Audit 101 2 Days Dec 2015 GoldSRD · Snapple Group • Former CAE - Tyler Technologies •...
Transcript of Audit 101 2 Days Dec 2015 GoldSRD · Snapple Group • Former CAE - Tyler Technologies •...

(C) GoldCal LLC 2015 1
AUDIT 101: BEGINNER AUDITOR TRAINING
Danny M. Goldberg, Founder
INTRODUCTION
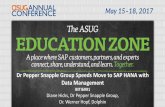
Danny M. Goldberg • Founder, GOLDSRD
(www.goldsrd.com) • Former Director of Corporate
Audit/SOX at Dr Pepper Snapple Group
• Former CAE - Tyler Technologies • Published Author (Book/
Articles) • Texas A&M University – 97/98
• Chairman of the Leadership Council of the American Lung Association - North Texas – Calendar Year 2012
• Served on the Audit Committee of the Dallas Independent School District (CY 2008)
• Current Dallas and Fort Worth IIA Programs Co-Chair
• Fort Worth IIA Board Member • IIA North America Learning
Committee Member Certifications: • CPA – Since 2000 • CIA – Since 2008 • CISA – Since 2008 • CGEIT - Since 2009 • CRISC - Since 2011 • CRMA – Since 2011 • CCSA – Since 2007 • CGMA – Since 2012

(C) GoldCal LLC 2015 2
Danny M. Goldberg • Highly-Rated, Internationally Recognized Speaker
– Asked to Speak @ 2015 IIA All-Star Conference (October, 2015) – One of the Top Rated Sessions, 2015 GAM Conference – 8th Rated Speaker, 2015 MISTI AuditWorld – 10th Rated Speaker, 2015 ISACA CACS – One of the Top Rated Speakers, 2014 IIA All-Star Conference – 7th Rated Speaker, 2014 ISACA ISRM Conference – One of the Top Rated Speakers, 2014 IIA Mid-Atlantic
Conference – 3rd Rated Speaker, 2014 ISACA CACS – One of the Top Rated Speakers, 2014 IIA Gaming Conference – 6th Highest Rated Speaker (out of 116), 2013 IIA International
Conference – 3rd and 5th Rated Sessions, 2013 IIA Central Regional
Conference – 8th Rated Speaker (out of 120), 2012 IIA International
Conference
People-Centric Skills • Added to IIA and ISACA Bookstores, Summer 2015 • Published August 2014 (Wiley Publications) • Coauthored with Manny Rosenfeld
– Chief Audit Executive with four global F500 Cos. and a global Financial Services organization.
• First book specific to internal audit communications and personal interactions
• This is not a reference book! – Story book format – Character development – Fictional Internal Audit Department – Fictional Professional Coach/Trainer – Situational
GoldSRD Snapshot
Staff Augmentation:
§ Market leader in locating cost-effective, recognized resources in accounting, finance, audit and IT
§ All requests filled within 72 hours
Professional Development:
§ Nationally-Recognized Leader in Audit and People-Centric Skill Training
§ Over 100 Full-Day Courses on Audit, Accounting, Finance and People-Centric Skills
§ Registered with NASBA to offer CPE’s for all courses in course catalog
§ Competitive Pricing
§ Interactive and Educational Courses for all levels
Executive Recruiting:
§ Unique approach to filling positions, including personality assessment for candidate and organization
§ Expansive network of qualified candidates actively looking

(C) GoldCal LLC 2015 3
PPT Business Card Danny M. Goldberg Founder – GoldSRD [email protected] P: (214) 514-8883
www.linkedin.com/in/dannymgoldberg
https://twitter.com/DannyMGoldberg
Course Overview I. Introduction and
Background II. Overview of Internal Audit
Guidance III. Internal Audit Annual
Planning IV. Internal Audit Process
a. Planning b. Fieldwork c. Reporting
V. Control Best Practices
VI. Fraud Overview and Fraud Red Flags
VII. Sampling Methodologies and Overview of Application
VIII. Internal Audit Wrap-Up IX. Flowcharting X. Crucial Communication/
The Role of Internal Audit XI. Interview Techniques XII. Future Steps and Hurdles
Let’s Set Up Our Teams • Introduce Yourselves to Your
Team – Interesting Fact – Specific Area of Interest in this
Course • Create a Team Name • Complete Your Name Tent &
– Put your High School/College Nickname on the Reverse side

(C) GoldCal LLC 2015 4
INTRODUCTION, OVERVIEW AND BACKGROUND
Discussion – What is the Goal of Internal Auditing?
Definition of Internal Auditing (Red Book) • Internal Auditing is an independent,
objective assurance and consulting activity designed to add value and improve an organization’s operations. It helps an organization accomplish its objectives by bringing a systematic, disciplined approach to evaluate and improve the effectiveness of risk management, control, and governance process

(C) GoldCal LLC 2015 5
Auditor Guidance? • International Professional Practice
Framework (“IPPF”) • Governmental Auditing Standards (“Yellow
Book”) • Generally Accepted Auditing Standards
(AICPA/ASB/PCAOB) • State Requirements (varies) • Major differences between standards are
minimal
The Institute of Internal Auditors • Formed in 1941 • Headquartered in Altamonte Springs, Florida • 130,000 members worldwide and growing • Sets standards for practicing internal audit
(IPPF) • Conferences • Research • Guidance is somewhat “loose”
IIA IPPF • Definition • Code of Ethics • Standards (attribute,
performance, implementation)
• Position Papers • Practice Advisories • Practice Guides

(C) GoldCal LLC 2015 6
Assurance Services • Assurance services involved the
internal auditor’s objective assessment of evidence to provide an independent opinion or conclusions regarding a process, system, or other subject matter. The nature and scope of the assurance engagement are determined by the internal auditor
Consulting Services • Consulting services are advisory in
nature, and are generally performed at the specific request of an engagement client. The nature and scope of the consulting engagement are subject to agreement with the engagement client.
Code of Ethics • Integrity • Objectivity • Confidentiality • Competency

(C) GoldCal LLC 2015 7
Standards • Attribute Standards (1000 series) – address
the characteristics of organizations and individuals performing IA services
• Performance Standards (2000 series) – describe the nature of internal audit activities and provide quality criteria against which the performance can be measured.
• Implementation Standards – under Attribute and Performance Standards that apply to specific engagements.
Attribute Standards • 1000 – Purpose, Authority, Responsibility • 1100 – Independence and Objectivity • 1200 – Proficiency and Due
Professional Care • 1300 – Quality Assurance and
Improvement
Performance Standards • 2000 – Managing the Internal Audit Activity • 2100 – Nature of Work • 2200 – Engagement Planning • 2300 – Performing the Engagement • 2400 – Communicating the Results • 2500 – Monitoring Progress • 2600 – Resolution of Management’s
Acceptance of Risks

(C) GoldCal LLC 2015 8
Definition Elements
Practice Guides
Practice Advisories
Position Papers
International Standards
Code of Ethics
Definition
for conducting internal audit activities. Includes detailed , such as tools and techniques, programs, and step-by-step approaches, including examples of deliverables.
Address and considerations, but NOT detailed processes and procedures. Concise and timely guidance to assist internal auditors in applying Code of Ethics and Standards and promoting good practices. Includes practices relating to: international, country, or industry specific issues; specific types of engagements; and legal or regulatory issues.
IIA statement to assist a wide range of interested parties, including those not in internal auditing profession, in understanding governance, risk or control issues and delineating related
.
Mandatory requirements consisting of: • Statements of basic requirements for professional practice of internal auditing and for evaluating
the effectiveness of its performance, which are internationally applicable at organizational and individual levels. -focused and provide a framework for performing and promoting internal auditing. Includes Attribute, Performance and Implementation .
, which clarify terms or concepts within the Statements.
Consider both Statements and Interpretations to understand and apply correctly.
Statement of principles and expectations governing behavior of individuals and organizations in the conduct of internal auditing. Description of minimum requirements for conduct. Describes
rather than specific activities.
Statement of purpose, nature, and scope of internal auditing.
Definition of Internal Auditing • Internal auditing is an independent,
objective assurance and consulting activity designed to add value and improve an organization's operations.
• It helps an organization accomplish its objectives by bringing a systematic, disciplined approach to evaluate and improve the effectiveness of risk management, control, and governance processes.
Code of Ethics • Integrity
– The integrity of internal auditors establishes trust and thus provides the basis for reliance on their judgment.
• Objectivity – Internal auditors exhibit the highest level of professional objectivity
in gathering, evaluating, and communicating information about the activity or process being examined. Internal auditors make a balanced assessment of all the relevant circumstances and are not unduly influenced by their own interests or by others in forming judgments.
• Confidentiality – Internal auditors respect the value and ownership of information
they receive and do not disclose information without appropriate authority unless there is a legal or professional obligation to do so.
• Competency – Internal auditors apply the knowledge, skills, and experience
needed in the performance of internal auditing services.

