable Gate Array and
Function Block Logic
I tells him to Pressy the butensies!! Press them!!! He does not.

CYBER SECURITY
The problem is, use of normal IT stuff has caused Control Systems to inherit the same vulnerabilities of those IT systems…
Ever been hacked? How did that affect your computer? Other computers you own?
Imagine being the computer that runs the Chemical Plant down the road.
I be doin the hackring.. Hackring and slashring in Skyrim… MY KNEE!!

BUT…
.
Computation evolved into Networked systems
Prioritized the fast, efficient, and easy sharing of data
Control Systems and Information Systems were easily connected together, up to and including the Internet
Vulnerabilities in these Systems allows Malicious Individuals to Access and Disrupt operations
Coding Practices assumed good behavior, but did not enforce it.
Networked Systems allowed access from remote locations, or over the Internet
The
Intr
oduct
ion o
f Com
puters
als
o Bro
ught the
Vulner
abili
ty o
f the
Info
rmat
ion A
ge
Heh. Goatsies.

WE A
POLO
GIZE F
OR THE
FAULT
IN T
HE SUBTI
TLES..
T HO
S E RE S P O
NS I B
L E HAV
E BE E N
SA
CK E D

NOTABLE
CYB
ER EVEN
TS
Government Developed Computer Virus
Designed to disrupt the Iranian nuclear enrichment process at Natanz
Three Modes of Operation Windows Based, designed to infect
Windows systems Siemens Simatic, designed to subvert
communications between the PLC and Simatic Applications
Siemens S7 PLC Based, designed to run equipment outside of operating envelope, and conceal operating parameters from operators.
Stuxn
et is
the
Prime
Exam
ple o
f a C
yber
Sec
urity
issu
e
affec
ting C
ontr
ol S
yste
ms

TARGETED IRAN’S NATANZENRICHMENT FACILITY
Control Systems
Mahmoud Ahmadinejad

INFECTED PLCS BROKE CENTRIFUGES
This Runs These
Also Mahmoud Ahmadinejad

STUXNET’S GOAL
Reduce the capability of the Iranian Government to produce Nuclear materials
It Damaged Systems It reduced quality of the product Destroyed Centrifuges
Hid itself from the operators
Personally, I have great sympathy for the Iranian Engineers…. I’d hate to have to go to my boss, repeatedly, and tell him my system
was f*cked up, not matter what I was doing to fix it.
This is Enriched Uranium

DANCING MONKEYS….
Super Secret Easter Egg in Siemens PLCs, Used at Natanz
found
by Dillon Beresford

DIGITAL BOND’S PROJECT BASECAMP
Intended to focus attention on vulnerabilities in control system devices, to get vendors to change how insecure their devices actually were.
Full Disclosure: I work for Digital Bond

THREATPOST, 2011
Hacker pr0f gained access to, and posted pictures of the South Houston water Treatment plant.

CONCLUSIONS
Control Systems run Industrial Stuff
They use normal IT components
They don’t spend much time on security, if any
Governments have used control systems to do bad things to other governments
You can find these things on the Internet
…. Bad guys can exploit this stuff over the internet.