626 Information leakage and Data Loss Prevention Tools
-
Upload
splitty -
Category
Technology
-
view
1.083 -
download
1
description
Transcript of 626 Information leakage and Data Loss Prevention Tools
Information Leakage
• Any event, either accidental or malicious, that allows an unauthorized party to access data that is not already public information
Information Leakage
• How? – Negligence 40%, System glitch 36%, Malicious
attack 24%
• Why?– Advances in data storage technology– Proliferation of consumer technology in corporate
IT environment
Examples of Information Leakage
• Sony Playstation network data breack– As of May 24, 2011: $171 million in costs
• 1,000 laptops go missing daily; only 3% recovered
• National Institute of Health lost a laptop with unencrypted patient data
Costs of a Data Breach
• Regulatory fines• Increased government oversight• Loss of customer trust• Reputational damage• Loss of proprietary business intelligence• $6.75 million– The total data breach cost in the US in 2009
DLP: What should it do?
• Manage the data• Discover sensitive data• Monitor the use of sensitive data• Protect the sensitive data
Protecting Data: The 3 States
• Data in Motion– Data leaving the organization in a email or other
network
• Data at Rest– Data stored in an internal server within the organization
• Data in use– Data being used by users in the laptop, USB storage
devices, or CDs
DLP in Action
• Crawls through the firm’s servers to search for sensitive data as defined by the user
• Monitors network traffic and blocks transmission of sensitive data
• Applications that limit a user’s ability to download and save sensitive data on their laptops
DLP and Encryption
• Last line of defense if DLP fails to prevent sensitive information from leaving the organization
• However: DLP tools CANNOT locate, monitor, or scan encrypted data
• Organization need to allow the DLP tool to have access to the decryption keys
DLP: Beyond the Technology
• Technology and applications are only as good as the people who operate it
• Educate users about data leakage consequences
• Empower employees to take responsibility of data
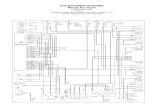
Implementation: Analyzing Processes and Data Flows
• Analyzing business processes and data flows• Information life cycle• Understand the government regulations that
governs that data the company owns• Classify data into different categories: public,
private, sensitive, business intelligence, etc.• Recommended to use a DLP application to crawl
through the server to locate all sensitive data
Implementation: Risk Assessment
• Need to prioritize data based on its risk (probability of loss * impact of loss)
• Allows for priorization– Without it, IT department and users will be
overloaded by data and data usage warnings• Exercise judgment in DLP strategy
Implementation: Applying Controls
• Training employees about new processes and technologies
• Use of encryption, traffic monitoring, security over USB ports
• Testing the controls
Implementation: Monitoring and Improvements
• Take lessons learned to implement DLP program to other sets of data
DLP Checklist
• What sensitive data do we own? • Where is this data stored?• What is the information life cycle of the data?• What are the regulatory requirements
regarding the data we own?• What is the risk prioritization of each classes
of data?
DLP Checklist
• What controls are currently in place?• What additional controls do we need to
address each classes of data?• Does our staff have the capabilities to operate
the new business processes/controls/technologies?
• How do we apply the DLP program in compliance with the firm's change management policy?
Limitations of DLP
• Cannot detect/monitor encrypted data without a decryption key
• Cannot interpret graphic files– Employees can “print-screen” and send it out
DLP on a Tight Budget
• Communicate to employees and raise awareness
• Move critical files off laptops to an offline desktop
• Change local shared storage access settings• Talk to email host about filtering outbound
emails to authorized email addresses only
























![Dies Irae - Requiem in D Minor K. 626 [K. 626]](https://static.fdocuments.in/doc/165x107/616e2e726c1eb666d037d848/dies-irae-requiem-in-d-minor-k-626-k-626.jpg)