(C) GoldCal LLC 2015 9
PAs related to Attribute Standards 1000-1: Internal Audit Charter
1110-1: Organizational Independence
1111-1: Board Interaction
1120-1: Individual Objectivity
1130-1: Impairments to Independence or Objectivity
1130.A1-1: Assessing Operations for Which Internal Auditors were Previously Responsible
1130.A2-1: Internal Audit’s Responsibility for Other (Non-audit) Functions
1200-1: Proficiency and Due Professional Care
1210-1: Proficiency
1210.A1-1: Obtaining Services to Support or Complement the Internal Audit Activity
1220-1: Due Professional Care
1230-1: Continuing Professional Development
1300-1: Quality Assurance and Improvement Program
1310-1: Requirements of the Quality Assurance and Improvement Program
1311-1: Internal Assessments
1312-1: External Assessments
1312-2: External Assessment - Self Assessment with Independent Validation
1321-1: Use of “Conforms with the International Standards for the Professional Practice of Internal Auditing”
PAs related to Performance Standards 2010-1: Linking the Audit Plan to Risk and
Exposures
2020-1: Communication and Approval
2030-1: Resource Management
2040-1: Policies and Procedures
2050-1: Coordination
2060-1: Reporting to Senior Management and the Board
2120-1: Assessing the Adequacy of Risk Management Processes
2130-1: Assessing the Adequacy of Control Processes
2130.A1-1: Information Reliability and Integrity
2130.A1-2: Evaluating An Organization's Privacy Framework
2200-1: Engagement Planning
2210-1: Engagement Objectives
2210.A1-1: Risk Assessment in Engagement Planning
2230-1: Engagement Resource Allocation
2240-1: Engagement Work Program
2330-1: Documenting Information
2330.A1-1: Control of Engagement Records
2330.A2-1: Retention of Records
2340-1: Engagement Supervision
2410-1: Communication Criteria
2420-1 Quality of Communications
2440-1: Disseminating Results
2500-1: Monitoring Progress
2500.A1-1: Follow-up Process
GENERAL IT AUDIT GUIDANCE

(C) GoldCal LLC 2015 10
General IT Guidance • IIA GTAG Series – IT Auditing for Non-IT
Auditors • ISACA • CobiT
Practice Guides • 15 Global Technology Audit Guides (GTAG)
• Guide on the assessment of IT Risk (GAIT)
• Additional Practice Guides will be issued regularly
ANNUAL AUDIT PLANNING

(C) GoldCal LLC 2015 11
Guidance on Planning and Scheduling of Engagements Contained in IIA Professional Standards and Related Practice Advisories • CAE has a responsibility to assure the audit committee that the
outcomes of planned internal audits will result in maximum value to the organization in relation to their cost
IIA Professional Standard 2010 requires: • The CAE should establish risk-based plans to determine the
priorities of the internal audit activity, consistent with the organization’s goals
• Plan should be : – Detailed enough to enable the internal audit activity to achieve
the objectives of internal auditing that are set forth in its mission statement and charter document
– The plan should also be based on an assessment of risks throughout the organization
Guidance on Planning and Scheduling of Engagements Contained in IIA Professional Standards and Related Practice Advisories • Practice Advisory 2010-1, Planning explains in paragraph 1 the process as
establishing: goals, engagement work schedules, staffing plans and financial budgets, and activity reports. The Practice Advisory (2010-1) goes on in paragraph 4 to outline various factors that should be considered in establishing planning and scheduling priorities: – Dates and results of the last engagement; – Updated assessments of risks and effectiveness of risk management
and control processes; – Requests by the board and senior management; – Current issues relating to organizational governance; – Major changes in the enterprise’s business, operations, systems, and
controls; – Opportunities to achieve operating benefits; and – Changes to and capabilities of the audit staff. The work schedules
should be sufficiently flexible to cover unanticipated demands on the internal audit activity
What is an Audit Risk Assessment? • The Audit Risk assessment is the identification and analysis of
relevant risks to the achievement of an organization's objectives, for the purpose of determining how those risks should be managed
• Risk assessment implies an initial determination of operating objectives, then a systematic identification of those things that could prevent each objective from being attained. In other words, it's an analysis of what could go wrong
• Not all risks are equal. Some are more likely than others to occur, and some will have a greater impact than others if they occur. So, once risks are identified, their probability and significance must be assessed
• The risk assessment process is an ongoing one. Internal and external threats constantly develop, presenting new hazards to the organization. Change itself is a risk, and management must continually adapt its policies and procedures to manage its changing risks to a comfortable level

(C) GoldCal LLC 2015 12
THE INTERNAL AUDIT PROCESS
Internal Audit Process
Planning Fieldwork Reporting
Continuous Communication
Planning Fieldwork Reporting Results & Follow-Up
• Information Gathering
• Documentation • Gain an
Understanding • Engagement
Risk Assessment
• Audit Testing • Audit Testing
Types • Workpaper
Creation • Finding
Discussions • Conclusions
• Issue Discussion
• Report Finalization
• Report Issuance
• Update RA • Finalize
Documentation • Issue Management
PLANNING
Planning

(C) GoldCal LLC 2015 13
PRELIMINARY ENGAGEMENT-LEVEL RISK ASSESSMENT (INHERENT RISK)
Preliminary Risk Analysis (PRA) • Risk - Function of probability and potential impact
– Each business function or entity has approved tolerance levels for risk exposure
– Risk exposure tolerance must be monitored to determine whether it is increasing, decreasing, or remaining stable
• Key to an effective PRA is understanding the goals and objectives of an audit – The objective of an audit is not to perform the audit – Why is this audit being performed? – How can we narrow the focus of the audit to the greatest risks? – Why was it identified as a risk? – Why was it deemed important enough to appear in the audit plan?
• Information collected alters audit scope • Higher risk = More testing • Lower risk = Less/possibly no testing • A good risk analysis refocuses the audit to the most relevant
points (this is where real value is added!)
Risk Categories - Standard • Reputational - Potential that negative publicity regarding
an the company’s business practices, whether true or not, will cause a decline in the customer base, costly litigation, or revenue reductions
• Regulatory and Compliance - Risk of rating adjustments and reputational impact that stems from regulatory oversight of the Company’s conformance with regulations and guidelines
• Strategic and Emerging - Related to the current and future impact on earnings, capital or potential growth that may arise from adverse business decisions, improper implementation of decisions, or lack of responsiveness to industry changes. Strategic risks are closely related to identifying and monitoring emerging risks

(C) GoldCal LLC 2015 14
Risk Categories – Standard (cont) • Operational/Fraud - Risk of direct or indirect loss
resulting from inadequate or failed internal processes, people, strategies or external events; Includes fraud risk
• Technology - Risk of loss due to inadequate security, confidentiality, integrity, capability or availability of systems affecting an organization’s operations, assets, customers, shareholders or employees
• Financial Reporting – Risk of unreliable or misleading financial reporting and disclosures, including to the U.S. Treasury, SEC, FDIC, FFIEC and other external reporting
Discussion – What Other Risk Categories Should be Used in Your Organization?
Assess Inherent Risk – What is IR? Inherent Risk: The risk that an activity would pose if no controls or other mitigating factors were in place (the gross risk or risk before controls) • Tempting to equate Inherent Risk to Cost, since both
terms refer to the importance of a process or asset to a business before controls (“vulnerabilities”) are taken into account
• Alternatively, Inherent Risk could equated to the Probability that records are incorrect
• Inherent Risk is not always HIGH!

(C) GoldCal LLC 2015 15
Preliminary Analytical Procedures • Five general types of procedures for analysis of
current year account balance are as follows: – Compare to balances for one or more comparable
periods – Compare to anticipated results (budget and
forecasts) – Evaluate relationships to other current-year balances
for conformity with predictable patterns – Compare with similar industry information – Study relationships with relevant non–financial
information
CASE STUDY
Case Study - Payroll • Assess Inherent Risk for the Case Study • Include All Risk Categories
– Reputational – Regulatory and Compliance – Strategic and Emerging – Operational/Fraud – Technology – Financial Reporting
• Rank 1-3 (1=Low, 2=Medium, 3=High) • Explain rankings for each • What Ratios could be helpful in assessing risk?

(C) GoldCal LLC 2015 16
AUDIT PLANNING PROCESS
Elements of Preliminary Work 1. Define Objectives
a. Define Business Objectives for Area Under Review (verified in Interviewing)
b. Define Business Risks to Meeting Those Objectives (verified in Interviewing)
c. Define Preliminary Audit Objectives (Risk-Based) 2. Define Scope (Sufficient) 3. Knowledge Gathering (Readily Available) 4. Authoritative Research 5. Interview Management (Who/What/Why/When) –
Covered Later in Course 6. Identify Internal Controls (Key vs. Non-Key) – Covered
Later in Course 7. Walkthroughs/Narratives/Documentation 8. Assess Key Control Design 9. Resource Allocation (Appropriate) 10. What Else Can we Provide?
1. Define Preliminary Audit Objectives • General idea (initial perspective) as to what
we should be auditing and why we are auditing it
• Define Preliminary Audit Objectives – Why are you performing this audit? – What is the point of this audit? – What are the expected outcomes? – What are the expected benefits?
NOTE: Audit Objectives cannot be developed without understanding the (a) business objectives and (b) risks to those objectives!

(C) GoldCal LLC 2015 17
Audit Engagement – Planning Objectives =
pecific easurable chievable esults-Orientated ime-Based
Define Audit Objectives – Common Pitfalls • Objectives are not SMART! • Too General to Try to Cover Everything • Too Specific – Limits Possible Scope • Do Not Make Sense to Auditee
CASE STUDY

(C) GoldCal LLC 2015 18
Case Study - Payroll • Identify business objectives for case study • Identify key risks that could impede the
company form meeting those objectives • Identify preliminary audit objectives (refined
after planning is complete)
2. Define Scope • What are we auditing? • What period? • What depth? • What area?
3. KNOWLEDGE GATHERING

(C) GoldCal LLC 2015 19
3. Knowledge Gathering • Narratives • Policies & Procedures • Organizational Chart • Intranet • Previous Audit Reports • Organizational Files, etc.
DISCUSSION
Utilizing Public Information • Should you Google the names of key
auditees during planning? • What if the key auditee has a
bankruptcy? – Would you want to know? – Does it matter?

(C) GoldCal LLC 2015 20
4. Authoritative Research • Audit Director’s Roundtable • Knowledgeleader.com • www.aicpa.org • www.auditnet.org • www.theiia.org • www.isaca.org • www.acuia.org • www.sec.org • Peer Groups
6. Internal Controls • Controls are relevant for any type of
audit and any process • All controls should be identified (not
necessarily by internal audit) and key controls (defined later in section) should be identified
• Throughout the process, review for: – Controls that make sense – Controls that are efficient – Are there better ways to do things?
Control Assertions • Validity - Ensure that recorded transactions are the ones that
should have been recorded. • Completeness - Ensure that valid transactions are not omitted
entirely from the accounting records. • Authorization - Ensure that transactions are approved before
they are recorded. • Accuracy - Ensure that dollar amounts are figured correctly. • Classification - Ensure that transactions are recorded in the
right accounts. • Accounting and Posting - Ensure that the accounting process
for a transaction is completely performed and in conformity with GAAP.
• Proper period - Ensure that transactions are accounted for in the period in which they occur.

