3-Basic-Techniques-2 - cs.ru.nljhh/secsem/slides/3-Basic-Techniques-2.pdf · jan jansen...
Transcript of 3-Basic-Techniques-2 - cs.ru.nljhh/secsem/slides/3-Basic-Techniques-2.pdf · jan jansen...

22-03-18
1
Jaap-Henk Hoepman
* [email protected] // 8 www.cs.ru.nl/~jhh // 8 blog.xot.nl // @xotoxot
Privacy & Identity LabRadboud University
Tilburg UniversityUniversity of Groningen
Privacy SeminarBasic Techniques II
Jaap-Henk Hoepman //
Signal’s rachet
n Start with a root key !n Alice uses ephemeral DH keys
(#$, &$ = ()*); Bob similarly● Advertise &$ with every message
● Generate next key &$,- whenreceiving (correct) ./ from Bob
n Whenever Alice generates new ephemeral key, advance the root
● !’ ← ! #23 #$,- #23 ./● Derive hash rachet key H = ℎ(!’)● Hash this with every new message
sent/received 6’ = ℎ(6)● Derive message key 7 = ℎ 6
30-01-2018 // Privacy by design 2
Jaap-Henk Hoepman //
Hiding metadata
● Mixnetworks
● Onion routing
● DC networks
n Discussed in several other TRU/e courses…
11-2-2016 // Privacy Enhancing Technologies 3

22-03-18
2
Homomorphic encryption
Jaap-Henk Hoepman //
(Partial) Homomorphic encryption
n A public key encryption protocol !": $ ↦ &● From plaintext space $, with group operation +● To ciphertext space &, with group operation ×
n Such that● !" ) + * = !" ) ×!" * andhencealso 6×!" ) = !" ) 7
n Example: Paillier (1999)
n What can you do with homomorphic encryption● Jointly compute the sum of private values, e.g. smart grid
● Electronic voting
11-2-2016 // Privacy Enhancing Technologies 5
Private information retrieval
30-01-2018// Privacy by design 6

22-03-18
3
Jaap-Henk Hoepman //
Private information retrieval
n User wants to access record !" from a remote database with # records, without revealing $ to the database
n Obvious but bad solution● Send the whole database to the user; this costs # bits
n Q: can we do better?
n A: yes, if we assume the database is split over % non-colluding servers● Also with 1 server, but then not information-theoretically secure
11-2-2016 // Privacy Enhancing Technologies 7
Jaap-Henk Hoepman //
PIR (k=2)
n Two non-colluding servers with a copy of the database !", … . , !&n User generates a set ' by randomly deciding for each ( ∈ {1, … , ,}whether j ∈ ' or
not, with / = 0.5n User sends ' to server 1 and J ∪ 5 to server 2
● I.e. sends two bit vectors of length ,● Only 5 occurs in one of these bit vectors; all other j either in both or in none● The fact that some bit is 0 or 1 does not say anything about whether this is the index the
user is interested in.
n Each server computes 6 =⊕8∈9 !8 for the set ' it receives and returns 6 to the user● I.e. this message is as large as a single record
n The user receives 6, 6′ and computes !; = 6⨁6′● This equals !; because for all ( ≠ 5 we have either !8 included in both 6, 6’ or none
n Bit complexity 2, plus the record size
11-2-2016 // Privacy Enhancing Technologies 8
Blind signatures & anonymous e-cash
11-2-2016// Privacy Enhancing Technologies 9

22-03-18
4
Jaap-Henk Hoepman // 11-2-2016 // Privacy Enhancing Technologies 10
Blind signatures: Digicash
issuer acquirer
mon
eyflo
at
�
�
�
�
�
�
�
clearing & settlement
Jaap-Henk Hoepman //
Blind signature
11-2-2016 // Privacy Enhancing Technologies 11
Jaap-Henk Hoepman // 11-2-2016 // Privacy Enhancing Technologies 12
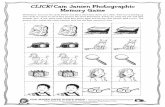
DigiCash offline coinjan jansen
blind signature
jan jansenjan jansenjan jansenjan jansenjan jansenjan jansenjan jansenjan jansenjan jansenjan jansen
coin number1 $
jan jansen
jan jansen
01001001.. 10100011..
zdd 01001001.. + 10100011.. = Jan Jansen

