Approaches for Ensuring Security and Privacy in Unplanned Ubiquitous Computing Environments V....
-
Upload
johnathan-york -
Category
Documents
-
view
215 -
download
0
Transcript of Approaches for Ensuring Security and Privacy in Unplanned Ubiquitous Computing Environments V....

Approaches for Ensuring Security and Privacy in Unplanned Ubiquitous
Computing Environments
V. Ramakrishna, Kevin Eustice, Matthew Schnaider
Laboratory for Advanced Systems ResearchComputer Science Department, UCLA

In a Nutshell
Ubiquitous computing poses new security and privacy challenges,
… and exacerbates existing ones Usability goals necessitate security and
privacy tradeoffs Threat mitigation is a more realistic goal than
threat elimination 3-layer classification of the solution space
helps in better analysis and understanding

Ubiquitous Computing
Internet
Home Network
Coffee ShopPHYSICAL INTEGRATION
SPONTANEOUS INTEROPERATION
No Milk !
Characteristics
Decentralized controlHeterogeneityAd hoc interactionsOpen environmentsCommunication with strangers
Personal Network
Location (GPS)
Video
Change route!
My location?

Trading off Security and Privacy with Usability Usability for naïve users
• Ease of handling and interfacing with devices• Minimal required interaction• Primary goal of ubicomp
Characteristics of ubiquitous computing environments forces three-way tradeoff
Examination of tradeoffs enable better understanding of system security limits
We need to seriously think about security before it is too late … again

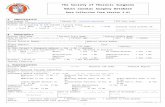
Security and Privacy Challenges
GPS
N/W Infrastructure
N/W Infrastructure
Coffee Shop
Home Network
Small devices areprime targets for
theft.
Who is my serviceprovider?
Is he authentic?
More devices becomevectors for
spread of malware.
Mobile code posessignificant threats.
Privacy concerns:Eavesdropping on
Conversations;Location inference.
Install Plug-in

Mitigating Failure
Problem areas• Theft of devices and content
• Applications releasing more data than necessary
Applicable paradigms• Least privilege
• Abdication of privilege
• Segregation of functionality
• Multiple fidelity levels for contextual info

Establishing Identity
Leverage physical presence Enrollment: secure sideband interaction
• E.g., USB drives and PKI
• Physical contact creates logical connection
• Reduces dangers of anonymity
Sensory mechanisms for authentication• Infrared, RFID tags
• Embedded cameras, barcodes
• Audio cues

Protecting Devices: A 3-Layered View
DEVICE / NETWORK
RESOURCES DATA
CONTROLLING / OWNINGENTITY
Resource and ContentProtection Mechanisms
Secure Interaction Protocols
Trust Frameworks and Mechanisms
DEVICE / NETWORK
RESOURCES DATA
CONTROLLING / OWNINGENTITY
Resource and ContentProtection Mechanisms

Benefits of this Classification
Analyze vulnerable ubicomp interactions in a top-down manner
Demarcates scope of each solution
Complementary, yet interdependent systems of defenseResource and Content
Protection Mechanisms
Secure InteractionProtocols
Trust Frameworksand Mechanisms
DEVICE / NETWORK
RESOURCES
DATA
CONTROLLINGENTITY

Resource / Content Protection
Examples• Access control lists
and capabilities
• Secure file systems
• Zero-interaction authentication
• Firewalls
• Proof-carrying codeResource and ContentProtection Mechanisms
Secure InteractionProtocols
Trust Frameworksand Mechanisms
DEVICE / NETWORK
RESOURCES
DATA
CONTROLLINGENTITY

Secure Resource Discovery and Access
Enforcing security policies through communication protocols
Examples• Protecting networks from
vulnerable nomads
• Automated negotiation among peersResource and Content
Protection Mechanisms
Secure InteractionProtocols
Trust Frameworksand Mechanisms
DEVICE / NETWORK
RESOURCES
DATA
CONTROLLINGENTITY

Safeguarding Nomadic Behavior
Network firewalls are inadequate
Some solutions• Quarantine, Examination
and Decontamination
• Cisco Network Admission Control
These solutions only scratch the surface
Open issues:• Running foreign code
• Verifying veracity of returned results
• Leveraging trusted hardware
MOBILITY:Vulnerable Devices
+
OPEN NETWORKS:Offering Ubiquitous
Services
EPIDEMIC:Spread of malware
+
CONTACT withSTRANGERS

Automated Peer Negotiation
Facilitate interactions among strangers Decentralized policy resolution Compromise on resource sharing Use trust model and utility model to
determine risk/benefit tradeoff of action

Evaluating and Using Trust
Cross-domain frameworks: trust as a basis for interaction among entities
Possible approaches• Globally centralized?
• Certificate hierarchies
• Webs and chains of trust, delegation
• Quantitative trust models
Resource and ContentProtection Mechanisms
Secure InteractionProtocols
Trust Frameworksand Mechanisms
DEVICE / NETWORK
RESOURCES
DATA
CONTROLLINGENTITY

Future Targets and Promising Approaches Problems inherent in infrastructure?
→Work around it (e.g., enrollment) Mobility increases number of threats?
→Flexible guards and enforce compliance (e.g., QED) Unplanned interactions may violate security
policy?→Automated negotiation among peers→Least privilege paradigm
Must communicate with strangers?→Leverage trust as far as possible→Develop better models for trust inference and use

Conclusion
Ubicomp poses new security and privacy challenges, and exacerbates existing ones
Usability goals necessitate security and privacy tradeoffs
We should direct our efforts toward threat mitigation rather than threat elimination
A 3-layer classification of the solution space helps in better analysis and understanding
In practice, a hybrid solution will yield best results

References
For more info, contact•[email protected]
Panoply project web page•http://lasr.cs.ucla.edu/panoply