(C) GoldCal LLC 2015 21
Control Specifics Each control should describe the actions taken by management to mitigate the related risk, including: • WHO (or what system) performs the control activity • WHAT is used to perform the activity (reports/
systems) • WHEN (how often/relational timing) the activity is
performed • WHERE is the activity is performed, if relevant to
mitigating the risk • WHY the activity is performed • HOW (specific action) the activity is performed
Controls are Either: • Preventive Control - Designed to prevent
or deter the risk event from occurring • Detective/ Corrective Control - Designed
to discover and/or correct the risk event that has already occurred. Detective controls must occur on a timely basis (before the event has had an unacceptably negative impact) to be considered effective
Control Types • Control: Activity conducted by management to mitigate
risks to an acceptable level and increase the likelihood that objectives will be achieved
• Key Control: Strongest control designed to mitigate a risk; usually addresses three control assertions or more
• Compensating Control: Control designed to supplement key controls that are either ineffective or cannot fully mitigate the risk themselves to an acceptable level.
• Complementary Control: Control that must be combined with one or more other controls to mitigate the risk to an acceptable level
• Monitoring Control: Control that provides management timely and accurate feedback on compliance and effectiveness of other controls; must have a strong level of precision

(C) GoldCal LLC 2015 22
CASE STUDY
Case Study - Payroll • Identify three key controls in the case
study • Explain why these controls are key
7. Walkthroughs/Narratives/Documentation Walkthrough - Procedure used during an audit of a process to gauge its reliability • Walkthough tests trace the transaction step-
by-step through the process from its inception to the final disposition/recording
Other Benefits: • Validate Documentation • Reliability of Information • Get to know and understand personnel • Verify control design effectiveness

(C) GoldCal LLC 2015 23
Walkthrough Questions • Use Open-Ended questions • Get them talking about their job and what they do • It is not the first question, it is usually the next
question – Interfaces – Reports – When discussing controls, make sure to ask if the
control: • Is in the system? • If it is manual, could it be done in the system?
– Include SME with Process Owner in interviews?
8. Assess Key Control Design • Determine whether each key control is designed
adequately to mitigate the associated risk(s) • Primary focus of testing - Determine whether the key
controls are designed adequately to provide reasonable assurance that the risks are adequately
• When assessing control design, focus on: – Alignment between controls and the business and audit risks
identified – Whether controls satisfy the information processing objectives
(Completeness, Accuracy, Validity, Restricted Access) and relevant financial statement assertions
– Knowledge and experience of the people involved in performing the controls
– Segregation of duties relevant to the process being controlled
10. What Else Can We Provide? • Always ask the auditee “how else can we
help you?” (last question) – Shows trust – Builds confidence – We are not on the other team – We want to help – We are consultants, not auditors

(C) GoldCal LLC 2015 24
UPDATED ENGAGEMENT-LEVEL RISK ASSESSMENT (RESIDUAL RISK)
Updating the Risk Hypothesis • No steadfast template…but be consistent! • Numerical Ratings or H/M/L • Show Starting Point (prior to planning), Planning and
End Point (prior to fieldwork) – walk auditee through the logic
Residual Risk • Residual Risk: The risk that remains after
controls are taken into account (the net risk or risk after controls)
• Commonly known as Risk (generalized)

(C) GoldCal LLC 2015 25
CASE STUDY
Case Study - Payroll • Update the Inherent Risk Rating based
on the additional information that has been uncovered during planning – People Rating: Based on the experience
and know-how of the personnel, will this increase or decrease the current inherent risk rating?
– Process/Control Design Rating: Based on the design of the controls (see Planning) and the risks the controls should mitigate, rank the risk
BUILDING AN EFFECTIVE AUDIT WORKPROGRAM

(C) GoldCal LLC 2015 26
Discussion – What Should be in a Workprogram?
Workprogram Contents • Basic criteria for audit programs include:
– Carefully stated objectives, agreed to by the client. – Programs should be tailor-made to the audit assignment. – Each step of the program should include the reason for the step. – Step priority should be indicated. – Programs should be flexible and permit use of initiative and
judgment. – Audit work requested by the client should be identified.
• One of the objectives of the audit is to ensure that the client is effectively managing risks. During the audit, the auditor should maintain a record of the accomplishment of this element of the audit.
Writing Workprograms – Leading Practices • Tailor the program to fit the specific audit as to the type of
organization, personnel involved, systems and procedures in effect, degree of sophistication, etc.
• Each work program step should clearly set forth the work to be completed and the reason (objective) for performing – Each audit team member must fully understand and comprehend
why each audit step is being completed (e.g. succession planning) – Minimizes the inclusion of possible unnecessary work steps. – Efficient and effective review of audit work papers
• Program should be flexible and permit application of initiative in deviating from prescribed procedures
• Provide for the development of individual findings: – Performance is analyzed and reported – Evidence to support conclusions – Evaluate performance and evidence in comparison with relevant
standards

(C) GoldCal LLC 2015 27
STEPS TO BUILDING AN EFFECTIVE AUDIT WORKPROGRAM
Steps to Building an Effective Audit Workprogram
1. Identify Specific Audit Risks 2. Define Audit Scope 3. Define Audit Objectives 4. Define Audit Criteria 5. Define Overall Steps to Testing
Objectives 6. Define Specific Work Sub-Steps for Each
Overall Step 7. Verify Specific Audit Risks are covered
through Work Steps
Define Audit Criteria • Make all Audit Objectives Measurable! • Efficiency and effectiveness is defined as:
– Key Performance Indicators that will be defined by Management and the business and measured against
– Leading industry practices – Balance of controls and efficiency
• Tools and materials are defined as: – Guidance on current role and responsibilities – Access, both physical and logical – Role of hiring manager in process
• Messaging is defined as: – Documents/Presentations that highlight the strengths of the
organization – Document/Presentations that outline the benefits of working at
the organization – Analysis of role and key stakeholders each new employee should
meet and be introduced to

(C) GoldCal LLC 2015 28
CASE STUDY
Case Study - Payroll • For the audit objectives previously
identified in Exercise #2, identify any audit criteria (if necessary)

(C) GoldCal LLC 2015 29
Keys to Building an Effective Workprogram • Remember – testing should correlate
to risk – Higher Risk: need more/reliable evidence – Lesser Risk: do we test at all? Can we just
walkthrough? • Writing for ANY PRUDENT AUDITOR • Need lots of detail but cannot
eliminate (nor do you want to) professional judgment.
Do Not Forget! • How will testing be performed? • How will samples be selected? • What is the source(s) of information? • What types of information are needed? • Must evaluate sufficiency, reliability, relevance? • How will the objectives be tested? • How reliable does the testing method need to
be? • Can we integrate other audits?
– IT General Controls/Application Controls – Fraud Risk Assessment/Red Flags
Determining Sampling Sizes • Identify your population first • Base sample size on risk • Consider transaction frequency • Establish a sampling technique/
process/policy • Consider the number of exceptions
you expect to find (more exceptions = more samples) – set your error rate
• Ask your external auditor

(C) GoldCal LLC 2015 30
Evidence Requirements • Sufficient – Measure of quantity of the evidence; should be
collected and evaluated sufficient information so that the reasonably informed unbiased person agreed with the auditor’s conclusions.
• Reliable – Comprises the measure of reliability and adequacy of the source of evidence and the method of seeking thereof; generally, information received from a third party that is independent is more reliable; the evidence is reliable where it is gained via direct physical examination, observations and inspection and where it is received in the documentary form, rather than verbally. Degree of information reliability increases where it is received from several sources;
• Adequate – Measure of adequacy of the evidence. Audit evidence may be physical, testimonial, documentary and analytical.
Types of Audit Tests • Design only (no control testing) • Interviews only (must corroborate) • Procedural review (not
representative) • IT testing (analyze files, screens,
procedures, logs, and audit trails) • Tests of controls • Substantive tests • CAATs
CASE STUDY

(C) GoldCal LLC 2015 31
Write the Workprogram • For the controls identified as key in
Exercise 3, write the workprogram steps necessary in order to test each.
Build Workprogram Steps - Example • Audit Objective - Employees are not
provided applicable tools and materials to begin tenures successfully
• Audit Criteria - Tools and materials are defined as: – Guidance on current role and
responsibilities – Access, both physical and logical – Role of hiring manager in process
Workprogram Steps - Example Based on the IA Sampling Policy, select a sample of 30 new hires during calendar year 2013: 1. Verify Human Resources coordinates with the hiring manager
and applicable department to obtain the new employee’s role guidance summary and presentation of detail of job description (this is verified through the new employee coordination checklist).
2. Obtain the new employee building access form and verify it has been completed by the hiring manager and approved by facilities at least three days prior to start date
3. Obtain the new employee equipment forms and verify they have been completed by the hiring manager and approved by IT and Facilities in regards to office equipment, smart phone and laptop
4. Obtain the new employee system access forms and verify they have been completed by the hiring manager and approved by IT Security at least five days prior to start date

(C) GoldCal LLC 2015 32
FRAUD AUDITING
The Definition of Fraud “… any illegal act characterized by deceit, concealment, or violation of trust. These acts are not dependent upon the threat of violence or physical force. Frauds are perpetrated by parties and organizations to obtain money, property, or services; to avoid payment or loss of services; or to secure personal or business advantage.”
Fraud Auditing Overview • Audits are not designed to detect fraud
– Goal: Determine whether the financial statement is free from material misstatements.
• Auditors test only a small fraction of transactions
• Auditors must: – Be aware of the potential of fraud – Discuss how fraud could occur – Delve into suspicious observations and report
them

(C) GoldCal LLC 2015 33
Fraud Quiz 1. What % of its revenue does the typical organization
loose to fraud each year? 2. How many months does a fraud usually last before
being reported? 3. What is the most common type of occupational fraud? 4. Three industries most common victimized by fraud are: 5. How many prior offenses have occupational fraudsters
often committed? 6. Do the higher fraud losses tend to be committed by
fraudsters with low or high tenure with an organization? 7. What departments do most fraudster’s work in?
Fraud Quiz Answers 1. Answer – 5% 2. Answer – 18 months 3. Answer – asset misappropriation 4. Answer – banking & financial services, government & public
administration, and manufacturing 5. Answer – None! Most are first offenders with clean histories 6. Answer – the higher the fraud loss – median of $229,000 are
committed by fraudsters with more than 10 years. Those during the first year on the job committed a median of $25,000
7. Answer – accounting, operations, sales, executive/upper mgmt., customer service, and purchasing
The Fraud Triangle Opportunity • Must gain access to assets/
records • Can be controlled/prevented
by organization
Rationalization • Follow through and commit
the fraud • Can be controlled/prevented
by organization
Pressure • The more incentive, the easier it is to justify • Financial or personal problems, financial
pressure, mental instability

(C) GoldCal LLC 2015 34
How is Fraud Discovered?
How is Fraud Discovered?
Detection of Fraud Schemes

(C) GoldCal LLC 2015 35
Factors Contributing to Fraud Contributing Factor Percentage
Poor Controls 59%
Management Override 36%
High Risk Industry 34%
Third Party Collusion 33%
No Ethics Policy 7%
No Board of Directors Control
6%
Other 2%
Truth – White Collar Criminal • Older (30+ years) • 55% male, 45% female • An appearance of a stable family situation • Above average (postgraduate) education. • Less likely to have a criminal record. • Good psychological health. • Position of trust. • Detailed knowledge of accounting systems
and their weaknesses. • Prior accounting experience.
Categories of Fraud Risk • Misappropriation of Assets
– involve the theft or misuse of an organization’s assets. (Common examples include skimming revenues, stealing inventory, and payroll fraud.)
• Corruption – fraudsters wrongfully use their influence in a business transaction in
order to procure some benefit for themselves or another person, contrary to their duty to their employer or the rights of another. (Common examples include accepting kickbacks and engaging in conflicts of interest.)
• Fraudulent Financial Statements – falsification of an organization’s financial statements. (Common
examples include overstating revenues and understating liabilities or expenses.)