22-03-18
5
Jaap-Henk Hoepman // 11-2-2016 // Privacy Enhancing Technologies 13
Coin depositjan jansen
blind signature
jan jansenjan jansenjan jansenjan jansenjan jansenjan jansenjan jansenjan jansenjan jansenjan jansen
coin number1 $
jan jansen
jan jansen
random
L,R,R,R,L,L, ..
merchant bank
jan jansen
jan jansenjan jansenjan jansenjan jansenjan jansenjan jansenjan jansenjan jansenjan jansenjan jansen
coin number1 $
jan jansen
jan jansen
Zero-knowledge protocols
11-2-2016
// Privacy Enhancing Technologies 14
Jaap-Henk Hoepman //
Zero knowledge
n The cave of Ali Baba
11-2-2016 // Privacy Enhancing Technologies 15

22-03-18
6
Jaap-Henk Hoepman //
Proofs of knowledge
n Completeness ● Verifier accepts the proof if the assertion is true
● Assumption: the parties follow the protocol
n Soundness● If the fact is false, the verifier rejects the proof
● Assumption: the parties follow the protocol
n Zero knowledge● No information about the prover’s private input is revealed to the
verifier
● The verifier cannot convince a third party of the correctness of the assertion
11-2-2016 // Privacy Enhancing Technologies 16
Jaap-Henk Hoepman //
Schnorr protocol
n Cyclic group G with generator g
11-2-2016 // Privacy Enhancing Technologies 17
Jaap-Henk Hoepman //
n Completeness?
n Soundness?
n Zero knowledge?
11-2-2016 // Privacy Enhancing Technologies 18

22-03-18
7
Attribute based credentials
19
Jaap-Henk Hoepman //
Attribute based credentials (ABC)
11-02-2015 // IRMA: Current status and future developments 20
Proving an attribute about yourself (age, nationality, preference, …) without revealing your full identity
Jaap-Henk Hoepman //
I Reveal My Attributes
11-02-2015 // IRMA: Current status and future developments 21
http://rivacybydesign.foundation

22-03-18
8
Jaap-Henk Hoepman //
Credential
n Secure container
n Issued and signed by credential issuer
n Contains attributes, selectively disclosable
11-02-2015 // IRMA: Current status and future developments 22
Jaap-Henk Hoepman //
Using such credentials
n Anonymous● Concert tickets (>16,>18,event,seq. no)
● Age verification (>16, >18 or <60, <65)
● Public transport year/track pass (type, period,class)
n Pseudonymous● Loyalty card (card number)● Online newspaper member (membership type, number)
● Role based access control (military rank, clearances)
n Identifying● Passport-like (name, BSN, address)
● Student card (student number, institute)
● Emergency health info (name, blood group, allergies)
11-02-2015 // IRMA: Current status and future developments 23
Jaap-Henk Hoepman //
Identity management: traditional
11-02-2015 // IRMA: Current status and future developments 24
Identity Provider Relying Party
User
attributes
request serviceSign
in
All parties are on lineSecurity and privacy
risks

22-03-18
9
Jaap-Henk Hoepman //
Security issues
n IdP is single point of failure● Treasure trove of personal data
● Risk of surveillance
n The janitor story….
n Increased risk of phishing● Authenticity of IdP hard to establish
n How many identities should one have?
n Federations are risky● RP interprets attribute differently from IdP
13-7-2015 // Privacy and Identity Management 25
Jaap-Henk Hoepman //
Privacy issues
n Linkability across scopes
n IdP knows all user transactions
13-7-2015 // Privacy and Identity Management 26
Jaap-Henk Hoepman //
Usability issues
n Location independence● Sign in from anywhere
n “Who am I today?”● Allow people to choose roles
n When complex transactions require multiple credentials...
n User profile management● User data scattered over IdP and RP….
● CMR instead of CRM
13-7-2015 // Privacy and Identity Management 27

