COEN 350 Network Security Introduction. Computer Networks OSI Reference Model Application Layer...
-
Upload
isaac-ford -
Category
Documents
-
view
213 -
download
0
Transcript of COEN 350 Network Security Introduction. Computer Networks OSI Reference Model Application Layer...

COEN 350 Network Security
Introduction

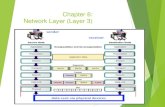
Computer Networks OSI Reference Model
Application Layer Presentation Layer Session Layer Transport Layer Network Layer Data Link Layer Physical Layer

OSI Reference Model
Useful to establish terminology Not implemented Upper layer implemented in terms
of lower layer.

OSI Reference Model Application Layer
Locus of applications that use networking P2P HTTP ftp
Presentation Layer Encodes application data into a canonical
form Decodes it into system-dependent format at
the receiving end.

OSI Reference Model
Session Layer Extra functions over reliable one-to-
one connection RPC
Transport Layer Reliable communication stream
between a pair of systems. IP, UDP, TCP, ICMP

OSI Reference Model
Network Layer Computes paths across an
interconnected mesh of links and packet switches
Forwards packets over multiple links from source to destination

OSI Reference Model
Data Link Layer Organizes physical layer’s bits into
packets and controls who on a shared link gets each packet.
Physical Layer Delivers an unstructured stream of
bits across a single link of some sort.

TCP/IP Suite

Protocol Layers and Security
Security measures often layer network protocols. Protect contents of packages is
protection at layer 2. Still allows traffic analysis.
IPSec protects (encrypts) packages at layer 4
Does not work with NAT.

Goals Authentication
Who are you? Authorization
Are you allowed to do that? Integrity
Is this the real message? Privacy
Does anyone else know about it?

Zone of Control The zone that needs to be secured in order to prevent
eavesdropping. Physical access needs to be prevented.
Tempest program (US military) All computer systems radiate information.
Possible to reconstruct image on a monitor from 20 ft. Wireless access point rated for e.g. 50 ft radius for receiving
data. Special antenna (built from a Pringles box, etc.) can read
traffic from a mile away. Define a perimeter of a commercial wired network:
Need to include backdoor channels like modems, etc. Tempest: Set of standards for limiting electric or
electromagnetic radiation emanations from electronic equipment.
Shortcut for filed of compromising emanations / Emissions Security

Legal Issues Patent Law
First inventor has the right to invention. In other countries: First one to file.
Patents issued based on what inventors present regarding
Novelty ( Prior Art) Importance (“Aha” effect)
Patent process flawed since Reagan under-funding, but slowly getting better
Patent decision needs to be made within a day. Many cryptography algorithms are / were patented.
Are now moving into the public domain. Still, many standards are built around patented methods.
Kerberos uses secret key encryption instead of public key encryption.

Legal Issues Export Control
Cryptographic algorithms and tools were considered to be restricted technology.
Treated like ammunition. Taking a laptop to Mexico for a week-end could be a
violation of export control. Government gave up after PGP fiasco
Zimmermann invented PGP 1.0 in 1991. PGP fell under the ammunition clause. Zimmermann circumvented export restriction by
publishing code in book form (under first amendment protection)
Book was intended to be bought by exactly one person in Norway to scan in code and publish PGP outside of US (for free downloads).

Legal Issues Key Escrow
Cryptography algorithms became unbreakable in the nineties.
Prevent wiretaps, computer forensics, etc. National security efforts sponsored Clipper:
1993 Encryption chip with secret key. User gets chip, secret key is broken up and stored at
two different agencies. Two different agencies needed to cooperate to recover
secret key. Considered to be almost impossible if cooperation were
legal and impossible if cooperation were illegal. Government gave up.