(C) GoldCal LLC 2015 36
FRAUD RED FLAGS
Red Flags Are Indicators, Not Proof • Living beyond means (36%) • Financial difficulties (27%) • Close association with vendors/customers
(19%) • Poor internal controls (18%) • Employee morale changes • Employee turnover • Pressure to meet targets • Management infighting • Addiction problems
Employee Red Flags • Significant change in lifestyle, such as new
wealth • Financial difficulties may create need
– Gambling or drug addiction – Infidelity is an expensive habit
• Criminal background • Chronic legal problems
• Dishonest behavior in other parts of life • Beat the system
– Break rules commonly
• Chronic dissatisfaction with job

(C) GoldCal LLC 2015 37
Organizational Red Flags
• Lack of communication of expectations
• Too much trust in key employees
• Lack of proper authorization procedures
• Lack of attention to detail
• Changes in organizational structure
• Tendency towards crisis management
Financial Document Red Flags • Missing/Altered
documents • Excessive number of
voided documents • Documents not
numerically controlled
• Questionable handwriting or authorization
• Numerous duplicate payments
• Unusual billing addresses
• Address of employee same as vendor
• Duplicate or photocopied invoices
• Invoices not folded for envelope
Accountability and Control Red Flags
• Lack of segregation of duties
• Lack of physical security and/or key control
• Weak links in chain of controls and accountability
• Missing independent checks on performance
• Weak management style
• Poor system design • Inadequate training

(C) GoldCal LLC 2015 38
How to Minimize Fraud Risk • Adhere to policies/procedures
(especially documentation and authorization)
• Identify and understand of key controls and fraud areas
• Ensure physical security over assets • Provide proper training to employees • Independently review and monitor tasks • Review segregation of duties • Ensure clear lines of authority
How to Minimize Fraud Risk • Rotate duties in positions susceptible to fraud • Ensure employees take regular vacations • Schedule regular independent audits of areas
susceptible to fraud • Ensure background checks including criminal and
credit for all employees • Make sure internal controls are followed • Ask for documentation • Ensure that one person does not have total
responsibility for a process • Evaluate performance regularly • Report suspicious activity
CONTROLS OVERVIEW

(C) GoldCal LLC 2015 39
What Do We Do on a Daily Basis that Involves Internal Control?
§ Lock-up valuable belongings § Keep copies of your tax returns and related
support § Balance your checkbook § Keeping passwords unique and separate § Planning Ahead § Home and Car Insurance § Seat Belts § Physical Control of Credit Cards
What is the Risk of Weak Internal Controls? Business Interruption § system breakdowns or
catastrophes, excessive re-work to correct for errors.
Erroneous Management Decisions § based on erroneous, inadequate
or misleading information.
Fraud, Embezzlement and Theft § by management, employees,
customers, vendors, or the public-at-large.
What is the Risk of Weak Internal Controls? Statutory Sanctions § penalties arising from failure to
comply with regulatory requirements, as well as overt violations.
Excessive Costs/Deficient Revenues § expenses which could have been
avoided, as well as loss of revenues. Loss, Misuse or Destruction of Assets § unintentional loss of physical assets
such as cash, inventory, and equipment.

(C) GoldCal LLC 2015 40
What is the Benefit of Strong Internal Controls? § Providing appropriate checks and
balances. § Reducing and preventing errors in a
cost- effective manner. § Ensuring priority issues and risks are
identified and addressed. § Protecting employees & resources. § Having more efficient audits,
resulting in shorter timelines, less testing, and fewer demands on staff.
Controls Applicable to All • EXERCISE – Based on your view of
internal controls, what controls apply to all processes regardless of type?
The foundation of our controls
home!
ANSWER • Segregation of Duties • Physical and IT Access • Review and Reconciliation Controls
(Management Oversight) – Balance Sheet Reconciliations – JE Reviews
• Tiered Approvals • Pre-numbered documents • Policies and Procedures

(C) GoldCal LLC 2015 41
Other Controls • Code of Conduct • Hotline • Whistle-blower policy • Conflict of interest policy • Fiscal Policy
Update Considers Changes in Business and Operating Environments
Environments changes... • Expectations for governance oversight • Globalization of markets and operations • Changes and greater complexity in
business • Complexities in laws, rules, regulations,
and standards • Expectations for competencies and
accountabilities • Use of, and reliance on, evolving
technologies • Expectations relating to preventing and
detecting fraud …have driven Framework updates • COSO Cube (2013 Edition)
Update Articulates 17 Principles of Effective Internal Control Control Environment (CE)
1. Demonstrates commitment to integrity and ethical values
2. Exercises oversight responsibility 3. Establishes structure, authority
and responsibility 4. Demonstrates commitment to
competence 5. Enforces accountability
Risk Assessment (RA) 6. Specifies suitable objectives 7. Identifies and analyzes risk 8. Assesses fraud risk 9. Identifies and analyzes
significant change Control Activities (CA)
10. Selects and develops control activities
11. Selects and develops general
controls over technology 12. Deploys through policies and
procedures
Information & Communication (IC) 13. Uses relevant information 14. Communicates internally 15. Communicates externally
Monitoring Activities (MA) 16. Conducts ongoing and/or
separate evaluations 17. Evaluates and communicates
deficiencies

(C) GoldCal LLC 2015 42
AUDIT SAMPLING
Reasons for Sampling • Efficiency • Standards permit sampling to obtain
sufficient evidence to support assertions
• Reasonable Assurance – not Absolute!
Statistics as an Audit Tool • Auditors use inferential statistics to
draw conclusions about populations based on samples of data.
• Why do auditors use samples—usually too costly and time-consuming to examine entire “universe”

(C) GoldCal LLC 2015 43
Three Instances When Not to Use Sampling
• Total is auditable • Inquiry/Observation • Analytical Procedures – Trending – Ratios
STATISTICAL VS NON-STATISTICAL SAMPLING
Types of Sampling • Statistical – provides quantitative
measure of sampling risk • Nonstatistical – does not provide
quantitative measure of sampling risk
What does this mean?

(C) GoldCal LLC 2015 44
Types of Sampling (cont.) • When using nonstatistical sampling,
errors or issues identified cannot be quantified over the population as there is no strategy to the sampling – Reliability – Replacing issues/errors/omissions – Bias in sampling
Advantages of Statistical Sampling • Objective and defendable – Not subject to bias
• Estimate of degree of risk that sample may not be representative of entire population
• Results are quantifiable • Stat sampling can be more accurate
than review of population (volume and tediousness of review can lead to errors of omission or fact)
• Can save time and money
SELECTION METHODOLOGIES

(C) GoldCal LLC 2015 45
Selection Methodologies • REMEMBER: Valid statistical references
can only be made when each sampling unit has an equal probability of being selected -> Truly Random Technique – Simple Random Sampling – Stratified Random Sampling – Systematic Sampling
• All units in a population have an equal chance of being selected.
• Example – Texas Lottery
Simple Random Sampling
• Stratification is the process of grouping members of the population into relatively homogeneous subgroups before sampling. The strata should be mutually exclusive: every element in the population must be assigned to only one stratum.
• Proportionate allocation uses a sampling fraction in each of the strata that is proportional to that of the total population. If the population consists of 60% in the male stratum and 40% in the female stratum, then the relative size of the two samples (three males, two females) should reflect this proportion.
• Divide population into groups (Select from all disbursements less than $50,000 and test all disbursements > $50,000)
Stratified Random Sampling

(C) GoldCal LLC 2015 46
• Choosing every Xth disbursement in order of disbursement (check number)
• Systematic sampling is a statistical method involving the selection of elements from an ordered sampling frame.
• The most common form of systematic sampling is an equal-probability method, in which every kth element in the frame is selected, where k, the sampling interval (sometimes known as the skip), is calculated as: – K=N/n – n is the sample size, and N is the population size.
• Forces us to ensure a pattern is not hidden • Population must also be homogenous
Systematic Sampling
Nonstat Sampling Methodologies • Haphazard Selection – selection without
intentional bios • Judgmental Selection – attempt to select
an unbiased sample by specifically selecting large items and a selection of smaller items
• Block Selection – selection of adjoining transactions (invoices 1-1000 or all payments in May)
• Cluster Selection – attributes similar, geographic location
Don’t Forget! Consideration of: • Voids – replace – Not a valid selection
• Missing – control not effective/ value of $0 – Why is it missing?
• Debit/Credit – test separately? – Debit/Credits skew the ultimate results. – For example, if we are testing accounts
receivable balances and we come across a credit and attempted to quantify the error, this could be significant.

(C) GoldCal LLC 2015 47
• Population is numbered or are listed in a register – Random
• Random number is too burdensome and there is no pattern in the population and items missing can be identified – Intervals/Systematic
• Significant variation in the population and more reliability would be achieved by breaking the population into similar groups – Stratification
• Population is geographically dispersed and making random selections from the population would be burdensome - Cluster
Population Selection Methodology
FIELDWORK
Fieldwork
What is Audit Documentation? • Principal written record • Performed in compliance with applicable
standards • Provide a clear link between significant
matters • Contain sufficient information and detail • Clear understanding of:
– The purpose of the work; – The work performed; – The source of the information analyzed and supporting evidential
matter obtained, examined, and evaluated; and – The nature, timing, and extent of the auditing procedures planned;
– The conclusions reached.