22-03-18
10
Jaap-Henk Hoepman //
Identity management: ABC based
11-02-2015 // IRMA: Current status and future developments 28
Credential Issuer Relying Party
User
Issue
cre
dent
ial
Jaap-Henk Hoepman //
Identity management: ABC based
11-02-2015 // IRMA: Current status and future developments 29
Credential Issuer Relying Party
User
Show/reveal credentialunlinkable Has certificate granting
access to attributes
Jaap-Henk Hoepman //
ABC Properties
n Unforgeable
n Unlinkable● Issuing with disclosing, and
● Between two disclosures
n Revocable
n Non transferable
n (Inspectable)
// Privacy and Identity Management 3013-7-2015

22-03-18
11
Jaap-Henk Hoepman //
Three techniques
n Idemix (IBM) : proof ownership in zero knowledge● Rich feautureset
● Reusable credentials
● Resource intensive
n Uprove (Microsoft) : blind issuing● Average featureset
● Single show credentials
● Efficient
n Self blindable (RU / TNO) : rerandomise● Limited featureset
● Reusable credentials
● Efficient
19-04-2012 / Anonymous credentials in practice 31
Jaap-Henk Hoepman //
The IRMA card (outside)
n Outside n Contactless● NFC phones/tablets as terminals
n Inside● Multos (Infineon)
● SmartMX (NXP) is option
n Credentials ● Idemix (by IBM)
● 1024 bit
// IRMA: Current status and future developments 3211-02-2015
Jaap-Henk Hoepman //
The IRMA terminals
// IRMA: Current status and future developments 3311-02-2015

22-03-18
12
Revoking attribute based credentials
30-01-2018// Privacy by design 34
Jaap-Henk Hoepman //
Revoking ABCs
n White-listing● Inefficient for applications with many users
n Accumulator based● Verifiers have accumulator A representing all valid credentials.
Simplified: ! = #$%$&…$(
● Prover i has witness : W = #$%$&…$*+% $*,%…$(● Prover proves possession of -, #$* and proves that ./ is part of
credential.
n Black-listing
13-7-2015 // Privacy and Identity Management 35
Jaap-Henk Hoepman //
Verifier local revocation
n Revocation authority maintains list MRL of revoked credential
n Every epoch, each verifier gets a personalised list of revoked credentials RL● This prevents verifiers to track users across verifier domains, and
across epochs
n Verifier sends current epoch to the prover● Prover knows last seen epoch, so no turning back of clocks…
● Prover computes epoch/verifier specific challenge
● Is the same during the epoch, and for one verifier
n Prover proves his credential is not on the list, using this challenge
13-7-2015 // Privacy and Identity Management 36

22-03-18
13
Jaap-Henk Hoepman //
Verifier local revocation
n Revoked credentials MRL = %& … %(n Epoch/verifier specific generator )*,, = -(/, 0)n Verifier gets 23*,, = )*,,45 , … . , )*,,47 , sorted
n Verfier sends /, 0 to the prover● These values are signed by Revocation Authority
n Prover with revocation value %● Computes )*,, = -(/, 0)● Computes 2 = )*,,4 and sends this to the verifier
● Proves % is part of used credential
n Verifier checks that 2 ∉ 23
13-7-2015 // Privacy and Identity Management 37
Private handshaking
11-2-2016
// Privacy Enhancing Technologies 38
Jaap-Henk Hoepman // 11-2-2016 // Privacy Enhancing Technologies 39
Spot the Fed

22-03-18
14
Jaap-Henk Hoepman // 11-2-2016 // Privacy Enhancing Technologies 40
Private handshake
Jaap-Henk Hoepman //
Requirements
11-2-2016 // Privacy Enhancing Technologies 41
Jaap-Henk Hoepman //
Protocol
11-2-2016 // Privacy Enhancing Technologies 42

22-03-18
15
Jaap-Henk Hoepman //
Vragen / discussie
30-01-2018 // Privacy by design 43
twitter: @xotoxot8 www.cs.ru.nl/~jhh* [email protected] 8 blog.xot.nl
[Monty Python’s Argument Clinic sketch]