(C) GoldCal LLC 2015 48
Purpose of Audit Documentation • Assisting auditors to plan and perform the audit; • Assisting those responsible to direct, supervise, and review the
work performed; • Providing and demonstrating stand alone documentation on
the accountability of those performing the work (i.e., compliance with applicable standards);
• Assisting quality-control reviewers to understand and assess how the engagement team reached and supported significant conclusions;
• Enabling internal and external inspection teams and peer reviewers to assess compliance with professional, legal, and regulatory standards and requirements; and
• Assisting successor auditors.
What Does Audit Documentation Include?
• Audit documentation and workpapers can be stored in any medium and include a variety of documents, including the following: – Audit programs and other planning documents; – Analyses; – Memoranda; – Confirmations; – Representation letters (if relevant); – Extracts of important documents; – Significant correspondence; – Details of tests performed and documents examined; and – Includes significant emails
WHY is working paper quality so important? • Working papers are the basis for our conclusions – they must
stand on their own and be understandable by external parties who review them.
• Execution project management – Quality documentation enables us to effectively supervise and review engagement execution.
• Documentation provides evidence of compliance with IIA Standards and attention to professional standards.

(C) GoldCal LLC 2015 49
Opening Remarks – Documentation Concepts
§ What are workpapers? – Evidence of audit performance in all phases – Documents that support:
§ Audit findings & observations – Exist in each phase of the audit process
§ Why do we have workpapers? – Objective evidence for audit conclusions
§ Used if issues arise after report published – Required by professional standards – Reference for other audit teams – May be relied upon by external parties (DCAA, D&T)
Opening Remarks – Documentation Concepts
§ Workpaper documentation concepts – Sufficient
§ Support program steps & audit results
– Relevant § Clear relationship to audit objectives & results
– Economical § Include only what is essential
– Complete § Support conclusions and findings
– Sensitivity § Generally considered “attorney-client privilege”
AUDIT DOCUMENTATION GUIDANCE

(C) GoldCal LLC 2015 50
IAPPF • 2240 – Engagement Work Program
– Internal auditors must develop and document work programs that achieve the engagement objectives
• 2240.A1 – Work programs must include the procedures for identifying,
analyzing, evaluating, and documenting information during the engagement
– The work program must be approved prior to its implementation, and any adjustments approved promptly
• 2240.C1 – Work programs for consulting engagements may vary in
form and content depending upon the nature of the engagement
IAPPF • 2310 – Identifying Information
– Internal auditors must identify sufficient, reliable, relevant, and useful information to achieve the engagement’s objectives
• 2320 – Analysis and Evaluation – Internal auditors must base conclusions and engagement results
on appropriate analyses and evaluations
Workpaper Overview • At a minimum, audit documentation should be sufficient to: Enable reviewers
to understand the tests that were conducted, the results thereof, and the evidence accumulated.
• Indicate which members of the engagement team performed and reviewed the work.
• Show that the accounting records agree with or reconcile to the financial statements (or other information being reported upon).
• In determining the type and extent of audit documentation for a particular audit area, the following factors should be taken into account:
• The risk of material misstatement. – The degree of judgment involved in performing the work and in
evaluating the results. – The significance of the evidence in relation to the assertions being tested. – The nature and extent of exceptions found. – Documentation should include identification of items examined in
substantive tests of details and of items reviewed to determine the operating effectiveness of internal controls.

(C) GoldCal LLC 2015 51
Workpaper Overview • Significant findings or issues should be documented, as should actions
taken to address them and the final conclusions reached. Significant findings and issues generally include: Matters involving the selection, application, and consistency of accounting principles.
• Results of procedures performed indicating that the financial statements could be materially misleading or a need to revise a previous assessment of the risk of material misstatement.
• Circumstances causing difficulty in applying auditing procedures. • Findings that could result in a modification to the auditor's standard
report.
Audit Documentation – Common Errors • Constructing workpapers that sufficiently evidence work performed in an
efficient and effective fashion requires judgment, skill, and experience. It is a task that many auditors find to be among the most difficult in performing an audit. Reviewers often note that workpapers are simply incomplete, unreadable, unintelligible, or unwisely constructed. Other more subtle deficiencies, such as the following, have also been noted: Narratives of discussions, meetings, and so forth, have no clear indication as to the relevance to the audit.
• The auditor has failed to properly cross-reference copies of evidential matter to narratives, lead sheets, or tables summarizing sample results.
• Comparative analyses do not provide complete comparisons or analyses. • Written conclusions are not supported by, or referenced to, evidence. • Copies of memoranda, invoices, purchase orders, and other forms of
evidence have no reference or commentary as to why they are present. • Copies of computerized reports (in whole or in part) have no indication as to
why they are present. • Copies of flowcharts, procedural narratives, and policy statements do not
clearly relate to the audit objective.
DOCUMENTING AN AUDIT TEST

(C) GoldCal LLC 2015 52
Testing • The procedure of testing is a methodology
that is a major part of the previously described process of verifying. It is simply the determination of: – Validity – Accuracy – Compliance – Competence of controls
Audit Test Documentation • For each test performed, the following
detail MUST be included: – Control Objective – Clearly Document testing attributes – Document sample size, why sample is appropriate, sampling
methodology, population and source – If exceptions are identified, document what the impact is and
how it is addressed (i.e., extended testing sample, isolated error and why, etc).
– Document testing results and conclusion – Support documentation to be retained to allow re-performance
by external auditors, where applicable. – Photocopy support and make binders available on the first day of
fieldwork.
Audit Testing • Should describe identifying characteristics of the specific items
tested (sufficient to enable reperformance of the test for the same items), such as the source or population and the selection criteria
• For example: For an audit sample selected from a population of checks, the specific check numbers of the items included in both the population and the sample; or
• For a test of all items over a specific amount from a given population, the scope and the population, such as “all journal entries over $50,000 in the general ledger for the year”; or
• For procedures that involve inquiries, the name and job description of persons interviewed, the date and content of the inquiries, and the responses received.

(C) GoldCal LLC 2015 53
Other Workpaper Considerations • Due to the significant variety of internal audit engagements
and related workpapers, assessing the adequacy of audit documentation often can be difficult. The specific audit procedures performed can result in different documentation requirements. – For example, if the engagement involves a review of sensitive
payroll information, the auditor likely would not be able to retain example information and instead would have to create a detailed memo explaining the procedures performed. The amount of auditor judgment used to determine any observations also will impact documentation requirements. Any assumptions, inferences, or other uses of judgment will need to be documented clearly and reviewed by appropriate levels of internal audit management.
Other Workpaper Considerations • Finally, the quantity and severity of exceptions noted will
require varying degrees of audit documentation. If there are no exceptions, one thorough walk-through example of procedures performed likely would suffice. How ever, if multiple significant exceptions are noted, internal auditors likely would need to obtain all related source documentation and provide detailed explanations for each exception. – Keeping these considerations in mind, internal auditors always
should try to adhere to any standard in-house work paper styles and templates. They also should exercise caution when relying on prior year workpapers, as the documentation may not meet current quality standards. Careful consideration of key audit work paper characteristics and essential elements will improve the quality of audit documentation and reflect on the audit project itself.
Pet Peeves • Do not just N/A a workprogram step; detail exactly
why it is N/A. • Do not just “DONE” a review note; explain how this
note was cleared. • Self-review all work; regardless of the time it takes.
This includes every review step the supervisor would do.
• PFW (Pass Further Review) – use sparingly or never; are you complete or is this more of a short cut?
• Know what your supervisor is looking for – understand the expectations up front.

(C) GoldCal LLC 2015 54
Four Essential Workpaper Characteristics • COMPLETENESS
– Each work paper should be completely self-standing and self-explanatory. – If a work paper is separated from the engagement file, readers should be able to
ascertain the purpose, work performed, and results based solely on information included on that single work paper. Because internal and external parties reviewing audit documentation may only select a sample of files, all individual documents must provide adequate evidence of the work performed.
– One key to achieving complete workpapers is to prepare audit documentation timely.
• ACCURACY – High-quality workpapers include statements and computations that are accurate
and technically correct. – Errors included in final workpapers certainly will shed doubt on the procedures
performed and results noted from an internal or external review perspective. – Use defined tick marks and to cross-reference computation data to source
documentation. Auditors should also clearly differentiate statements based on facts from those based on inquiry or matters of judgment.
Four Essential Workpaper Characteristics • ORGANIZATION
– Workpapers should have a logical system of numbering and a reader friendly layout so a technically competent person unfamiliar with the project could understand the purpose, procedures performed, and results.
– Workpapers should be arranged logically and cross-referenced from source documentation to test grids and audit work steps.
– The cross-referencing should extend to an issue summary that links to the audit report, thus clearly communicating the derivation of audit observations.
• RELEVANCE & CONCISENESS – Audit workpapers and items included on each work paper should
be relevant to meeting the applicable audit objective. – Writing concise notes and removing unnecessary pages of bulky
policies will also help improve the efficiency of review and ultimately the quality of the documentation.
Audit Testing • What do we test against? • What type of tests for what type of
reliability? • What is our criteria? • What are we attempting to
accomplish?

(C) GoldCal LLC 2015 55
Evidence Must Be:
Sufficient –
Information is factual, adequate and convincing so that a prudent, informed
person would reach the same conclusion as the auditor
Reliable–
The best attainable information through the use of appropriate audit techniques
Relevant –
Information supports audit findings and recommendations and is consistent with the
objectives of the audit
Useful –
Information helps the organization meet its goals
AUDIT EVIDENCE
TEST OF CONTROL
Audit Testing • For each test performed, the following detail
MUST be included: – Control activity – Clearly document testing procedures – Document sample size, why sample is appropriate,
sampling methodology, population and source – If exceptions are identified, document what the
impact is and how it is addressed (i.e., extended testing sample, isolated error and why, etc)
– Document testing results and conclusion – Support documentation to be retained to allow re-
performance by external auditors, where applicable

(C) GoldCal LLC 2015 56
Audit Testing • Should describe identifying attributes of the specific
items tested (sufficient to enable reperformance of the test for the same items), such as the source or population and the selection criteria
• For example: For an audit sample selected from a population of checks, the specific check numbers of the items included in both the population and the sample; or
• For a test of all items over a specific amount from a given population, the scope and the population, such as “all journal entries over $50,000 in the general ledger for the year”; or
• For procedures that involve inquiries, the name and job description of persons interviewed, the date and content of the inquiries, and the responses received
AUDIT WRAP-UP
Reporting
Findings • Issues should be discussed with auditee prior
to inclusion in report • Stick to the facts • Verify – no opinions • Level of Finding – direct correlation to level
of interest • Staff – can write findings and Senior can
develop and verify recommendation or Staff does it all.

(C) GoldCal LLC 2015 57
Contents of a “Typical” Audit Report • Executive Summary • Observations • Appendices
Contents of a “Typical” Audit Report • Observations – Criteria – Condition – Cause – Effect – Recommendations – Action Plans
Watch Out Words • Think through some words that should
not be used and make a list (at least five)

(C) GoldCal LLC 2015 58
Watch Out Words • Emotional Triggers
– Adequate/Inadequate
– Fail – Wrong – Finding – Opinion – Fraud
• Mysterious Terms – Discovered – Appeared – Revealed – Captured
• Definitive Terms – Absolutely – Never – Always – Must
• Ambiguous Terms – Reasonable – Should
• First/Third Person – Personally – We/I/You
Audit Follow-Up • Responsibility to follow-up and track
issues • Time, method and depth is
determined by level of importance of audit and finding – Inquiry – Re-audit – Follow-up during next year
Effective Exit Conference 1. Arrange a mutually convenient time, well in advance of fieldwork completion 2. Provide advance information to permit study and formulation of response 3. Provide a draft of the final report, if feasible (make sure to stamp this document
“DRAFT”) 4. Any significant issues identified should be discussed with the auditee real-time; the
draft report should not contain any surprises 5. Derive conclusions for each matter. The following categories indicate the variety of
possible alternatives: – Eliminate the finding. – Perform further specific research or checking. – Alter the language used in particular sections. – Attempt to identify compensating controls that would mitigate the exposure
and reduce the severity of the finding. – OK as is
6. Conduct the meeting as though it were for evidence-gathering purposes 7. Thank Everyone and Avoid arguments, disagreements, or unpleasantness 8. Listen and carefully observe reactions and responses 9. Continually reassess findings and recommendations in light of the discussion

(C) GoldCal LLC 2015 59
IT AUDITING BASICS
GENERAL COMPUTER CONTROLS
Information Security — Designing, implementing, and maintaining information security, including both physical and logical security over all access paths to programs and data. Accessing and prioritizing relevant security risks. Defining data owners, classifying data as to necessary security, and selecting and implementing security tools and techniques.
• Critical Areas • Tools and techniques restrict access to
programs, data, and other information resources
• Restricts access to programs and information
• Physical access restrictions are implemented and administered to restrict access to information
• All information resources subject to appropriate physical and logical security
• Value Add Areas • Virus Protection • Software is used in accordance with
licensing agreements and management’s authorization
• Information is protected against environmental hazards and related damage
• Security policies • Security standards • Data ownership • Information security architecture • Security administration • Logical access • Security logging & monitoring • Physical access • Environmental
Control Objectives Covers

(C) GoldCal LLC 2015 60
Access Controls • No matter what method is chosen to scope the review of application controls, the
module’s or application’s logical access controls need to be reviewed periodically. The strategies employed to determine which logical access rights will be assigned to users vary from a need-to-know basis to a need-to withhold basis. Regardless, the access rights should be granted based on the user’s job function and responsibilities.
• When a review of an application’s logical access controls is performed, it is important to ensure that the general application security controls are reviewed as well, including: – The length of the user name or user identification – The password’s length. – Password character combinations. – Password aging (e.g., users must change their password every 90 days). – Password rotation (e.g., users cannot use any of their last eight passwords). – User account lockout after six unsuccessful login attempts. – Session timeout (e.g., the application automatically logs out a user if the user has not
interacted with the application within 15 minutes)
Information Systems Operations — Supervising and maintaining computer systems operations. Providing scheduled, monitored, and secure computer operations. Satisfying end-user requirements for computer processing support and problem resolution.
• Critical Areas • Production to process batch and on-line
transactions and prepare related reports are executed timely and completely
• Only valid production programs are executed
• Value Add Areas • Data is retained in accordance with laws,
regulations, and company policy • Computer processing environment service
levels meet or exceed management’s expectations
• Users receive appropriate systems training in the use of application systems
• Users receive appropriate support to ensure that application systems function as intended
• Job scheduling • Processing control • Output control • Problem logging, tracking & reporting • Problem escalation & resolution • Capacity planning • Performance monitoring • Facilities management • Help desk procedures • Backup & Recovery • Business Continuity/Disaster Recovery
Control Objectives Covers
Application Systems Implementation and Maintenance — Selecting or developing, implementing, and maintaining application systems.
• Critical Areas • New application systems are implemented
appropriately and function as expected • When new application systems are
implemented, existing data that is appropriately converted
• All necessary modifications to existing application systems are implemented timely
• Modifications to existing systems are properly implemented and function as expected
• Value Add Areas • New application systems are acquired or
developed consistent as expected § Application systems are maintainable and
supportable
• Project planning & management • Project prioritization • Project budgeting • Systems development methodologies
• Design Specifications • Programming standards • Programmer access • Modifications to purchased software • Testing • Change control • Program documentation • User documentation
Control Objectives Covers

(C) GoldCal LLC 2015 61
Change Control • Types of changes:
– Program code changes, software updates, system patches, new software implementations
• Change controls should include: – Monitoring and logging of all changes – Steps to detect unauthorized changes – Confirmation of testing – Authorization for moving changes to production – Tracking movement of hardware and other infrastructure components – Periodic review of logs – Back out plans – User training
• Specific procedures should be defined and followed for emergency changes
Database Implementation and Support — Managing the data architecture and maintenance in terms of defining and maintaining the structure of master file data, transaction data, and organization data. Maintaining the database management system (or its equivalent).
• Critical Areas • The data structure is appropriately
implemented and functions consistent with management’s intentions
• All necessary modifications to the data structure are implemented timely and with proper approval (SDLC)
• Modifications to the data structure are appropriately implemented and the modified data structure functions consistent with management’s intentions
• Data architecture • Database implementation • Database administration & monitoring • Database maintenance & modifications
Control Objectives Topics Covered
Network Support — Designing, installing and operating networks and communication software and protocols. This includes defining the structure and interrelationships between components of the network, configuring the physical locations of files and equipment, and planning the operating capacity and capabilities to meet current network needs.
Critical Areas • New network and communication
software is appropriately implemented and functions properly and implemented in a timely manner.
• Modifications to existing network and communications software are properly implemented and function as expected
Value Add Areas • New network and communication
software is acquired consistent with management’s intentions
• Network and communication software is maintainable and supportable
Network & communication software: • Acquisition & approval • Implementation & testing • Support • Maintenance
• Performance monitoring • Documentation
Control Objectives Topics Covered

(C) GoldCal LLC 2015 62
Systems Software Support — Selecting, implementing, and maintaining necessary systems software, including the parameters that configure and control such software. Implementing and monitoring system software changes, including vendor upgrades.
• Critical Areas • New system software is appropriately
implemented and functions properly • All necessary modifications to system
software are implemented timely • Modifications to system software are
properly implemented and function as intended
• Value Add Areas • New system software is acquired
consistent with management’s intentions • System software is maintainable and
supportable
• Operating system acquisition, installation, configuration and updates/patches
Control Objectives Topics Covered
AUDITING APPLICATION SYSTEMS
Defining Application Controls • Application controls are those controls that pertain to
the scope of individual business processes or application systems, including data edits, separation of business functions, balancing of processing totals, transaction logging, and error reporting.
• Objective of application controls is to ensure that: – Input data is accurate, complete, authorized, and correct. – Data is processed as intended in an acceptable time
period. – Data stored is accurate and complete. – Outputs are accurate and complete. – A record is maintained to track the process of data from
input to storage and to the eventual output

(C) GoldCal LLC 2015 63
Application Systems Auditing • All key business processes are supported by application systems.
– Financial Reporting, Sales, Inventory Management, et al. • Most companies have not optimized identification of application
controls and flipped the switch on application versus manual controls
• Application systems help achieve: – Efficiency and effectiveness of operations – Reliability of financial reporting – Compliance with applicable laws and regulations
• What are application controls?
Types of Application Controls • Input Controls – These controls are used mainly to check the integrity
of data entered into a business application, whether the data is entered directly by staff, remotely by a business partner, or through a Web-enabled application or interface. Data input is checked to ensure that is remains within specified parameters.
• Processing Controls – These controls provide an automated means to ensure processing is complete, accurate, and authorized.
• Output Controls – These controls address what is done with the data and should compare output results with the intended result by checking the output against the input.
• Integrity Controls – These controls monitor data being processed and in storage to ensure it remains consistent and correct.
• Management Trail – Processing history controls, often referred to as an audit trail, enables management to identify the transactions and events they record by tracking transactions from their source to their output and by tracing backward. These controls also monitor the effectiveness of other controls and identify errors as close as possible to their sources.
Nature, Timing, & Extent of Testing • Nature of Testing will depend on if the control is
embedded or configurable • Configurable application control:
– Inspect configuration of each significant transaction type (can be performed via walkthrough also)
– Consider override capability • Other menu and record level functionality
– Generally can be viewed within a configuration screen or via a system generated report
• Embedded application control: – Walkthrough of each significant transaction type – Consider override capability – Positive and negative aspects of control
• Identify any dependencies on other controls

(C) GoldCal LLC 2015 64
Nature, Timing, & Extent of Testing • By recognizing that application controls
operate in a systematic manner, we may be able to perform testing of application controls in conjunction with the walkthrough for each applicable transaction type and processing alternative.
• We perform tests to obtain evidence that the application controls operated effectively throughout the period of reliance.
• Testing ITGC’s is the most effective way to obtain evidence that the application control have continued to operate throughout the period.
Electronic Audit Evidence (EAE) • Data generated by or processed through an
application, spreadsheet and/or end user computing solution, be it in electronic or printed form, used to support audit procedures – Data used for analytical and data analysis
procedures – Data supporting the performance of internal controls,
including key performance indicators – Data that represents substantive audit evidence to
support assertions for significant accounts • Aging list of accounts receivable • Spreadsheet specifying hedging transactions • List of gains and losses from sales of marketable securities
EAE Reliance • Establishing a basis for relying on
electronic data includes: – Determining the source of the electronic
data (which application produces the data)
– Determining, through identification and evaluation of internal controls or through substantive procedures, whether the electronic data is complete and accurate

(C) GoldCal LLC 2015 65
Testing Report Logic • Evaluate to what extent the logic of the report or
query guarantees that the report is complete and accurate
• Test procedures are determined based on risk assessment: – What is the origin of the software? – Is the report used frequently by the client? – Can the client influence the content of the report? – Can the client edit the output of the report? – Are we sure the data in the underlying database is
complete and accurate? • Test procedures are based on controls testing or
substantive testing
COMMUNICATION: PEOPLE-CENTRIC SKILLS FOR AUDITORS
Why Is Communication Important?

(C) GoldCal LLC 2015 66
SEVEN C’S TO EFFECTIVE COMMUNICATION
Clear/Coherent • Focused • No question about intention or
objective • Leave no doubt • Eliminate irrelevance • Embrace logic • Straight forward • Comprehendible
Which is more clear? • Please take care of the assignment I
emailed you a few weeks back regarding the memo on accounting.
• Brent, a few weeks back (May 12th) I emailed you concerning the accounting for our new acquisition (ABC Company). I wanted to check in and see the status of the memo. Please let me know at your earliest convenience.

(C) GoldCal LLC 2015 67
Which is more clear? • Please take care of the assignment I emailed you a few weeks
back regarding the memo on accounting. • Brent, a few weeks back (May 12th) I emailed you concerning
the accounting for our new acquisition (ABC Company). I wanted to check in and see the status of the memo. Please let me know at your earliest convenience.
Brent – I wanted to check on accounting memo on our new acquisition (ABC). Please let me know the
status as soon as possible. Thanks!
Somewhere in the middle
Concise • Minimize word usage but…. – Do not spare words for the sake of being
brief
• Use useful words, not space killers • Do keep your audience engaged and
interested
Complete/Correct • Be thorough, paint a picture • Beginning to end • Get your point across – Introduce – Support – Reiterate
• Truthful • Accurate • Honest • If you do not know, admit it!

(C) GoldCal LLC 2015 68
Captivating • Interesting • Know when to dive into an area and know
when you are giving too much detail – Subject matter must be flexible
• Command more attention and better responses
• Compelling language that encourages action • Know your objective and consistently reiterate • Well organized messages
Which is more captivating? • Thank you for your presentation this morning; it
was exciting, endearing and very engaging. I would like to follow up this presentation with a request for the presentation slides as I would like to pass them on to my superiors. Thank you so much.
• Thanks.
Question – Is the latter too concise?
Conversational • Easy to follow and understand • Speak with an audience, not to them • Personalize the experience, make
them connect

(C) GoldCal LLC 2015 69
Courteous • Professional demeanor • Friendly • Approachable • Talk with not to
Concrete • Specifics and certainty • No ambiguity • Direct and to the point
GENERAL COMMUNICATION ISSUES & CONFLICT MANAGEMENT

(C) GoldCal LLC 2015 70
Personal vs. Professional • Separation of Church vs. State or
Personal vs. Professional • Know the difference • Be emotionally-savvy (recurring theme
throughout the course) • Personal attack vs. getting to the root
of the problem • Casualness of emails (know your
audience)
Miscommunication • #1 cause of unnecessary conflict – Happens in many cases due to the mode
of communication • Emotion/feelings are difficult to interpret via
email, Blackberry, IM, etc.
• People always fear the worst outcome – “Hey, can we talk?”
• Assumptions take on a world of its own
Optimize Your Conflict Resolution • Personally confront the issue • Make your initial statement and stop talking • Avoid arguing during the confrontation • Know the resolution you want prior to the
confrontation • Focus on the real issue of the confrontation • Acknowledge feelings

(C) GoldCal LLC 2015 71
Fact Conflicts • Conflicts over facts are usually the easiest to
resolve since facts are subject to independent verification
• In these cases, the questions will concentrate on gathering the information needed to confirm or refute the facts
• Once everyone is satisfied that the facts are correct, the conflict will be resolved
• Walk through the steps to lead to the conclusion – gain agreement on each step
Feelings & Perceptions • Well-intentioned recommendations may
sometimes be perceived as criticisms or even accusations
• The natural human response to a perceived threat is “fight or flight”
• Defensive and making excuses – Make the situation not personal – Look for cost/benefit – Respect the other person – who knows more? – Make sure they understand – you are doing
your job
Personalities • We are not psychologists • Researchers have found that most
differences in working styles result from differences in two basic characteristics: 1) Ask vs. tell 2) task-oriented vs. people-oriented
behavior • Manage the situation and person

(C) GoldCal LLC 2015 72
Individual Values • May be no immediate resolution • Generally not subject to negotiation or
compromise • Asking questions about fundamental
values can actually be counter-productive – Avoid deep conflict – Stay at a higher level – Find a mutual ground/understanding
EMAIL EXCELLENCE
Caution – Be Careful What You Send • Email can hang around forever • Your emails can be subpoenaed • You may be called to explain or defend
something you emailed years later • Regardless of personal or business

(C) GoldCal LLC 2015 73
Caution – Be Careful What You Send Try to avoid: • Making accusations of fraud or error via email • Making personal attacks or derogatory comments
about others • Sending confidential, classified or personal
identifiable information (like SS#’s, etc.) via email • Blunt statements (I will respond to you at my earliest
convenience) • Emotional responses
Best Practices - Practical Tips to Improving Your Email Skills
• Clarity is key • Understand your audience • White space is good • It’s not just what you say, but how you say it • Never send an email angry • Don’t forget about verbal communication • Consider what you are communicating • Ambiguity in tone
Typical Bad Practices • Blank or non-descriptive subject lines • Reply to all • One-liners • Address exposure • BCC

(C) GoldCal LLC 2015 74
Misc. Email • Keep relevant emails
– Create and utilize folders (easy to find)
• Who do you CC and BCC? – CC relevant parties but watch over CCing; do they really need to
be on the email string? – Use BCC sparingly
• Utilizing read receipts – Only use if you feel this is very necessary. Remember – recipient
receives notice that read receipts are being utilized; not readily accepted in the workplace
• Personal emails – Nothing via email is personal – watch usage
INSTANT MESSAGING
Leading Practices • Knock, Knock – Anyone There? • Concision is Key • Be Professional • Watch Emotional Responses • What are we Trying to Accomplish? • Speed is Key!

(C) GoldCal LLC 2015 75
AUDIT INTERVIEWING BASICS
What is an Audit Interview? • Small, personal, controlled
conversational meeting in which auditors obtain needed information from people who have it.
• Conversation with an agenda.
Interview = Evidence? • Four kinds of audit evidence: – Physical – Documentary – Analytical – Testimonial
• QUESTION – Which is the strongest and which is the weakest?
• QUESTION – What is an interview?

(C) GoldCal LLC 2015 76
Interview Evidence • STRONGEST = Physical • WEAKEST = Testimonial • Interviewing is……
• Allegations/Opinions are NOT evidence.
Steps in the Audit Interview Process ① Planning/
Preparation
a. Objectives b. Types of Questions c. Background on
Interviewee d. Information
Requests e. Participants f. Location g. Time
② Conducting the Interview
a. Agenda b. Environment
i. Interviewer(s) ii. Participant(s)
c. Interview Variations d. Recording the
Interview e. Ending the Interview
Steps in the Audit Interview Process
③ Interview Results a. Professional
Skepticism b. Documenting the
Interview
④ Follow Up

(C) GoldCal LLC 2015 77
INTERVIEW PREPARATION
Managing Yourself - Interviewing Interview
“A meeting at which
information is obtained from a person.”
Merriam-Webster
Managing Yourself - Interviewing Preparation – Objective(s) • Clearly defined • Documented • Understood by interviewer(s) • Foundation of questions and
information requests

(C) GoldCal LLC 2015 78
Types of Interview Questions Type Advantage
Open Ended Detailed explanations and descriptions; conversation can veer in numerous directions
Closed Simple Information, Yes/No
Qualifying Establishes witness credibility
Range Provides general areas
Motives Reveals why people did/did not do
Opportunity Reveals whether people could have done
Lead to Others Sets stage for subsequent questions
More Info Asks that more information be provided
GROUP EXERCISE –INTERVIEW QUESTIONS #1
Interview Questions • You are performing an audit of an
area you have not audited before and you have limited information on the auditee and the business area.
• Please list, in order, the questions you would ask (at least 10) YES/No Questions.

(C) GoldCal LLC 2015 79
Questionnaires • Can be more efficient than the open-
ended interview • Yes/No Questions will drive Yes/No
Answers • Questionnaires are not very valuable
without open-ended follow-up
Creating a Standard Questionnaire • Use a variety of questions such as yes/no, ratings
from best to worse and request explanations. • Make the questions as simple as possible so your
interviewees can understand and answer them in the same way.
• Standardize as much as possible but know they limit the answer given (make it easier on the employee)
• Leave plenty of white space for answers • Be sure questions can only be answered one way,
with the exception of explanation questions. • Make sure range options are very specific. • Review and test prior to using the questionnaire.
Managing Yourself - Interviewing Participants • Individual or Group • Information Dependent • Backgrounds • Personality Styles (Driver, Expressive,
Amiable, or Analytical)

(C) GoldCal LLC 2015 80
Background on Interviewee • Do your homework • Review old workpapers and PY audit
work • Ask other auditors about interviewee • Google….
Managing Yourself - Interviewing Time • Number of Questions
and Information Requests
• Availability of Participants
• Number of Participants
• Interview Venue • Use of Pre-reads and/
or Questionnaires
Eight Stages of an Interview 1. Defining its purpose 2. Identifying information needed from
interviews 3. Identifying people to interview 4. Preparing for the interview 5. Conducting and controlling the interview 6. Recording the interview 7. Analyzing the results 8. Documenting the analyze results in the
working papers

(C) GoldCal LLC 2015 81
LISTENING TECHNIQUES
Listening Skills • Depending on the study being quoted,
we remember a dismal 25-50% of what we hear.
• Good communication skills require a high level of self-awareness. By understanding your personal style of communicating, you will go a long way towards creating good and lasting impressions with others.
• Become an active listener and eliminate bad habits!
Listening Optimized (1 of 2) • Ignore phone calls during the conversation
and abstain from multitasking • Look at the other person and focus on the
words and meanings – Content and intent
• Avoid interruptions • Resist jumping to conclusions • Concentrate on the flow and back and forth
of the conversation, rather than becoming hung up on bits of information or parts of past conversation

(C) GoldCal LLC 2015 82
Listening Optimized (2 of 2) • Take on the responsibility of listening:
being bored, not liking the speaker, or disagreeing with what he or she has to say does not excuse you from actively listening
• Consider body language and respond with both words and actions, taking into account your own body language and concern
• Restate key points to ensure accuracy and prevent potential misunderstandings
Active Listening • When the listener provides feedback
(verbal and/or non-verbal) to the speaker demonstrating to that the speaker’s message has been understood and will be retained.
• Active Listening Involves: – communicating verbally and nonverbally – practicing “uninterrupted” listening – restating the message – observing the sender’s nonverbal signals
Why practice active listening? • Helps us understand others better • Show others we respect them • Allows us to receive accurate
messages • Enables us to respond appropriately

(C) GoldCal LLC 2015 83
Attending posture Nonverbal skill = SOLER • S= squarely face person • O= use open posture • L= lean toward the person • E= use eye contact • R= relax, keep it natural
SOURCE: According to Gerald Egan, author of the supplement “Skilled Helper: A Problem-Management Approach to Helping.
Verbal Active Listening Techniques (1 of 2)
• Using encouraging words and reassuring sounds to convey interest (“I see.”)
• Restating in your own words what the person said
• Repeating exactly what the person said (“Mirroring”)
• Reflecting to show you understand how they feel (“You were pretty upset by this…”)
Verbal Active Listening Techniques (2 of 2)
• Probing the interviewee’s initial response in order to expand and/or clarify the information given (“Please tell me more about that”)
• Summarizing (“these seem to be the main ideas you stated”)

(C) GoldCal LLC 2015 84
Nonverbal Listening • Facial Expressions – eye/eyebrow movements
and smiles, frowns and grimaces • Gestures – Hand & arm gestures are numerous
Look for open or closed arms and hands for sincerity or obstruction.
• Postures – Shows attitude and feelings. Sitting or standing in straight or slouched positions for example.
• Environment – open, comfortable office arrangements indicate sociability, while close arrangements indicate control or self-protection.
Barriers to Active Listening (1 of 2) • Not keeping an open mind by letting
biases interfere • Jumping to conclusions • Interrupting or debating the
interviewee: seek understanding first! • Monopolizing the conversation (70/30
rule) • Thinking ahead to your next question
Barriers to Active Listening (2 of 2) • Reading documents provided by the
presenter • Not suppressing disruptive habits such
as finger drumming or pencil tapping • Assuming you know what the presenter
meant and not requesting clarification

(C) GoldCal LLC 2015 85
FUTURE TRENDS AND TECHNIQUES
Pulse of Internal Audit 370 Completed Surveys
• October 2014 • 7th consecutive year • 63% Public/Private
companies • 84% CAEs and Directors (311
responses) • 92% internal audit managers
or above
311 Responses From CAEs and Directors • 28% Finance and Insurance • 14% Manufacturing • 10% Educational services • 7% Healthcare and social
assistance
Surveys & Demographics
CBOK 12,570 completed the survey
• Q1 2015 • Conducted every five years • 32% CAEs and Directors/Sr.
Managers (4,043 responses) • 28% North American participants • 878 CAEs and Directors/Sr.
Managers from North America
878 Responses From CAEs and Directors/Sr. Managers in North America • 30% Finance and Insurance • 10% Healthcare and social
assistance • 10% Manufacturing • 8% Public Administration
Sources: The Pulse of Internal Audit survey: © 2015 The IIA Audit Executive Center conducted in collaboration with the 2015 Common Body of Knowledge Study, © 2015 The IIA and The IIA Research Foundation. All rights reserved. No part of this data may be copied, reproduced or otherwise disseminated without explicit permission from The IIA.
• Assessing emerging and evolving risks
• Linking risks and audit coverage
• Navigating an emerging talent shortage
• Address gaps in quality assurance and improvement
Five Priorities for 2015!

(C) GoldCal LLC 2015 86
Source: The CBOK 2015 Global Internal Audit Practitioner survey: : © 2015 The IIA Research Foundation
• Stakeholders often expect base level of coverage: o Financial risks o Regulatory risks o Compliance risks
• Once base is addressed: o Operating risks o IT risks
• Only then, is there interest in strategic and business risks
• The paradox: o Base level coverage
often provides the lowest perceived value
34%
46%
20%
Linking Risks and Audit Coverage: The Paradox of “Structural Expectations”
They Add Value by:
1. Identifying improvement opportunities
2. Mitigating risk 3. Increased efficiency 4. Stronger corporate
governance 5. Stronger financial controls
compliance
Barriers Include:
1. Budget constraints (60%) 2. Talent quality or capacity
(47%) 3. Focus on financial controls
and compliance (43%) 4. Perception of internal audit
(40%) 5. Organizational politics (40%)
Source: “Competing Priorities: Are CAE and audit committee priorities in sync?” © 2015 Grant Thornton LLP
Delivering Internal Audit Value: According to Grant Thornton, CAE’s Believe
Source: The CBOK 2015 Global Internal Audit Practitioner survey: : © 2015 The IIA Research Foundation Survey respondents were asked to estimate the distribution of their audit plan coverage. This figure reflects a summary of the data.
Total “Financial”
16%
Audit Plan Coverage in 2015

(C) GoldCal LLC 2015 87
• Undertake a comprehensive assessment • Develop an audit plan based on the “real
risks” • Identify resources and expertise gaps • Formulate strategies for addressing gaps • Have candid conversations with
management and the audit committee regarding: • Resource shortfalls • Expertise gaps • Risks that may fall victim to resources • A plan of action
• Develop a long-term strategy for addressing gaps
• Don’t let the “tail wag the dog”
“Disclosing the gaps in risk coverage and discussing the resources needed to address the gaps is essential.” • Joe Steakley, CAE
of Hospital Corporation of America
Linking Risks & Audit Coverage: Key Imperatives
Internal audit functions providing significant value have more diversified skill sets:
The talent gap is “fueling a poor perception of internal audit’s relevance and value: 65 percent of stakeholders who do not find value in the internal audit functions cite talent as a top barrier.” - PwC
Source: 2015 State of the Internal Audit Profession Study, © 2015 PwC
Navigating an Escalating Talent Shortage: PwC’s View
Skill Sets
Business Continuity 84%
Data Privacy 80%
Specialized IT 77%
Data Analytics 72%
Supply Chain 69%
AUDITING EMERGING RISKS

(C) GoldCal LLC 2015 88
• 93 percent use risk-based methodologies when planning
• But, emerging risks present a challenge
• Risks often materialize with little or no warning
• Decades of accumulated value can evaporate
• We must be able to “audit at the speed of risk”
Assessing Emerging and Evolving Risks
Assessing Emerging/Evolving Risks • Industry Trends (what is in the news) • ERM – predicting changes over 5+
years • Change to ERM -> Change ARM &
Audit Plan
• Assess existing risk assessment maturity
• Develop/refine processes to identify and report on emerging risks
• Assess existing processes for updating the annual audit plan
• Obtain stakeholders’ input on the need for frequent updates
• Develop/refine audit reporting to demonstrate a stronger link between changes to:
o The organization’s risk profile
o Associated changes to the audit plan
Continuously Assessing Emerging and Evolving Risk – Key Imperatives

(C) GoldCal LLC 2015 89
DYNAMIC RISK ASSESSMENT PROCESS
Source: The Pulse of Internal Audit Survey Conducted in collaboration with the 2015 Common Body of Knowledge Study, © 2015 The IIA and The IIA Research Foundation. All rights reserved. No part of this data may be copied, reproduced or otherwise disseminated without explicit permission from The IIA.
Continuous Risk Assessment is Still Aspirational for Many
How frequently does internal audit conduct a risk assessment? Frequency
Annual assessment without formal updates
38%
Annual assessment with periodic formal updates 41%
Continuous assessment 13%
Never (Internal audit does not conduct a risk assessment.)
4%
Other 4%
SOURCE: IIA/Richard Chambers Presentation “Pulse of Internal Audit” to the FTW IIA, September 4, 2015
How are We Assessing Risk? • How many are performing a formal
annual risk assessment? • How many are performing a formal
engagement-level risk assessment? • What is the process? – Numerical/Ratings? – Interviews? – Questionnaires? – Surveys?

(C) GoldCal LLC 2015 90
Source: The Pulse of Internal Audit survey: © 2015 The IIA Audit Executive Center. No part of this data may be copied, reproduced or otherwise disseminated without explicit permission from The IIA.
Continuous Risk Assessment Methodologies
The degree to which internal audit utilizes these methodologies to continuously assess risk
Very/Extensively Utilized
Periodic manual monitoring of KRIs 27%
Using technology to continuously monitor KRIs 10%
Periodically interview management to identify changes in the organization's risk profile
71%
Initiate formal updates of the internal audit risk assessment & audit plan
60%
Initiate informal or ad hoc updates of the internal audit risk assessment & audit plan
61%
Periodically update risk assessment based on changes to risk ratings identified during ongoing audit operations
54%
AUDIT TRANSPARENCY
Audit Transparency • Do You Share Your Risk Assessment with
Your Auditees? • Do You Post Your Audit Plan for the
Year? • Do You Give Your Auditees Your
Workprogram During Planning?

(C) GoldCal LLC 2015 91
MARKETING INTERNAL AUDIT
3 Pillars of Marketing internal audit Consistent Messaging • Define Internal
Auditing • Focus on
Objectives • Marketing Plan • Marketing Sheet • Outreach w/ new
managers • Periodic outreach
w/manager (take the pulse)
• Intranet Site
Continuous Education • Alleviate the Fear • Focus on “Value” • Brown Bag
Lunches • Newsletters • Email with Issues/
Findings • Don’t Use
Independence as an Excuse
Transparency • Try to Help • Try Not to Hide
Anything • Walk Auditees
through ARA • Post the Audit
Plan • Give Auditees
Audit Work program (Path to Success)
COMMUNICATION & CRITICAL THINKING

(C) GoldCal LLC 2015 92
Top Skills Being Recruited or Built in Internal Audit Departments
Source: The CBOK 2015 Global Internal Audit Practitioner survey: : © 2015 The IIA Research Foundation
Navigating an Escalating Talent Shortage
Skills Recruited or Built Recruited Essential
1 Analytical/Critical Thinking 74% 96%
2 Communication Skills 57% 96%
3 Data Mining and Analytics 48% 44%
4 Industry-specific Knowledge 43% 69%
5 IT (general) 42% 43%
6 Business Acumen 40% 80%
7 Accounting 31% 48%
8 Risk Management Assurance 27% 40%
Course Summary • Understand and Manage Expectations • Over-communicate – Transparency is
Key! • Ask for More and Ask for Feedback!